TL;DR
| A compliance framework is a structured system of policies, controls, processes, and documentation that helps organizations meet regulatory, security, and customer requirements. |
| Frameworks like SOC 2, ISO 27001, HIPAA, GDPR, and PCI DSS differ in scope, rigor, and applicability, but share 60–90% control overlap, enabling efficient multi-framework adoption. |
| Implementing a framework requires a clear roadmap: scope → choose framework → gap assessment → implement controls → document → audit → maintain — and automation platforms like Sprinto dramatically reduce effort, risk, and audit fatigue. |
Compliance doesn’t seem urgent, until it is. Everything becomes real when a prospect asks if you’re SOC 2 ready or a deal slows down. Suddenly, you’re digging through scattered docs, second-guessing every file, and wondering if anything you have is actually correct. Notion pages multiply. Slack threads spiral. And despite everyone’s best intentions, the team still ends up asking, “Are we actually ready for an audit?” If this sounds familiar, you’re not alone, and that’s precisely why we have written this guide.
This guide helps you cut through the noise. It explains what a compliance framework is, breaks down key components, and shows how to implement one with clarity and confidence. You’ll learn how to pick the proper framework for your business, understand where frameworks overlap, and see how automation can reduce effort without losing control.
What is a compliance framework?
A compliance framework is a structured system of policies, procedures, and controls that helps an organization meet legal, regulatory, and industry-specific standards while managing operational and reputational risks. It serves as a roadmap for aligning business activities with required obligations and ethical standards, ensuring transparency and accountability across teams and systems.
By embedding processes like risk assessments, governance structures, employee training, and monitoring mechanisms, compliance frameworks support sustained, enterprise-wide adherence and prepare businesses for audits, certifications, and external scrutiny.
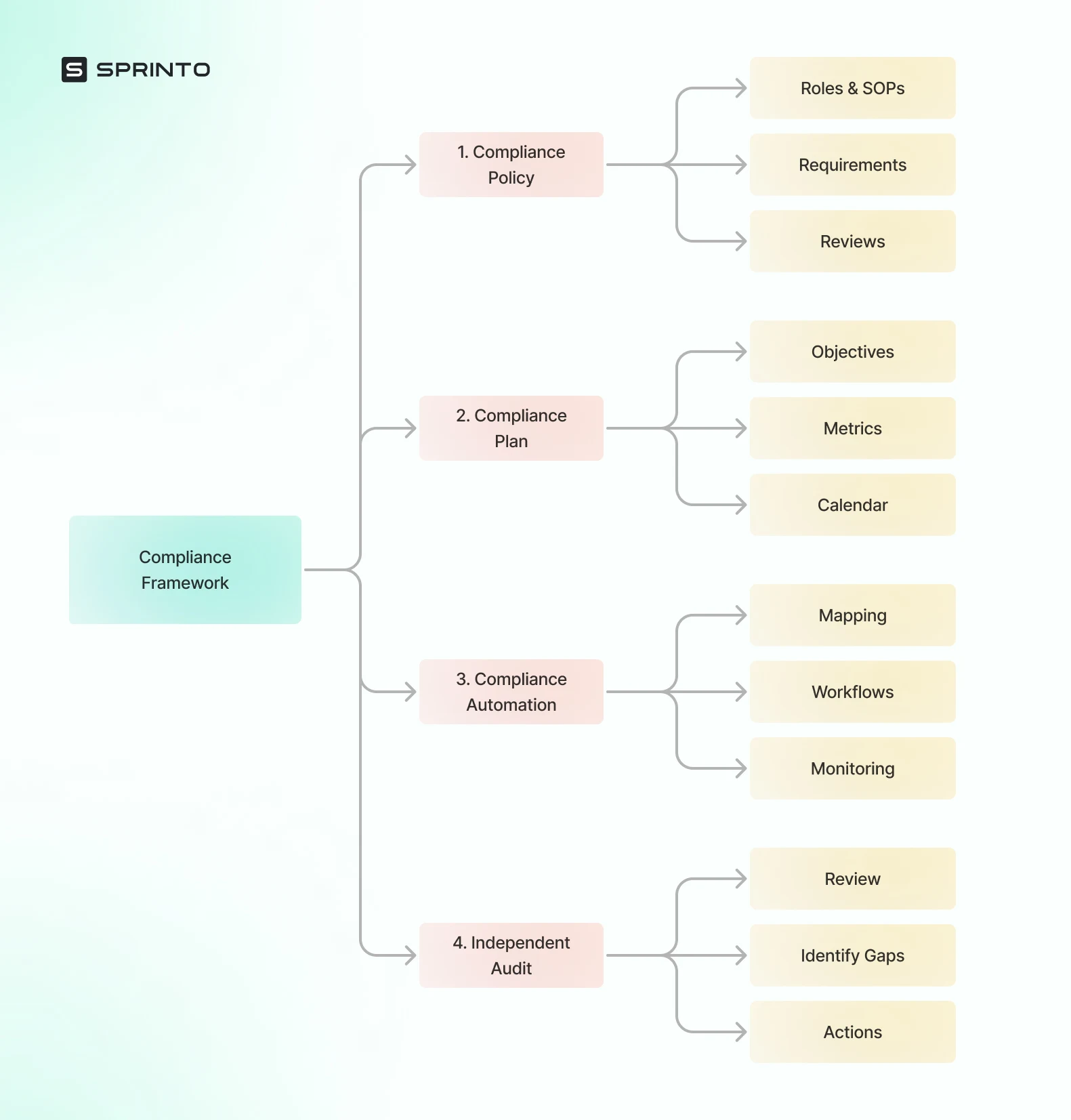
What does a compliance framework contain?
A compliance framework is a comprehensive system that connects requirements with actions, responsibilities, and evidence. To ensure alignment between regulatory expectations and operational practices, every framework includes a core set of components, which are:
