For many startups, a SOC 2 report is no longer a nice-to-have. It is often a baseline requirement for establishing trust with security-conscious customers and closing deals in SaaS and B2B environments. But preparing for a SOC 2 audit can be time-consuming, and before engaging an external auditor, most teams want to know: Are we actually ready? Have we covered the right controls? Are there gaps that could delay the audit or result in costly remediation?
That is where a SOC 2 self-assessment can help. It gives your team a structured way to review scope, controls, evidence, and readiness internally before the formal audit begins and without the cost of hiring an external consultant.
Unlike a formal SOC 2 readiness assessment, a self-assessment is led by an internal team. It covers the same ground control mapping, gap identification, and remediation planning but relies on internal expertise rather than an external auditor. Read on to learn how to run one effectively.
Bonus: A downloadable SOC 2 Self-assessment checklist.
Why do you need to conduct SOC 2 self-assessment?
A SOC 2 assessment can help you comprehensively identify and asses your entire control environment before the formal SOC 2 audit. It will help surface deficiencies, gaps, and other problems that need immediate corrective action.

It’s a good idea to understand SOC 2 requirements and have a functional SOC 2 compliance checklist before undertaking SOC 2 self-assessment.
Must check: SOC 2 Auditors and Service Providers [How to Choose One]
What you need to conduct SOC 2 self-assessment
Before we move on to the steps in self-assessment, let’s quickly look at what are your absolute must-haves.
Start your self-assessment months before your SOC 2 audit
No matter which option you choose, remember that you must review your audit readiness months before your actual audit. Doing this would give you ample time to remediate, make edits, and plug control gaps.
Ensure the subject matter expertise of your internal resource
Your internal resource who will lead the self-assessment must have established expertise and authority in conducting it. Otherwise, the exercise may prove futile, and you would risk getting an unfavorable auditor opinion in your SOC 2 report.
Conduct a SOC 2 audit self-assessment in three steps
SOC 2 assessment helps you evaluate your controls, and find any gaps or deficiencies in your control environment. The compliance process is far from easy, but here’s a simple step-by-step guide to executing it.

Step 1: Review audit scope
The first step of a SOC 2 assessment is reviewing the audit scope: the portion of your organization that must be included in the audit – related to information systems, people, and locations. When you determine the specific systems that would be critically assessed, there is a high likelihood of your discovering that you must include more of your organization’s systems and controls in the scope. Better now than later though.
You don’t want to be surprised by ‘scope creeps’ during your SOC auditing process! At this stage, you must also verify if all the relevant Trust Services Criteria (TSC) (security, availability, confidentiality, processing integrity, and privacy) have been chosen for your organization.
Get Our Practical SOC 2 Guide;
Yours at No Cost

Step 2: Evaluate control mapping
You can start by gathering and reviewing the evidence you’ve collected with respect to the documentation, policies, and internal controls based on the chosen TSCs. Each chosen TSC has a subset of individual criteria and requirements. You must evaluate whether your controls are mapped to each individual criterion as well as the common criteria series.
A review of your SOC 2 risk assessments is also a good starting point for examining the identified risks and the controls implemented to address them.
You will also review the organization controls mapping spreadsheet, relevant procedure documents such as management assertion letter, system description, and policies, and the evidence of security compliance at this stage. Doing this will bring to the fore any missing or deficient controls and gaps that need fixing before your SOC 2 compliance audit.
Step 3: Implement remediation plan and test for more gaps
With an overview of the missing links, security control designs and oversights, you must now make recommendations for plugging the gaps and bolstering the controls matrix of your organization to meet the compliance requirements.
You must also document the remediation plan with details of the gaps, the corrective actions, the person responsible for implementing the remediation, and the time taken to complete it. Some of the corrective actions to your security program can include access controls, incident response in case of a data breach, to name a few.
You must also communicate the results and the corrective actions of the self-assessment process with all the stakeholders in the organization. It is important for all stakeholders to have an understanding and overview of the organization’s network security posture.
Also read: A Guide on SOC 2 Compliance

