SOC 2 compliance is as much about securing your information assets as it is about maintaining documentation of the same.
Good documentation isn’t just a checkbox exercise in compliance. It standardizes processes and allows organizations to scale their operations safely while ensuring the implementation of sound security practices.
So even though maintaining documentation can seem like a drag, it helps reduce risk, ensures safe operations, and cultivates a strong security culture within companies. And no matter how tedious the task may seem, these goals should always remain a priority!
In this article, we dive deep into SOC 2 compliance documentation, its requirements, and how companies can ensure long-term success with the right documentation.
What is SOC 2 documentation?
SOC 2 documentation refers to the documentation of policies, procedures, and reports that demonstrate compliance with the SOC 2 standard. This is especially helpful during the SOC 2 audit stage, where the auditor has a clear view of all your procedures and policies and their compliance with the TSCs chosen for evaluation.
SOC 2 documentation is the tangible proof of your implemented policies, procedures and other internal controls in relation to the five Trust Services Criteria (TSC) of SOC 2. It also includes other documentation requirements, such as system description, management assertion, risk assessments, and more.
Your documentation should include a detailed assessment of your security controls – from authentication measures to technical testing – and evidence that all systems have been properly updated and configured with the latest patches.
This information should be provided in an organized way that will enable your auditor to validate the accuracy and relevancy of the documents in relation to the audit objectives.
This means that your procedures and processes should be clearly outlined, with regular checks for weaknesses or outdated components within each component reviewed during the audit process.
Note: If you are curious about the controls to include in your detailed assessment, we have a resource for you. Our experts have curated a list of SOC 2 controls to help you with your compliance.
Download Your SOC 2 Controls List
For instance, you must keep collecting evidence through screenshots, logs, docs, tickets, and paperwork to become SOC 2 compliant.
By providing comprehensive documentation, you can ensure that when subjected to a SOC 2 audit, there will be no surprise risks lurking or outdated protocols neglected.
Remember that SOC 2 isn’t a set of hard and fast rules; instead, it is a framework that properties the five TSCs – security, availability, processing integrity, confidentiality, and privacy. And documentation is the best way to achieve it.
It demonstrates that your organization follows security best practices around protecting and managing customer data. As a result of completing SOC 2 documentation, you can demonstrate to customers and business partners your undivided commitment to responsible data management.
Completing the SOC 2 document also provides third-party verification for IT systems and software development processes, giving your users confidence that your company will handle their information responsibly.
A comprehensive and updated SOC 2 documentation is key to an organization clearing the audit without any exceptions. Therefore, getting your SOC 2 documentation in order is never too early.
To see how this works in action, read about how Fyle received their SOC 2 type 1 with zero auditor intervention, as all the document collection was automated.
Why is SOC 2 documentation important?
SOC 2 documentation provides proof that you comply with the established protocol parameters for secure data access and storage per the framework requirements.
The SOC 2 documentation helps define policies and handle any gaps found during inspections or audits within a specific period. The list of documents that you provide will enhance your chances of completing the audit.

These documents that serve as evidence will allow the auditor to conduct the audit efficiently. This way, auditors will have a better understanding of your business operations, systems, and infrastructure.
Ultimately, preparing for SOC 2 documentation demonstrates an organization’s commitment to ensuring security measures are being appropriately implemented and kept up-to-date to protect customers’ sensitive information at all times.
Find out how to automate SOC 2 documentation process. Talk to our experts
What kind of documentation is required for SOC 2?

The documentation required for SOC 2 depends on which TSC you want to include in your audit. Here’s the list of TSCs your documentation should be based upon:
Security: Provide an attestation of data protection controls to avoid unauthorized access.
Availability: Here, the documentation must include reasonable information about security controls that ensures that the service is available and access controls are being implemented.
Processing integrity: The documentation must provide authentication that all transactions are processed promptly and accurately.
Confidentiality: You must show that all private or confidential data is protected according to the security policies in the organization’s service agreement.
