How can your customers assess whether you are as secure as you claim to be? By asking for an independent, third-party audit and review of your information security posture. But what about when your prospect is one of the US federal agencies? A SOC 2 attestation wouldn’t cut the mark here. You will need a FedRAMP certification.
This article dwells on FedRAMP vs SOC 2 and details the definition, scope, and differences between the two compliance frameworks.
What is FedRAMP?
The Federal Risk and Authorization Management Program (FedRAMP) is a US federal cybersecurity risk management program for purchasing cloud products and services federal agencies use. It addresses the security and reliability of the cloud by standardizing its approach to security management, authorization, and continuous monitoring for cloud products and services.
FedRAMP was developed in 2011 by the Joint Authorization Board (JAB) in collaboration with multiple government agencies such as the National Institute of Statistics and Technology (NIST), the General Services Administration (GSA), the Department of Defense (DOD), and the Department of Homeland Security (DHS).
FedRAMP applies to all the cloud infrastructure and applications that hold federal data. So, all the cloud service providers (including IaaS, PaaS & SaaS applications) used by federal agencies or looking to pursue similar partnerships must demonstrate FedRAMP compliance.
As a SaaS firm wanting to offer services to the US federal government, you must not only run your software on a FedRAMP-compliant cloud service provider (CSP), your software too should pass the FedRAMP audit.
Getting FedRAMP Authorization
Getting FEDRAMP certified is no mean feat; it requires rigorous compliance efforts. But at a high level, you can break down the steps to achieve FedRAMP authorization and compliance.
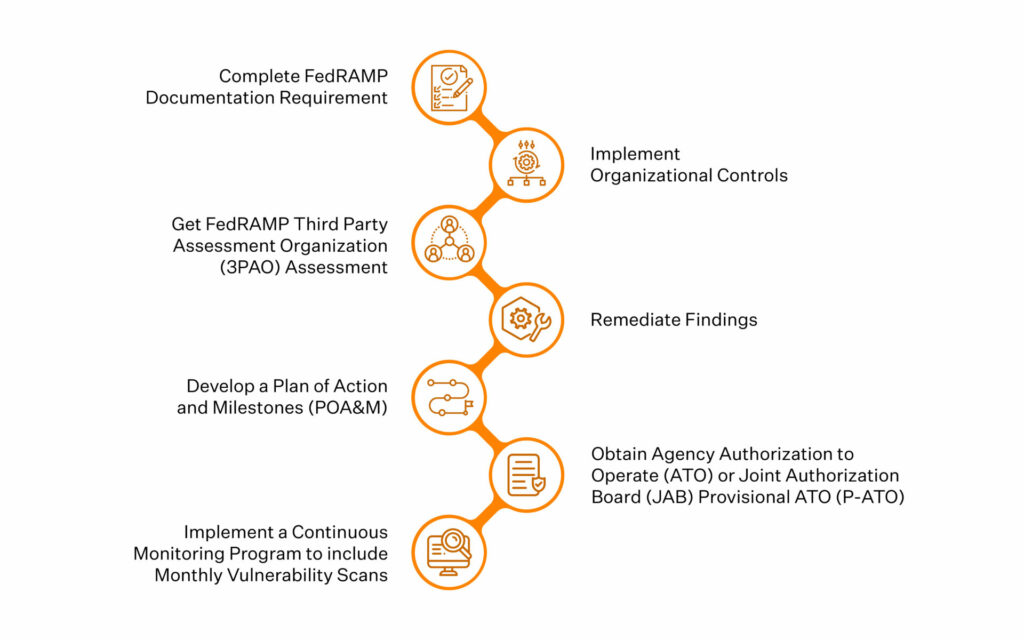
- Complete FedRAMP Documentation Requirement
- Implement Organizational Controls
- Get FedRAMP Third Party Assessment Organization (3PAO) Assessment
- Remediate Findings
- Develop a Plan of Action and Milestones (POA&M)
- Obtain Agency Authorization to Operate (ATO) or Joint Authorization Board (JAB) Provisional ATO (P-ATO)
- Implement a Continuous Monitoring Program to include Monthly Vulnerability Scans
Wondering what some of these terms are? Here’s a quick overview of the primary players in the FEDRAMP certification process, apart from you.
