Every business looking to get SOC 2 (Service Organization Control) compliant must work with a credible SOC 2 auditor—either a licensed CPA or an American Institute of Certified Public Accountants (AICPA) accredited third-party firm. Auditors must be independent, with no connection to your organization, to ensure unbiased reporting.
When selecting the best SOC 2 auditor, don’t rely solely on online reviews. Instead, understand the types of organizations they typically work with, ask about their experience auditing businesses like yours, and how they handle challenges such as remote workforces. This helps you anticipate what your SOC 2 audit experience will be like.
In this blog, we’ll guide you on how to choose the right SOC 2 auditor and what to expect during your SOC 2 audit.
What is a SOC 2 Auditor?
A SOC 2 auditor is a licensed CPA or a professional from an AICPA-accredited firm who evaluates an organization’s security controls against the Trust Services Criteria (TSC). They review your policies, procedures, and safeguards to ensure sensitive data is properly protected and provide an official report detailing their findings.
Who are qualified SOC 2 Auditors?
Qualified SOC 2 auditors are certified public accountants (CPAs) from firms accredited by the American Institute of Certified Public Accountants (AICPA). Other requirements for qualification include:
- The auditor or auditing firm must be a completely independent CPA, meaning they have no relationship with the service organization they’re auditing.
- Comply with the professional standards set by AICPA.
- Adhere to the latest guidance for planning, executing, and supervising audit procedures.
What do SOC 2 Auditors do?
A SOC 2 auditor evaluates an organization’s security posture by thoroughly assessing how well its controls are designed and implemented. They review policies, procedures, and technical safeguards aligned with the chosen Trust Services Criteria (TSC). This confirms that controls aren’t just on paper but actually in place and functioning effectively.
The responsibilities of SOC 2 auditors include the following:
- Evaluate the effectiveness of controls over a period of time based on the selected TSC (Trust Services Criteria). They also advise corrective actions throughout the audit procedures and help you meet your compliance goals.
- Prepare a detailed SOC report listing the description of your systems, management assertion, control environment, control activities, risk assessment, and monitoring activities.
- Ensure that your organization’s security, availability, confidentiality, processing integrity, and privacy controls align with the guidelines issued by AICPA and the applicable audit type (SOC 1, SOC 2, or SOC 3).
When and how to use SOC 2 auditors?
An Auditor is brought in the final stage of the compliance process. Before an Auditor gets involved in your SOC 2 journey, clearly define the audit scoping and understand and implement controls that are relevant.
For example, choose which of the five trust service categories apply to your organization and apply the controls required for the chosen ones.
Document all the policies, controls, and measures deployed within your organization. This enables you to seamlessly demonstrate to your Auditor how the deployed controls and measures meet the requirements for the chosen trust service criteria of SOC 2.
Before an Auditor begins the audit, perform a readiness assessment exercise. It gives you insights into any gaps in the system and organizational controls. Solving these gaps helps you go through the audit process with minimal non-conformities.
Who else is involved in a SOC 2 audit?
Apart from the CPA firm that is central to conducting a SOC 2 audit, several internal stakeholders and sometimes external partners may be involved.
| Stakeholder Type | Roles/Examples |
| Internal Stakeholders | – Management (CISO, CTO, Compliance Officer) – Engineering / DevOps – IT Team – PeopleOps / HR – Legal Team |
| External Stakeholders | – SOC 2 Auditors – Third-party platforms (e.g., Sprinto) that facilitate audit collaboration, evidence collection, and reporting |
How to choose the best SOC 2 Auditor in 2025?
Choosing a SOC 2 auditor is not only about AICPA certification but also about finding someone who understands your business, fits your budget, and moves fast. Whether it’s a Big 4 firm or a nimble CPA, choose expertise and speed over brand.
Here are a few things you should keep in mind when choosing an auditor for your SOC 2 audit:
AICPA Certification
The AICPA (American Institute of Certified Public Accountants) regulates the SOC audit process. When any organization undergoes an audit, they are audited by AICPA-approved
SOC 2 Auditors from licensed CPA firms or independent auditors.