- Requirements: These include specific rules, obligations, and expectations derived from laws, regulations, standards, or contractual agreements. Examples include GDPR clauses, HIPAA mandates, or SOC 2 Trust Services Criteria.
- Controls: Actionable measures that enforce compliance, including technical safeguards (like encryption), administrative policies (like access reviews), and physical security controls (like badge access).
- Processes: Defined workflows and day-to-day activities that ensure ongoing compliance — such as onboarding protocols, change management, or incident response.
- Documentation Rules: Expectations for Maintaining and Organizing Evidence. This includes audit logs, policy documents, training records, vendor contracts, and exception reports.
- Testing & Audit Expectations: Guidelines for performing regular internal checks, preparing for third-party audits, and addressing non-conformities. May include certification procedures, attestation cycles, or regulatory inspections.
Why do compliance frameworks matter
The growing complexity of regulatory environments makes it essential for organizations to adopt structured, reliable mechanisms to stay compliant. A compliance framework serves as this mechanism by integrating compliance into daily operations, mitigating risk, and facilitating growth.
Below are some key reasons why a compliance framework is essential for your business.
- Meet regulatory obligations: Ensure your organization complies with industry regulations, customer mandates, and legal requirements across regions.
- Standardize internal controls: Implement a uniform set of policies and procedures across departments, reducing discrepancies and ensuring consistency.
- Reduce audit pain: Cut down audit prep time with organized evidence, mapped controls, and consistent documentation.
- Build customer trust: Demonstrate to customers, partners, and investors that security and compliance are integral to your operating culture.
- Enable secure, scalable operations: Establish scalable processes that support security and compliance as your business grows or enters new markets.
Types of compliance frameworks (with examples)
Organizations don’t pick compliance frameworks just for fun. The choice usually comes down to what kind of data they access, who their customers are, and which regulators might come knocking, quietly or otherwise. Broadly speaking, most frameworks cluster into four buckets: security, privacy, industry-specific, and governance/risk.
Below is a practical walk-through of what each category actually covers, with examples you’ll hear about a lot (sometimes more than you’d like).