Third-Party Assessment Organizations (3POA): The 3PAO provide an initial security assessment of the CSP’s compliance with the FedRAMP requirements. As independent third parties, they also conduct more assessments to ensure continued compliance and maintenance. The federal government uses 3PAO assessments to make informed, risk-based authorization decisions. You can find the list of approved 3PAO in the FedRAMP Marketplace.
Joint Authorization Board (JAB): The JAB is the primary governance and decision-making body for FedRAMP. It consists of Chief Information Officers from the DoD, the DHS, and the GSA. The JAB’s responsible for defining and updating FedRAMP security authorization requirements, approving accreditation criteria for 3PAOs, reviewing and granting provisional authorizations of CSPs, and establishing the priority queue requirements for CSPs, to name a few.
Program Management Office (PMO): It is part of the GSA, and supports agencies and cloud service providers through the FedRAMP authorization process. PMO also maintains a secure repository of FedRAMP authorizations to enable the reuse of security packages.
FedRAMP Certification Requirements
To achieve FedRAMP authorization, organizations must meet a series of controls and give a detailed description of how it meets them in a System Security Plan. It then gets audited by a FedRAMP-approved auditor and must be authorized either by a government agency or the JAB.
In essence, to become a certified FedRAMP vendor, organizations can obtain a P-ATO through the JAB or an ATO by working with a government agency.
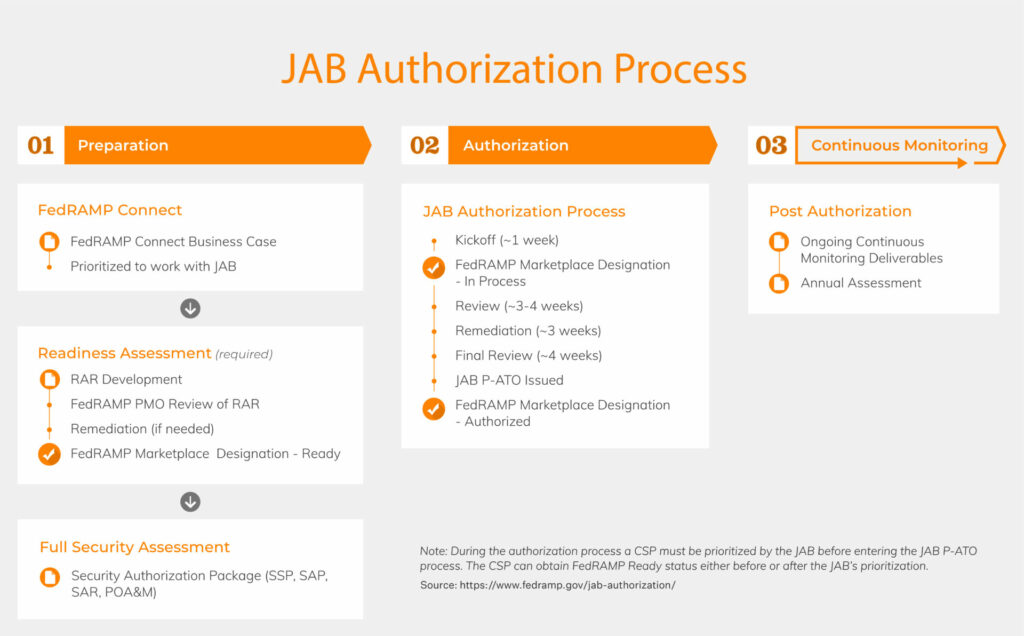
Joint Authorization Board (JAB) Provisional Authority to Operate
The JAB issues a FedRAMP Provisional Authorization to Operate to the organization after an approved 3PAO has assessed its risk. But since the JAB doesn’t have the authority to accept risk on behalf of any other federal agency, the authorization is provisional. The power to do this lies with the Authorization Officer (AO) of the specific federal agency.
