TL;DR
| SOC 2 helps service organizations prove they protect customer data by meeting the AICPA’s Trust Services Criteria. |
| The five Trust Services Criteria, Security, Availability, Processing Integrity, Confidentiality, and Privacy, define the control areas auditors evaluate. |
| SOC 2 Type I assesses control design at a point in time, while Type II verifies control effectiveness over a defined observation period. |
| Implementing SOC 2 requires structured scoping, gap assessment, control implementation, continuous evidence collection, and independent audit validation. |
The SOC 2 framework is a voluntary compliance standard developed by the AICPA that helps service organizations demonstrate their commitment to protecting customer data. Built around five Trust Services Criteria, it has become a market expectation for SaaS providers and cloud-based businesses. This guide covers everything from understanding the framework’s core components to implementing the controls necessary for audit readiness.
Data breaches are so common these days that you no longer see them as breaking news.
IBM’s 2025 report puts the average breach cost at $4.44 million, with customers’ personal information caught in the crosshairs 53% of the time. These numbers are proof of why organizations that work with sensitive data need robust security frameworks.
That’s what SOC 2 is for. But ditch the mental image of rigid, crushing compliance checklists. Unlike other regulations that dictate exactly which firewalls you must buy, SOC 2 is flexible; you design security that fits your environment, then prove it works.

What is the SOC 2 framework?
The SOC 2 framework is a voluntary compliance standard created by the American Institute of Certified Public Accountants (AICPA). It’s designed to help service organizations demonstrate how they protect customer data. Before I begin, here’s some history.
First introduced in 2010, the framework brings a modern approach to data security practices that the older SAS 70 standards could not address. (Statement on Auditing Standards No. 70 were an auditing standard developed by the American Institute of Certified Public Accountants. Its purpose was narrow and specific. It allowed service organizations to demonstrate how their internal controls affected a customer’s financial reporting.)
SOC 2 compliance assesses whether an organization’s internal controls meet the AICPA’s Trust Services Criteria across five key areas: Security, Availability, Processing Integrity, Confidentiality and Privacy.
What’s unique about SOC 2 is that rather than dictating specific technologies or processes, it establishes principles that organizations must satisfy through their own tailored controls.
A SOC 2 audit is conducted by an independent CPA firm that evaluates whether an organization’s security practices align with the selected Trust Services Criteria. The resulting report acts as a third-party verification that your information security program meets recognized standards. This independent attestation carries a heavy weight with customers, partners and regulators who need assurance that their data is in safe hands.
Why is the SOC 2 framework necessary for organizations?
Third-party breaches have doubled to 30% of all incidents according to Verizon’s 2025 Data Breach Investigations Report. That means your customers are scrutinizing their vendors’ security practices before signing contracts. On the same note, here are four reasons why SOC 2 is important:
1. It builds trust in a security-conscious market
78% of enterprise clients now require SOC 2 Type II certification from their service providers. This means that without a SOC 2 report, you are locked out of lucrative deals simply because you cannot demonstrate your security posture to prospective customers.
And on top of that, the trust benefits go a long way.
A SOC 2 report tells all stakeholders, including investors, partners, and employees, that your organization works with transparency and accountability.
2. It reduces risk and strengthens your security posture
The process of achieving SOC 2 certification naturally strengthens your organization’s security foundation.
As you document policies, implement controls, and establish monitoring mechanisms, you also create a more resilient operational environment. In fact, data from the Ponemon Institute found that organizations with SOC 2 Type II certification experience 57% fewer data breaches compared to those without formal security attestations.
Now, that’s a number you cannot just ignore.
And beyond breach prevention, SOC 2 compliance helps you identify vulnerabilities before attackers can exploit them. SOC 2 requires regular risk assessments and continuous monitoring. For organizations wanting to formalize their monitoring program, our NIST 800-137 continuous monitoring guide covers the ISCM implementation process across all three organizational tiers.
3. It accelerates your sales cycles and reduces friction
You might have noticed that security reviews have become a standard part of the procurement process, particularly for B2B software purchases.
Vendor risk assessments can take up a lot of time from your IT teams. Having a current SOC 2 report reduces this friction by providing pre-validated answers to most security questionnaire items.