Privacy: The documentation must show that the personal information is handled according to the relevant privacy regulations or controls specified in the privacy notices.
Here is the list of document types that you need to prepare before the auditor comes to audit your SOC 2 compliance:
Management Assertion
The management assertion is essential for any organization as it sets the expectations for your audit. It gives an overview of the systems, controls, and processes in place, assisting the auditor in comprehending your organization’s infrastructure.
It’s your way of saying, “these are our controls, these are systems, and this is what we are doing right now.”
The document should contain information on areas such as:
- Operational objectives
- Internal control processes
- System security requirements
- Physical security arrangements
When you provide detailed information on the practices and operations through the management assertion document, an organization can significantly facilitate the audit process and ensure that it meets all of its obligations as efficiently as possible.
It might be the shortest document and seem redundant, but it serves as the basis between your company and the auditor. Moreover, the management assertion is a part of your main SOC 2 report. This section summarizes the organization’s services, structures, products, systems and controls. It, however, doesn’t contain any technical details.
Minimize the error in documentation by automating the entire process. Take an expert’s advice
Complementary user entity controls
Complementary user entity controls refer to the SOC 2 controls you expect one of your service providers to perform. Even though a third-party entity may perform them, they are still relevant and applicable to your system.
For instance, if one of your third-party service providers fails to back up their system, it could still affect your system.
