SOC 2 automation helps streamline the preparation for the audit process by assisting with scoping your report, outlining necessary actions, and running assessments to ensure you’re ready for the audit.
While not everything in a SOC 2 audit can be automated, automating what you can is a huge time-saver and cost-cutter for your business. Compliance automation.
Essentialy, it eliminates the need for doing things from scratch, such as manually mapping the relevant SOC 2 criteria or validating controls. It is a quick and confident approach to compliance that helps you build a responsive compliance program.
Read on to understand what SOC 2 automation is and how you can achieve it with the right software.
TL, DR :
| SOC 2 compliance automation is the way forward as it automates repetitive tasks and helps organizations get audit-ready quickly |
| Automation is less expensive and time-consuming and helps establish mechanisms that let you stay ever-compliant |
| Some must-have features of a SOC 2 compliance automation software include policy support, continuous monitoring, automated evidence collection and integrations |
What is SOC 2 compliance automation?
SOC 2 compliance automation uses technology to streamline crucial parts of the SOC 2 attestation. Continuous monitoring of controls, management of policies, and evidence collection are some examples that can be automated with SOC 2 compliance automation.Moreover, it gives you control over your security program and 360-degree visibility into your compliance and security posture.
Why do you need SOC 2 automation?
Organizations need SOC 2 automation to streamline SOC 2 implementation, monitor controls continuously, ensure resource optimization, maintain exhaustive documentation, and ensure scalability. SOC 2 automation expedites audit readiness and helps achieve certification faster. Fill your details in the block to get a complete list of SOC 2 controls.
Download your SOC 2 controls list
As a cloud-hosted business, you have several information assets, such as servers, S3 buckets, load balancers, laptops, and more. And if you list all the assets where information is stored, including your vendors, the list could run into thousands! SOC 2 Compliance requires you to secure all your information assets per the risks identified for each of them.
For instance, if it’s an S3 bucket, you must ensure it isn’t publicly accessible. Or, if it’s an EC2 instance, you need to protect its Secure Socket Shell (SSH) access and keep the database and hard disk encrypted.
In essence, every asset type needs a different kind of security check. Now imagine running and monitoring these checks on thousands of assets every day. Trust us; it will soon snowball into a security nightmare!
Automate SOC 2 in weeks, not months.
What can be automated for SOC 2?
A SOC 2 compliance automation software can eliminate the need to work hundreds of hours. Following are the list of processes that can be automated for SOC 2 compliance framework:
- Automated mapping of Trust Service Criteria to relevant controls
- Creation and distribution of policies org-wide
- Risk identification and assessments, along with automated scoring and prioritization
- Deployment of controls such as access provisioning, de-provisioning, encryption, etc.
- Continuous monitoring of internal controls to raise alerts for any failures
- Automated evidence collection and mapping to criteria
- Monitoring of third-party risks
- Automated generation of compliance reports
- Facilitating change management with automated tracking of changes and approval of requests
- Helping track vulnerabilities and incidents till closure by integrating with third-party tools
Steps to automate SOC 2 with Sprinto
Sprinto is a compliance automation platform that can help you automate SOC 2 and ensure your systems are continuously compliant with the framework.
You can automate SOC 2 with Sprinto in 4 easy steps:
- Integrate Sprinto with your tech stack and map all entities that impact data security
- Conduct an integrated risk assessment to understand your risk status and use the risk library to identify and implement missing security controls
- Activate automated checks to continuously monitor controls and minimize compliance instances of non-compliance
- Leverage Sprinto to collect compliance evidence in an audit-friendly manner and launch an external audit with an auditor from the Sprinto’s network to complete audits fast
The main dashboard gives you a quick snapshot of the real-time view of controls and enables you to take actions quickly while automated workflows help you streamline repetitive tasks.
Capabilities like in-built policy templates, training modules, role-based access controls and integration with 200+ cloud applications help you get audit-ready in weeks.
Take the case of one of our clients ZapScale. They were looking for an automation solution that could ease the burden off of compliance tasks and help them with granular-level monitoring.
Sprinto enabled 24/7 compliance checks for different information assets and ensured that the organization achieved continuous readiness. In the words of the co-founder Bratish
“Like a personal assistant Sprinto reminds us when and where we need to take action whether it’s related to infrastructure or access and nudges us towards it”
SOC 2 Manual vs Automated: What’s the Difference?
As cloud-hosted companies, you would have an intrinsic understanding of the benefits of automation. Aside from the generic advantages, here are the key factors that swing the deal in favor of automation.
The opportunity cost of time and employee productivity
It is possible and common for organizations to use a DIY approach or hire a consultant to get their SOC 2. Many organizations have taken up the task and succeeded in it too. However, it would help if you asked whether you have the time and resources to allocate toward getting SOC 2 audit ready in-house.