Organizations with formal trust documentation can save time spent manually filling out security questionnaires. This efficiency gain spills directly to faster deal closures and shorter sales cycles. This in itself is a big competitive advantage that compounds over time as your reputation for security excellence spreads through your target market.
4. It helps you meet regulations and standards
While SOC 2 itself is voluntary, it often satisfies requirements imposed by other regulations. The framework overlaps significantly with GDPR, HIPAA, ISO 27001, and other compliance standards.
Organizations pursuing SOC 2 frequently discover they have completed much of the groundwork needed for additional certifications, making it an efficient foundation for broader compliance programs.
Many enterprise contracts now explicitly require SOC 2 attestation as a condition of doing business. In regulated industries like healthcare and financial services, vendors without proper security certifications face immediate disqualification from procurement processes.

What are the five Trust Services Criteria (TSC)?
The Trust Services Criteria form the pillars of the SOC 2 framework.
These five categories are developed by none other than the AICPA itself, and they define the specific areas auditors evaluate when assessing an organization’s controls.

1. Security (mandatory)
Security is the only mandatory criterion for every SOC 2 audit and is the basis upon which all other criteria are built. It addresses how your organization protects systems and data from unauthorized access, cyberattacks, and other threats.
Security criteria cover access management, vulnerability management, and incident response. For ISO 27001 specifically, our guide to vulnerability management under ISO 27001 covers the Annex A controls, scanning requirements, and risk response strategies that ISMS auditors evaluate. Auditors will examine whether you have implemented appropriate safeguards such as multi-factor authentication, encryption protocols, intrusion detection systems, and formal policies governing user access.
Key security controls typically include
- Access controls with role-based permissions and regular access reviews
- Network security through firewalls, segmentation, and monitoring
- Data encryption for information at rest and in transit
- Incident response procedures with documented escalation paths
- Vulnerability scanning and penetration testing programs
Because security controls all other criteria, you cannot receive a SOC 2 report without satisfying its requirements. Even if your audit scope excludes availability or privacy, you must demonstrate strong security controls.
2. Availability (optional)
Availability evaluates whether your systems remain operational and accessible when customers need them. Organizations that promise high uptime or offer mission-critical services should strongly consider including this criterion in their audit scope.
Demonstrating availability requires documented business continuity plans, disaster recovery procedures, and capacity management processes. Auditors will look for evidence that you monitor system performance, maintain redundant infrastructure, and can restore services within defined recovery time objectives.
For SaaS providers whose value proposition depends on reliability, the availability criterion provides formal validation of operational resilience. It shows customers that you have planned for outages and tested your ability to recover from disruptions.
3. Processing integrity (optional)
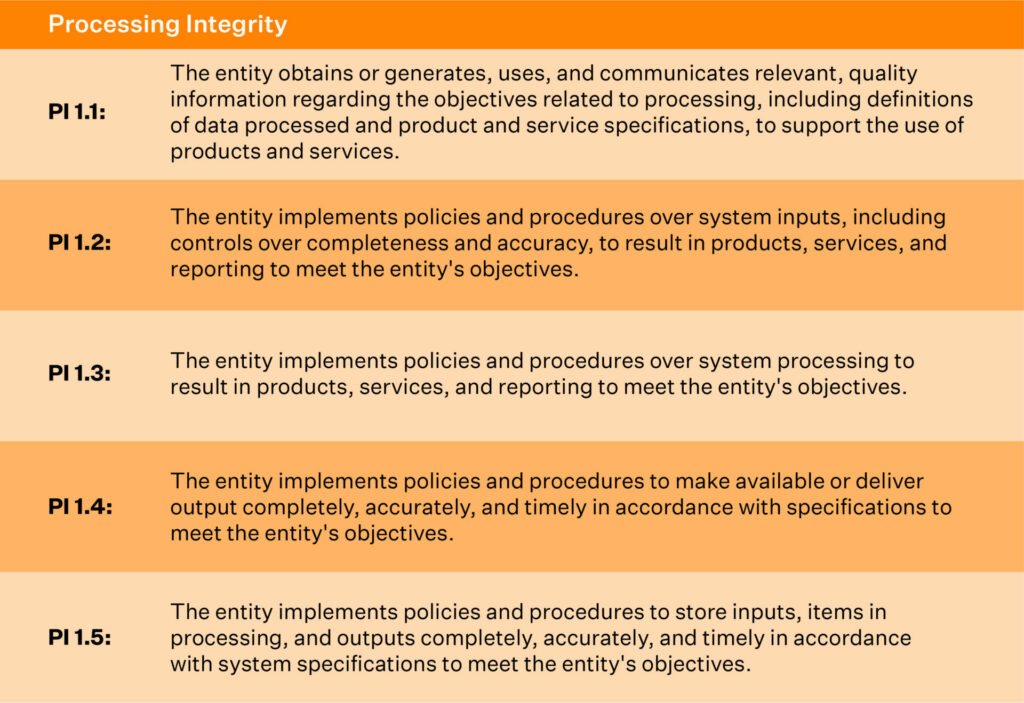
Processing integrity addresses whether your systems process data accurately, completely, and in a timely manner. This is relevant for organizations that transform, calculate, or deliver real-time data as part of their core services.