If a SOC 2 audit report does not have CUECs, it is important to know that this means the report is unfinished. This will cause an inadequate or flawed audit at the user organization’s end.
Recommended: List of SOC tools
Technical security documents
Ensuring the security of your organization’s network and data is of utmost importance. Technical security documents provide a complete set of records that can be used to monitor and manage any changes made to the network infrastructure.
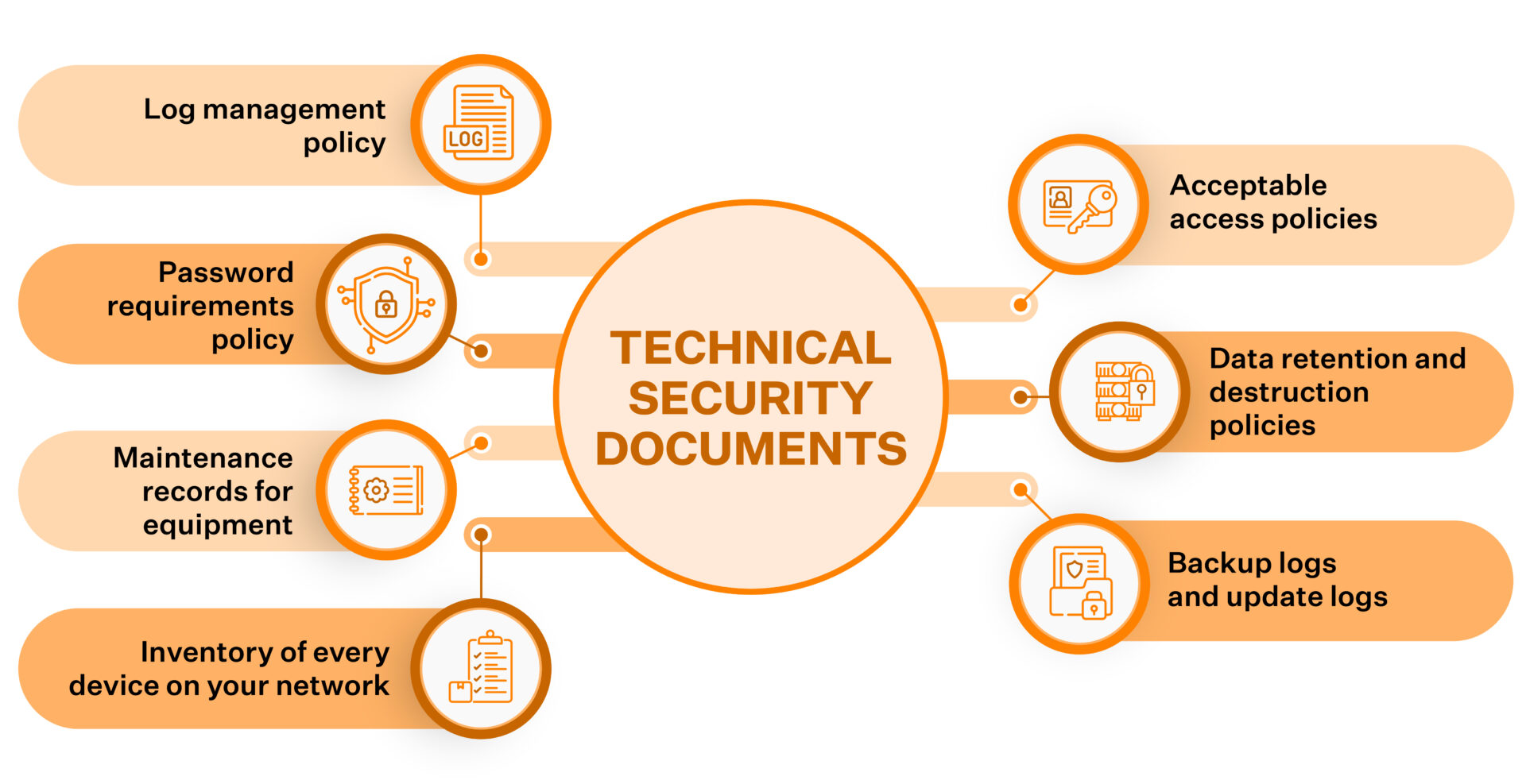
This includes:
- Log management policy
- Password requirements policy
- Maintenance records for equipment
- Inventory of every device on your network
- Acceptable access policies
- Data retention and destruction policies
- Backup logs and update logs
All these documents must be carefully monitored to maintain the organization’s highest physical and digital security standards. With the necessary technical security documents in place and efficient measures for monitoring them regularly, your documentation process will be in place.
Fastrack your SOC 2 evidence collection
Operational Documents
Maintaining operational documents is important in complying with industry regulations and providing a secure environment for customers, employees, and vendors.
Here is what operational documents constitute:
- Diagram of your physical office
- Corporate governance manual
- Risk management plan
- Compliance program budget
- Vendor agreements
- Business continuity and incident response plans
Adherence to these operational documents is critical for ensuring business continuity, strong security practices, commitment to standards, and overall customer satisfaction.
Human Resource Documentation
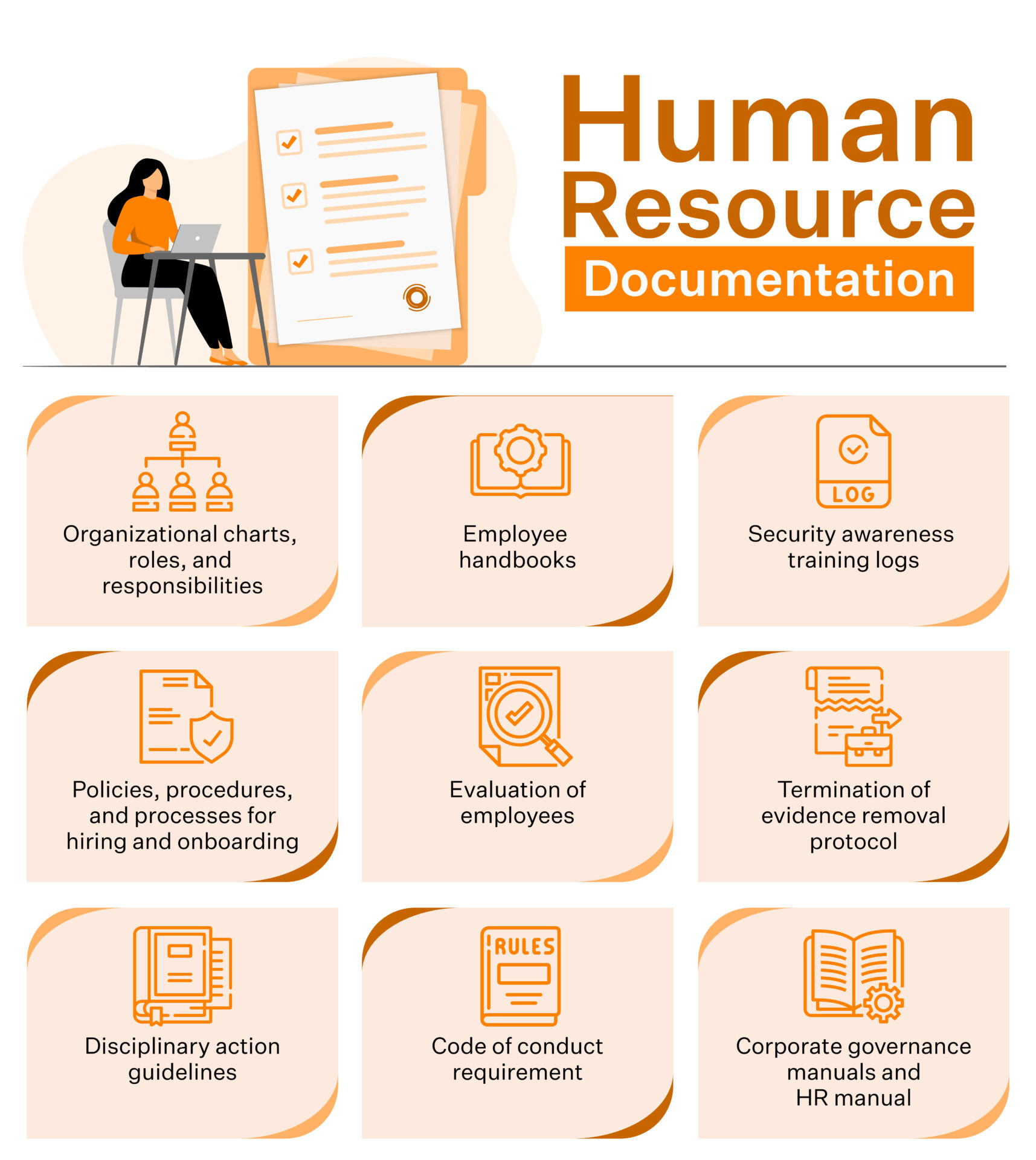
An effective human resources team is critical to any company’s success, and the collection of SOC 2 documents is central to that success. These documents record several essential items related to maintaining a compliant and secure work environment, such as:
- Organizational charts, roles, and responsibilities
