With cloud-hosted applications becoming a mainstay in today’s world of IT, staying compliant with industry standards and benchmarks like SOC 2 is becoming a necessity for SaaS firms. Therefore, getting SOC 2 compliance isn’t a question of ‘why’ as much as it is a ‘when’. With that in mind, here’s a handy SOC 2 compliance checklist to help you plan and kickstart your compliance journey.
But before we get into the SOC 2 checklist, let’s understand the various nuances of the SOC 2 framework that will help you prepare better.
Getting audit-ready involves months of preparation, planning, and ticking things off on a rather lengthy checklist. Defining a scope, choosing the right trust service criteria, implementing internal risk, and assessing controls – these are just a few of your obligations before the reward – is certification. Let’s understand what each step under SOC 2 compliance checklist entails and also an easy shortcut at the end.
| TL;DR The SOC 2 compliance process involves defining objectives, choosing the report type, conducting internal risk assessments, performing gap analysis, contacting an auditor, and more. Autonomous compliance reduces the need for repeated SOC 2 work by keeping controls, evidence, and ownership aligned as your environment changes. Using automation tools for SOC 2 compliance will save you time and reduce costs associated with manual processes and potential non-compliance issues. |
What is the SOC 2 compliance checklist?
The SOC 2 compliance checklist acts as a guide that helps organizations assess how customer data is collected, processed, stored, and accessed, thereby ensuring compliance with the Service Organization Control 2 (SOC 2) framework.
The SOC 2 checklist also reviews vulnerability management and risk mitigation. The checklist enables organizations to meet SOC 2 requirements, demonstrating effective controls over customer information security, availability, processing integrity, confidentiality, and privacy.
Why should you implement a SOC 2 checklist?
Implementing a SOC 2 checklist provides comprehensive coverage and simplifies the audit readiness process. It showcases your commitment to security, reassuring customers that their data is safeguarded. The SOC 2 audit prompts organizations to formalize and document policies, procedures, and controls.
Documenting these essential practices significantly diminishes business risks, enhances vendor management, and frequently streamlines operational efficiency.
SOC 2 requirements checklist
A well-designed SOC 2 requirements checklist will lay out actionable steps organizations can take to meet the extensive criteria of the framework across security, availability, processing integrity, confidentiality, and privacy. Based on our experience of helping hundreds of businesses become SOC 2 compliant.
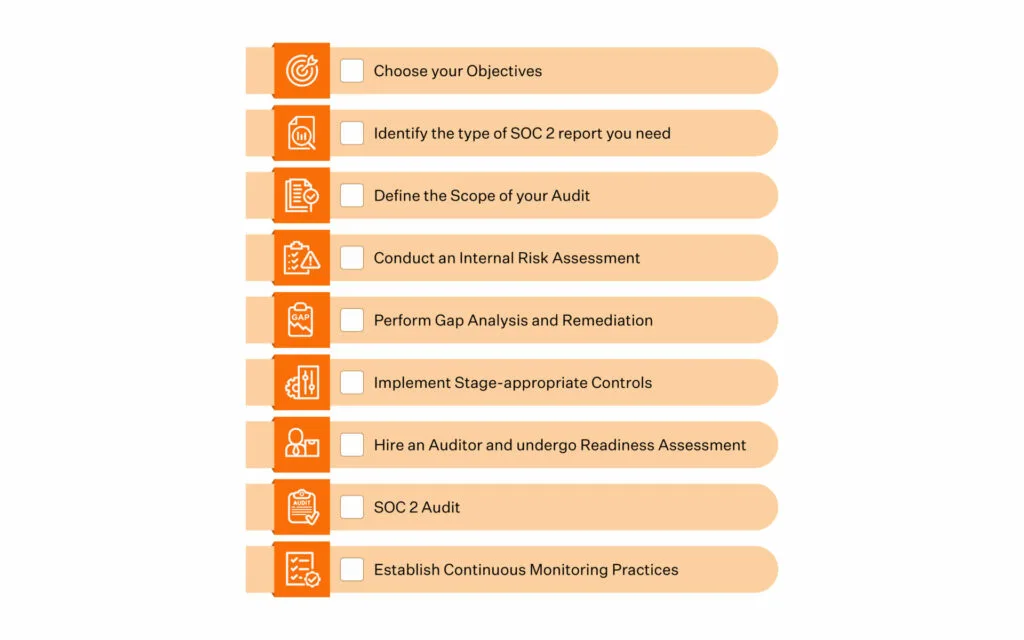
Here’s a 9-step SOC 2 checklist:
1. Choose your objectives
2. Identify the type of SOC 2 report you need
3. Define your SOC 2 scope
4. Conduct an internal risk assessment
5. Perform gap analysis and remediation
6. Implement relevant controls and test them
7. Undergo readiness assessment
8. Conduct the SOC 2 audit
1. Choose your objectives
The first action item of the SOC compliance checklist is to determine the purpose of the SOC 2 report. The specific answers to why SOC 2 compliance is important to you would serve as the end goals and objectives to be achieved in your compliance journey.
