For any fast-growing company, a strong security and compliance foundation is never built in the audit season. It’s built through continuous, structured gap analysis that keeps controls healthy, teams aligned, and surprises off the audit report.
A missed access revocation, a dormant control, an outdated policy, or an unnoticed vendor lapse can quietly accumulate until they surface as costly problems or customer concerns. A compliance gap analysis helps teams uncover these weaknesses early.
This blog breaks down the five core steps of a compliance gap analysis and the strategic decisions involved, including whether to run manual reviews or automated assessments.
What is a compliance gap analysis?
Compliance gap analysis is the process of evaluating an organization’s current security, privacy, or regulatory posture against the requirements of a specific compliance framework such as SOC 2, ISO 27001, HIPAA, or GDPR, to identify areas where the organization falls short.
A compliance gap exercise helps businesses detect missing or inefficient controls, prioritize remediation efforts, and minimize risks of fines and penalties before an external audit.
Why conduct a compliance gap analysis?
Every organization, regardless of it’s size must conduct compliance gap analysis to strengthen audit readiness, prioritize risk remediation and ensure smooth compliance operations as the business grows.
Here are the key benefits of a compliance gap analysis:
Audit Impact
A compliance gap analysis helps teams identify missing, outdated, or misaligned controls before an external auditor flags them as formal observations. Without this step, organizations face delays, repeated audit cycles, and avoidable findings that can erode customer and partner trust. Gap analysis ensures you enter an audit with clarity and confidence instead of surprises.
Strategic Benefits
Beyond audit readiness, a gap analysis shifts teams from a reactive to a proactive compliance posture. It highlights high-risk areas, prioritizes remediation, and reveals which controls can be reused across frameworks, reducing duplication and unnecessary work. This strategic visibility helps SMBs plan compliance investments more intelligently and avoid over-scoping efforts.
Operational Efficiency
Compliance isn’t set-and-forget. Controls drift, risks evolve, and frameworks change. Many teams still assume their cloud provider fully covers compliance or treat it as a one-time project, which creates blind spots. A recurring gap analysis transforms compliance into an ongoing operational practice, helping teams maintain alignment, catch issues early, and turn compliance into a sustained business advantage rather than a periodic scramble.
Compliance frameworks that expect you to run a gap analysis
Nearly every major security and privacy framework expects some form of self-assessment or readiness check before a formal audit. A compliance gap analysis is the starting point to meet that expectation. While each framework has its nuances, they all require a clear understanding of the current control state and the state of required controls.
Here are some of the most widely adopted compliance frameworks where a gap analysis is critical:
- SOC 2 focuses on internal controls related to security, availability, confidentiality, processing integrity, and privacy. Conducting a gap analysis helps organizations identify which Trust Services Criteria (TSC) are not fully addressed and highlights missing or insufficient evidence that could lead to audit issues.
- ISO 27001 requires organizations to perform a formal risk assessment and define a Statement of Applicability. A compliance gap analysis ensures that existing policies and technical controls are aligned with ISO’s Annex A requirements and the broader Information Security Management System (ISMS) framework.
- HIPAA mandates rigorous administrative, physical, and technical safeguards to protect healthcare data. A gap analysis helps healthcare organizations and their partners assess compliance with the Privacy Rule, Security Rule, and Breach Notification Rule, reducing the risk of violations and penalties.
- GDPR governs how organizations handle the personal data of individuals in the EU. A gap analysis in this context uncovers deficiencies in areas such as data processing, user consent, breach notification procedures, and data subject rights, helping ensure compliance with one of the world’s strictest privacy laws.
- PCI-DSS applies to any business that processes, stores, or transmits credit card data. A gap analysis identifies control failures or missing safeguards in encryption, access control, vulnerability management, and audit logging—any of which could result in non-compliance and financial penalties.
- NIST 800-53 / NIST Cybersecurity Framework (CSF) is widely used in government agencies and critical infrastructure sectors. These frameworks require extensive documentation and operational controls, and a gap analysis ensures alignment with federal security standards and risk management practices.
How to perform a compliance gap analysis?
A compliance gap analysis is performed by comparing your current controls and processes against the requirements of a chosen framework to identify what’s missing, weak, or undocumented. It may be performed by internal teams or external partners.
Here’s a step-by-step breakdown of how to conduct a compliance gap analysis:
1. Define the framework scope and objectives
Begin by selecting the specific compliance framework or regulation to assess, such as SOC 2, ISO 27001, HIPAA, GDPR, or PCI DSS. This framework sets the benchmark for the gap analysis. Then, establish clear boundaries for the analysis. This includes outlining which business units, systems, processes, and policies fall within scope.
It’s also essential to document the objective of the exercise, whether that involves preparing for a certification audit, responding to new regulatory requirements, or building the foundation for a long-term compliance program.
2. Assess the current state
Once the scope is defined, the next step is to document how your organization currently operates in relation to the chosen compliance framework. This involves gathering existing policies, SOPs, system configurations, risk registers, and any previous audit findings or assessments.
