TL,DR:
| An audit log is a sequential record capturing event time, responsible users, and impacted entities across 7 categories: user activity, access control changes, data changes, system events, configuration changes, security incidents, and custom events |
| Audit logs are essential for compliance with SOC 2, ISO 27001, HIPAA, and PCI DSS, all requiring documented evidence of access monitoring and event tracking |
| Best practices include defining clear logging policies, enabling real-time anomaly alerts, establishing retention periods aligned to regulations, and maintaining tamper-proof storage with restricted access |
Transparency and visibility enhance the flexibility and resilience of a cybersecurity program. In the absence of audit logs, security professionals heavily relied on manual records and periodic review reports as their watchful eyes. However, as threats advanced, the demand for real-time updates increased and necessitated an automated and continuous system of tracking activities. Enter audit logs.
Audit logs diligently track and document every user activity offering real-time traces of suspicious behaviour that help initiate faster responses. Audit log entries are a crucial resource during security incident investigations. Audit management software centralizes these logs alongside control evidence and audit workflows, making them immediately accessible when auditors or incident responders need them
Read on to learn more about the basics of audit logging and the implementation of audit logs.
What is an audit log?
An audit log is a sequential record of events or actions taken by users to change or update controls pertaining to security and compliance. It contains details on time of the event, users who carried out the changes and the entities impacted.
An example of such actions may include org-wide system updates, changes on access control settings or policy updates.
Activities you can track under audit logs
Activities tracked under audit logs help security teams understand system modifications, data access, and suspicious events – and they provide the visibility a compliance audit relies on. Auditors typically request log samples for the specific user actions tied to each control they’re testing, so the quality of the logging program directly shapes how long an audit takes to clear.
Following is the list of activities that you can track under audit logging:
User activity
An audit log records user logins and logouts and other user actions such as authentication attempts, creation of a new user account or deletion of an account, password modification by users etc.
Access control changes
The log captures failed login attempts to track unauthorized access, permission changes, elevated privileges, role modifications, access revocation, access policy changes etc.
Data changes
It documents any changes made to data records including deletion, modification etc, entries related to data exporting or downloading, data ownership changes, bulk actions, etc.
System events
Audit logs record system events such as system startup, shutdown, performance changes, troubleshooting issues, and other system changes.
Configuration changes
The log indexes any changes to the application, network connection, or web server configurations, modifications to backup and recovery settings, system updates, and patch installations, among other configuration changes.
Security incidents
Audit logs notify of any changes to firewalls, intrusion detection events, malware or virus detection, data exfiltration events, and any other security incidents.
Custom events
Custom event records vary based on organizational needs. Depending on the events defined, the logs can capture any application-specific events, integration events, regulatory compliance events, and more.
Breeze through your audit logs
How to implement an audit log?
The ultimate goal of implementing audit logs is to quickly search for uncommon events in case of a security event and analyze them for future protection. You must jot down the logging requirements and choose a tool accordingly.
Here’s how to implement an audit log:
- Define requirements