Security frameworks
Security frameworks are about one thing, really: keeping sensitive information out of the wrong hands. They focus on controls, processes, and habits that reduce the chances of breaches, leaks, or late-night incident calls.
- ISO 27001
Often treated as the global gold standard, ISO 27001 lays out how to build and maintain an Information Security Management System (ISMS). It’s structured, documented, and not exactly light reading, but it’s widely respected. Global organizations lean on it to show they’re serious and systematic about data security, not just winging it. - SOC 2
SOC 2 is especially popular (and frequently demanded) in the U.S. SaaS world. Instead of telling you what controls to implement, it evaluates how well you manage data against trust principles like security, availability, and confidentiality. Enterprise customers love asking for it, usually before contracts are signed. - NIST CSF
The NIST Cybersecurity Framework is more flexible, less audit-heavy, and often used as a starting point. Built around five core functions—Identify, Protect, Detect, Respond, Recover—it gives organizations a solid security baseline without forcing them into formal certification. Good for maturity-building, or when you need structure but not bureaucracy.
Privacy frameworks
Privacy frameworks zoom in on personal data—how it’s collected, used, stored, and, sometimes awkwardly, deleted. Consent, transparency, and individual rights are the main themes here.
- GDPR
The General Data Protection Regulation is an EU law with global reach. If you handle EU residents’ personal data, GDPR applies, whether you’re based in Berlin or Bangalore. It’s strict, detailed, and backed by serious fines, which is why companies tend to take it very seriously, eventually. - CCPA
The California Consumer Privacy Act gives California residents more control over their personal information. It’s especially relevant for U.S.-based consumer apps and eCommerce companies. Compared to GDPR, it’s narrower, but it still forces organizations to rethink how data is shared and disclosed. - ISO 27701
Think of ISO 27701 as ISO 27001’s privacy-focused sibling. It extends an existing ISMS into a Privacy Information Management System (PIMS). Companies already aligned with ISO 27001 often adopt it to cover privacy obligations without reinventing their entire compliance setup.
Industry-specific frameworks
Some industries don’t get a choice. These frameworks are mandatory, highly targeted, and usually enforced with audits that feel very real, very fast.
- PCI DSS
If you store, process, or transmit credit card data, PCI DSS is unavoidable. It applies to fintechs, payment processors, and eCommerce platforms alike. The requirements are technical, prescriptive, and updated regularly, often just when teams think they’re done. - HIPAA
HIPAA governs healthcare organizations and their vendors in the U.S., covering how Protected Health Information (PHI) is handled. It doesn’t just apply to hospitals; software providers and service partners (Business Associates) fall under its scope too, sometimes unexpectedly. - FedRAMP
Cloud providers that want to sell to U.S. federal agencies must go through FedRAMP. It enforces standardized security controls, deep risk assessments, and third-party authorization. The bar is high, the process is long, and the documentation stack grows fast. - DORA
The Digital Operational Resilience Act targets EU financial institutions, focusing on operational continuity and cyber resilience. It’s less about a single system and more about ensuring that financial services can survive disruptions, technical, third-party, or otherwise.
Governance & risk frameworks
Governance and risk frameworks sit slightly higher up the stack. They’re less about specific controls and more about alignment, making sure IT, risk, and business goals don’t drift in opposite directions.
- COSO
COSO centers on enterprise risk management and internal controls, especially around financial reporting. Large enterprises use it to create consistency and accountability across complex organizations, where small gaps can turn into big problems. - NIST RMF
The NIST Risk Management Framework is widely used by U.S. government agencies and contractors. It provides a structured way to identify, assess, and continuously manage risk across information systems—methodical, iterative, and very thorough. - COBIT
Developed by ISACA, COBIT helps organizations govern and manage IT in a way that balances compliance, risk, and performance. It’s often used when leadership wants visibility and control without turning IT into a compliance-only cost center.