Organizations handling financial transactions, analytics platforms, or automated decision-making systems should consider processing integrity. Auditors evaluate controls such as input validation, reconciliation procedures, quality assurance processes and error handling mechanisms.
The goal is to demonstrate that data flowing through your systems arrives at its destination without corruption, loss or unauthorized modification. This assurance can be decisive for customers who depend on your outputs for critical business decisions.
4. Confidentiality (optional)
Confidentiality focuses on protecting sensitive business information from unauthorized disclosure. The 2024 SOC Benchmark Study by CBIZ found that 64.4% of SOC 2 reports now include confidentiality as an in-scope category, up from 34% in 2023.
This criterion applies to non-personal sensitive data such as intellectual property, financial records, strategic plans and proprietary algorithms. Organizations must show controls for data classification, encryption, secure disposal and access restrictions that limit exposure to authorized personnel only.
The sharp increase in the adoption of confidentiality reflects growing awareness that protecting business-sensitive information is as important as protecting personal data. Organizations working with trade secrets or regulated business information benefit significantly from this criterion.
5. Privacy (optional)
Privacy is responsible for how organizations collect, use, retain, disclose, and dispose of personal information. It needs alignment with your published privacy policy and applicable privacy regulations.
For businesses that have to handle huge amounts of consumer data, particularly in B2C contexts, the privacy criterion shows compliance with principles like consent management, data minimization and individual access rights.
Controls typically include privacy notices, opt-out mechanisms, and secure deletion processes.
Organizations subject to GDPR or similar privacy regulations often find that the privacy criterion helps satisfy overlapping requirements. Including it in your SOC 2 scope signals to customers that you treat their personal information with appropriate care.
Also check out this video for a detailed SOC 2 Checklist
SOC 2 Type I vs Type II: What’s the difference?
SOC 2 audits result in one of two report types. The choice between Type I and Type II affects your timeline, evidence requirements, and the level of assurance you can provide to customers.
A SOC 2 Type I report evaluates whether your controls are properly designed and implemented at a specific moment. It captures your security posture on the audit date, but does not assess whether those controls operate effectively over time.
A SOC 2 Type II report goes further by checking how well your controls work over an observation period, typically three to twelve months. Auditors sample evidence throughout this window to verify that controls functioned as intended day after day.
| Aspect | SOC 2 Type I | SOC 2 Type II |
| Definition | Evaluates the design of controls at a specific point in time | Evaluates the design and operating effectiveness of controls over a period of time |
| Time period | Point-in-time assessment (single date) | Minimum 6-month observation period (typically 6-12 months) |
| What it tests | Whether controls are suitably designed to meet the Trust Services Criteria | Whether controls operate effectively and consistently over time |
| Assurance level | Moderate; confirms controls exist and are documented | Higher; confirms controls actually work and are followed consistently |
| Typical duration | 2-4 weeks to complete | 4-12 months (including observation period and audit time) |
| Cost | Lower | Higher |
| Report validity | Becomes outdated quickly as systems change | More durable (covers historical performance period) |
| Use cases | Early-stage startupsFirst-time SOC 2Quick sales requirementInternal assessment | Enterprise customersRegulatory requirementsLong-term vendor relationshipsAnnual compliance maintenance |
| Evidence required | Policies, procedures, system configurations, screenshots | Historical logs, tickets, access reviews, change management records, metric data over time |
| Customer recognition | Generally accepted for initial vendor assessments | Preferred or required by enterprise procurement teams |
Which report type should you choose?