Taking up the manual approach to SOC 2 requires your key engineering hires and the CTO to spend considerable time (300+ hours) setting up the processes and documentation initially.
And later, after a successful attestation, they will need to monitor and maintain compliance and repeat the entire process before the SOC 2 attestation expires (a year later).
See how Sprinto saves 300+ hours in SOC 2 Prep
Automation solves this problem smartly. It only needs an initial investment of time and effort during the implementation of SOC 2 compliance automation software. However, subsequent audits and monitoring are relatively simple.
Sprinto’s SOC 2 automation software further reduces your team’s investment in terms of time by allocating a dedicated compliance expert who walks you through the entire process.
Having a dedicated compliance expert’s support allows your infosec team to eliminate the time they would have otherwise spent attending self-learning tutorials on software implementation.
Read about how HackerRank streamlined security due diligence and regained 20% of engineering time with Sprinto.
A faster and more confident approach to SOC 2
A manual approach to SOC 2 (whether you do it yourself or hire an external consultant) easily takes up 3-4 months in audit preparation. Much time gets spent understanding the SOC 2 requirements, implementing them, and undergoing rounds of SOC 2 self-assessments and SOC 2 readiness assessments.
Even after all this, you wouldn’t walk into an audit as confidently as when using automation software.
Most SOC 2 compliance automation softwares offer health dashboards that give you an objective real-time overview of compliance.
Once you have plugged all the control gaps and hit the 100% audit readiness mark on your dashboard, rest assured that you can walk into the audit without worrying about the outcome.
What’s more, when you automate SOC 2, your audit prep time reduces considerably. Depending on the type and size of your organization, the scope and type of SOC 2 report and your security readiness, it would roughly take you anywhere from a couple of weeks to a maximum of a month to get your SOC 2 ducks in a row if you work with Sprinto.
Here’s how PreSkale completed SOC 2 audit in under 30 days using Sprinto’s compliance automation software.
Cost of compliance
The cost of SOC 2 compliance with traditional compliance systems can range between $50000-$200000 and with modern day tools can range between $7000-$50000 depending on various factors.
Aside from the auditor’s fee, the SOC 2 compliance cost depends on the type of attestation needed, the size of your organization, the scope of the audit, and the cost of security tools needed.
Sprinto’s compliance automation platform is priced at a starting price of only $8000 (depending on the organization’s size).
The evidence collection
The manual route requires you to maintain pieces of evidence to demonstrate compliance, such as screenshots, policy documents, and whatnot. Therefore, the back-and-forth email threads with the auditor tend to be long and cumbersome.
It also requires you to establish a secure way to share the required evidence with the auditor.
SOC 2 automation softwares integrate with your systems and infrastructure and simplify evidence collection and audits. So, instead of sifting through folders looking for specific evidence, your auditor gets presented with pieces of evidence that are bagged and tagged – in a neatly organized manner.
Pro Tip: Look for a SOC 2 automation software that supports automatic and manual evidence collection to accommodate edge cases.
Continuous monitoring
As we mentioned, SOC 2 automation software continuously monitors your compliance status and alerts you in cases of lapses, delays and non-compliance.
For instance, most softwares automatically alert you if an employee has yet to be offboarded (in terms of revoking access) or if a new employee still needs to undergo the staff security training program.
Real-time monitoring helps you know your compliance status at any point in time. And take quick remedial actions when needed. In contrast, the manual route isn’t continuous and relies on spot checks to monitor your compliance status.
Vendor risk management
Most SOC 2 compliance automation softwares offer robust vendor risk management features, allowing you to manage vendor agreements and certifications. The manual approach, in comparison, is long-winded and less robust.
Also check out: SOC 2 guide for startups
Run a SOC 2 compliance program end-to-end with Sprinto
Must-have SOC 2 automation software features
There are plenty of SOC 2 automation tools available in the market. How do you pick one that best fits your current and future needs?