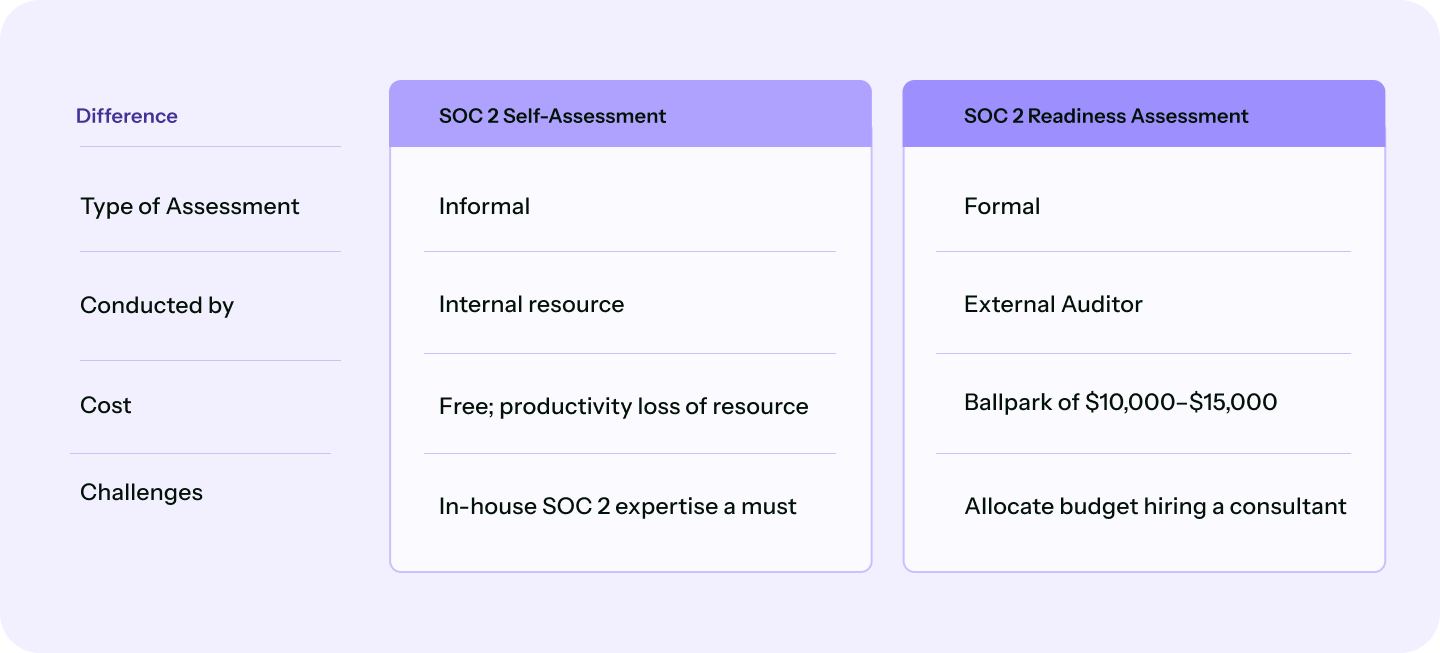
SOC 2 readiness assessment vs SOC 2 self-assessment: What’s the difference?
SOC 2 readiness assessment and SOC 2 self-assessment are essentially the same; they review your organization’s audit preparedness and help you remediate the gaps, wherever applicable. In short, both approaches prepare you for your SOC 2 audit, where an independent CPA firm evaluates whether your controls are suitably designed to meet the applicable Trust Services Criteria, and in the case of a Type 2 report, whether those controls operated effectively over a defined review period.
But there are some significant differences that you should know before deciding which way to take.
Type of assessment
A self-assessment is an internal review of your controls and readiness led by your own team, without external involvement. It is flexible, low-cost, and useful for identifying obvious gaps before committing to a formal audit process.
A readiness assessment is a more structured review, often supported by an experienced external advisor, audit firm, or compliance specialist, to systematically identify gaps before the formal audit begins. It is more rigorous than a self-assessment but does not need to be performed by the same CPA firm that will issue the final SOC 2 report, and is not required to be conducted by an AICPA-credentialed auditor specifically.
Both approaches serve the same purpose: surfacing gaps and giving your team time to remediate before the formal audit clock starts.
Owners
As we mentioned earlier, a readiness assessment is carried out by an external auditor you hire for the job. The external auditor will review your audit scope & controls mapping, among other things and share a detailed remediation plan with your management.
Self-assessment is carried out by an internal resource with relevant expertise. It also involves mapping of your existing information security controls to your selected Trust Services Criteria (TSCs or Trust Service Principles), identifying gaps, and creating a remediation plan ahead of your SOC 2 audit.
Cost
A readiness assessment can set you back by about $10000-$15000. Self-assessment, on the other hand, comes at no cost; except the cost of lost productivity and time of your internal resource(s).
Challenges
Your choice of assessment, therefore, would boil down to the question of resource allocation. Are you ready to expend $10k-$15k, or would you rather allocate internal resources that come bundled with productivity costs alone? The challenge would be to have the right internal SOC 2 expert to spearhead the self-assessment process.
If you are in a supply chain business then click here.
SOC 2 self-assessment checklist
SOC 2 assessment is more time-consuming than tough. It’s a good idea to approach it in a planned and phased manner. Here’s a handy checklist to ensure you haven’t missed anything critical to help your organization prepare for an audit.
Download your SOC 2 Self Assessment Checklist
Get audit-ready faster with Sprinto
Sprinto is an autonomous trust platform that helps you get audit-ready faster and stay that way with less manual effort. With autonomous audit management capabilities, it takes care of the heavy lifting from evidence collection and control mapping to risk assessments and policy management.
You also get a real-time view of your compliance posture, so it’s easy to see what’s on track, what needs attention, and what could put your audit readiness at risk. Built-in SOC 2 self-assessments help you spot gaps early and fix them before they become bigger issues.
What really makes the difference is continuous monitoring. Instead of checking controls only when an audit is around the corner, Sprinto keeps an eye on them year-round so you can maintain a continuously compliant, audit-ready posture.
Book a demo with Sprinto to see how you can simplify SOC 2 and stay continuously audit-ready.
Author
Radhika Sarraf
Radhika Sarraf is a content marketer at Sprinto, where she explores the world of cybersecurity and compliance through storytelling and strategy. With a background in B2B SaaS, she thrives on turning intricate concepts into content that educates, engages, and inspires. When she’s not decoding the nuances of GRC, you’ll likely find her experimenting in the kitchen, planning her next travel adventure, or discovering hidden gems in a new city.
Reviewer
Sonali Samantaray
Sonali Samantaray is a Senior Solutions Architect at Sprinto with deep expertise in SaaS presales, consulting, and cybersecurity compliance. A certified PCI QSA, 3DS QSA, and ISO 27001 Lead Auditor and Implementer, she helps organizations untangle complex security frameworks and build audit-ready environments with confidence.Explore more SOC 2 articles
SOC 2 Compliance Overview
SOC 2 Preparation and Documentation
SOC 2 Audit and
Reporting
SOC 2 Differences and Similarities
SOC 2 Updates & Management
SOC 2 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.