Difference between major compliance frameworks
With numerous frameworks, it’s easy to become overwhelmed. This table simplifies your decision-making by comparing the most commonly adopted compliance frameworks across key dimensions, including who they apply to, what they focus on, and the rigor of their audit requirements.
| Framework | Category | Applies to | Focus Areas | Audit Requirement | Difficulty |
| ISO 27001 | Security | Global orgs | ISMS, risk-based controls | Certification audit | High |
| SOC 2 | Security | SaaS companies | Trust Services Criteria | Independent audit | Medium |
| NIST CSF | Cybersecurity | US/global | 5-function cybersecurity | None | Low |
| PCI DSS | Payments | Merchants, processors | Card data protection | Qualified assessor | High |
| HIPAA | Healthcare | Covered entities & BAs | PHI protection | Regulatory enforcement | Medium |
| GDPR | Privacy | Global | Consent, governance, data rights | Fines by regulators | High |
Key components of a compliance framework
Every compliance framework has several foundational components that work together to ensure regulatory alignment and operational discipline. These components provide structure, clarity, and accountability, allowing organizations to effectively manage risk and maintain a consistent compliance posture over time.
Policies & standards
These form the foundation of a compliance program. Policies outline what is expected in terms of security and behavior, while standards specify how those policies are to be implemented. Together, they create a formal structure for decision-making and ensure consistency across the organization.
Controls
Controls are the specific mechanisms implemented to fulfill the intent of policies. These include administrative controls (like access reviews), technical controls (such as encryption or MFA), and physical controls (like security badges or surveillance). Effective control implementation reduces the risk of security incidents and ensures compliance with relevant regulations and requirements.
Governance & roles
Transparent governance defines who owns what within the compliance framework. This includes establishing accountability, decision-making authority, and escalation paths. By assigning responsibilities, organizations can ensure compliance activities are managed proactively rather than reactively.
Documentation
Compliance is only as substantial as its documentation. This includes everything from policies and procedures to training logs, evidence repositories, and vendor contracts. Proper documentation supports audit readiness and provides a historical record of compliance actions.
Monitoring & continuous review
Ongoing monitoring ensures that controls remain effective and aligned with both internal policies and external regulations. This involves automated system checks, regular reviews, and alerts that flag potential non-compliance issues before they become a problem. It supports a dynamic and resilient compliance program.
How compliance frameworks work (step-by-step breakdown)
Implementing a compliance framework requires a clear roadmap that guides your organization from intent to execution. Each step in the process plays a crucial role in ensuring that compliance is not only achieved but also maintained in a sustainable and scalable manner.
Here’s how the lifecycle typically unfolds:
Step 1: Define scope
Before selecting a framework, organizations must first define the scope of their compliance efforts. This involves identifying the types of data processed (e.g., financial, health, personal), key business systems, the departments involved, third-party vendors, the geographic locations of operations, and the applicable regulatory environments. A well-defined scope sets realistic boundaries, ensuring that compliance activities are targeted and effective.
Step 2: Adopt or select a framework
Once the scope is clear, the next step is to choose a framework that aligns with your industry, business model, geographic requirements, and customer expectations. For instance, a SaaS startup selling to U.S. enterprises might opt for SOC 2, while a fintech company in the EU might lean towards PCI DSS and DORA. This decision also depends on the organization’s risk tolerance and the complexity of operations.
Step 3: Gap assessment
After selecting a framework, conduct a thorough gap assessment to compare your current security posture with the framework’s requirements. This assessment helps identify missing controls, outdated policies, and process inefficiencies. It also highlights areas that are already compliant, enabling teams to avoid redundant work. The output typically includes a remediation roadmap with prioritized actions.
Step 4: Implement controls
At this stage, organizations operationalize the framework by implementing necessary administrative, technical, and physical controls. This may include deploying new tools (e.g., encryption software), formalizing policies (e.g., access control), training staff, and configuring systems to meet compliance obligations.