With a clear understanding of your objectives, you can ensure the SOC 2 process addresses your particular reasons for pursuing compliance. This clarity will help drive decision-making as you work through defining the scope, assembling a cross-functional team, evaluating controls, undergoing auditing, and taking necessary actions to remediate gaps.
Download your SOC 2 Compliance Checklist
Here are some examples:
- Your customers have asked for it
- You are entering a new geography, and SOC 2 compliance will add to your strength
- You want to bolster your organization’s security posture to avoid data breaches and the financial and reputation damage that comes with it
That said, not wanting SOC 2 compliance because customers aren’t asking for it or because none of your competitors has it isn’t advisable. It’s never too early to get compliant. And it’s always an advantage to be proactive about your information security.
Also read: How to make compliance your superpower
2. Identify the type of SOC 2 report you need
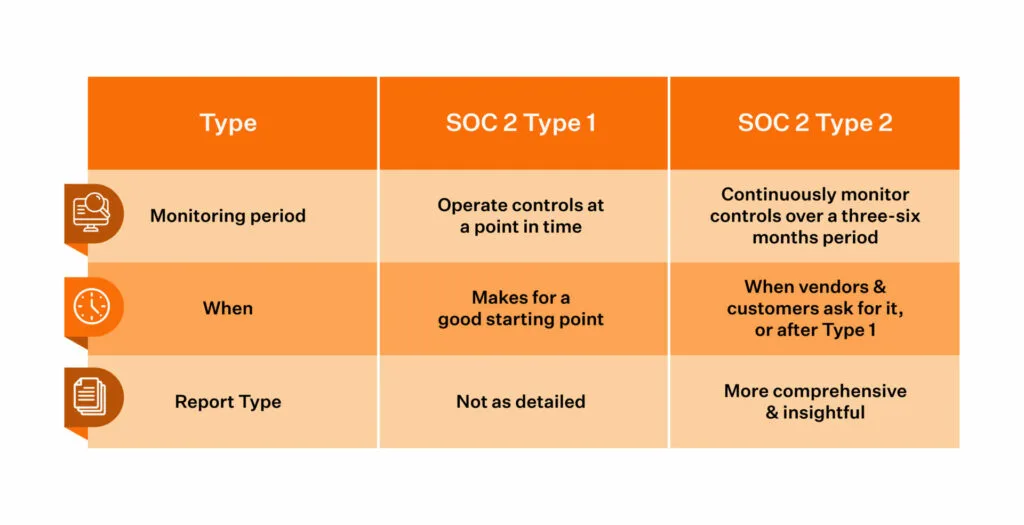
SOC 2 reports can be Type 1 or Type 2. You decide which one is appropriate based on your compliance goals.
