According to the AICPA, demand for SOC 2 reports is up nearly 50%, and more companies are taking a hard line: no report, no deal. Consequently, risk teams have tightened their vendor-assessment checklists. Buyers also want a fresh PDF certifying that your services are secure, not promises that the audit is “in progress.”
If you’re trying to land bigger contracts or build trust with security-conscious customers, a SOC 2 audit is the indispensable signal that your business takes data protection seriously and can prove it.
This guide outlines what a SOC 2 audit entails, what it demonstrates to the outside world, and how to navigate the process without disrupting your regular operations.
📋 Quick Summary in 60 Seconds
What is a SOC 2 Audit?
SOC 2 is a security compliance standard that evaluates how a service provider safeguards customer data across five key trust principles: security, availability, processing integrity, confidentiality, and privacy.
Why a SOC 2 Audit Matters:
- Proves your organization’s security, privacy, and availability controls work as designed.
- Builds customer trust and unlocks enterprise deals where SOC 2 is mandatory.
- Demonstrates operational maturity and ongoing compliance readiness.
Challenges in the Audit Process:
- Lengthy evidence collection and remediation cycles.
- Complex scoping and documentation requirements.
- Manual efforts increase the risk of errors and audit delays.
How Sprinto Helps:
- Automates readiness, evidence collection, and control mapping.
- Keeps systems continuously compliant with SOC 2 trust criteria.
- Sprint through SOC 2 audits without slowing operations — Book a Demo with Sprinto!
What’s a SOC 2 audit?
A SOC 2 audit is defined as an independent assessment that verifies if an organization’s internal controls align with the AICPA’s Trust Services Criteria: security, availability, confidentiality, processing integrity, and privacy to ensure adequate data protection and risk mitigation.
It evaluates how your systems are designed and operated over time, focusing on policies, processes, and day-to-day practices. From access management and incident response to employee onboarding and data handling, each control is tested against relevant TSC domains. A successful audit demonstrates trustworthiness to customers, partners, and regulators.
Note
Because SOC 2 is a principles-based framework, auditors interpret how your specific controls align with the criteria and determine what constitutes sufficient evidence.
For instance, if your policy states that all laptops are encrypted, they’ll ask for a sample of device IDs and request screenshots or logs to prove encryption. If you claim monthly access reviews happen for high-risk systems, they’ll want to see dated records showing those reviews took place.
So why go through it at all? Let’s look at why it matters.
What’s the purpose of a SOC 2 audit?
The purpose of a SOC 2 audit is to prove your organization can be trusted with customer data. It provides independently verified evidence that your internal controls meet rigorous security standards, helping you win trust, close deals, and meet regulatory demands.
A clean SOC 2 report is more than a checkbox;, it’s a business enabler. It reduces risk, builds credibility, and accelerates growth by removing barriers in sales and compliance.
Here’s a breakdown of the primary purposes of a SOC 2 audit:
- Radically reduce sales friction: Many SaaS vendors see deals stall during protracted security reviews. A SOC 2 report pre-answers most security, compliance, and risk questions, shortens the sales cycle, and reassures prospective buyers.
- Acts as a forcing function for maturity: The audit process drives continuous improvement, enabling teams to transition from informal workflows to formally documented and consistently executed procedures. It leads to accountability, transparency, and embeds security discipline into day-to-day operations.
- Protects the brand: A clean SOC 2 report instantly helps with credibility and often becomes the clincher for security-conscious clients. The strong internal controls required by the framework also reduce the long-term risk of data breaches.
- Satisfies regulatory and contractual demands: SOC 2 has become almost compulsory in fintech, healthcare, and other regulated sectors. Its controls overlap with ISO 27001, HIPAA, and GDPR, allowing organizations to fulfill multiple compliance obligations through a single, focused effort.
Who needs to go through the SOC 2 audit process?
Any service organization that handles or impacts customer data, whether directly or through its infrastructure, should go through the SOC 2 audit process. While not legally required, a SOC 2 report has become a de facto standard in B2B, especially when selling to enterprises that demand verified proof of your security posture.
SOC 2 is most closely associated with SaaS companies, but it applies broadly to any B2B provider whose systems are critical to client operations or that stores, processes, or transmits sensitive data.
This includes:
- Infrastructure and platform providers (IaaS/PaaS): Companies like AWS, Google Cloud, and Azure undergo rigorous SOC 2 audits.
