In the cult movie Wall Street, Gordon Gekko unapologetically proclaims, “I don’t throw darts at a board. I bet on sure things.” Don’t worry. This isn’t an article in adoration of his shameless villainy. We want to direct your attention to what he was particularly good at – hedging his risks before making a play. He always assessed and managed his risks. SOC 2 risk assessment, if we take a leaf from Gordon’s playbook, is somewhat similar.
It is about knowing what you’re going to do to mitigate the many potential and prevalent risks to your business, hedging them by implementing SOC 2 controls, and building a cheat sheet on what should be done if and when a risky eventuality does occur.
In this article, we will talk about the steps in risk assessment, control gaps, strategies you can use, and many other informational tips you can use in the process.
- A SOC 2 risk assessment helps identify and evaluate risks across systems, processes, and data that could affect security, availability, confidentiality, processing integrity, or privacy.
- The process involves defining scope, listing assets, spotting threats/vulnerabilities, assigning likelihood-impact scores, and prioritizing remediation steps.
- Regular assessments strengthen your security posture, support continuous monitoring, and keep you aligned with SOC 2 Trust Services Criteria.
What is SOC 2 risk assessment?
SOC 2 risk assessment identifies the risks to your information assets, assesses their impact, assigns a likelihood of their occurrence, and deploys suitable mitigation measures (SOC 2 controls).
It is critical in your SOC 2 compliance journey, but it is easier said than done. As you would soon realize, the entire exercise is subjective; no two companies would have identical risks. What are the requirements for risk assessment for SOC 2?
Automate SOC 2 risk assessment with the help of Sprinto. Talk to us now!
Why Is SOC 2 Risk Assessment Important?
A SOC 2 risk assessment is crucial because it helps organizations identify, analyze, and prioritize security risks that could impact customer data and system reliability. It ensures your controls align with the SOC 2 Trust Services Criteria, reduces the chances of audit gaps, and strengthens your overall security posture.
By regularly assessing risks, companies can identify vulnerabilities early, enhance remediation planning, maintain continuous compliance, and demonstrate trustworthiness to customers and auditors. It also supports faster SOC 2 readiness and smoother audits by keeping risks documented, tracked, and managed throughout the year.
Download Your SOC 2 Risk Assessment Template
How to Perform a SOC 2 Risk Assessment (5 Simple Steps)
SOC 2 risk assessment is a critical step in your SOC 2 compliance journey. In a nutshell, it requires you to identify and assess the impact of various risks on your business, assign a likelihood of occurrence and potential impact, and deploy suitable mitigation measures (SOC 2 controls).
It’s easier said than done, however. As you would soon realize, the entire exercise is subjective; no two companies would have identical risks. Wondering what the requirements for risk assessment for SOC 2 are?

Here are the five steps to perform a SOC 2 Risk Assessment:
- Define your Business Objectives
- Identify In-Scope Systems
- Perform Risk Analysis
- Document Risk Responses
- Stay Consistent
Step 1: Define your business objectives
The first step is to define your business objectives clearly. These are to your customers. These commitments are typically outlined in contracts, Service Level Agreements (SLAs), and publicly available materials, such as your website, brochures, and product documentation.
You should also factor in your selected Trust Services Criteria (TSC) and align your objectives with the promises made under each criterion. For example, if your organization handles sensitive client data under an NDA or commits to deleting data after service completion, your risk assessment should focus strongly on maintaining data confidentiality and security.
In such cases, organizations typically include the Confidentiality criterion in their SOC 2 scope because it directly supports the commitments made regarding the protection of sensitive data. Security (Common Criteria) is mandatory for every SOC 2 audit, so it must always be included as a core business objective during the risk assessment process.
Set up controls based on your business objectives. Take our expert’s advice.
Step 2: Identify critical systems
The next step is to identify the critical systems that enable your organization to serve its customers effectively. You can sift through the essential elements of various verticals, including infrastructure, software, data, people, and procedures, among others. For instance, if you sell software-as-a-service, your production system would be critical, and non-production systems would not be.
Make an inventory of the critical systems that dovetail with the scope (TSCs) you have defined for your SOC 2 audit. This step is crucial for removing unnecessary bloat from your SOC 2 audit.
The systems you identify as ‘in-scope’ now would be tested for the design and operating effectiveness of the controls you deploy to mitigate risks during your SOC 2 audit. But more on that later. Also check out: How much does a SOC 2 audit cost
Step 3: Perform risk analysis
In the first two steps, you identified your critical systems based on business objectives and selected TSCs. The next step is to map all business-specific and inherent risks that could disrupt your operations. These risks can arise from vendors, employees, regulatory changes, leadership changes, or shifts in economic, physical, and technological environments.