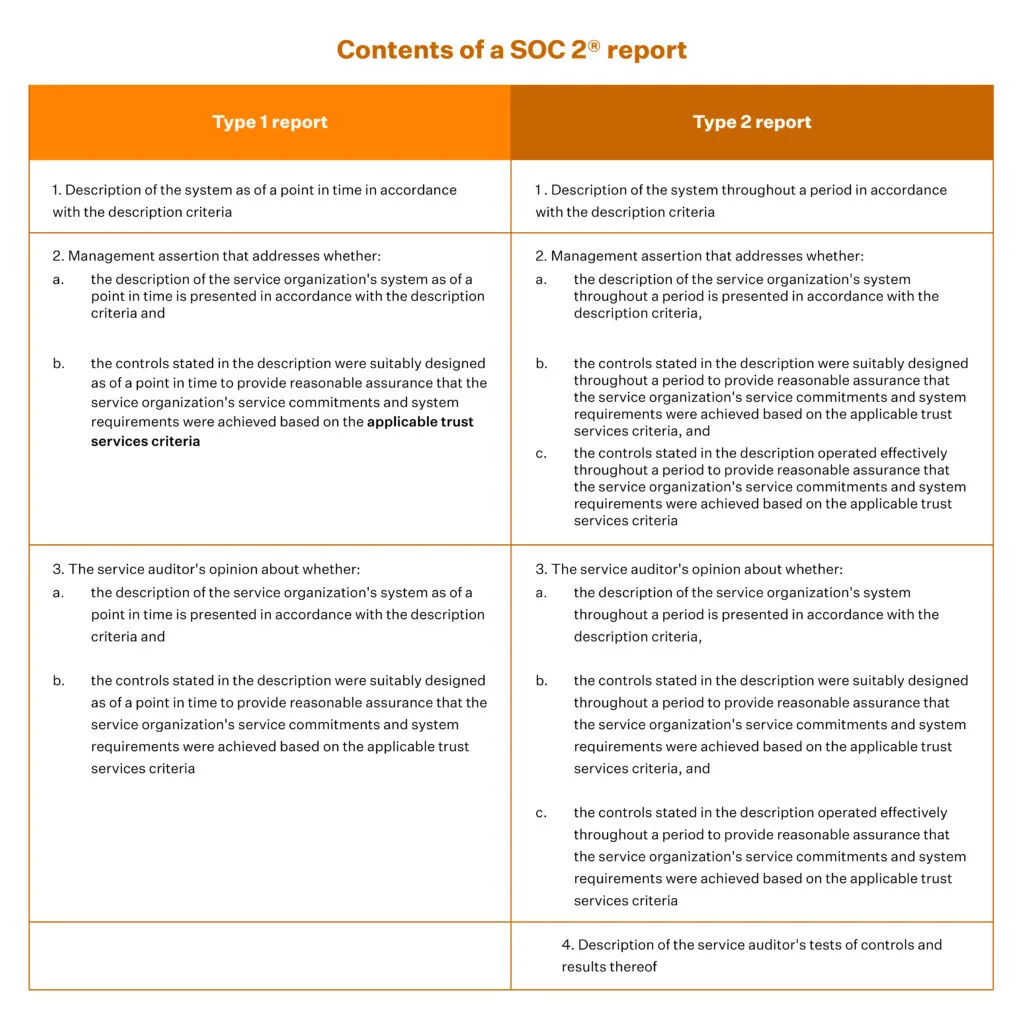
A Type 1 report is faster, but only reflects the performance of controls at a point in time and affirms that your internal controls are in place.
Type 2 confirms that the controls are working as expected when tracked over a period of time, and it is likely that you will be asked to produce a Type 2 audit report shortly after. It is comprehensive and demands a control monitoring period that can be as long as 6 months, but it produces a more vivid picture of the performance of your security controls.

Kickstart with our automated,
ready-to launch toolkit.
3. Define scope
Defining the scope of your audit is crucial as it will demonstrate to the auditor that you have a good understanding of your data security requirements as per SOC 2 compliance checklist. It will also help streamline the process by eliminating the criteria that don’t apply to you.
You must define the scope of your audit by selecting the TSC that applies to your business based on the type of data you store or transmit. Note that Security as a TSC is a must. Regulatory requirements will also have a bearing on your criteria selection. That said, in our experience, most SaaS businesses typically only need Security, Availability and Confidentiality (or their combination) as TSC in their SOC 2 journey.
Here are some examples:
- Choose Availability if your customers have concerns about downtime.
- Choose Confidentiality if you store sensitive information protected by non-disclosure agreements (NDAs) or if your customers have specific requirements about confidentiality.