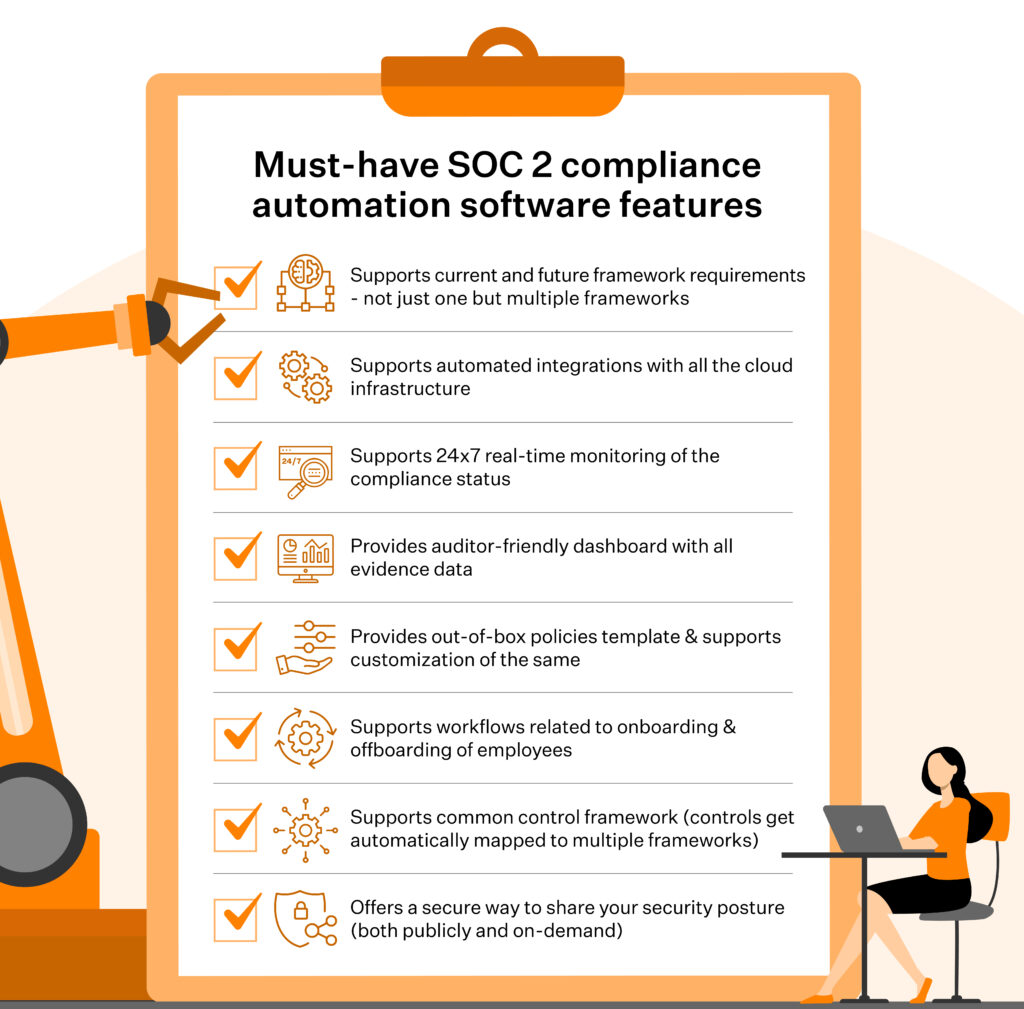
Here’s a list of the must-have SOC 2 compliance automation software features.
- Supports current and future framework requirements – not just one but multiple frameworks
- Supports automated integrations with all the cloud infrastructure
- Supports 24×7 real-time monitoring of the compliance status
- Provides auditor-friendly dashboard with all evidence data
- Provides out-of-box policies template & supports customization of the same
- Supports workflows related to onboarding & offboarding of employees
- Supports common control framework, such that controls get automatically mapped to multiple frameworks
- Offers a secure way to share your security posture (both publicly and on-demand)
Also, check out: Difference between SOC and ISO 27001
Leverage 1:1 guided implementation for SOC 2 with Sprinto
Breeze through SOC 2 Compliance with Sprinto
Forward-thinking organizations that want to streamline the path to attestation have realized that SOC 2 automation is the way to go. It paves the way for quicker certification and helps secure better enterprise deals. Compliance automation tools like Sprinto not only solve immediate compliance needs but also help formulate a long-term strategy.
With capabilities such as in-built policy templates, integrated risk assessments, continuous monitoring, automated evidence collection, access controls, and training modules, it helps you become audit-ready in a matter of weeks.

FAQs
How does SOC 2 automation work?
SOC 2 automation removes the grit and grinds from infosec compliance by automating repeatable tasks. It uses APIs to integrate with your many applications, such as cloud servers, code repos, and HRMS, and automates procedures for evidence collection and 24×7 real-time continuous monitoring.
This ensures you have a proof for every implemented SOC 2 control, reducing the back and forth with the CPA. When done manually, these tasks could eat up hundreds of hours!