- Employee handbooks
- Security awareness training logs
- Policies, procedures, and processes for hiring and onboarding
- Evaluation of employees
- Termination of evidence removal protocol
- Disciplinary action guidelines
- Code of conduct requirements
- Corporate governance manuals and HR manual
The attention given to SOC 2 documents reflects an organization’s dedication to creating a safe working environment with clear lines of authority and sound procedures for protecting company assets.
Collecting all this evidence involves a lot of manual, repetitive, error-prone work.
A typical company takes around three-six months to implement its SOC 2 program. Moreover, you must spend 600-800 hours per year operating the program and one-two months of back-and-forth with the auditor. You can cut this short by automating your SOC 2 compliance journey.
Using compliance automation platforms such as Sprinto can help you bring down the time to SOC 2 significantly and at competitive costs. Sprinto is designed explicitly for cloud-hosted SaaS companies, and makes it fairly simple to monitor and collect evidence as everything is continuously maintained online. Maintaining and updating your SOC 2 documentation is easier with Spinto.
Plan your compliance budget:
Want to learn how to budget for compliance? Use our cost calculator to estimate your expenses accurately and get insights into the financials of your compliance journey.
Privacy and Compliance Documentation
Privacy documents are essential to determine how your organization protects customer information. Here are some of the privacy documents you need to provide during the audit:
- Notice of privacy practices
- Unsubscribe and opt-out policies
- Data use agreement
- Confidentiality policy
Compliance documentation also includes submission of records of your previous compliances. self-assessment questionnaires, risk assessments, and penetration testing results are also included here.