- If you execute critical customer operations, such as financial processing, payroll services, and tax processing, you should include processing integrity.
- Include Privacy if your customers store PII (Personally Identifiable Information) such as healthcare data, birthdays, and social security numbers.
On that note, a bad example here would be leaving a relevant TSC out of your SOC 2 scope. Such oversight could significantly add to your cybersecurity risk and potentially snowball into substantial business risk.
A SOC 2 audit looks at your infrastructure, data, people, risk management policies, and software, to name a few items. So, at this stage, you must also determine who and what within categories will be subject to the audit. For instance, you can keep some of your non-production assets from the scope of the audit.
4. Conduct an internal risk assessment

Risk assessment is crucial in your SOC 2 compliance journey. You must identify any risks and document the scope of those risks from identified threats and vulnerabilities.
Assign a likelihood and impact to each identified risk and then deploy measures (controls) to mitigate them as per the SOC 2 checklist.
Once you have identified the risks, score them based on its impact and likelihood of that risk scenario actually playing out. A common mistake organizations make in this stage is scoring risks based on guts rather than reality. A better, auditor approved way of scoring risks is by using industry grade benchmarks.
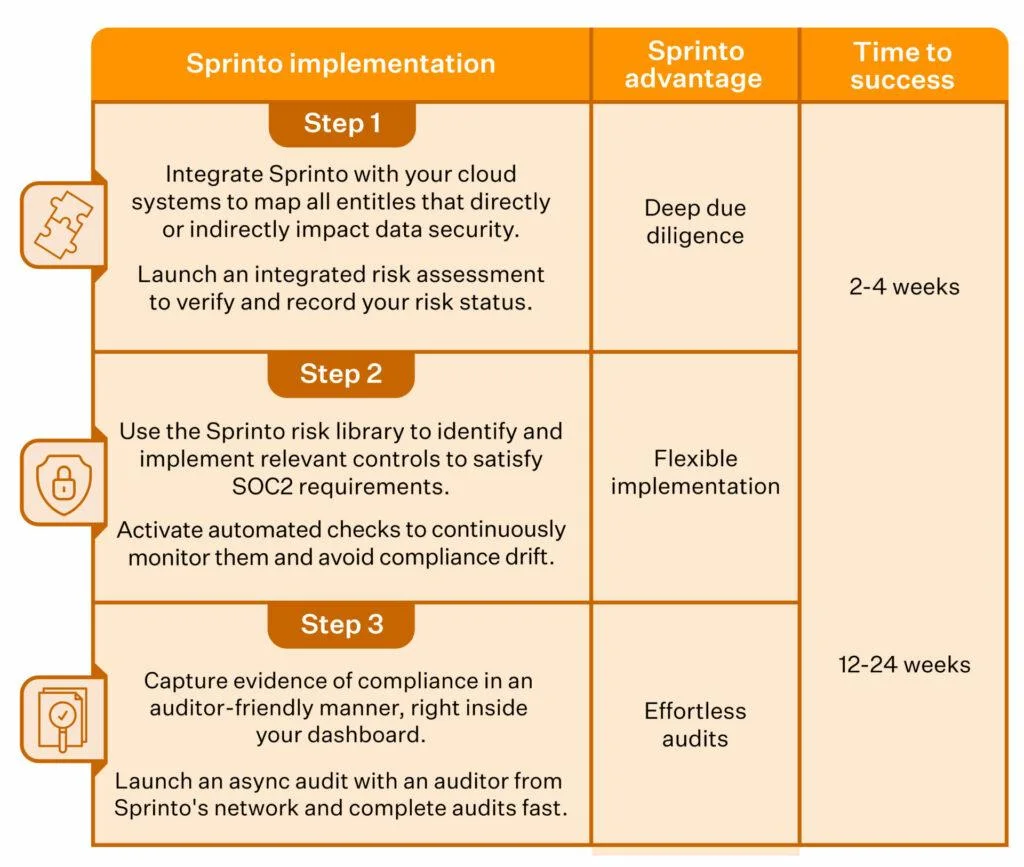
Sprinto helps you run this step with autonomous compliance workflows that keep asset inventory, controls, and risk context connected. Instead of relying on static spreadsheets, you can assess risk with a live view of assets, controls, findings, vendor dependencies, and other changes that affect current exposure.