Start with identifying the events that must be logged such as authentication attempts, configuration changes etc., and the level of details that must be included. Assess the regulatory requirements the organization is subject to and conduct a preliminary risk assessment to identify loopholes. Make your selection based on the framework audit requirements and the risk profile.
- Choose an audit logging tool
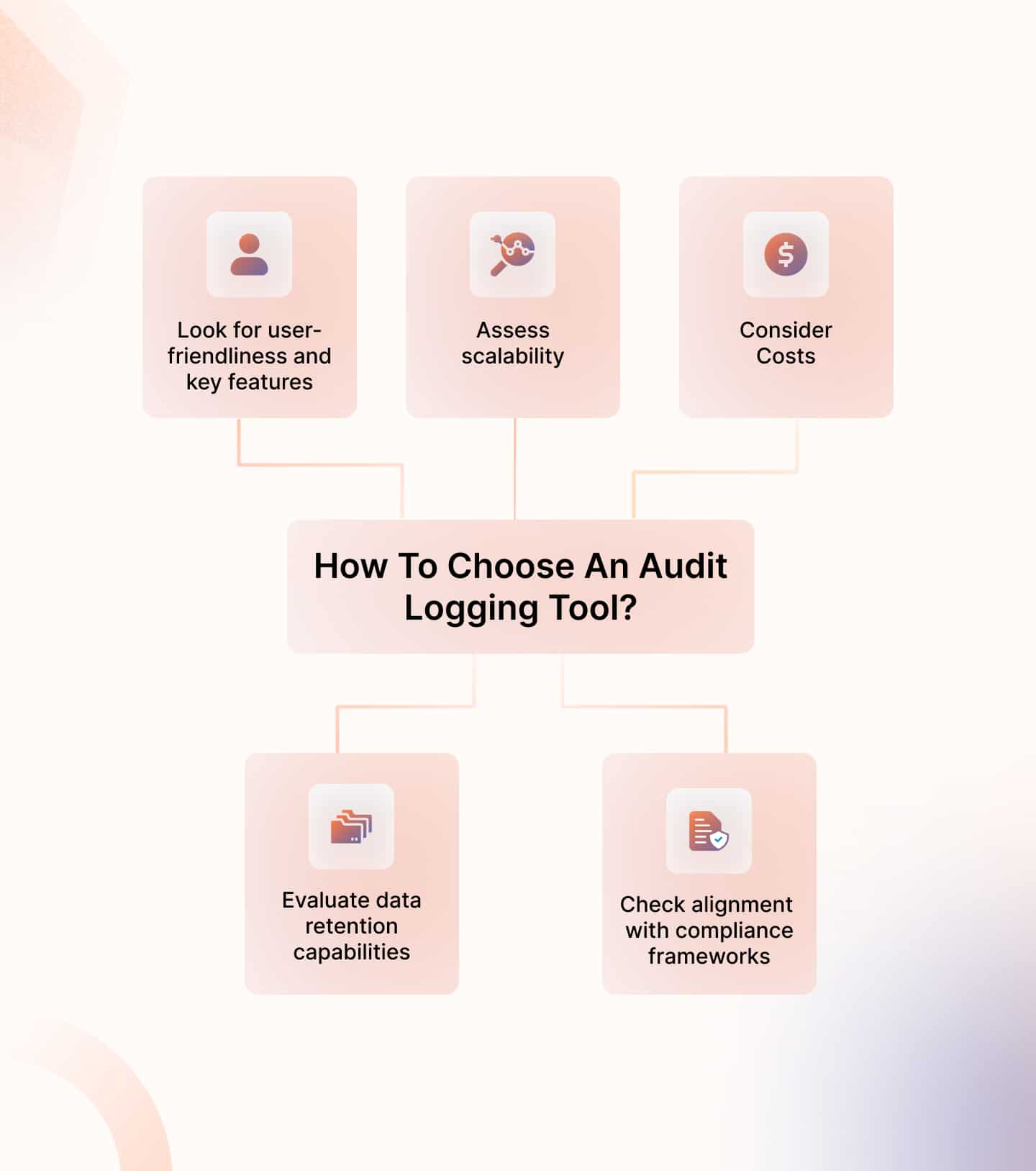
Explore available audit logging tool options and assess compatibility with organization needs. The tool selection must be based on:
Features: Evaluate the friendliness of the user interface and product capabilities such as visualization and dashboards, search and query ease, real-time monitoring and notifications etc.
Scalability: Assess the tool’s capability to handle large logs rapidly to ensure scalability and growth.
Cost: Compare total costs with other competing tools and evaluate if the tool fits your budget.
Data retention capabilities: ask about the number of days data is retained, since access to historical data is what makes evidence collection work in the first place – most frameworks expect to see at least 12 months of log evidence on demand, and the retention setting on your logging tool is what determines whether you can actually produce it.
Compliance: Check alignment with regulatory requirements you are subject to. - Integrate and configure
Integrate the chosen tool with your application/software and start configuring the log formats as per your specialized needs. Get the teams onboard with the new tool and run a test log to validate the configuration and setup. It is usually recommended to encrypt these logs and set access controls to protect the integrity of information.
- Documentation and training
Create policies and documentation for stakeholders to ensure standardized practices for audit logging. Arrange workforce training to equip the team with the knowledge and skills to interpret and analyze audit logs.
- Monitor and maintain
Establish a monitoring mechanism to ensure audit logs are working as intended. Conduct frequent internal audits to validate the accuracy of audit logs and obtain insights from the entries. Periodically update policies based on these insights and strengthen your internal controls.
Continuously monitor all controls
Best practices for audit logging
Audit logging best practices revolve around defining clear policies around audit log maintenance, storage, protection, and retention. You must regularly review audit logs to ensure comprehensive security and adherence to best practices.
Here are 4 best practices for audit logging:

Store logs in an encrypted format
Encrypt audit log data to protect data at rest and in transit. Encryption is a key requirement for various data protection regulations to safeguard sensitive information and secure storage. It also prevents insider threats and unauthorized transmission.
Define retention periods
Minimize the storage costs of audit logs by defining clear audit log retention policies and freeing up space. Critical information subject to regulatory requirements may be required to be stored for anywhere between 6 months to 7 years, depending on the applicable framework. However, shorter retention periods such as 90 days may be deemed sufficient for other less critical events.
Implement access controls
Set access permissions to limit access to stakeholders working in audit-related functions and protect the integrity of access logs. Follow the principle of least privilege and leverage identity and access management tools to minimize unauthorized access and tampering with audit logs.
Ensure regular backups
Regular backups are generally a cybersecurity best practice to prevent accidental data loss. Audit logs can be backed up in databases to restore them in case of a security incident and preserve evidence for investigations and root cause analysis.
Challenges of implementing audit logs
One of the biggest challenges of audit logs is narrowing down the scope of events to be logged. Especially for large-scale organizations, it is crucial to select what must be logged to minimize associated difficulties like storage costs and inadequate visibility. Most teams resolve this during audit preparation: working backwards from the controls being tested makes it obvious which event types must be logged and which can be safely filtered out before they bloat retention.