Third-party and vendor contracts
It is not enough that you trust your vendors to manage your data securely, you must document why you think so. The auditor will want to see proper documentation outlining your third-party contracts’ safety procedures.
This includes the use of:
- Service Level Agreements (SLAs) designed to guarantee the responsiveness and quality of service from vendors
- Additional Vendor & Third Party Contracts like Non-Disclosure Agreements may be used to tailor specific scenarios based on an organization’s needs.
Also, check out: SOC 2 report examples
How to prepare SOC 2 documentation (Step-by-step)?
We know that SOC 2 compliance is arduous, but with Sprinto, you don’t need to worry about your documentation process not working in alignment. Here is how you can prepare before the auditor arrives to weigh against the auditing standards.
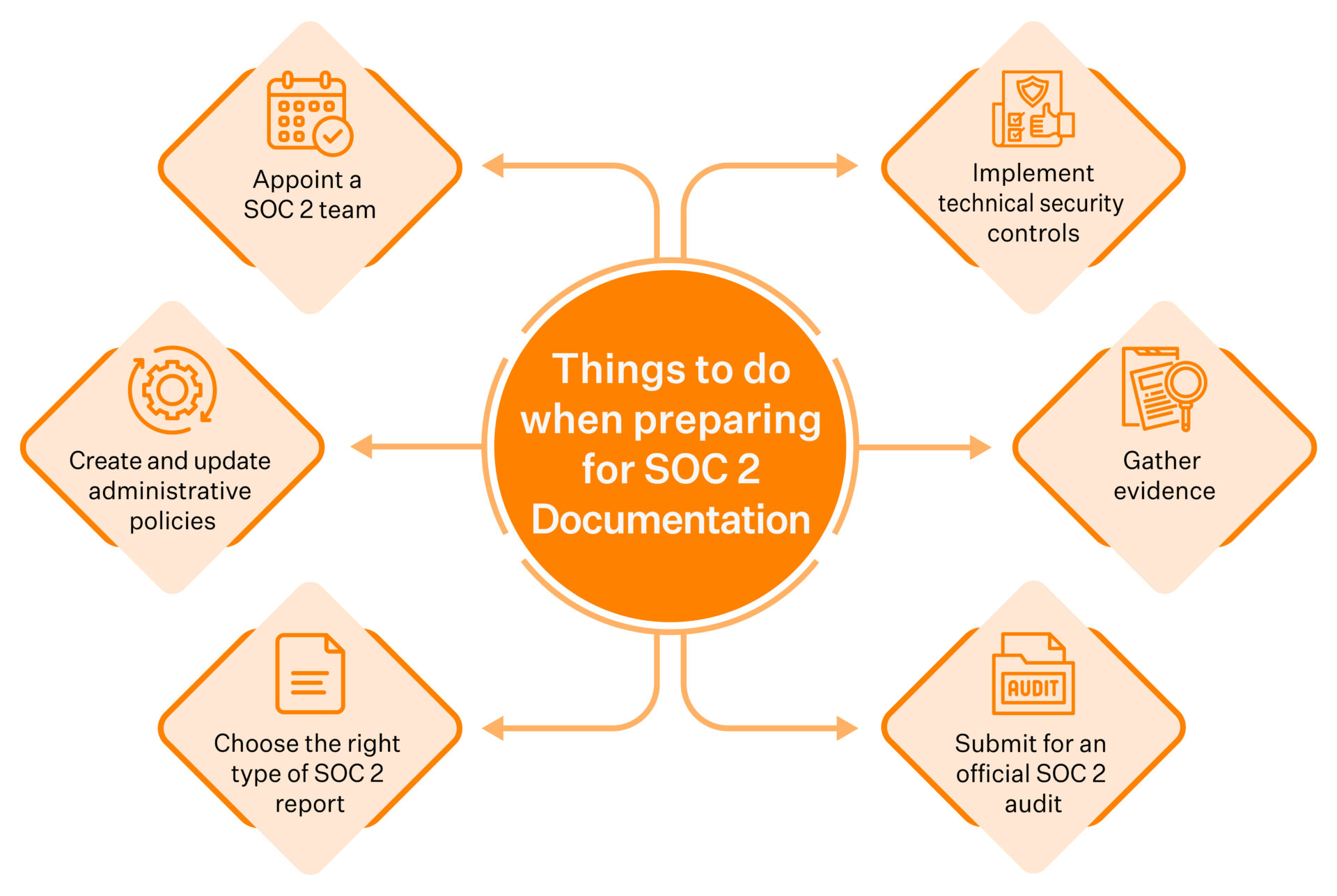
Step 1: Appoint a SOC 2 team
Building a strong compliance team before your documentation process can help avoid potential issues. This includes identifying all the necessary roles and which employees of your organization would fill them best.