- Data center and colocation services: They physically house the servers and infrastructure for other businesses.
- Managed Service Providers (MSPs): Firms that manage IT, security, or network infrastructure for their clients.
- Payment processors and fintech companies: Any organization handling financial data is under immense scrutiny.
- Marketing and HR technology platforms: These systems handle sensitive customer lists (PII) or employee data.
What are the types of SOC 2 audits?
There are two types of SOC 2 audits, Type 1 and Type 2. Both are distinctly different in the depth of what they assess and how they do so.
SOC 2 Type 1 audit
A SOC 2 Type 1 audit focuses on the suitability of the design of your company’s controls. The auditor evaluates your security program, processes, and procedures to determine if they are theoretically sound and designed to meet the SOC 2 criteria.
The scope is a single point in time, “as of” a specific date. They attest that on that particular day, your controls were designed and implemented correctly. With controls already documented and operating, a SOC 2 Type 1 report typically takes about four to six weeks to complete.
The Type 1 report is a starting point. It demonstrates that you have designed and implemented a comprehensive security program. Use this if you’re new to SOC but don’t yet have the months of evidence for a Type 2.
SOC 2 Type 2 audit
A SOC 2 Type 2 audit evaluates both the design of your controls and their operating effectiveness. Auditors test to ensure that controls are functioning as intended.
The scope typically spans a period of 6 to 12 months. The auditor examines evidence collected throughout this entire window to verify that your controls were operating as intended, day in and day out.
This audit provides a significantly higher level of assurance and is what most customers and partners expect to see.
| SOC 2 Type I | SOC 2 Type 2 | |
| Main question answered | Are your security controls appropriately designed? | Do your security controls actually work consistently over time? |
| Focus | Evaluates the design of your controls at a single moment. | Evaluates the effectiveness of your controls over a period. |
| Time period | A snapshot on a specific date | A window of time, usually 6-12 months |
| Auditor role | Reviews policies and confirms controls are in place. | Reviews policies, confirms that controls are in place, and then tests samples of evidence from the entire period to determine if they were effective. |
| Level of assurance | Moderate. | High. |
SOC 2 audit scope
The SOC 2 scope has two components. The first step is to define the system or service being audited, which includes products, infrastructure, and relevant teams. The second, and more important, is selecting the Trust Services Criteria (TSC) to be included.
Here are the five TSCs you need to know about:

- Security (Required): The bedrock of every SOC 2 engagement, Security addresses safeguards like firewalls, MFA, and vulnerability management that prevent unauthorized access, misuse, or modification of systems and data. Regardless of industry or size, an organization cannot issue a SOC 2 report without meeting this domain.
- Availability (Optional): Chosen by providers who commit to strict uptime or disaster-recovery objectives. Controls focus on capacity planning, fault tolerance, backups, and incident‐resolution SLAs. It’s a common add-on for cloud infrastructure, SaaS, and critical B2B services.
- Confidentiality (Optional): Required when the service handles proprietary or otherwise sensitive business information such as legal documents, source code, or intellectual property. Encryption in transit and at rest, granular access controls, and data-retention rules are key controls.
- Processing Integrity (Optional): Relevant to platforms that perform calculations, transformations, or transactions where accuracy and completeness are paramount (e.g., fintech apps, payroll engines, tax-filing software). Controls cover input validation, error handling, reconciliation, and quality assurance testing.
- Privacy (Optional): Appropriate for services that collect or store personal data subject to regulations such as GDPR, CCPA, or HIPAA. Controls focus on notice and consent, purpose limitation, data subject rights, secure disposal, and breach notification procedures.
SOC 2 audit readiness assessment
The SOC 2 readiness assessment is a systematic, top-to-bottom review of your current environment mapped against the specific SOC 2 Trust Services Criteria you plan to include in your scope.
The goal is simple—to identify every single gap between your current practices and what an auditor will expect to see long before they walk in the door.
A good readiness assessment produces a detailed gap analysis report. It specifies exactly which controls are failing, why they are failing, and the evidence you’ll need to produce to prove you’ve fixed them. If you’re unsure of where to begin, here’s a pre-built self-assessment catered to SOC 2:
Download your assessment template
Coming up with a SOC 2 remediation plan
The next step is to create an action plan that addresses the gaps identified in the readiness assessment and defines the scope. The SOC 2 remediation plan is a detailed, project-managed effort to close every identified gap, establish new controls where necessary, and generate the evidence an auditor requires to verify compliance.