Starting with Type I often makes more sense for organizations new to SOC 2. It establishes your baseline, identifies gaps requiring remediation and provides a reportable milestone while you build toward operational maturity. Many companies pursue Type I first and then transition to Type II within the following year. Working through a clear plan on how to prepare for SOC 2 audit at the Type I stage usually saves considerable rework later, since the controls scoped and documented for Type I become the same controls auditors expect to see operating consistently across the Type II observation period.
That said, mid-market and enterprise buyers almost universally prefer SOC 2 Type II reports because they provide meaningful assurance about ongoing operations. Plan your roadmap to reach Type II as quickly as feasible if your sales pipeline includes security-conscious customers or regulated industries.
The good news is that much of the work overlaps. Controls implemented for Type I carry forward to Type II; you simply need to operate them consistently and collect evidence throughout the observation period.
Working with an autonomous trust platform will massively reduce the operational burden of maintaining continuous compliance.

Key components of the SOC 2 framework
You need to understand the major building blocks of SOC 2 to implement it in your organization. Each component I have discussed below plays a specific role in your overall compliance program.
1. Policies and procedures
SOC 2 policies establish the rules and expectations that govern how your organization handles data security. Auditors will review these documents to verify that you have formally defined your approach to access management, incident response, change control, vendor oversight and other critical areas.
2. Technical controls
While policies describe what should happen, technical controls make it happen through system configurations, automated enforcement and monitoring mechanisms. These controls translate policy requirements into operational reality.
Common technical controls include:
- Access management: Single sign-on, multi-factor authentication, role-based permissions
- Encryption: TLS for data in transit, AES-256 for data at rest
- Monitoring: SIEM platforms, intrusion detection, log aggregation
- Vulnerability management: Automated scanning, patch management, penetration testing
- Endpoint protection: Antivirus, EDR solutions, mobile device management
The specific controls you implement will depend on your technology stack, risk profile and audit scope. The framework does not mandate particular tools, it requires demonstrating that your chosen controls effectively address the relevant Trust Services Criteria.
3. Risk assessment and management
Risk assessment is a recurring requirement throughout the SOC 2 framework. Organizations must identify potential threats, evaluate their likelihood and impact, and implement appropriate mitigations. This process cannot be a one-time exercise; auditors expect to see evidence of ongoing risk management.
A comprehensive risk management program considers risks from multiple sources including technology vulnerabilities, vendor relationships, employee actions and environmental factors. Each identified risk should be documented, scored and linked to specific controls that reduce exposure.
4. Evidence collection and documentation
Auditors do not accept verbal assurances; they need documented evidence that controls exist and operate effectively. This evidence takes many forms including system configurations, access logs, policy acknowledgments, training records and security scan results.
For Type II audits, evidence must demonstrate consistent control operation throughout the observation period. This means collecting and organizing documentation continuously rather than scrambling before the audit. Automated evidence collection has become essential for organizations seeking to manage this burden efficiently.
5. Vendor management
Modern organizations rely heavily on third-party services, from cloud infrastructure to payroll processing. The SOC 2 framework requires demonstrating that you understand and manage the risks these relationships introduce.
Vendor management controls typically include due diligence assessments before onboarding, contractual security requirements, ongoing monitoring and periodic reassessment of critical vendors. Auditors want to see that you have visibility into your supply chain and processes for addressing vendor-related risks.

How to implement the SOC 2 framework?
Getting SOC 2 compliant follows a predictable path from scoping to audit. Here’s how to move through it without losing momentum.
Step 1: Define your scope and objectives
Start by figuring out what you’re actually auditing. Map out which systems touch customer data, identify the services your customers care most about, and decide which Trust Services Criteria apply to your business.
Most companies start with Security (it’s mandatory anyway) and add Availability if they make uptime promises. Include Processing Integrity, Confidentiality or Privacy based on what you’ve committed to contractually or what your customers expect.
Keep your first scope tight. You can expand later as your program matures; an overly ambitious scope just drags out timelines and inflates costs.
Step 2: Conduct a gap assessment
Now compare where you stand against SOC 2 requirements. This readiness assessment shows you exactly what’s missing.
Walk through your policies, technical controls, processes and documentation. For each area, ask: Does a control exist? Is it working? Can you prove it?