Step 5: Document everything
Documentation is essential not only for proving compliance during audits but also for internal alignment. This includes maintaining policy documents, process workflows, access logs, training completion records, risk registers, and evidence of control execution. Well-organized documentation provides traceability and demonstrates maturity to auditors, customers, and regulators.
Step 6: Test & audit
Once the controls are in place and the documentation is complete, it’s time for the internal testing and audits to validate the effectiveness of the compliance program. Organizations may conduct periodic self-assessments, internal audits, or hire third-party auditors for formal certifications or attestations. The goal is to identify and fix gaps before an official audit or regulatory review.
Step 7: Maintain & improve
Compliance is not a one-time project; it requires continuous attention. Organizations should implement monitoring tools to track the effectiveness of their controls, stay updated with regulatory changes, and conduct periodic reassessments. Lessons from previous audits should inform a continuous improvement cycle, ensuring the compliance program evolves in response to changes in the business and threat landscape.
How to choose the right compliance framework
When evaluating frameworks, consider multiple factors that align with your operational reality and compliance goals. These include the type of data your business handles (such as personal, health, or financial data), customer expectations, regulatory jurisdictions, and industry-specific mandates.
You should also factor in whether your operations are regional or global, if you’re dealing with public sector clients, the level of automation you can support, and how soon you need to be audit-ready. Other variables include the criticality of data handled, the potential impact of a compliance breach, and the certifications your customers expect.
The table below provides a high-level snapshot of which frameworks are typically suited to different business types:
| Business Type | Best Frameworks | Why |
| SaaS | SOC 2, ISO 27001 | Customer trust + global readiness |
| Healthcare | HIPAA, HITRUST, ISO 27001 | PHI + data security |
| Fintech | PCI DSS, SOC 2, DORA | Transaction security + resilience |
| Gov Cloud | FedRAMP, NIST RMF | Federal mandates |
| Consumer Apps | GDPR, CCPA, ISO 27701 | Privacy-first approach |
Framework mapping: How controls overlap
When pursuing multiple compliance certifications, one of the most strategic advantages lies in understanding the overlap between frameworks. Widely adopted standards, such as ISO 27001, SOC 2, and NIST CSF, share control requirements ranging from 60% to 90%. This means that becoming compliant with one often lays the groundwork for others. For example, organizations compliant with ISO 27001 typically find they’ve already covered a majority of controls required for SOC 2.
Framework mapping helps visualize this overlap, revealing how controls under one framework may entirely or partially satisfy the requirements of another. Compliance automation platforms further enhance this by automatically mapping controls across frameworks, providing organizations with clear visibility into control coverage. These tools can quantify the incremental effort required to add a new certification—sometimes reducing it to as little as 10% to 20%. This enables businesses to plan for multi-framework compliance without redundancy or wasted effort.
Below is the table that shows how controls often overlap among multiple frameworks.
| Control Category | ISO 27001 | SOC 2 | NIST CSF | PCI DSS |
| Access Control | Yes | Yes | Protect | Yes |
| Encryption | Yes | Yes | Protect | Yes |
| Logging | Yes | Yes | Detect | Yes |
| Vulnerability Mgmt | Yes | Yes | Identify/Protect | Yes |
| Incident Response | Yes | Yes | Respond | Yes |
Benefits of using a compliance framework
Adopting a compliance framework isn’t just about ticking regulatory boxes and moving on. In reality, it becomes a kind of backbone, quietly holding things together as the company grows, changes tools, hires fast, or expands into new markets. When done right (and supported by automation and actual governance, not just good intentions), the benefits compound over time.
Standardization & repeatability
A framework brings order to what would otherwise be a mess of one-off decisions. Access reviews happen the same way everywhere. Incident response isn’t reinvented at 2 a.m. Policies stop living in five different formats. This consistency matters more as teams multiply and systems sprawl. Repeatability keeps compliance from cracking under scale, which is usually when cracks show up.
