TL;DR
- SOC 2 Type 1 is an attestation audit that evaluates whether an organization’s internal controls are suitably designed at a specific point in time to meet the AICPA’s Trust Services Criteria, covering security, availability, confidentiality, processing integrity, and privacy.
- It provides a snapshot of your control design rather than monitoring controls over an extended period (which is what SOC 2 Type 2 does), making it ideal for companies that need to demonstrate compliance readiness quickly or unblock enterprise deals.
Within 30-45 days of becoming compliant, we onboarded 2 enterprise clients!
“We looked at what we needed to do and across which aspects of the business. We figured out the controls and implemented a few of them, but managing them with the right set of information and updating them periodically were lacking. This is where Sprinto became a need,”
These are common sentiments shared by our customers. However, they often inquire about key aspects of SOC 2 Type 1 compliance:
- What is a SOC 2 Type 1 report?
- Why is SOC 2 Type 1 important?
- How much does SOC 2 Type 1 cost?
- How do you obtain a SOC 2 Type 1 report?
And this article will answer all the questions and beyond. You will learn the basic difference between SOC 2 type 1 compliance and Type 2, its importance, and how to prepare for a SOC 2 Type 1 audit.
Compliance is increasingly becoming a buyer requirement, not just a security milestone. In Sprinto’s Business ROI of Compliance 2026 report, 40% of organizations said over half their customers now consider compliance non-negotiable.
What is SOC 2 Type 1?
SOC 2 Type 1 compliance reviews whether the organization’s internal controls are suitably designed at a period in time to meet AICPA’s trust service criteria (security, availability, confidentiality, processing integrity, and privacy).
SOC 2 controls could be preventative, detective, or corrective.
The basic idea is to assure your current and potential clients that you follow security best practices to manage sensitive information.
While getting SOC 2 compliance isn’t compulsory, it is highly beneficial. This is because large organizations put paramount importance on information security. They are unlikely to partner with any organization that does not present a strong security-first posture.
“Our clients want to know that any information they share with us is secure.”~ Rafael Urgilés, Chief IT-S Consultant at Kin Analytics. They pursued SOC 2 after clients started asking for assurance around shared data, and Sprinto helped the team complete its SOC 2 Type 1 audit in 3 days.
Who needs SOC 2 Type 1 compliance?
The types of organizations that consider SOC 2 Type 1 are SaaS firms, companies storing sensitive customer data in the cloud, and cloud service providers. Let’s see the breakdown below:
- Are a SaaS vendor who processes, gathers, or manages sensitive data
- Need to demonstrate security compliance urgently, SOC 2 Type 1 report will come to your rescue as the timeline is significantly shorter
- Are you starting your security compliance journey and want to know if you can meet the goals of Type 2
- Are low on the budget but need one to land more sales deals
Getting SOC 2 compliance isn’t compulsory. Usually, businesses opt for SOC 2 Type 1 first, but this depends on your organizational needs. It surfaces areas for improvement, which you can address during a SOC 2 audit.


Kin Analytics
What is the difference between a SOC 2 Type 1 and Type 2?
SOC 2 Type 1 and SOC 2 Type 2 differ in the assessment and monitoring period of the internal controls. SOC 2 Type 1 evaluates the design of the security controls at a point in time, whereas SOC 2 Type 2 reviews the design and operational effectiveness of the controls over a period of 3-12 months.
While organizations that are initiating their security compliance journey or require an immediate review of their controls should opt for Type 1, those that have already completed Type 1 or do not require an immediate report should choose Type 2.
SOC 2 Type 1 is generally opted for by those who are beginning their security compliance journeys. It is sometimes also used as a buffer to buy in time.
Businesses start off with a Type 1 attestation to show their prospects their intent towards becoming compliant to move their business deals forward while simultaneously laying the roadmap to becoming SOC 2 Type 2 compliant.
Another differentiating factor is the objective of the report. SOC 2 Type 1 testifies that you have the controls in place. SOC 2 Type 2, on the other hand, attests to the operating effectiveness of your internal controls along with the design.