Each remediation task should have a clear owner responsible for its completion, a specific deadline, and a definition of what done looks like.
For instance, if your risk assessment process has a gap, you must task it with tasks such as developing a risk assessment methodology, conducting a company-wide risk assessment, and securing management approval of the results by Q3.
This plan builds the foundation of a compliant program. Now, let’s see how you do the audit.
How to navigate the SOC 2 audit process step by step
Your SOC 2 audit should be a well-defined project that progresses from high-level planning to a granular review of evidence. Here are the steps you can expect once you’ve completed your readiness work:
Step 1: Source and select your auditor
SOC 2 reports can only be issued by a licensed CPA firm, so the first task is to identify audit partners who
(a) Specialize in SOC 2,
(b) Understand cloud-native environments like yours, and
(c) Can commit to a realistic timeline and budget.
Vet each candidate’s peer-review record, methodology, and industry references.
If you’re using a compliance platform such as Sprinto, you can tap its pre-vetted auditor network of firms that already understand the platform’s data feeds, and cut weeks of back-and-forth during scoping.
Step 2: Audit kickoff and planning
You’ll meet with the audit team to finalize the practical details of the project. Here, you confirm the audit’s scope (which TSCs are included), the audit period for the report, and the key timelines for evidence submission and fieldwork.
During this phase, you will provide the auditors with your core set of documentation, including your system description, key policies, and the list of controls you’ve designed. This provides them with the roadmap they will use for the remainder of the audit.
Step 3: Evidence request and collection
Shortly after the kickoff, you will receive the first, and typically most substantial, evidence-request list from your auditors. The list is an exhaustive and specific inventory of required proofs. Your team’s primary task during this phase is to gather and upload evidence to the auditor’s secure portal.
Manually chasing these artifacts by pulling logs, screenshots, and tickets into worksheets can take months and drain engineering bandwidth. Compliance-automation software, such as Sprinto, plugs directly into your cloud and SaaS stack, automatically collects real-time evidence, and pipes it into an auditor’s dashboard so both parties work from the same live data.
Step 4: Auditor fieldwork and testing
Fieldwork is the audit’s main event, though it’s almost always conducted remotely now. During this phase, the auditors investigate the evidence you’ve provided. They operate on a principle of sampling to test the operating effectiveness of your controls (for a Type 2 report).
They will select random samples from the populations you provided, like new hires, system-change tickets, or terminated employees, and perform detailed testing on that sample to verify your controls worked every time.
It’s an interactive phase; expect numerous follow-up questions and requests for clarification.
Step 5: Addressing exceptions
If auditors identify control failures or “exceptions,” you have a brief window to remediate the root cause or document a management response.
Minor exceptions may only require additional evidence; more significant ones could trigger a redesign of control or a modified opinion. Prompt and transparent fixes demonstrate a culture of continuous improvement and often satisfy the audit team without delaying issuance.
Step 6: Draft report review and management assertion
Once the auditors have completed their testing, they compile their findings into a draft report. They provide this draft so you can check it for factual accuracy and confirm that they have correctly described your company, technology stack, and systems.
At the same time, you will be asked to provide a “management assertion” letter, a formal document signed by leadership stating that you are responsible for the design and operation of the audited controls.
Step 7: Final report issuance
After your team has reviewed the draft and returned the signed management assertion, the audit firm issues the final, signed SOC 2 report.
This document contains the auditor’s opinion, the management assertion, a detailed system description, and the results of control testing. It’s the attestation you can now share with customers, prospects, and partners.