For example, if you process payroll for North American clients, any regulatory change in the United States can affect your service delivery. Similarly, cloud-hosted companies commonly face risks related to fraud, data security, and vendor management. Fraud risk assessment is also closely reviewed in SOC 2 audits, which include identifying risks related to conflicts of interest, bribery, or employees receiving improper gifts.
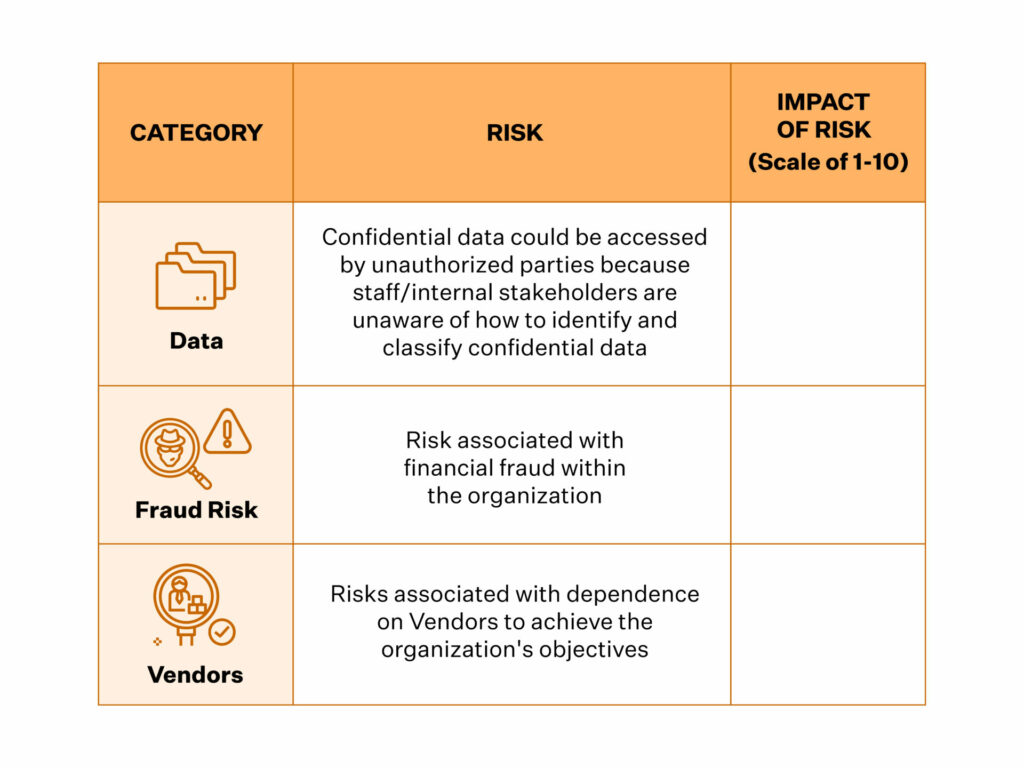
Your risk universe may include categories such as vendor risk, fraud risk, security incidents, production infrastructure, physical security, data risks, endpoint security, and people-related risks. Once identified, the next step is to rank only the risks that are critical to your business. A simple method is to list each risk category, the specific risks associated with it, and the impact on your commitments under the chosen Trust Services Criteria.
Risks can be rated on a scale of 1 to 10 based on likelihood and potential impact, such as legal, regulatory, financial, or reputational damage. While assigning impact ratings, consider both the speed at which the effect would be felt and the probability of the risk occurring.
Analyze compliance risk automatically with the help of Sprinto. Talk to our experts
Step 4: Document risk responses
Now that you have assessed the risks and assigned an impact, the next step is to incorporate risk mitigation plans and responses. For SOC 2 compliance, you must map the controls (based on chosen TSCs) to your various identified risks. The controls should help mitigate the risk impact and outline your risk response plan as well.