Also check out: A Quick Guide to SOC for Supply Chain
“Point-in-time audits show compliance on a given day, while Type 2 evidence gives auditors a clearer picture of how the posture was maintained across a period.” ~ Abir Dey [An excerpt from Crafting a Compliance Engine That Runs Itself webinar]
What are the benefits of a SOC 2 Type 1 compliance report?
As previously outlined, the SOC 2 report is not a must-have but a good one. Below are the 5 reasons to get SOC 2 Type 1 for your organization.
- Competitive edge for startups
- Shorter sales cycle
- Immediate requirement
- Cost-effective
- Kickstarts compliance
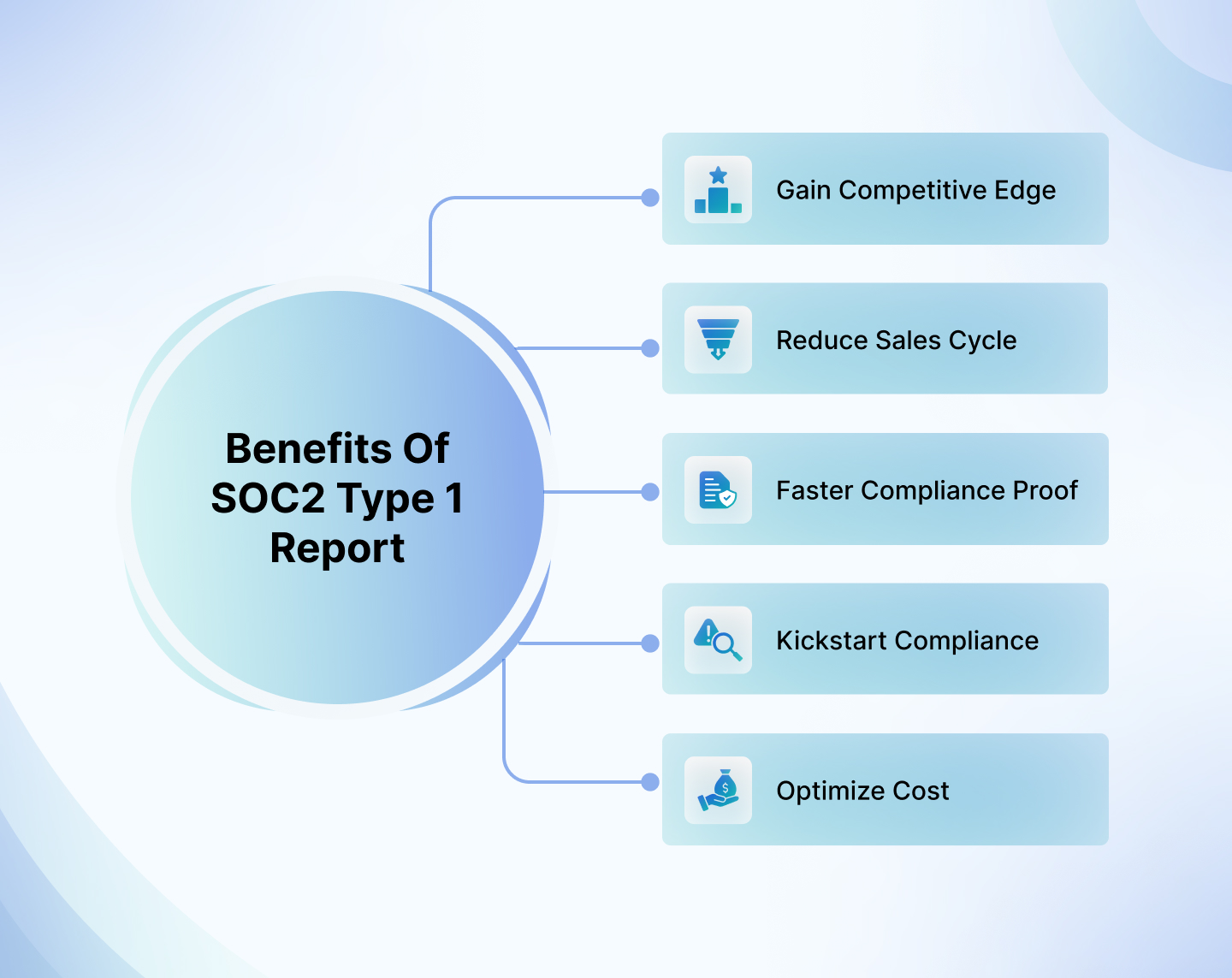
1. Competitive edge for startups
As a SaaS vendor, customer acquisition and retention can be daunting. With many new vendors offering the same service, you must square up to survive an ever-expanding B2B space. As a new player in the market, you won’t have the time to wait months to get Type 2 to show security compliance.