See how Sprinto reduces SOC 2 prep work across controls, evidence, and ownership.
5. Perform gap analysis and remediation
You must examine your current control status and security practices and compare their compliance posture with how they measure against SOC requirements.
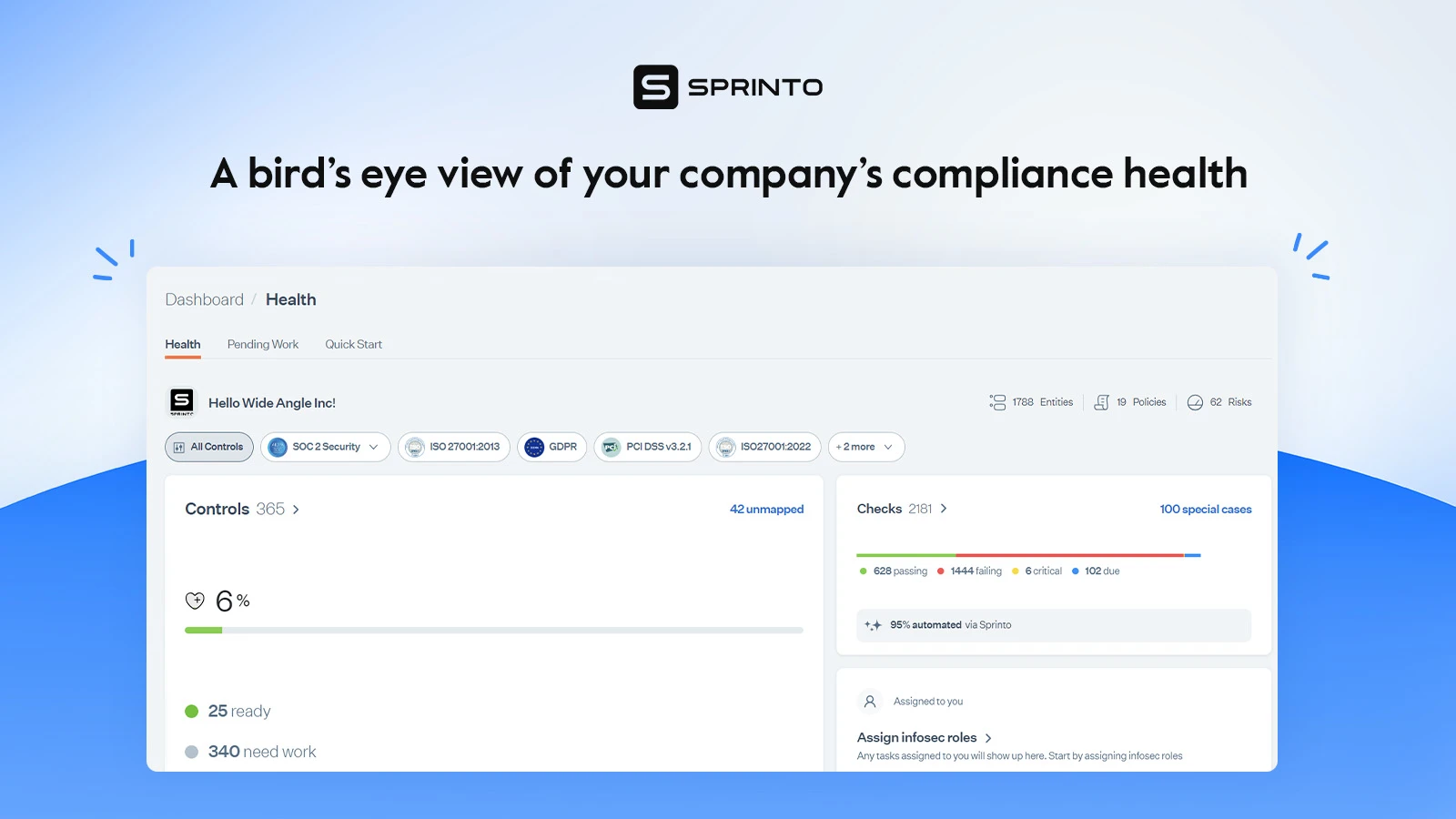
Sprinto makes gap analysis more useful by continuously checking live system configurations, access permissions, vendor integrations, and other control signals against your SOC 2 requirements. That gives you a current view of what is passing, what is drifting, and what needs action before evidence goes stale.