Tip:
- The Auditor should be AICPA certified.
- The SOC 2 service Auditor should also have a specialization in information security. They usually have this, but it doesn’t hurt to check 🙂
Budget & Big 4 Companies
CPAs who work independently charge less than ones from a CPA firm. It is a common misconception that since independent CPAs charge less, their work might not be on par with CPAs firms. Unfortunately, that’s not the case.
Unless you are an organization with enterprise-grade clients, you wouldn’t necessarily need an Auditor from the large CPAs (Deloitte, KPMG, EY) to stamp your audit report.
Tip:
- Unless your customers specifically request an audit report from a CPA firm, or you notice a pattern in your line of work where a SOC 2 audit report from an independent Auditor is not considered, the idea of working with an independent Auditor is not worth dismissing.
- Independent Auditors work faster, give their undivided attention (since they usually take on one client at a time), and are significantly cost-effective.
Industry Experience
Working with a SOC 2 Auditors who have audited organizations similar to yours is always a huge plus. In the SOC 2 audit process, the Auditor often comes back asking for evidence for things like specific controls or asks you to show training acknowledgments.
This to-and-fro could become more complicated if the Auditor has never previously worked with organizations similar to yours. For instance, the complication could be profound if you are a fully remote organization.
So, conversing about their experiences and introducing them to your organization prevents a terrible audit experience.
Remote vs. On-site Audits
SOC 2 audits can be performed either remotely or on-site, depending on your organization’s setup and auditor preference. Each approach has its own advantages and considerations.
| Remote Audit | On-site Audit | |
| Description | Conducted digitally with auditors reviewing documentation, policies, and evidence online. | Auditors visit your physical location to examine systems, processes, and controls in person. |
| Pros | Faster, flexible, ideal for remote teams, less disruption. | Limited ability to inspect physical setups or on-site processes. |
| Cons | Provides deeper insights, better for hands-on evaluation of physical controls. | Requires more time, coordination, and potentially higher costs. |
Working with SOC 2 service providers
SOC 2 audit readiness platforms (also known as compliance automation platforms) and other software designed to help companies become SOC 2 compliant can only go as far as assisting them to become audit ready.
Audit-readiness platforms can support preparation, evidence collection, and workflow management, but the audit opinion itself must come from an independent licensed CPA or AICPA-accredited firm.
Working with a compliance automation platform is optional, but an independent SOC 2 audit is required if you want a formal SOC 2 report.
Compliance automation platforms aim to smoothen your audit readiness journey. Some platforms help structure collaboration by centralizing evidence, requests, and follow-ups, so teams and independent auditors can work from a single source of truth.
With compliance automation, businesses are now freed from the laborious and time-intensive activity of setting up appropriate controls, measuring the effectiveness of deployed controls, conducting gap analysis, conducting an audit readiness assessment, and providing additional evidence to the Auditor.
Compliance automation services automate repeatable technology-based requirements in SOC 2 compliance framework.
They enable businesses to channel their focus back to core business activities that contribute to revenue generation and business expansion instead of spending hundreds of hours on becoming SOC 2 compliant.
Once you understand the role service providers can play, the next practical question is cost, timeline, and what the audit itself will involve.
SOC 2 Auditors’ cost and timeline
SOC 2 auditor cost
For small and mid-sized businesses, SOC 2 audit costs typically fall in the following range:
- SOC 2 Type 1: $8,000 – $12,000
- SOC 2 Type 2: $15,000 – $40,000
Some auditors offer fixed pricing based on selected Trust Services Criteria (TSC), such as $20,000 for only the Security criterion. These estimates are based on boutique and mid-tier firms. Big 4 firms like Deloitte or PwC generally cater to enterprise clients and charge significantly higher fees.
SOC 2 audit timeline
The audit timeline depends on the type of report:
- SOC 2 Type 1: Typically completed in 4–6 weeks
- SOC 2 Type 2: Can take 3–6 months
Keep in mind that preparation and readiness before the audit can significantly affect these timelines. Working with an experienced auditor or using a compliance automation platform can speed things up.
SOC 2 audit process: what to expect?