At this stage, you should consider Type 1 compliance. It is a unique selling point (USP) for your business and provides a competitive edge against other new players.
For example, let’s take the case study of Zipy we mentioned above:
Here, the main problem statement for Zipy was that at some point, customers began requesting that independent auditors review and verify their policies and practices, with SOC2 compliance being a primary concern, particularly in North America. Without this, they lost some deals to customers.
However, once they integrated themselves into Sprinto, Zipy realized that if they could achieve SOC2 compliance, other compliances would fall into place quite easily – SOC2 coverage is comprehensive that way.
Since achieving SOC2 compliance, Zipy has experienced a noticeable increase in customer interest. More people are willing to talk to them now. Hence, having a SOC 2 Type 1 attestation report clearly builds confidence in the business and the platform.
63% of early-stage organizations unlocked new TAM post-certification, while the proportion rose to 83% among larger organizations. [Source: Sprinto’s Business ROI of Compliance 2026 report]
2. Shorter sales cycle
With growing security concerns, your prospects can keep going back and forth on infosec controls before finalizing the deal. A SOC 2 report here can help you answer security questionnaires easily and shorten your sales cycle.
At Sprinto, customers often find that answering “no” to “Are you SOC 2 certified?” leads to an avalanche of about 160 additional questions.
“Companies no longer pursue SOC 2 only because existing contracts require it; they pursue it so they can enter sales cycles where SOC 2 is required.” ~ Ricky Waldron, GRC Leader [An excerpt from Crafting a Compliance Engine That Runs Itself webinar]
This can significantly slow down the sales process. However, once they achieved SOC 2 readiness within just 4 weeks of implementation, the sales cycle accelerated, and trust with customers increased more than ever before.
3. Immediate requirement
Many SaaS organizations don’t implement security protocols without an immediate requirement. If your client wants proof of good security practices and you don’t have one, Type 1 will come to your rescue.
This is because a SOC 2 report, irrespective of the Type, is the primary document to demonstrate your overall data security efficiency. It is an industry-standard report accepted by organizations of all sizes.
One of our clients, Recruit CRM, faced issues closing large enterprise deals due to a need for SOC 2 certifications. Initially, they chose a security assessment vendor who couldn’t help them get compliant, so they started searching for an implementation partner.
They discovered Sprinto, and within an hour of the first call, they had admin users appointed, alerts for potential spikes were set up, and a Slack channel was created for communication with the Sprinto team.
Sprinto oversaw a control-based compliance program across various security standards. They linked the compliance evidence to controls associated with multiple standards, creating a comprehensive audit evidence library.
Ultimately, Recruit CRM achieved SOC 2 audit readiness in under 10 sessions with Sprinto’s assistance.
4. Kickstarts compliance
If you are considering security compliance, Type 1 is a good option to start with. This is because it is ideal to check if you are ready for Type 2 and can handle more rigorous security protocols.
5. Cost-effective
Security compliance is important if you are a startup or small business, but budget restrictions may keep you from getting one. While both types of SOC 2 audit reports are costly, Type 1 costs between $8000 and $30000, while Type 2 will set you back anywhere from $20000 to $50000.
However, Sprinto can save your costs by up to 60%, and you can get the report within your budget. Investing in compliance automation platforms like Sprinto can save you money over time. Audits and compliance come with ongoing expenses, which rise as you expand into new regions and adopt more frameworks.
Automating SOC 2 Type 1 will strengthen security by continuously adhering to best practices. Also, with Sprinto, collecting evidence is much easier and makes the process efficient, accurate, and swift.