6. Implement relevant controls and test them
Following gap assessment, implement controls to meet compliance and keep asset security in check. These may include modifying security workflows, introducing employee training modules, and creating new process documentation, among others. The risk ratings (carried out earlier) will help you prioritize controls.
Once you have implemented the control, test them for its effectiveness. This is a critical part of SOC 2 Type 2 because here the auditor tests if the controls are working as they should.
Common issues you may face at this stage is not remediating or not getting alerted on failing controls on time and overlooking non-compliance issues which puts you at the risk of not meeting auditor expectations.
Sprinto helps you move from ‘set a control and hope it holds’ to continuous SOC 2 compliance. It maps controls to live evidence, tests them continuously, and routes the next action to the right owner when something drifts. That means fewer missed failures, less follow-up across teams, and better visibility into what actually needs fixing now.
7. Undergo readiness assessment
Undertake a readiness assessment to see if you meet the minimum SOC compliance requirements to undergo a full audit.
Here are your focus areas for the assessment:
- Gap analysis – It aims to detect vulnerabilities and gaps and generate a list of specific recommendations and actions. It takes around 2-4 weeks from start to finish.
- Controls matrix – It lists the objectives map, internal controls identification, and control characteristics.
- Auditor documentation – It involves drafting the request list for auditors and testing procedures.
Based on the auditor’s findings, remediate the gaps by remapping some controls or implementing new ones. Even though technically, no business can ‘fail’ a SOC 2 audit, you must correct discrepancies to ensure you receive a good report.
Readiness work breaks down when policies, control checks, evidence, and ownership are scattered across different places. Manual coordination slows teams down, creates stale proofs, and increases the chance that gaps will only show up when the auditor asks for them.
Sprinto helps you prepare for readiness reviews with autonomous audit management capabilities that keep evidence tied to the live control state, preserve decision trails, and make audit-ready outputs easier to generate when needed. Instead of rebuilding the story during audit week, you can review what is current, what is missing, and what still needs sign-off from a unified dashboard.
“We only need to spend 5-10 minutes a week on compliance now,” notes Rodney Olsen, VP of Engineering at Ripl.
Check out How Ripl achieved SOC 2 compliance while spending 1/3 of the expected effort with Sprinto.
8. SOC 2 audit
Authorize an independent certified auditor to complete your SOC 2 audit checklist and generate a report. While SOC 2 compliance costs can be a significant factor, choose an auditor with established credentials and experience auditing businesses like yours. In your Type 2 audit, you may expect a long-drawn exchange of information with the auditor as you answer their questions, provide evidence, review your internal samples, and discover non-conformities.
Typically, SOC 2 Type 2 audits may take between two weeks to six months, depending on the volume of corrections or questions the auditor raises. Type 2 has a mandatory monitoring period of three-six months. A Type 2 report, therefore, offers more significant insights into your organization’s controls and its effectiveness.
Here are some questions the auditor may ask:
- Can you share evidence to show that all your employees undergo background verification?
- Can you show proof of how you ensure that the changes in your code repositories are peer-reviewed before it is merged?
- Can you demonstrate with evidence that you remove access to emails and databases once an employee resigns from your organization?
- Can you show proof that you run background checks on all your employees?
- Can you share proof of how you maintain the endpoint security of all systems?
The audit for Type 1, in comparison, doesn’t require a monitoring period, is less intrusive, and requires you to give a snapshot (with evidence) of the various checks and systems (read as controls) you have put in place to meet the SOC compliance checklist requirements. Note that after you clear your SOC 2 Type 1 audit, you will need to go through an observation period of three-six months before you can apply for Type 2.
Get Our Practical SOC 2 Guide;
Yours at No Cost

9. Establish continuous monitoring practices
Getting your SOC 2 compliance report isn’t just a one-time event. The report is just a start as security and compliance are on-going efforts . It pays to establish a robust continuous compliance monitoring practice as SOC 2 audits must happen annually.