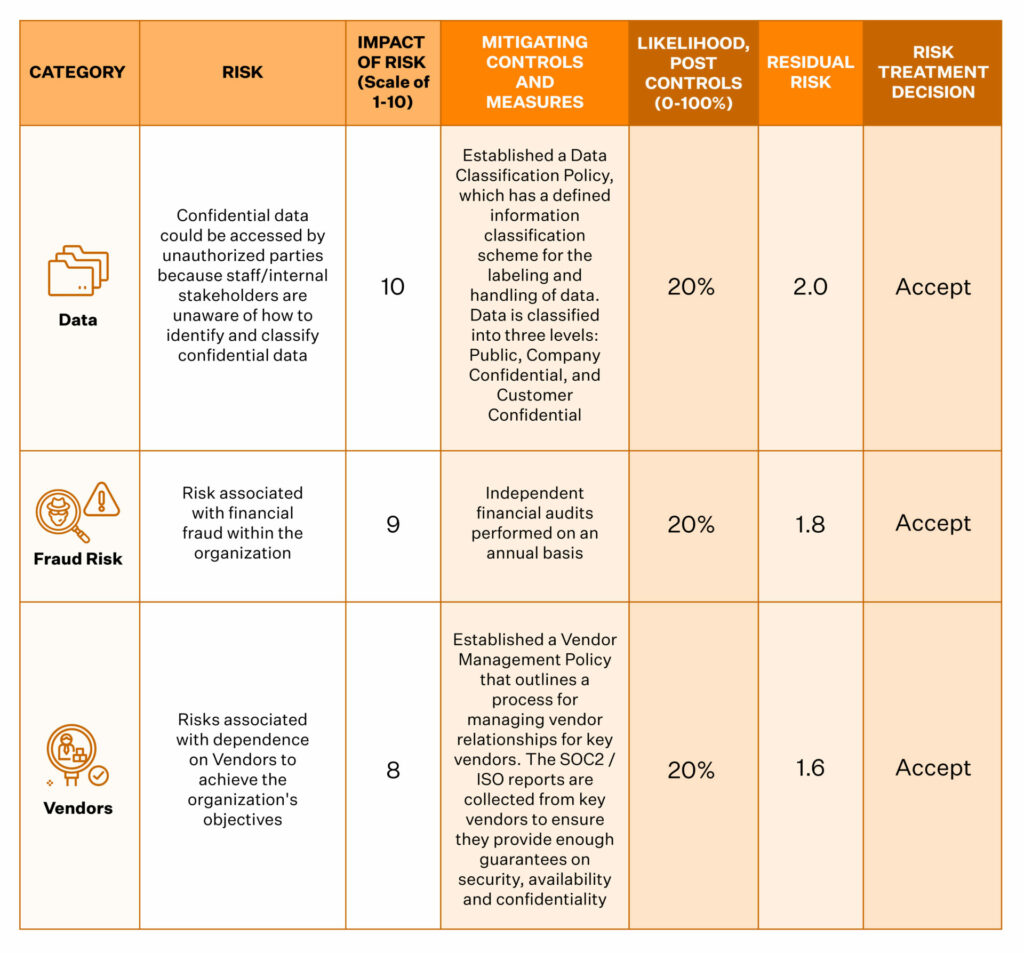
Documentation is the devil here. So, remember to document the risk treatment plan. While you won’t be able to eliminate risks, your documentation on what should be done in the event of any such eventuality will hold you in good standing during the audit.
Documentation should also include the periodicity of the control evaluations and the person responsible for conducting them. Conduct an internal audit of your controls, essentially a dry run, to identify any glaring gaps in the process.
During this stage, you also identify any control gaps in the design or operating effectiveness of your existing controls and document your remediation plan.
Step 5: Stay consistent
Risk assessment is not a one-time event; it is an ongoing process. You must undertake a risk assessment at least once a year, in the event of a significant event that alters your risk quotient or when new risks are identified. Remember, SOC 2 audits are an annual event, and you will be asked to share evidence of how you identify, assess, monitor, analyze, and avoid potential impact from your identified risk universe in every audit.
Criteria to consider during a SOC 2 risk assessment
As we mentioned, your risk assessment process is based on the SOC 2 criteria you have chosen. Popularly known as the Trust Service Principles or Trust Service Criteria, the five criteria listed here are what your organization will be evaluated on during your SOC 2 audit.

Security, Availability, Confidentiality, Processing Integrity, and Privacy – each focuses on a specific area, describing a set of compliance objectives your business must meet with the help of controls.
Selecting the relevant TSCs is one of the first steps in your SOC 2 compliance journey. With a clearly stated objective and scope of the audit, your risk assessment will be much more focused and relevant.
For instance, if your organization only chooses security in its scope for the audit, your risk assessment must focus on the line items that add to your security risks alone. You don’t need to rank all the identified risks in your universe.
Your risk assessments should be able to grow with your business. For instance, you may have implemented SOC 2 controls in the seed stage solely for meeting standard criteria. But as you grow, there is a high likelihood of you adding more TSCs to your scope. Your risk assessment should accommodate such changes wholly by establishing mature controls, performing regular monitoring activities, and holding quarterly risk meetings.
Also check out: SOC 2 controls
Get Our Practical SOC 2 Guide;
Yours at No Cost

What strategies can help evaluate SOC 2 risk assessment?
As we mentioned earlier, no two companies will have identical risks. And therefore, there are no surefire strategies. Besides, risk assessment is a subjective exercise. Hence, it’s advisable to involve your organization’s top management.
Your risk strategy will be based on your management’s decision to do either of the following:

Your risk strategy will be based on your management’s decision to do either of the following:
Creating a Mitigation Plan
A mitigation plan outlines how you will reduce the likelihood or impact of your identified risks. Once you have assessed and ranked risks, map relevant SOC 2 controls to each one and document how these controls reduce residual risk.