Every organization going through a SOC 2 audit will need to demonstrate their compliance with the requirements of the SOC 2 framework depending on the trust principles they’ve chosen for their business.
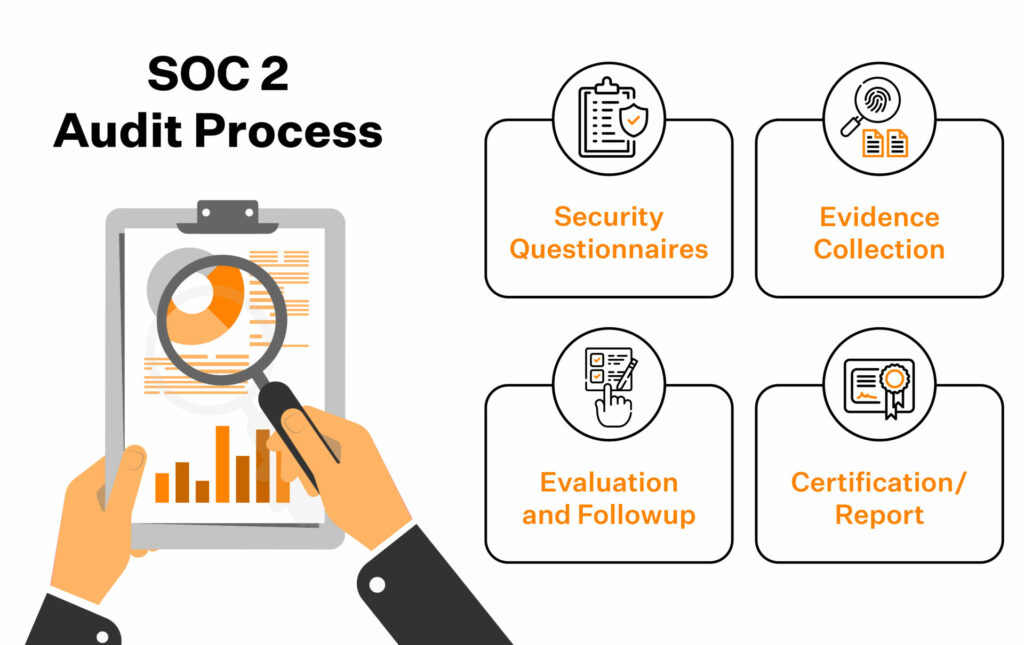
In SOC 2 audits, businesses are generally advised to expect these four things in their audit journey:
Security questionnaires
In the early stages of an audit, the Auditor sends a lengthy and exhaustive questionnaire asking for security controls to the organization.
They are asked to provide details on the trust principles applicable, a list of controls they’ve used, infrastructure in place, cloud security policies, people policies, security programs, and more.
Evidence collection
The organization is asked to provide evidence for all the controls they’ve deployed and evidence of optimum efficiency results of deployed controls. The Auditor then reviews this proof to make their assessment of how compliant the organization is.
Evaluation and followup
Suppose the Auditor feels that additional evidence is required to demonstrate compliance for any control(s). In that case, they ask the organization to provide more evidence.
When gaps in information security management are spotted, the audit process is paused until the organization remediates those gaps.
Certification/Report
For SOC 2 Type 1/Type 2, once the Auditor has completed the audit process, based on their assessment of your organization’s controls and policies, they write the report.
Recommended: How to get SOC 2 Type 2 certified
Get a wingman for your SOC 2 audit
How do I prepare for a SOC 2 audit?
Based on the SOC 2 certification Type, the audit readiness journey varies. For example, for SOC 2 Type 2, the audit preparedness time generally ranges from six days to a few months depending on the organization’s size and business model.
Before starting the SOC 2 audit, it is a good practice to ensure that your organization has implemented all the controls and policies required by SOC 2 for the chosen trust principles.
Conducting an audit readiness assessment allows you to analyze the current security compliance posture and identify gaps that require remediation.
It is also a good practice to map control and their respective evidence to ensure that the Auditor is presented with data that is easy to consume.