Continuous SOC 2 compliance is what keeps the checklist from becoming a once-a-year scramble. It means noticing change early, understanding what that change affects, and keeping proof current as systems, access, vendors, and workflows evolve.
That is where Sprinto’s newer capabilities fit naturally. Sprinto tracks live control signals, keeps evidence aligned with the current system state, and helps teams move from periodic compliance check-ins to an always-on program that stays closer to the truth of production.
Aligning Your Checklist with SOC 2 Trust Service Criteria
When going through a SOC 2 audit, your organization will be evaluated based on five Trust Service Criteria (TSC) defined by the AICPA. To properly prepare, you should review your internal controls and procedures to ensure they address each of these criteria.
Here are some tips for aligning your SOC 2 readiness checklist with the TSC:
1. Security
It must be in scope for every SOC 2 audit and is, therefore, referred to as the common criteria. It requires you to enable access control, network firewalls, and other operational/governance controls to protect your data and applications. Enable entity-level controls that establish baseline security policies.
2. Availability
Requires you to demonstrate that your systems meet operational uptime and performance standards. So, implement monitoring for system uptime and performance. Have disaster recovery and incident response processes ready as well.

3. Confidentiality
Shows how you safeguard sensitive data throughout its lifecycle. Implement access controls so only authorized users can access data.
4. Processing Integrity
Have quality assurance checks to validate the accuracy and reliability of data processing. Monitor systems to ensure timely processing and intended outcomes. It includes quality assurance procedures and SOC tools to monitor data processing.
5. Privacy
Requires you to protect Personally Identifiable Information (PII) from breaches and unauthorized access through rigorous access controls, two-factor authentication, and encryption.
Challenges of implementing SOC 2 compliance
Achieving SOC 2 compliance is a major undertaking that comes with some substantial challenges. One hurdle is the time-intensive process of thoroughly documenting all controls, policies, and procedures to SOC 2 standards. You can expect this to take quite some time and effort. There will also likely be costs associated with making required updates to infrastructure or systems to meet compliance criteria.
Even after achieving compliance, the work doesn’t stop. Maintaining SOC 2 requires rigorous ongoing internal control audits. With strict standards to meet, the process of becoming compliant is far from easy. However, for organizations handling critical customer data, the effort is worthwhile to gain trust and demonstrate security commitments.
The Sprinto advantage: We are not just talking about faster setup. It is less operational holdups after setup. Sprinto helps teams reduce repetitive work across controls, evidence, audit prep, and follow-ups, so the compliance load doesn’t keep bouncing back to engineering and ops.
Also check the comparison between ISO 27001 and SOC 2, if you are also considering ISO.
Tips to help you prepare for a SOC 2 audit
Despite SOC 2’s many challenges, organizations achieve compliance in less than three to six months. The more innovative way forward is to use tools that help you navigate its security controls while keeping an eye on them constantly.
Here are four tips to keep in mind before a SOC 2 audit:
1. Automate evidence collection without fail: Evidence are one of the most important parts of audits, so automate wherever possible to remain audit-ready at all times.
2. Review your internal controls regularly: All security controls as per your SOC 2 scope must be reviewed periodically with internal stakeholders assigned with clear ownership.
3. Conduct multiple readiness assessments: It is better to find gaps internally before the audit than after getting the CPA firm involved.
4. Use a platform built for autonomous compliance: The right platform should do more than collect evidence on a schedule. It should keep controls, evidence, and ownership aligned as your environment changes, surface real exceptions early, and reduce manual audit review.
Run SOC 2 with less operational holdups using Sprinto
The SOC 2 process involves extensive documentation, evidence gathering, control testing, and follow-up across multiple teams. The cost is not just the audit itself. It is the repeated work needed to keep controls, evidence, and ownership current. Sprinto helps reduce that burden with autonomous compliance workflows built for continuous monitoring, audit preparation, and clearer accountability.