It is also important to go beyond the paperwork. Interview key stakeholders across IT, HR, Security, and other functions to understand how processes actually run. Conduct technical reviews to verify whether controls are functioning as intended and generating the required evidence. This assessment forms the baseline for identifying control gaps and prioritizing remediation.
3. Identify and document compliance gaps
Once the current state is mapped, compare it directly against the requirements of the selected framework. This exercise will help you identify three types of gaps:
- Missing controls: A required policy, process, or safeguard is not in place.
- Inadequate controls: A control exists but is outdated, incomplete, or not enforced effectively.
- Lack of evidence/documentation: The control is in place, but there’s no audit-ready proof that it’s functioning.
Each identified gap should be clearly documented with its associated risk level, audit impact, and functional owner. This creates a prioritized remediation list to guide the next phase of action.
4. Prioritize gaps and plan remediation
Not all gaps are equal. Once documented, categorize them based on factors like risk severity, audit criticality, and implementation effort. Start with high-risk gaps that could result in audit failures, data exposure, or legal non-compliance. Then, tackle medium- and low-priority issues in a phased manner.
Document all findings in a formal gap analysis report. This serves as a single source of truth for leadership, auditors, and implementation teams.
Next, define a measurable success criterion, assign ownership, allocate resources, and set clear deadlines for each gap. Your remediation plan should also outline required policy updates, tool implementations (such as MDM, IAM, or logging systems), employee training, and process documentation. Use these inputs to create a tactical remediation plan that’s aligned with business priorities.
5. Follow up and monitor continuously
After the implementation of the remediation plan, each fix needs to be validated to ensure it’s working properly and producing the required evidence for audits. This may involve control testing, reviewing audit logs, or analyzing system output to confirm effectiveness.
Establish ongoing monitoring practices to maintain compliance over time. Set up internal check-ins, automate alerts for control failures, and periodically revisit your gap analysis as systems, teams, and frameworks evolve. This continuous oversight transforms compliance from a point-in-time exercise into a repeatable and resilient business process.
Putting it all together: Working examples
1. SOC 2 gap analysis
Imagine a growing SaaS company preparing for its first SOC 2 Type II audit. During a routine gap analysis, they discover that while Multi-Factor Authentication (MFA) is enabled across most systems, it hasn’t been rolled out to internal developer tools. The control technically exists but is not enforced universally. This is a classic case of a partially implemented control.
In the gap analysis report, this is logged as a high-risk gap. The remediation plan includes rolling out MFA to the remaining tools, updating the access control policy, and capturing screenshots and logs as audit evidence. A security engineer is assigned to own the fix, with a two-week deadline. The team tracks progress via weekly check-ins and adds the control to their ongoing monitoring checklist to prevent regression.
2. HIPAA gap analysis
The table below shows how a HIPAA-regulated entity fared during an actual compliance gap assessment. Despite having policies and procedures (P&Ps) documented, implementation gaps led to multiple areas being flagged as ‘Not Compliant.’
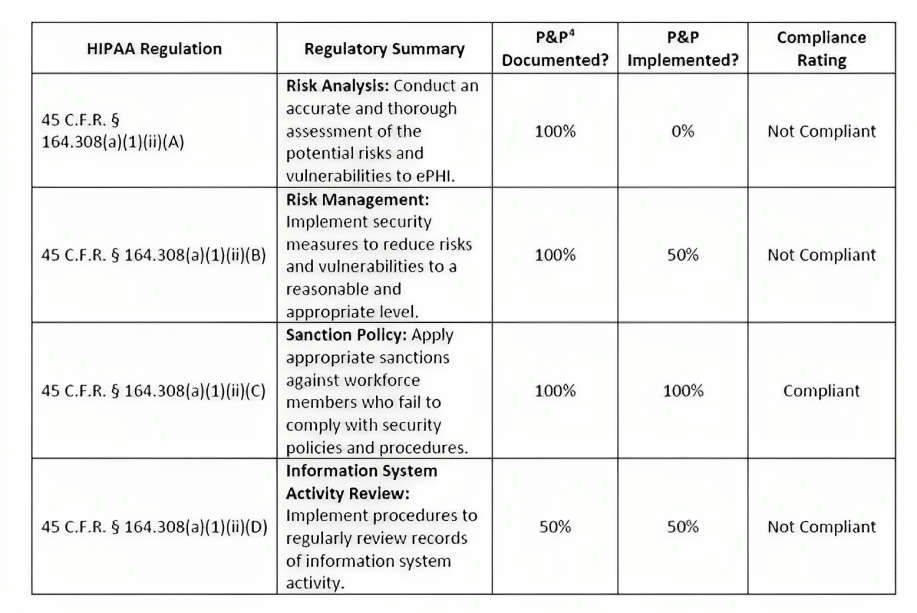
- Unencrypted emails containing PHI
Violates HIPAA’s Privacy Rule (45 CFR 164.502) and Security Rule (Technical Safeguards)
- Improper disposal of paper records containing PHI
Violates HIPAA’s Privacy Rule (45 CFR 164.310) and Security Rule (Physical Safeguards)
Manual vs automated gap analysis: Which approach scales
Manual gap analysis is how most companies start. It typically involves spreadsheets, interviews, and internal audits to assess whether controls align with a specific compliance framework. While useful for one-time audits or early-stage readiness, manual analysis is labor-intensive, highly subjective, and almost immediately outdated.