Identifying people with relevant technical knowledge and who are well-versed in security operations and management is essential.
For example, you can appoint an engineering team member to take care of documents related to security requirements because they have the most knowledge about them.
The roles may include:
- Project manager to coordinate with the SOC 2 processes and fellow team members.
- Legal personnel are necessary to get inputs for creating contracts and updating documentation throughout the SOC 2 process.
- Having one primary author for all reports will help to ensure that communication runs smoothly.
- IT/Security teams to take up the brunt of the SOC 2 work and update any changes that come out of the process.
- People ops team to manage infosec training to staff, background checks and take care of hiring evaluation requirements.
Additionally, team members should be collaborative and demonstrate an aptitude for troubleshooting as issues arise while they review existing procedures or implement new standards.
Also, check out: How to get SOC 2 for startups
Step 2: Choose the type of SOC 2 report
Before taking the necessary steps to earn SOC 2 documentation, it’s important to ask yourself these important questions:
- What type of SOC 2 report do you need? SOC 2 Type 1 or SOC 2 Type 2?
- Do you need an attestation for one service or your entire organization?
Answering these key questions early on can provide clarity throughout the process and pave the way toward achieving such an acclaimed attestation. When clear expectations are set, collecting information and making progress toward a successful SOC 2 attestation is easier than ever.
Also check out: Guide to SOC 2 Type II certification
Step 3: Create and update administrative policies
Writing and revising administrative policies is challenging, but it’s an important part of creating a strong security program. When you’re drafting them, make sure they are easy to read and understand – the purpose of a policy is not to tie people up in technicalities; it should provide clear guidance on the steps that need to be taken to ensure security.
Your security policies should detail how the security controls are implemented in your overall infrastructure and define the steps to manage them too. Here are some of the things you need to outline:
- System access with security protocol specifying how and when users can access sensitive data
- Disaster recovery to develop protocols for how to best back-up data and recover from disasters.
- Risk assessment to understand how the organization deals with security concerns, we must explore how they are identified and dealt with.
- Incident response that defines the process for reporting, investigating, and resolving security incidents.
- Security roles to determine how to best assign security and staff roles and responsibilities based on organizational needs.
- Creating a training program for your organization to improve security awareness
Now your team can share the up-to-date information with the SOC 2 auditor without hiccups!
Sprinto offers editable template policies for you to pick and choose what information you need to submit to the auditor.

Sprinto’s auditor-friendly dashboard presents all your documentation and evidence to the auditor in the format they typically work with, drastically cutting down the back-and-forth emails between you two.
Step 4: Implement technical security controls
After your team has set up administrative security policies, you must ensure that technical security controls are in place throughout your applications and infrastructure. Your team should match your policies by implementing cloud security controls.