For example, if your live production database could become unavailable or corrupted, you might implement daily backups, redundancy across zones, and continuous monitoring to keep the risk within acceptable limits.
A well-designed mitigation plan aligns your critical risks with SOC 2 controls, ensuring that the remaining (residual) risk does not compromise business continuity.
Common SOC 2 Risk Assessment Mistakes to Avoid
Even well-prepared teams slip up during SOC 2 risk assessments. Avoiding these common mistakes can significantly improve the accuracy and effectiveness of your evaluation:
1. Treating risk assessment as a one-time activity
Many organizations perform a risk assessment only before the audit. SOC 2 requires ongoing monitoring, annual reviews, and updates to be implemented when new risks emerge or environments change.
2. Including too many systems or risks in scope
Adding every system, tool, or low-impact risk leads to unnecessary bloat and effort. Focus only on the assets and risks that materially affect your selected Trust Services Criteria.
3. Missing input from key stakeholders
Risk assessment becomes incomplete when engineering, security, product, and leadership teams are not involved in the process. Each function has unique insights into threats, dependencies, and real operational risks.
4. Poor documentation of risk responses
Controls may exist, but if documentation is weak or inconsistent, auditors treat it as a control gap. Clearly record mitigation plans, control owners, periodicity, and evidence expectations.
5. Not mapping risks correctly to SOC 2 controls
A common mistake is assigning generic controls that don’t actually reduce a specific risk. Each risk should be tied to the proper SOC 2 criteria and corresponding controls to demonstrate effective mitigation.
Risk Assessment vs Risk Management in SOC 2 Compliance
Risk management is the overarching umbrella for risk. It helps you address loss exposures and monitor your risk controls. Risk evaluation is a critical subset of this. It enables you to identify, evaluate, and report on any risk-related concerns.
For instance, risk evaluation will highlight the risk of your organization’s live database being unavailable. Risk management will help you actively manage and design an action plan such as daily data backups, hosting in multiple zones, using redundant network architecture, and vigorously monitoring system performance.
SOC2 risk assessment with Sprinto
Sprinto now offers a fully integrated risk assessment feature on its platform. It intelligently maps your risks, allowing you to choose the kind of SOC 2 risk assessment template you want. Your risks get added automatically thereafter. You only need to modify the values of each risk based on what holds true for your organization. Sprinto also suggests the average risk parameters for your industry for each identified risk.
Sprinto makes it easy to create a management review of the risk assessment, alerting the executive team for its timely review and approval. It then tabulates it all on the Auditor’s Dashboard, giving your auditor an overview of your risk universe, risk profile, and your risk mitigation plans with evidence.
Speak to our experts for a lowdown on how you can benefit from this smart feature. Book a demo today!
Frequently Asked Questions on SOC 2 Risk Assessment
A SOC 2 risk assessment is the process of identifying, analyzing, and prioritizing risks that could impact your organization’s systems, data, and compliance with the SOC 2 Trust Services Criteria. It helps you understand where vulnerabilities exist and what controls are needed to mitigate them.
A SOC 2 risk assessment is essential because it helps organizations identify and address security, operational, and compliance risks before they impact customers or service delivery. It ensures your controls align with SOC 2 requirements and reduces the chance of audit findings or control gaps.
The core components of a SOC 2 risk assessment include:
-> Defining business objectives
-> Identifying in-scope systems and assets
-> Listing threats and vulnerabilities
-> Assigning likelihood and impact scores
-> Mapping risks to SOC 2 controls
-> Documenting mitigation plans and responses
The SOC 2 risk assessment typically follows five steps:
1. Define business objectives
2. Identify critical in-scope systems
3. Perform risk analysis
4. Document risk responses and mitigation actions
5. Review and update the evaluation consistently
Yes. SOC 2 risk assessments are crucial because they help organizations stay ahead of emerging threats, strengthen their security posture, avoid audit gaps, and maintain continuous compliance. Auditors expect to see a documented, repeatable assessment in every SOC 2 cycle.
A SOC 2 risk assessment should be conducted:
-> At least once every year
-> Whenever your environment changes significantly (new tools, vendors, policies, or architecture)
-> When new risks emerge
Regular updates demonstrate continuous monitoring, which is a core SOC 2 requirement.

Author
Srividhya Karthik
Srividhya Karthik, is a Content Lead at Sprinto, she artfully transforms the complex world of compliance into accessible and intriguing reads. Srividhya has half a decade of experience under her belt in the compliance world across frameworks such as SOC 2, ISO 27001, GDPR and more. She is a formidable authority in the domain and guides readers with expertise and clarity.Explore more SOC 2 articles
SOC 2 Compliance Overview
SOC 2 Preparation and Documentation
SOC 2 Audit and
Reporting
SOC 2 Differences and Similarities
SOC 2 Updates & Management
SOC 2 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.