Classifying your audit readiness implementations into two categories for easy identification and classification is advisable:
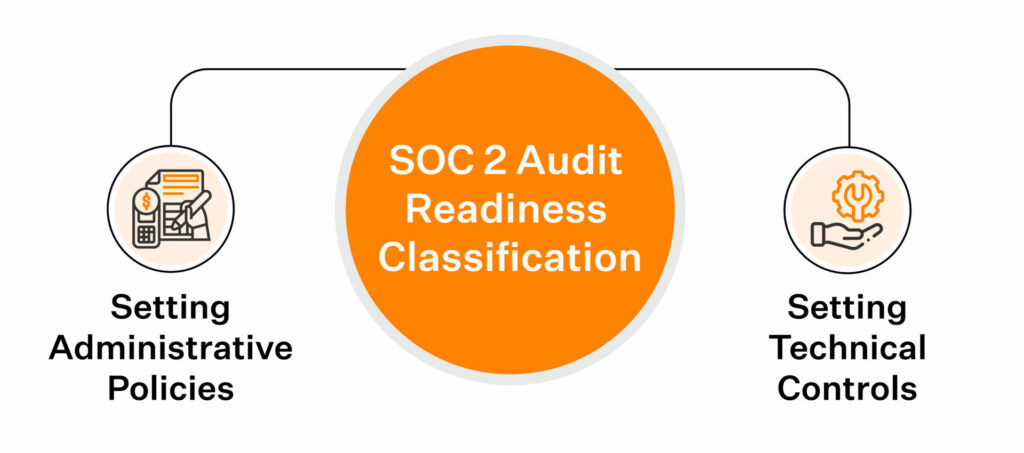
Setting administrative policies
Your organization’s policies should be centred around SOC 2’s key security principles and internal controls for disaster recovery, audit logging, employee training, onboarding and offboarding, and system access activities
Setting technical controls
Deploy controls around your organization’s cyber security information, encryption, access control, vulnerability scanning, threat detection, intrusion detection, penetration testing, firewalls, and network rules, among others.
Classifying the controls and policies helps systemically check if a strong compliance posture is successfully demonstrated. This then helps you identify the active requirements and controls that are actively contributing to the posture and list the dormant ones and fix those gaps.
Also read: Benefits of ISMS Implementation
Bring more structure to SOC 2 preparation with Sprinto
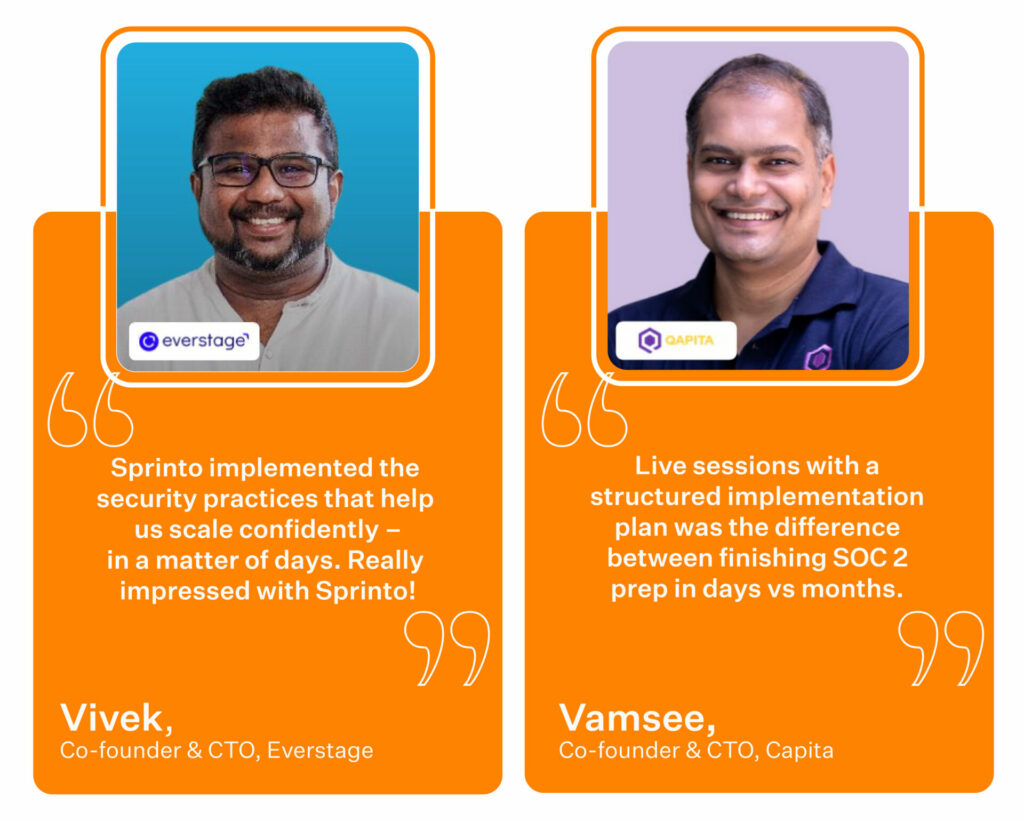
Let’s hear it from our clients!