There are several security control solutions that you should explore, including:
- Access Control
- Firewall and Networking
- Vulnerability Scanning
- Intrusion Detection Systems (IDS)
- Encryption
- Backup
- Audit Logging
Step 5: Gather Evidence
Before scheduling a SOC 2 audit, you should gather all relevant documentation, evidence, and policies. This will streamline the entire audit process for your company. Additionally, you must gather the following documents:
- Infrastructure Certifications – Collect any documents related to cloud infrastructure, including but not limited to agreements, certifications, and attestations. An example of such a document is an SLA.
- Administrative Security Policies – Your security program must have all the right administrative policies. Collect and provide them.
- Technical Security Control Documentation – Gather any records or documentation demonstrating the implementation and management of infrastructure security controls.
- Third-Party and Vendor Contracts – Collect all documentation associated with third-party companies, contractors, and service providers.
- Risk Assessment – Attach any relevant documents from past security assessments or third-party audits.
Step 6: Submit for an official SOC 2 audit
After your team has crafted your security program and is ready for a SOC 2 assessment, it is time to partner with a credible auditor.
You should look for an auditor or firm with expertise in conducting SOC 2 audits for similar-sized companies as yours and the know-how to provide a smooth SOC 2 audit process. Note that only AICPA-certified public accountants must only carry out these audits.
Automating SOC 2 documentation with Sprinto
When it comes to the SOC 2 audit process, it’s not enough to practice the requirements of SOC 2 anymore. You must demonstrate compliance with clear evidence with documents, agreements, logs, and screenshots. However, collecting these pieces of evidence and putting them together need not be your worry anymore!
With Sprinto, you can become SOC 2 compliant without the hassle of maintaining multiple folders for screenshots, evidence, and spreadsheets. Sprinto packs in a 24×7 real time continuous monitoring system that alerts you when checks are due or in cases of non-compliance. In short, Sprinto automates all the tedious,time-consuming, and repeatable processes.
Here’s how you can automate documentation in Sprinto way:
- Access the Sprinto dashboard and go to the evidence upload section
- Click on the option to upload evidence, screenshots, or documentation
- Select the files or documents you want to upload from your computer or cloud storage
- Add any necessary descriptions or notes to provide context for the evidence
- If needed, create a new custom process for manual reviews by specifying the details and requirements
- Set up periodic processes by defining the frequency and timeline for uploading evidence
- Sprinto will alert you when it’s time to upload evidence for periodic processes
In short, Sprinto automates all the tedious, time-consuming, and repeatable processes.
Maintaining, updating, and reviewing your SOC 2 documentation is now easier with Sprinto. It’s because the automated workflow facilitates documentation and evidence collection.
Talk to our team today to know more about how Spinto can help you sail through not just your SOC 2 documentation but even SOC 2 attestation in a breeze.
FAQs
SOC 2 documentation refers to the set of policies, procedures, and evidence that demonstrate your organization’s compliance with the SOC 2 framework. It outlines how you manage customer data securely in line with the Trust Services Criteria, security, availability, processing integrity, confidentiality, and privacy.
Evidence typically includes security policies, system configurations, access logs, employee training records, risk assessments, and incident response plans. These materials help auditors verify that your controls are designed and operating effectively.
The SOC 2 documentation should be reviewed and updated regularly—ideally quarterly or whenever major system, policy, or personnel changes occur—to ensure ongoing compliance.
Typically, the compliance or information security team oversees SOC 2 documentation, collaborating with IT, HR, and management to ensure all evidence and policies remain accurate and up to date.
Documentation should be retained for at least the duration of the audit cycle (usually one year) and longer if required by regulatory or contractual obligations.
Author
Meeba Gracy
Meeba, an ISC2-certified cybersecurity specialist, passionately decodes and delivers impactful content on compliance and complex digital security matters. Adept at transforming intricate concepts into accessible insights, she’s committed to enlightening readers. Off the clock, she can be found with her nose in the latest thriller novel or exploring new haunts in the city.Explore more SOC 2 articles
SOC 2 Compliance Overview
SOC 2 Preparation and Documentation
SOC 2 Audit and
Reporting
SOC 2 Differences and Similarities
SOC 2 Updates & Management
SOC 2 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.