Have a look at these challenges of implementing audit logs:

Massive amount of data
Organizations dealing with high-volume data find storing and managing audit logs difficult. Excessive data brings challenges such as significant resource consumption, bandwidth issues, delays in data transfers, and difficulties in real-time analysis.
Log retention
Another major challenge is decisions related to log retention. More often than not, organizations subject to compliance requirements need to retain audit logs for a fixed period. For example, in the case of HIPAA, the log retention period is 6 years. But this means increased storage costs and excess financial burden on the organization.
Varying log formats
The records collected across various systems, applications, and networks may have different formats. Lack of standardization can make it difficult to correlate events and conduct an in-depth analysis of events across the environment.
Visibility gaps
If the organization operates in a complex and distributed environment, it must narrow the scope of recording events because of resource constraints. As a result, there are visibility gaps across the IT infrastructure leading to limited context for key decisions.
Maintaining log integrity
Ensuring log integrity is itself a challenge in this dynamic and complex environment. There are dangers of insider threats, privilege escalation, log tampering incidents, inadequate security controls and other such events.
3 Best audit logs tool for security and compliance
Audit logging tools for security and compliance automate security monitoring, facilitate proactive incident response, and make accountability management easier.
Here are our top 3 tool recommendations:
Sprinto
Sprinto is a compliance automation platform that can streamline workflows related to compliance and auditing. It enables admins to track user activities that can impact organizational security and compliance and download evidence for audit purposes.
Top features:
Granular level monitoring: Sprinto enables continuous security and compliance monitoring at a granular level and raises automated alerts for deviations. You do not need to manually search logs to analyze which events caused the incident because it provides enough context.
Activity details: Sprinto empowers admins to see activity details performed by different users along with time, date and description.
Role-based access management: The platform supports role-based access controls and only authorized individuals track and access user activities.
Evidence of adherence: Automated checks are run throughout the day and the auditor can download evidence for any security or compliance activity at any given point in time.
Policy templates and enforcement: The platform provides in-built policy templates that you can customize based on audit needs and it can also automatically enforce these policies.
Besides these, you can expand the scope of your compliance program with training modules, real-time dashboards, integrated risk assessments, complementary security profiles page and more.
Frontegg
Frontegg is a user management platform that automatically traces every user action and provides flexible audit log models to choose from. It additionally manages authentication and provides insight into user access while ensuring alignment with industry regulations.
Features:
SIEM integration: The platform integrates with SIEM tools to enable you to export data and correlate it across other enterprise data easily.
Scalability: The product supports multi-tenant audit logs, enabling infrastructure sharing among multiple users while keeping data protected from each other.
Customization: The solution lets you customize your audit logs and decide the type of data that must be included while enabling features of your choice
Centralized management: Frontegg features centralized management of users and accounts for ease of use and optimum resource utilization.
Splunk
Splunk is a versatile platform with log management and analysis capabilities that can collect, search and analyze audit logs. It enables real-time monitoring of events to raise alerts in case of anomalous behaviour and helps interpret log data.
Features:
Proactive monitoring and alerts: Splunk continuously tracks user activity and raises alerts upon deviations from predefined criteria.
Visualization and correlation: The platform correlates data from multiple sources and supports visualization tools for better interpretation.
Log data search and analysis: It indexes log data across various sources to enable swift audit log searches and analysis.
Data protection: The solution helps protect data integrity by displaying events and event counts with sensitive information to implement controls.
Track security and compliance deviations with Sprinto
Audit logging tools are crucial sources of visibility, providing insights into user activities. However,you need more than just audit logging records to ensure all-round security and compliance. Organizations, therefore, rely on a combination of tools or comprehensive solutions like Sprinto to achieve a state of continuous resilience and readiness.
Sprinto can help you pinpoint security and compliance gaps and implement airtight controls that can make you audit-ready in weeks. The platform runs automated daily checks and helps you define an internal audit window. Just take timely action to get to >90% mark and ensure audit readiness in weeks instead of months.
Want to get certified quickly and unlock better business? Speak to a compliance expert today.
FAQs
An audit log is a specific, detailed, and timestamped record for security-related events while an audit trail is a series of audit logs but with more detail. Audit trails are comprehensive and provide more contextual information.
Audit logs are used to identify suspicious behavior, comply with regulatory requirements, conduct forensic analysis, and establish user accountability.
Critical systems and events should be monitored in real-time and for other events you can have periodic reviews such as monthly or quarterly assessments based on business requirements.
Effective audit logs should include timestamps, user identity, action performed, affected resource, source IP/device, outcome status, and session details to support security monitoring and investigations. They should also be centralized, tamper-resistant, and regularly monitored to maintain compliance and forensic integrity.
Author
Payal Wadhwa
Payal is your friendly neighborhood compliance whiz who is also ISC2 certified! She turns perplexing compliance lingo into actionable advice about keeping your digital business safe and savvy. When she isn’t saving virtual worlds, she’s penning down poetic musings or lighting up local open mics. Cyber savvy by day, poet by night!Explore more
research & insights curated to help you earn a seat at the table.