Document every gap with enough detail to act on it, which criterion it affects, how risky it is, how much effort it takes to fix and who owns it. Finding gaps now beats finding them during the audit.
Step 3: Develop a remediation plan
Turn your gap list into a project plan. Assign owners, set deadlines and define what “done” looks like for each item.
Prioritize based on audit impact:
- Critical gaps that could fail the audit go first
- Related items get grouped together (one IAM solution might close five gaps at once)
- Dependencies get sequenced properly; some controls need policies written before you can implement them technically
Remember that SOC 2 isn’t just an IT project. You’ll need buy-in from HR, legal and leadership throughout.
Step 4: Implement controls and collect evidence
For each control, build procedures your team can follow consistently and configure systems to enforce requirements automatically wherever possible.
Set up evidence collection at the same time. Figure out what auditors will need and start capturing it now, manual collection doesn’t scale, so automate what you can.
If you’re going for Type II, your observation period starts once controls are running. Make sure your monitoring is working before the clock begins.
Step 5: Prepare for and execute the audit
When your observation period ends (Type II) or your controls are in place (Type I), shift into audit prep. Review your evidence for completeness, close any remaining gaps and organize everything for easy auditor access.
Pick a qualified SOC 2 auditor, an independent CPA firm with relevant experience. Share your scope and documentation upfront and agree on how you’ll communicate during the engagement.
Review the draft report carefully before it’s finalized. Address any exceptions through fixes or management responses. Once issued, your SOC 2 report becomes a powerful trust signal for customers and partners.

Common SOC 2 controls you’ll need to implement
SOC 2 doesn’t hand you a checklist, but certain controls show up in nearly every audit. Here’s what to expect.
1. Access management controls
You need to prove that only the right people can reach your systems. That means solid authentication, clear authorization rules and regular reviews.
Focus on
- Multi-factor authentication for production access
- Single sign-on to centralize identity management
- Role-based permissions following least-privilege principles
- Quarterly access reviews to catch stale permissions
- Fast offboarding when employees leave
Auditors pay close attention here. Weak access controls create risk across your entire environment.
2. Change management controls
Change management governs how code and configurations move into production. Done right, it prevents untested changes from introducing vulnerabilities.
Processes should include formal change requests, role separation, testing, and complete audit trails. For a deep dive into audit log implementation best practices – from what to track to how to analyze log data – see our comprehensive guide. If you run CI/CD pipelines, build approval gates directly into the workflow.
3. Incident response controls
Security incidents happen. What matters is whether you can detect, respond to and recover from them effectively.
Auditors want to see
- Detection mechanisms that catch incidents quickly
- Documented response procedures with clear escalation paths
- Communication plans for internal teams and external stakeholders
- Post-incident reviews that prevent recurrence
- Regular testing through tabletop exercises
Having an incident response plan isn’t enough; you need to prove you’ve tested it and your team knows what to do.
4. Business continuity and disaster recovery controls
If Availability is in your scope, you’ll need controls for maintaining operations during disruptions.
Document your recovery time objectives (RTO) and recovery point objectives (RPO) for critical systems. Regular backups to cloud storage and annual DR testing are essential. If your cloud stores PHI, our HIPAA compliant cloud storage guide explains the additional safeguards – BAAs, encryption requirements, and shared responsibility obligations – you must have in place.
The depth here should match your commitments. Promising 99.99% uptime requires more robust infrastructure than 99.5%.
Download a customizable business continuity plan template:
5. Encryption controls
Encryption protects data even when other controls fail. Auditors expect it everywhere sensitive data lives or travels.
You’ll need TLS 1.2 or higher for network traffic, AES-256 for stored data, secure key management and proper certificate handling. Missing encryption is a significant finding, make sure your architecture covers the full data lifecycle.
Tools that help with SOC 2 framework implementation
You can manage SOC 2 manually, but it eats enormous amounts of time. The right tools make the difference between compliance as a burden and compliance as a background process. Dedicated SOC 2 software handles the time-consuming work of evidence collection, control monitoring, and audit-readiness reporting on a continuous basis, so the team can stay focused on operating the controls themselves rather than tracking the proof that they are operating.
1. Compliance automation platforms
These platforms connect to your infrastructure, collect evidence automatically, monitor controls continuously and keep you audit-ready without constant manual effort.