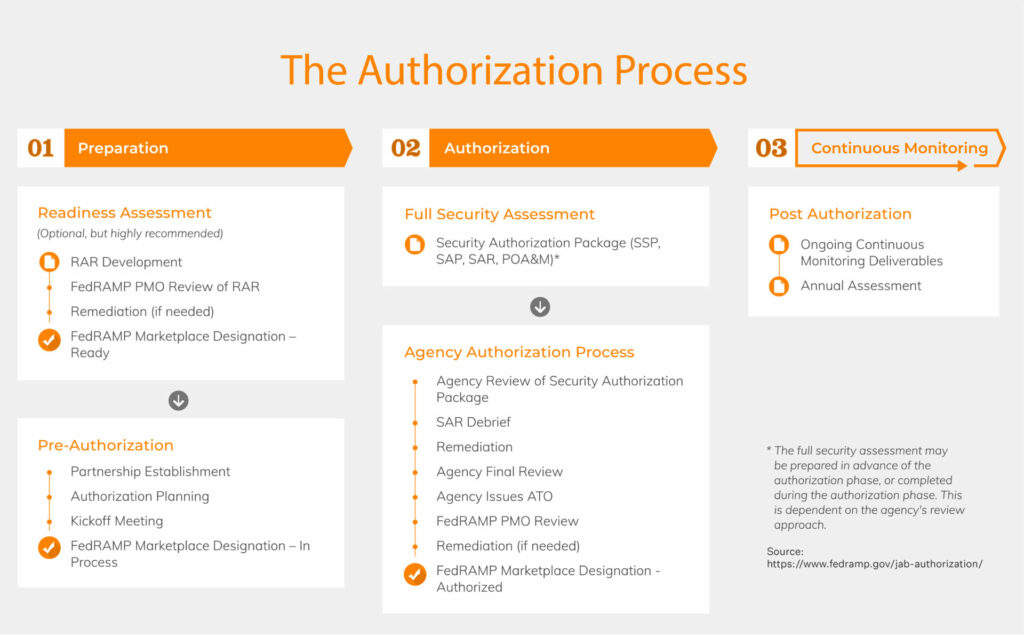
Agency Authority to Operate
Organizations must work directly with a specific agency (that’s sought their services) during the Agency Authorization process to obtain an ATO authorization. The organization’s federal agency partner works with them throughout the process and arranges approval for it from the FedRAMP PMO. Once approved, the organization will be issued with an ATO that authorizes them to work with the specific agency.
FedRAMP vs SOC 2 Similarities
FedRAMP and SOC 2, as far as compliance frameworks go, are rooted in the need to provide a safe and secure environment for businesses. They are voluntary compliances (unlike GDPR compliance) that organizations choose to comply with to meet the security requirements and standards of their customers and prospects, and win their trust.
Both FedRAMP and SOC 2 have an annual certification frequency. Besides, security controls such as penetration testing, access control, contingency planning, incident response, and risk assessments are common to both; of course, the scope varies.
Both allow the cloud service provider to gain a significant advantage over competitors.
SOC 2 vs FedRAMP Differences
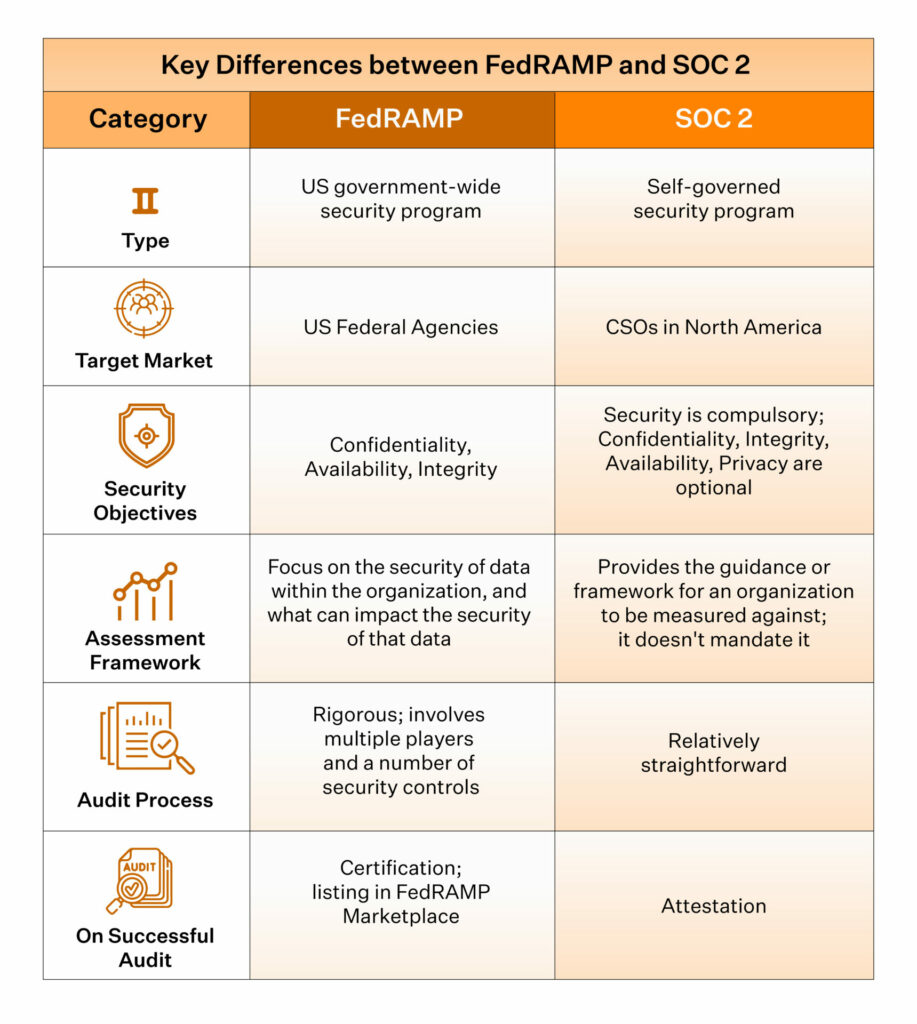
FedRAMP is extensive in its scope and has stricter norms whereas SOC 2 is relatively simpler and is self-governed. Here’s a quick lowdown on FedRAMP vs SOC 2.