Sprinto connects policies, controls, evidence, and auditors into a single workflow so teams can spend less time stitching the process together manually. Its continuous compliance engine keeps control status visible, while audit workflows help teams review what is ready, what is drifting, and what still needs action.
Read more: SOC 2 Automation: What Is It, and Why Do You Need It.
What’s more, you can now catalog all your evidence that demonstrates your SOC 2 compliance and present it to the auditors seamlessly, saving you a ton of time and resources.
Case in point: PreSkale completed its SOC 2 audit under 30 days while working with Sprinto.

Sprinto’s autonomous compliance platform also eliminates many additional costs. With Sprinto, you only pay the auditor and the pen testing vendor (not including company-specific incidentals).The result? You save hundreds of hours, fix issues quickly with continuous monitoring, and obtain a hassle-free SOC 2 report. Book a free demo here to see how Sprinto can help you successfully start and sail through your SOC 2 journey.
FAQs
SOC 2 is scoped to a defined system or service, not a blanket certification for everything your company does. In practice, your SOC 2 report describes what is in scope, typically the production environment and the people, processes, infrastructure, software, and data that support that service. This means you can often scope SOC 2 to a specific product or platform. However, shared company processes still matter if they affect the in-scope system, such as access provisioning, change management, incident response, HR onboarding and offboarding, and vendor oversight. The key takeaway is that the system description and scope statement determine what your SOC 2 report actually covers, so align the scope early with your auditor and avoid excluding anything that materially supports the service your customers rely on.
You have complete freedom to choose your own auditor. You are not required to use the compliance platform’s partner auditors. Many automation platforms offer an auditor network to speed up procurement and help standardize the process. However, the audit opinion is still issued by the CPA firm, not the software provider. You pay audit fees directly to the auditor, not through the platform, which ensures independence. This means you can continue working with an auditor you’ve used before or select any CPA firm that offers SOC 2 audit services.
Yes, you can go straight to Type 2 if you already have controls in place and need a report that shows they operated effectively over time. Still, Type 1 can be useful if you need a faster point-in-time report to unblock early deals. Type 1 focuses on whether controls are designed and implemented as of a specific date, while Type 2 evaluates both design and operating effectiveness across an observation period. Observation periods commonly range from 3 to 12 months, and many first-time Type 2 reports start with a shorter window, like 3 to 6 months, then move toward 12 months as the program matures and customer expectations rise.
The timeline depends on how mature your security program is today, how tight your scope is, and whether you are pursuing Type 1 or Type 2. For Type 1, teams with decent baseline controls and a focused scope can often get audit-ready in roughly 1 to 3 months, including time to close gaps and produce evidence. For Type 2, you add the observation period on top of implementation work, plus a few weeks for audit fieldwork and report issuance, so many first-time Type 2 timelines land in the 4 to 9 month range, and can be longer if you have major remediation work or a broad scope. The biggest accelerators are locking scope early, assigning clear control owners, using automation for evidence collection, and doing a readiness check before the formal audit.
Plan for three buckets: auditor fees, readiness and remediation effort, and ongoing tooling to reduce manual evidence work. Auditor fees vary widely by scope, Trust Service Criteria, report period, and auditor brand. Many organizations see Type 1 audits in the mid four figures to low five figures and Type 2 audits in the low five figures to higher, depending on complexity. Automation platforms are usually priced on an annual subscription basis, based on factors like employee count, the number of frameworks, and environment complexity, so costs can range from the high four figures to the low five figures per year for small teams and scale up from there. Also, budget for common add-ons such as penetration testing, vulnerability management, training, and internal engineering time, since remediation work and security tooling often become a significant part of the true first-year SOC 2 cost.
Author
Anwita
Anwita is a cybersecurity enthusiast and veteran blogger all rolled into one. Her love for everything cybersecurity started her journey into the world compliance. With multiple certifications on cybersecurity under her belt, she aims to simplify complex security related topics for all audiences. She loves to read nonfiction, listen to progressive rock, and watches sitcoms on the weekends.Explore more SOC 2 articles
SOC 2 Compliance Overview
SOC 2 Preparation and Documentation
SOC 2 Audit and
Reporting
SOC 2 Differences and Similarities
SOC 2 Updates & Management
SOC 2 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.