Tips for a successful SOC 2 audit
Don’t expect a perfect SOC 2 audit with a last-minute scramble. You’re building the framework for building a durable, ongoing security program. The final report is simply the byproduct of a well-run operation. It’s the process that matters. Here’s how you get the most out of the audit:
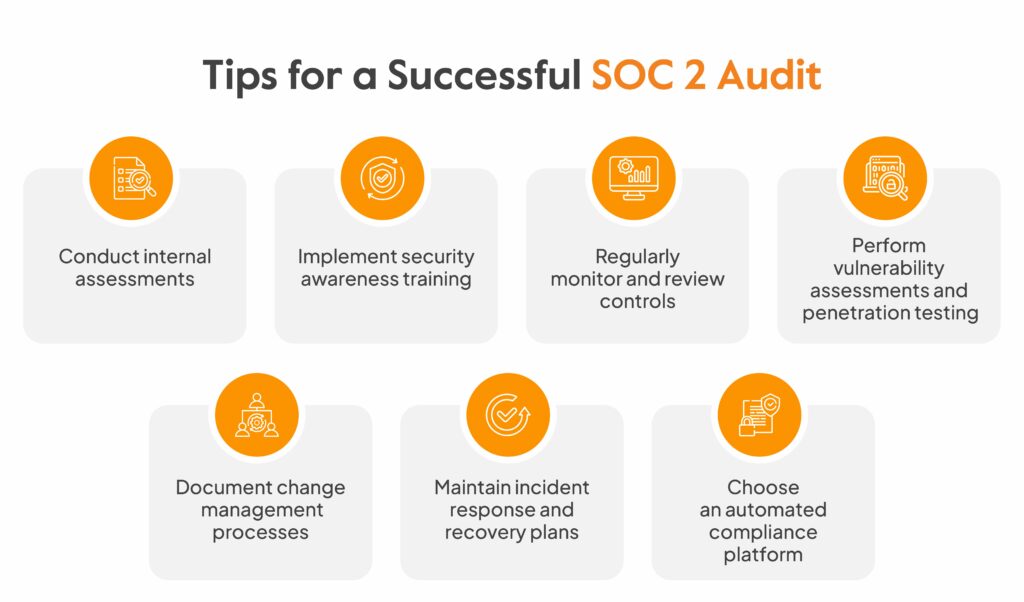
1. Conduct internal assessments
Before you pay a CPA firm for a formal audit, you need to know where you stand. A thorough internal assessment, or readiness assessment, is the single most crucial preparatory step you can take.
This is a full-scale simulation of the real audit, where you meticulously review your current practices against every single SOC 2 criterion in your scope. You are intentionally looking for the gaps, weaknesses, and areas where you lack sufficient evidence.
Ensure that the process yields a detailed gap analysis that serves as your remediation guide.
Sprinto, a compliance automation platform, takes the heavy lifting out of internal assessments by automating control checks, evidence collection, and policy enforcement across your cloud environment. Instead of manually tracking compliance tasks or chasing teams for documentation, Sprinto continuously monitors your systems, identifies control gaps, and generates audit-ready reports in real-time.
2. Implement security awareness training
Many SOC 2 controls hinge on your people. For organizations also pursuing ISO 27001, building an ISMS awareness training program ensures employees understand both SOC 2 and ISMS requirements. Your employees are your first line of defense, and auditors are aware of this. That’s why you need a strong security awareness training program.
Auditors will want to see evidence that this training actually happens and that employees understand it. You’ll have to keep records of who completed the training and when. It also means conducting periodic phishing simulations to test whether the training is practical.
3. Regularly monitor and review controls
You must have documented proof that you are continuously monitoring your security posture.
You’d perform periodic user access reviews to ensure that former employees have been de-provisioned and that current employees only have the access they need to perform their jobs. You’ll also regularly review system logs, firewall rules, and system configurations to detect any suspicious activity.
An auditor will specifically request evidence of these reviews.
4. Perform vulnerability assessments and penetration testing
You can have hundreds of well-designed controls, butto uncover technical weaknesses that well-designed controls alone can’t catch. Our penetration testing guide covers the five types of pen tests, methodology approaches, and how to interpret results for remediation.
This is where a vulnerability assessment becomes critical, helping you proactively uncover and address risks before they’re exploited.
Vulnerability scanning should be an automated process that constantly scans your environment for known security flaws. A penetration test is a more focused, manual effort in which security experts attempt to breach your defences.
5. Document change management processes
Auditors need to verify that you have an enforceable process in place for managing changes to your production environment. An undocumented change is an uncontrolled change, representing a significant risk.
Your change management process ensures that every modification, whether a minor code update or an infrastructure upgrade, is proposed, reviewed, tested, and approved before being deployed.
To satisfy this, you need an audit trail. You must be able to provide evidence for any change the auditor picks as a sample. This resides in a ticketing system, such as Jira, and is linked to your source control system, like GitHub.
6. Maintain incident response and recovery plans
Despite your best efforts, security incidents can and will happen. A mature organization is judged not just by its ability to prevent incidents, but also by how it responds when one occurs.