Target Market
Organizations seeking to offer US federal government services must get FedRAMP certified. There are no two ways about it as you can’t sell without a certification. It’s a US government-wide security program.
Getting SOC 2 attested, on the other hand, is a decision that vests with the organization irrespective of whom they sell to. Of course, having a SOC 2 attestation makes it easier to close deals that could otherwise have gone on the back burner (due to a lack of verifiable security practices). But it isn’t as big a deal breaker as FedRAMP as SOC 2 is a self-governed security program.
Security Objectives
When it comes to FedRAMP vs SOC 2, FedRAMP aims to protect government data in cloud environments and strengthen agencies’ IT security. It is centred on the security objectives of confidentiality, integrity and availability.
SOC 2 requirements, in comparison, are centered on its five trust service principles to protect customer data; security, availability, processing integrity, confidentiality, and privacy. The only security of these five is compulsory for a SOC 2 certification; organizations choose from the other four based on their requirements.
Assessment Framework
FedRAMP focuses on the security of data within the organization, and what can impact the security of that data. The risk assessment and authorization decision in FedRAMP, therefore, is based on the organization’s ability to scope its authorization boundary.
SOC 2, on the contrary, provides the guidance or framework for an organization to be measured against; it doesn’t mandate it. And during the audit, it tests and validates whether organizations follow their stated policies and procedures.
Audit Process
If we look at FedRAMP vs SOC 2, FedRAMP is one of the most rigorous security certifications for software-as-a-service organizations. The audit process is painstakingly elaborate thanks to the number of FedRAMP security controls and involves a number of players. Organizations are categorized as low, moderate, and high impact levels, and the number of controls are contingent on the categorization.
For instance, FedRAMP moderate has 325 security controls, and FedRAMP high has 421 controls.
SOC 2 audit, in comparison, is relatively straightforward.
For more information download our SOC 2 audit checklist.
Download Your SOC 2 Audit Checklist
So FedRAMP vs SOC 2, who is the winner?
In this SOC 2 vs FedRAMP tussle, who is the clear winner? The customer! With organizations upping their security postures and continuously monitoring and improving their data security game, the customer is the undefeated winner.
Security compliance adds a whole new dimension to customer delight when seen in this light. All you need to do is make compliance your superpower. Pick an autonomous compliance solution that frees up your engineering leadership to focus on growing your product, automates the majority of the compliance processes, and grows with your organization, both in terms of newer frameworks and the breadth and depth of their coverage.
Join Sprinto’s 450+ satisfied compliance conquerors
Talk to us today to discover how Sprinto can help you make confident strides in your compliance journey.

Author
Srividhya Karthik
Srividhya Karthik, is a Content Lead at Sprinto, she artfully transforms the complex world of compliance into accessible and intriguing reads. Srividhya has half a decade of experience under her belt in the compliance world across frameworks such as SOC 2, ISO 27001, GDPR and more. She is a formidable authority in the domain and guides readers with expertise and clarity.Explore more SOC 2 articles
SOC 2 Compliance Overview
SOC 2 Preparation and Documentation
SOC 2 Audit and
Reporting
SOC 2 Differences and Similarities
SOC 2 Updates & Management
SOC 2 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.