Audit readiness
Frameworks quietly train organizations to stay ready, even when no audit is on the calendar. Documentation is already aligned. Evidence isn’t hunted down in a panic. Internal reviews feel routine instead of theatrical. Auditors see cleaner trails, and teams don’t lose weeks of productivity to last-minute fire drills. Less chaos. Fewer surprises.
Risk reduction
Good frameworks force you to look at risk systematically, not emotionally. They push preventative controls where things tend to break and detective controls where problems sneak through anyway. Across people, processes, and tech, the result is fewer blind spots—and fewer “how did we miss that?” moments after something goes wrong.
Customer trust
Trust isn’t built with promises; it’s built with proof. When customers see SOC 2, ISO 27001, or similar frameworks in place, it signals maturity. Not perfection, just seriousness. In B2B and enterprise sales, this often shifts conversations from “Can we trust you?” to “How fast can we move?”
Cost efficiency
Yes, compliance can feel expensive at first. But unstructured compliance is worse. Frameworks reduce rework, cut down duplicated efforts, and make automation actually usable. Over time, fewer errors mean fewer legal scares, fewer audit overruns, and less staff burnout. Compliance stops being a blocker and starts behaving like infrastructure.
Challenges of working with compliance frameworks
For all their structure, frameworks aren’t frictionless. They come with very real operational headaches, especially if organizations underestimate what’s involved.
Framework overload
ISO 27001 here. SOC 2 there. GDPR, HIPAA, maybe PCI DSS on top. The problem isn’t just quantity, it’s overlap. Slightly different wording. Similar controls. Different evidence expectations. Without coordination, teams duplicate work, ownership fragments, and compliance becomes harder than it needs to be.
Constant change
Compliance never sits still. Regulations evolve. Standards release new versions. Privacy laws mature in public, sometimes messily. Staying compliant means tracking changes, updating controls, and revisiting documentation—often before anyone internally feels “ready” for another update.
Manual burden
Without automation, compliance turns into spreadsheet archaeology. Screenshots. Email threads. Approval chases. Evidence pulled together minutes before deadlines. It eats time and increases the risk of human error, which is ironic for something meant to reduce risk.
Ambiguity
Many frameworks are intentionally flexible. SOC 2, in particular, leaves room for interpretation. That flexibility is helpful, until different teams, auditors, and customers interpret it differently. Then you’re negotiating what “good enough” means, sometimes mid-audit.
Skill gaps
Compliance sits at the intersection of security, legal, and operations. Not every company has people who speak all three languages fluently. The result? Overreliance on consultants, controls that look fine on paper but fail in practice, or implementations that don’t survive audit scrutiny.
Automation tools in compliance framework management
Compliance frameworks are living systems. Controls need testing. Evidence needs collecting. Vendors need reviewing. Audits need coordination. Doing all of that manually doesn’t scale for long, which is why many organizations turn to automation tools to keep things moving.
What compliance platforms automate
Compliance platforms reduce the grind. They don’t eliminate responsibility, but they remove a lot of unnecessary friction and guesswork.