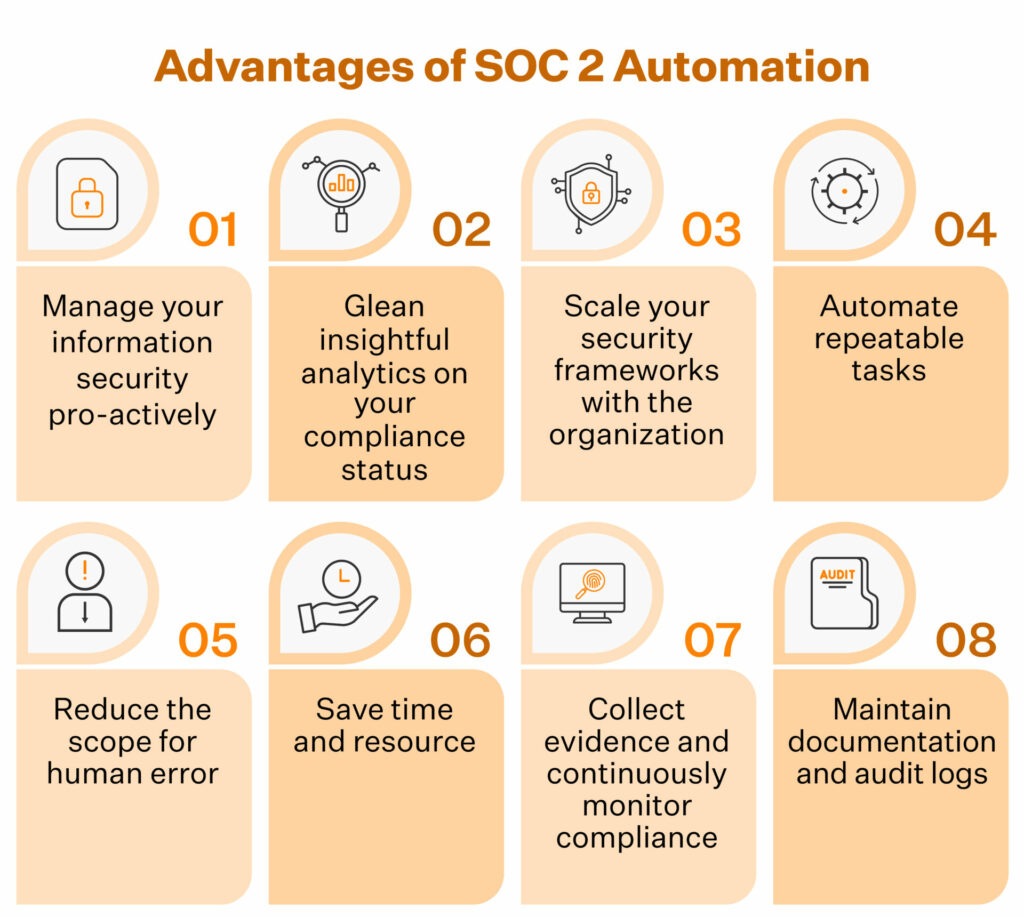
Why is SOC 2 automation important for organizations?
SOC 2 automation is important for companies on multiple counts. These include:
- Saving time and cost of compliance
- Improving evidence collection
- Managing growing compliance needs
- Ensuring 24×7 real-time continuous monitoring
- Reducing the scope for human error
- Ensuring quicker remediation to oversights, errors and attacks
What tasks can be automated with SOC 2 software?
SOC 2 software can help you navigate through compliance complexities by automating a range of tasks: evidence collection, risk assessments, access controls, continuous monitoring, reporting, training, vendor management and policy management.
Can SOC 2 software replace the need for human intervention?
While there are several tasks the software can automate, it cannot replace the need and creativity of a human resource. Human expertise is still needed for strategic thinking, manual pen tests, adaptation to changing environments, continuous improvements and communication.
How does SOC 2 automation facilitate better collaboration among teams?
SOC 2 automation facilitates collaboration among teams by enabling role-based task assignment, document sharing, access reviews, cross-functional reporting and through communication tools.
What can’t be automated in SOC 2?
SOC 2 automation can handle many repetitive tasks, but some areas still require human judgment and accountability. Examples include management reviews, risk acceptance decisions, leadership oversight, and auditor walkthroughs. Specific HR processes, such as background checks and access approvals, often require manual validation. Automation reduces effort and errors, but people are still responsible for control intent, exceptions, and sign-offs.

Author
Srividhya Karthik
Srividhya Karthik, is a Content Lead at Sprinto, she artfully transforms the complex world of compliance into accessible and intriguing reads. Srividhya has half a decade of experience under her belt in the compliance world across frameworks such as SOC 2, ISO 27001, GDPR and more. She is a formidable authority in the domain and guides readers with expertise and clarity.Explore more SOC 2 articles
SOC 2 Compliance Overview
SOC 2 Preparation and Documentation
SOC 2 Audit and
Reporting
SOC 2 Differences and Similarities
SOC 2 Updates & Management
SOC 2 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.