How did we achieve this?
Sprinto is purpose-built to focus on two key objectives. The first objective focuses on automating controls, policy workflows, and recurring checks so teams can reduce manual preparation.
Sprinto connects with your cloud system to map systems that process sensitive customer data and conduct a risk assessment to understand the audit scope. It implements the right checks to meet audit requirements through continuous testing of controls.
The second focus is on automating evidence collection and organizing it in a way that is easier for teams and independent auditors to review.
This allowed us to present evidence in a way that is easy to consume for the Auditor, thus eliminating the to-and-fro between Auditors and organizations.
This helped teams reduce repeated back-and-forth and move through review workflows more efficiently.
FAQs
SOC 2 audits are performed by licensed CPAs or professionals from AICPA-accredited firms. They evaluate an organization’s controls against the Trust Services Criteria (TSC) and issue an official report on their findings.
An experienced auditor will charge anywhere between $5,000 to $15,000. If the organization is larger in size, it could go up to $50,000. Keep in mind that factors like audit period, pricing structure of the vendor, location of the audit firms, and secluded Trust Services Category also influence the price.
A licensed CPA (Certified Public Accountant) firm or an AICPA-approved SOC 2 auditor are qualified to conduct your audit. They should have no prior relationship with your organization.
The duration of a SOC 2 audit depends on factors such as the scope of the audit, organization size, complexity of systems, and readiness level. Typically, a SOC 2 readiness assessment may take a few weeks, while the full audit can take 2–6 months.
You can become a SOC 2 auditor if you have qualifications like CPA, CISA, or CISSP, along with at least one year of under the supervision or mentoring of a licensed CPA.
Several licensed CPA firms provide both SOC 1 and SOC 2 audits. When evaluating one, verify its licensing or accreditation, independence, relevant industry experience, and fit for your scope and operating model.
Only licensed Certified Public Accountants (CPAs) or firms accredited by the AICPA (American Institute of Certified Public Accountants) can perform SOC 2 audits. While non-CPA professionals may support the process, the final report must be signed and issued by a licensed CPA. The auditor must also be completely independent from the organization being audited.
You need to be a licensed CPA or work under one at an AICPA-accredited firm. Most auditors also have at least one year of SOC or IT audit experience and a solid understanding of the Trust Services Criteria. While certifications like CISA or CISSP are optional, they enhance credibility. Many auditors today use platforms like Sprinto to speed up audits and reduce manual work.
Author
Vimal Mohan
Vimal is a Content Lead at Sprinto who masterfully simplifies the world of compliance for every day folks. When not decoding complex framework requirements and compliance speak, you can find him at the local MMA dojo, exploring trails on his cycle, or hiking. He blends regulatory wisdom with an adventurous spirit, navigating both worlds with effortless expertiseExplore more SOC 2 articles
SOC 2 Compliance Overview
SOC 2 Preparation and Documentation
SOC 2 Audit and
Reporting
SOC 2 Differences and Similarities
SOC 2 Updates & Management
SOC 2 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.