“The 200+ native connectors (like AWS, Jira, and Slack) make it incredibly fast to pull data without manual uploads. Because it integrates directly with our stack, it captures audit-ready evidence automatically, which saves us hundreds of hours during SOC 2 or ISO 27001 prep.” ~ Sunil C., Head of Data & Operations, Small-Business, in a G2 review.
How do you prepare for the SOC 2 Type 1 compliance audit?
A Type 1 audit evaluates the service organization’s security processes and other effectiveness of controls at a point in time. An AICPA-accredited Certified Public Accountant (CPA) will conduct this audit.
Here are a few steps your organization can take to prepare for SOC 2 Type
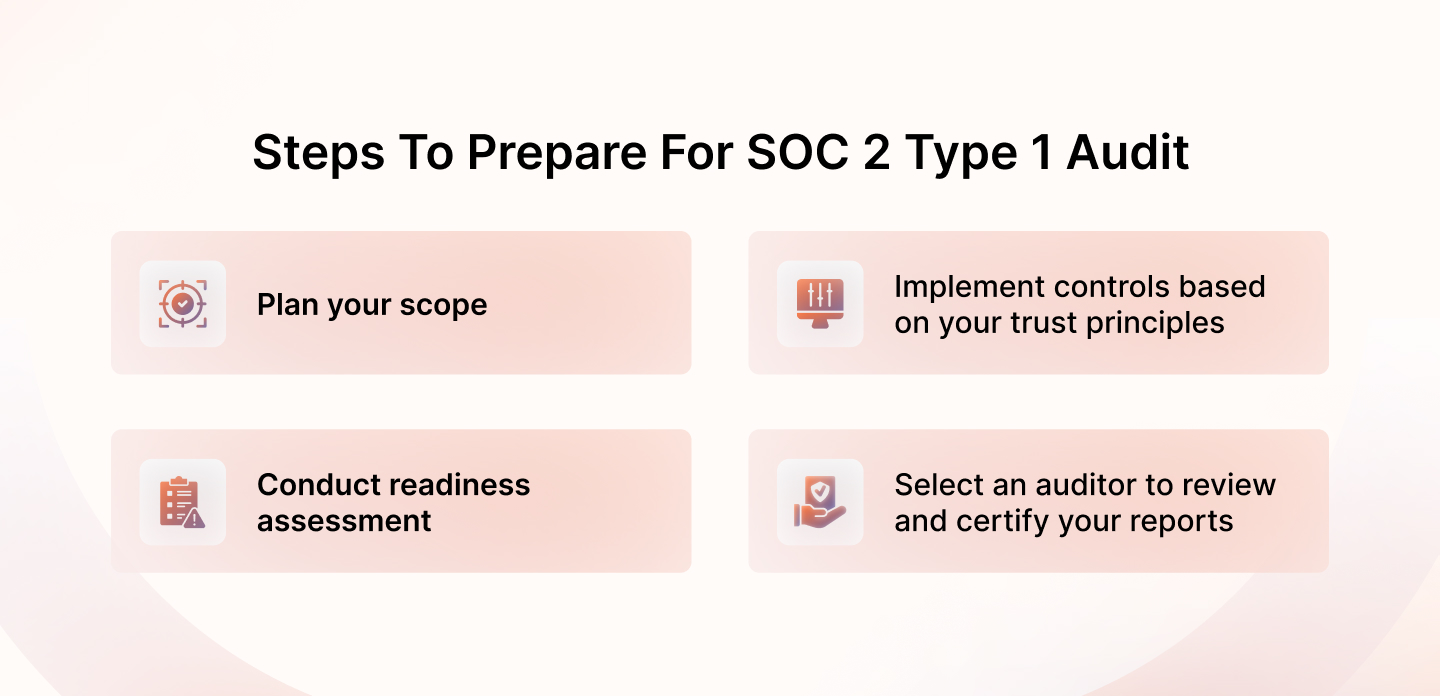
1. Plan your scope
There’s a ton of things to sort out before, during, and even after an audit, so things can get messy without a roadmap. We suggest setting the following roles:
- Department-wise team leads: Get someone from each department, like sales, IT, operations, and more.