SOC 2 requires you to have a documented incident response plan that details the steps your team will take in the event of a breach.
Alongside this, a disaster recovery plan is essential for availability. For data centers handling PHI, our guide to assessing HIPAA data centre compliance covers the additional physical safeguards, risk assessments, and HROC documentation requirements beyond standard SOC 2 criteria. This plan outlines the steps to recover your service in the event of a catastrophic failure. Auditors will ask to see both of these plans.
7. Choose an automated compliance platform
Managing the hundreds of controls, evidence requests, and policies required for SOC 2 manually is a monumental task, even for a dedicated team. Spreadsheets and shared drives are prone to human error. It’s wise to turn to compliance automation platforms.
That’s where tools like Sprinto provide pre-built policy templates, enable you to map your controls directly to SOC 2 criteria, and integrate with your tech stack to automatically collect evidence continuously. If you’re missing out on a huge efficiency boost without one of these.
What’s included in SOC 2 audits for service organizations?
Expect to see these in a SOC 2 Audit report:
- Auditor’s opinion: This is the main judgment from the CPA firm. In a Type 1 report, it verifies whether controls are appropriately designed at a specific point in time. In a Type 2, it also checks if those controls worked as intended over a set period.
- Management assertion: A signed statement from your leadership team taking responsibility for the control environment and confirming the accuracy of your system description.
- System description: Your team writes it and outlines what your service does, the people, processes, and technology behind it, and also the commitments you make to customers around security and reliability
- Tests of controls and results: This is the longest and most detailed part. It lists each control, the auditor’s testing methods, and the outcomes. This section provides the evidence that supports the auditor’s opinion.
Who performs a SOC 2 audit?
SOC 2 audits are typically conducted by independent, third-party Certified Public Accountant (CPA) firms licensed by the AICPA. Because the AICPA governs the SOC 2 framework, only its licensed members are authorized to issue valid reports.
To maintain objectivity, the auditing firm must have no prior involvement in designing or implementing your controls. While consultants can assist with readiness and remediation, auditors must maintain full independence.
How much does a SOC 2 audit cost?
The cost of a SOC 2 audit can vary widely based on the scope of the audit, the type of report (Type I or Type II), and the complexity of your systems and operations. While auditor fees comprise the core expense, there are often significant hidden costs associated with preparation and remediation. The table below outlines typical cost ranges and what each component includes.
| Cost Component | Estimated Range | What it covers |
| Type I Audit | $5,000 – $25,000 | One-time evaluation of control design at a specific point in time |
| Type II Audit | $7,000 – $50,000 | Evaluation of control effectiveness over a defined observation period |
| Typical Total SOC 2 Audit Cost | $30,000 – $50,000 | Full audit cost depending on size, scope, and selected Trust Criteria |
| Hidden/Additional Costs | Varies | Internal staff time, policy creation, security tools, remediation, legal |
How often does the SOC 2 audit occur?
SOC 2 audits are performed annually. They are not a one-time certification but a recurring process meant to provide ongoing assurance about your security posture. A report older than 12 months is considered outdated and may not satisfy customer or partner requirements.
Between audits, if customers request updated assurance, organizations typically issue a “bridge letter” or “gap letter,” a formal statement from management confirming that no material changes have occurred in the control environment since the last audit.
Sprint through audits without breaking your stride with Sprinto
SOC 2 isn’t hard because the controls are complex; it’s hard because tracking proof across tools, teams, and months is a mess. Left to manual effort, it slows down your team and turns compliance into a nightmare.
Sprinto is designed to eliminate all of this clutter. Sprinto connects to Google Workspace and other platforms for continuous monitoring. For healthcare organizations specifically using Gmail, our guide to making Gmail HIPAA compliant explains the Google Workspace setup, BAA signing process, and security configurations required. When a new hire joins, it automatically checks off the onboarding steps: account creation, access provisioning, security tooling, and logs timestamped evidence, all without you lifting a finger.