Look for integrations with your cloud providers and SaaS apps, control mapping to Trust Services Criteria, real-time alerts when something drifts out of compliance, policy templates and auditor-friendly dashboards.
The compliance automation market is projected to grow from $1.5 billion in 2023 to $3.8 billion by 2028, a clear sign that organizations are moving away from spreadsheet-driven compliance.
2. Security Information and Event Management (SIEM)
SIEM platforms aggregate logs across your environment for security monitoring and incident detection. For Type II audits, they provide continuous evidence that your controls actually work.
A good SIEM gives you centralized monitoring, anomaly detection, compliant log retention, and investigation capabilities. SIEM data often serves as primary evidence for multiple controls.
3. Identity and Access Management Solutions
IAM tools centralize authentication and authorization, ensuring consistent, auditable access controls. They handle provisioning, enable SSO, and generate the audit trails compliance requires.
Modern IAM platforms integrate with compliance tools to automatically prove your access controls are working.
4. Vulnerability Management Tools
Regular scanning demonstrates proactive security management. These tools automate discovery, prioritize remediation by risk, and track your patch management efforts.
Auditors expect you to find vulnerabilities quickly and fix critical issues within reasonable timeframes. Automated scanning gives you the evidence to prove it.
Stay SOC 2 ready, all year round with Sprinto
Managing SOC 2 doesn’t have to be a periodic, manual effort. With Sprinto, compliance runs continuously in the background, keeping your controls in check and your audit readiness never in question.
Sprinto brings together AI-driven workflows, deep integrations, and real-time monitoring to handle the heavy lifting of SOC 2. It automatically maps controls to framework requirements, collects and maintains audit-ready evidence, and flags risks as they arise so teams don’t have to chase gaps right before an audit.
Instead of treating SOC 2 as a one-time project, Sprinto helps you operationalize it as an always-on system. Controls are continuously tested, evidence is organized in auditor-ready formats, and any drift is surfaced early with clear remediation steps.
By centralizing controls, risks, and audit workflows in one place, Sprinto gives teams complete visibility into their compliance posture—making it easier to scale across frameworks without adding operational overhead.
The platform also includes vendor risk management, a public Trust Center for sharing your security posture, and AI-powered responses for security questionnaires.

FAQs
Yes. SOC 2 is designed for service organizations handling customer data. It’s voluntary, not legally required like HIPAA, but has become a market expectation for SaaS and cloud providers.
Type 1 is a snapshot; it checks whether your controls are designed properly at a single point in time. Type 2 tests whether those controls actually worked over 3-12 months. Enterprise buyers almost always want Type 2.
With minimal existing controls, 4-6 months for Type 1, 9-12 months for Type 2. With mature practices and automation, 6-8 weeks for Type 1, 3-6 months for Type 2.
Total costs typically run $30,000-$150,000, depending on size and scope. Audit fees alone are $10,000-$50,000 for Type 2. Compliance automation can cut total costs by 40-60%.
Security is mandatory. Add Availability if you make uptime commitments. Add Privacy if you handle PII. Most companies start with Security and Availability, then expand in later audits.
No, but many enterprise contracts require it. If you sell to mid-market or enterprise customers, SOC 2 is effectively mandatory for closing deals.
SOC 2 is a compliance reporting framework developed by the American Institute of Certified Public Accountants to evaluate how organizations manage customer data. It is based on the Trust Services Criteria—Security, Availability, Processing Integrity, Confidentiality, and Privacy—and is commonly used by SaaS and technology companies to demonstrate strong data protection practices.
The SOC 2 framework was created by the American Institute of Certified Public Accountants. It was developed to help organizations demonstrate that they have effective controls in place to protect customer data based on the Trust Services Criteria.
Author
Pansy
Pansy is an ISC2 Certified in Cybersecurity content marketer with a background in Computer Science engineering. Lately, she has been exploring the world of marketing through the lens of GRC (Governance, risk & compliance) with Sprinto. When she’s not working, she’s either deeply engrossed in political fiction or honing her culinary skills. You may also find her sunbathing on a beach or hiking through a dense forest.Explore more SOC 2 articles
SOC 2 Compliance Overview
SOC 2 Preparation and Documentation
SOC 2 Audit and
Reporting
SOC 2 Differences and Similarities
SOC 2 Updates & Management
SOC 2 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.