- Executive sponsor: Basically, it’s a fancy term for a project lead. A senior member with a good understanding of company processes and policies is right.
- Document creator: You should record every process, so assigning the compilation task to another person makes sense.
Once you decide who does what, it is time for more planning. As the SOC 2 report is based on the five trust principles, use those to define and scope your project.
Not every principle is applicable to every organization, so identify the areas of work. Security is an absolute must-have, irrespective of the type of data you process and how you handle it. Other principles are optional and depend on organizational needs.
For example, while availability can be relevant for all cloud-hosted businesses, processing integrity needn’t. Processing integrity comes into play when you manage financial transactions, data processing, and more. Confidentiality is required if you store sensitive information secured by a nondisclosure agreement (NDA).
2. Implement controls based on your trust principles
It is time to set up administrative and technical security policies across your IT environment. This will be based on the trust criteria. Here are the controls for each:
- Security: It has nine common criteria (CC), of which five are compulsory. These are control environment, risk assessment, communication and information, monitoring of control, and design of controls.
- Availability: Possible control to meet this requirement may include Incident Response Planning (IRP) and Distributed Denial of Service (DDoS) protection.
- Confidentiality: You should have internal controls like data encryption, access control, and network firewall to meet this criteria.
- Processing integrity: Controls related to policies and procedures to maintain operational efficiency and data accuracy. Endpoint security and server safety are important if you work with a Cloud Service Provider (CSP).
- Privacy: Comprises eight controls related to data management, security, use and disposal, and more. Possible internal controls to meet this requirement include encryption, two-factor authentication, and access control.
While this is a much-needed step to identify cybersecurity gaps, don’t strive for perfection at this stage. Instead, let the small gaps be and keep testing the procedures. Resolve issues as they arise and document them.
With Sprinto
Sprinto makes quick work of control mapping, saving you from long manhours and manual processes. With Sprinto, you can automate the process of mapping controls.
Simply designate your production and non-production assets and specify the security criteria for each.
For example, you have the flexibility to exclude certain non-production assets from the audit scope with ease.
3. Conduct readiness assessment
You are almost there, we promise.
Readiness assessments give an idea of how prepared you are. All the documents, processes, and evidence you gathered will finally come to use. At this stage:
- The consultant reviews if your audit scope aligns with the controls
- They will also review your documents and evidence
- You get an idea of what the overall security posture looks like
- Gain insight into the existing gaps and work to fix them before the grand finale – your compliance audit
- The consulate communicates their observations and suggestions to your organization’s heads
Two ways to do it are to hire an external vendor or use internal resources.
With Sprinto, however, you can access a dashboard that displays your SOC 2 audit readiness as a percentage. This dashboard offers a detailed breakdown of passing, failing, critical checks, and pending tests. Also, it provides an entity-level overview, clarifying responsibilities.
4. Select an auditor to review and certify your reports
You finally did it. Phew!
Look for a reputed third-party auditor who has previously worked with organizations of similar size and complexity. Verify the reviews from various sources and ask questions about their process and approach. Your SOC 2 auditors will:
- Set a date to conduct the test
- Demand a list of evidence for your controls
- Test the processes, document them, and work on issues
- Create and deliver the final report
With Sprinto, you gain access to a network of experienced auditors tailored to your needs. Once the SOC 2 Type 1 audit is complete, you can publicly showcase the results using Sprinto’s Trust Center feature.
The Sprinto Trust Center offers a personalized and customizable portal where you can easily display policies, documents, reports, and other essential resources.
What’s more, you can integrate control information to show the real-time status of your selected security and privacy controls on your page. With just a few clicks, you can publish your certifications for the world to see.
Note: Please note that Sprinto does not directly associate itself with any auditors. Instead, it facilitates connecting you with relevant auditing professionals or firms.
SOC 2 Type 1 certification: How much does it cost?
The starting cost of SOC 2 type 1 certification typically begins at $7500 for audits covering up to 3 Trust Services Criteria (TSCs). If you require coverage for more than 3 TSCs, costs can rise to $25000.