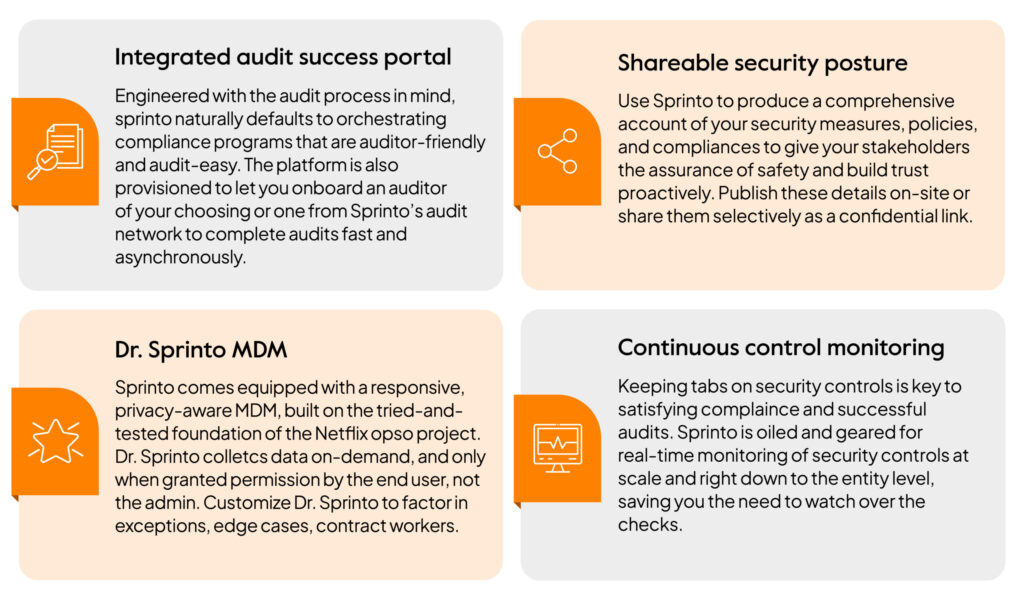
Beyond evidence collection, Sprinto:
- Provides auditor-ready policy templates you can customize and publish in minutes
- Tracks security training and certification completion automatically
- Maps controls to SOC 2 criteria across the Trust Service Principles in a unified dashboard
- Creates a portal for auditors to access documentation and test results directly, eliminating the tedious back-and-forth process.

Automate and Fastrack with Sprinto.
Frequently asked questions
SOC 1 is about controls that could impact a client’s financial reporting. It’s for services like payroll processors or loan servicers. SOC 2, on the other hand, is about controls related to data protection and security, based on the Trust Services Criteria. Cloud hosting providers storing customer data need SOC 2 and may also need PCI DSS compliance. Our guide to PCI compliant web hosting options reviews five providers and explains why hosting compliance is a shared responsibility between you and your provider.
No, there is no law that mandates a SOC 2 audit. It’s almost always a market-driven requirement. Your customers, especially larger enterprises, will likely demand a SOC 2 report as a condition of doing business with you, to ensure that you can be trusted with their data.
Only independent, licensed Certified Public Accountant (CPA) firms that the AICPA recognises can perform a SOC 2 audit. Your friendly neighbourhood IT consultant can’t do it; it must be a formal attestation from a licensed firm.
A SOC 2 audit needs to be performed annually. A report is just a snapshot in time (or over a period), so to provide continuous assurance to your customers, you need to renew your audit annually to demonstrate that your controls are still adequate.
Failing means the auditor issues a “qualified” or “adverse” opinion in your final report. This report is still shared with customers, but it will have a big red flag indicating that specific controls failed their tests. This erodes customer trust and can potentially block sales. If you fail, you must fix the issues before the next audit cycle.
To prepare for a SOC 2 audit, organizations should follow a structured checklist to ensure all key requirements are met:
Define audit scope and Trust Services Criteria
Perform a readiness assessment
Implement and document security controls
Collect evidence of control implementation
Conduct internal risk and gap analysis
Train employees on security policies
Engage an independent CPA firm for the audit
Address control exceptions, if any
Review and sign the management assertion
Finalize and receive the SOC 2 report
Author
Pansy
Pansy is an ISC2 Certified in Cybersecurity content marketer with a background in Computer Science engineering. Lately, she has been exploring the world of marketing through the lens of GRC (Governance, risk & compliance) with Sprinto. When she’s not working, she’s either deeply engrossed in political fiction or honing her culinary skills. You may also find her sunbathing on a beach or hiking through a dense forest.Explore more SOC 2 articles
SOC 2 Compliance Overview
SOC 2 Preparation and Documentation
SOC 2 Audit and
Reporting
SOC 2 Differences and Similarities
SOC 2 Updates & Management
SOC 2 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.