Automated gap analysis, on the other hand, is designed for scale and speed. It connects directly to your systems, policies, and processes to continuously monitor control health, flag gaps in real time, and collect audit-grade evidence along the way. It removes guesswork, reduces human error, and keeps your compliance posture current, even as your environment evolves.
| Aspect | Manual gap analysis | Automated gap analysis |
| Speed | Slow, resource-heavy | Fast, continuous |
| Accuracy | Prone to human error and oversight | System-verified, consistent |
| Evidence Collection | Manual, decentralized | Auto-collected, centralized |
| Scalability | Hard to scale across teams or frameworks | Built for scale and complexity |
| Monitoring | One-time snapshot | Real-time, continuous |
| Control Drift Detection | Only during audits or reviews | Immediate alerts on control failures |
| Stakeholder Dependency | High reliance on interviews and surveys | Lower reliance, higher system visibility |
| Remediation Planning | Ad hoc and often undocumented | Structured with ownership and deadlines |
| Framework Expansion | Redundant effort for each new framework | Controls can be reused and auto-mapped |
Manual gap analysis: Where it falls short
- Scope creep is common: Manual assessments often balloon in size and complexity without clear boundaries.
- Inconsistent Interpretation: Results vary heavily depending on the assessor’s experience and bias; introducing subjectivity weakens reliability.
- Evidence is fragmented: Tracking evidence across emails, folders, and tools creates audit risk.
- Stale data skews results. Compiling evidence and findings manually is time consuming and the environment may have changed while this is being done.
- Remediation lacks structure: Tasks often go undocumented, unassigned, or untracked, leading to missed deadlines.
- Regulatory drift: Every system, process, and control must be manually rechecked every time laws or regulations change.
Automated tools: What to be cautious about
- Automation does not equal autonomy: Some controls require human oversight, judgment, or manual evidence inputs.
- Misconfigured integrations lead to blind spots: Without proper setup, key systems may not be monitored.
- “Black Box” outputs: Some tools flag risks without explaining why, making it hard to investigate root causes or defend findings to auditors.
- Lack of customization can backfire: A rigid rules engine may not reflect how your business actually operates.
- Alert fatigue: Non-critical alerts can drown real issues.
- Cost complexity: Beyond licenses, teams often underestimate the setup, configuration, and maintenance effort required.
How can Sprinto help with compliance gap analysis?
Manual gap analysis is slow, error-prone, and disconnected from real operations. It relies on spreadsheets, interviews, and assumptions, often producing a static report that’s outdated the moment it’s done. It can’t scale across frameworks, lacks real-time visibility, and misses control drift until it’s too late. That’s where Sprinto steps in.
Sprinto turns the process into a dynamic, automated system that closes the loop between detection, remediation, and readiness.
- AI-powered gap detection: Identify missing, outdated, or misaligned evidence, controls, policies, and risks with no manual reviews required.
- Policy drift detection: Compare real-world configurations and practices against written policies to flag mismatches.
- Context-aware insights: Gain precise, entity-level gap visibility across policies, risks, vendors, evidence, and staff.
- Continuous compliance monitoring: Detect gaps as they emerge, including weak evidence, unmapped controls and outdated policies before they escalate.
- Evidence streamlined: Validate uploaded evidence for relevance, freshness, and completeness so you’re always audit-ready with minimal effort.
- Guided remediation: Turn gaps into actionable tasks with AI-generated recommendations and structured updates across risks, policies, and vendors.
- Multi-framework consistency: Reuse existing controls, automatically map them to new frameworks, and highlight coverage gaps.
Read how Rocketlane put compliance on autopilot with Sprinto, saving 2 weeks of work across five frameworks.
Want to streamline compliance gap analysis? Talk to our expert.
FAQs
Gap analysis should not be a one-time project tied only to audit prep. For fast-moving or regulated businesses, it’s best to perform a structured analysis annually, with ongoing control monitoring in between. High-risk environments may require quarterly reviews.
Yes. By using a common controls framework or a compliance crosswalk, teams can map one set of controls to multiple standards like SOC 2, ISO 27001, and HIPAA. This approach dramatically reduces duplication of effort and simplifies multi-framework readiness.
It depends on your maturity. Early-stage companies often benefit from external compliance experts who bring audit experience and benchmarking context. More mature orgs with in-house GRC talent can lead the effort internally, especially when supported by automation.
They’re similar but not identical. A gap analysis is broader and diagnostic and is used to identify all missing or weak controls. A readiness assessment is often a pre-audit dry run, focused specifically on whether you’d pass an audit today.
Author
Payal Wadhwa
Payal is your friendly neighborhood compliance whiz who is also ISC2 certified! She turns perplexing compliance lingo into actionable advice about keeping your digital business safe and savvy. When she isn’t saving virtual worlds, she’s penning down poetic musings or lighting up local open mics. Cyber savvy by day, poet by night!Explore more
research & insights curated to help you earn a seat at the table.