Although it is tempting to save on the cost of auditors, the experience and credibility of the auditor you choose will be the most critical, especially when he or she has previously been involved with firms similar to yours.
The real cost of the Type 1 audit would eventually be determined by factors including the size and complexity of your organization, the organization’s chosen trust service criteria, and your organization’s existing controls; the level of audit chosen – and the auditor’s determination.
For instance, if you’re a large organization with limited security measures and opt for a consultant to facilitate SOC 2 certification, expenses could exceed $25,000 for a Type 1 report.
Sprinto SOC 2 Type 1 Cost
If you plan to obtain your SOC 2 Type 1 report quickly, Sprinto offers two ways to assist you.
- First, you can download a free SOC 2 checklist to kickstart your journey.
- Secondly, there’s the option of compliance automation. Sprinto streamlines compliance with SOC 2, ISO 27001, HIPAA, and more through digitization and automation. This accelerates the compliance process, ensuring year-round adherence rather than just during audits. Companies utilizing Sprinto for SOC 2 compliance save up to 80% in time, effort, and costs.
if you opt for compliance automation software like Sprinto and already have security controls in place, you could slash your expenses by 50-80%. For smaller organizations, Type 1 reports typically range from $5000 to $10000.
Why Sprinto? How can it help your organization achieve SOC 2 Type 1 compliance?
SOC 2 Type 1 certification means a ton of work and a lot of headaches. We know you would rather focus on your sales and customers.
“Sprinto integrates with everything that we use, and collects evidence automatically. Centralizing evidence in one place is critical for us, so it’s nice that Sprinto does this out-of-the-box.”~ Deepak Balasubramanyam, CTO at Rocketlane.
What if there was a super easy solution that took care of the boring and time-consuming tasks? Well, there is one. Meet our compliance automation platform that makes your life easier.
- Instead of manually looking for evidence of compliance and oversights, you get a continuous monitoring feature on Sprinto that keeps your compliance game on all the time.
- Instead of spending hundreds of hours looking for gaps and improvement areas and following up repeatedly with your staff for policy acknowledgments and whatnot, automate it all at the click of a button.
- Lost in piles of data and business processes? Sprinto lets you track every action, process, and issue from a centralized dashboard. You can automate workflows and create custom rules.
- Figuring out the nuances of compliance can burn you out for months. With Sprinto, you can do it in weeks.
Ready to fast-track SOC 2 Type 1? Book a demo with Sprinto
FAQs
What is SOC 2 Type 1?
SOC 2 Type 1 is an audit report where an independent CPA assesses whether an organization’s controls are properly designed to meet the Trust Services Criteria at a specific moment in time.
Who needs to be SOC 2 Type 1 compliant?
SaaS firms, companies that store sensitive customer information on the cloud, and cloud service providers can consider getting SOC 2 Type 1 compliant.
How much does it cost to become SOC 2 Types 1 compliant?
The cost of the SOC 2 compliance framework depends on factors like the type of attestation, audit scope, security tools, business size, and more. Typically, it should cost you $8000 – $30000. You can learn more about the cost structure of SOC 2 compliance here.
Is SOC 2 a requirement?
No, SOC 2 is not a must. Part of the choice to go for SOC 2 compliance is that it does not always come from specific regulations like HIPAA and PCI-DSS. For instance, when it comes to SaaS and cloud computing and, respectively, IT-managed service providers, they demonstrate their dedication to information protection through SOC 2.
Who are SOC 2 audits designed for?
SOC 2 audits are designed for companies offering client entities services and systems. Examples include cloud service providers, software developers, web marketing firms, and financial services companies.
Author
Anwita
Anwita is a cybersecurity enthusiast and veteran blogger all rolled into one. Her love for everything cybersecurity started her journey into the world compliance. With multiple certifications on cybersecurity under her belt, she aims to simplify complex security related topics for all audiences. She loves to read nonfiction, listen to progressive rock, and watches sitcoms on the weekends.Explore more SOC 2 articles
SOC 2 Compliance Overview
SOC 2 Preparation and Documentation
SOC 2 Audit and
Reporting
SOC 2 Differences and Similarities
SOC 2 Updates & Management
SOC 2 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.