- Control mapping
Automatically connects existing systems, tools, and policies to framework requirements, cutting down repetitive tagging and duplicated effort. - Evidence collection
Continuously pulls logs, access data, and system records—no screenshots, no shared folders full of “final_final_v3” files. - Continuous monitoring
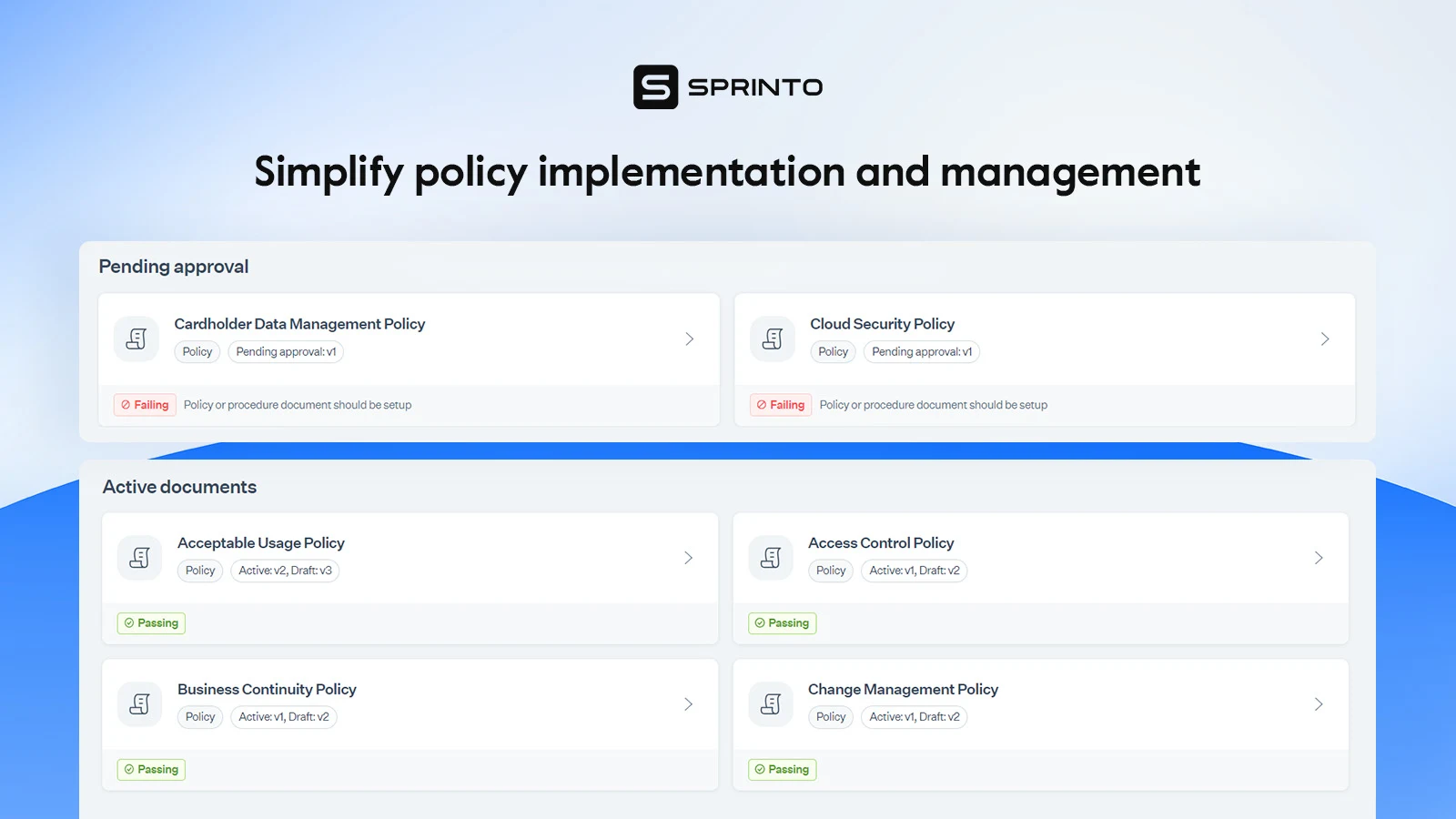
Keeps tabs on control health in real time, instead of relying on point-in-time checks that age badly. - Policy lifecycle
Centralizes drafting, approvals, distribution, and revisions so policies don’t quietly go stale. - Vendor reviews
Automates questionnaires, documentation requests, and validation steps for third-party risk management, one of the most time-consuming areas. - Audit workflows
Organizes timelines, assembles audit packs, and supports auditor collaboration with less back-and-forth and fewer “just one more thing” emails.
What tools can’t replace
Automation helps, a lot. But it doesn’t replace judgment, context, or leadership. Some parts of compliance still need humans in the loop.
- Legal interpretation
Regulations are nuanced. Applying them to a specific business model still requires legal expertise and informed decision-making. - Risk evaluation
Tools can flag issues, but deciding which risks matter most—and how to address them—is a strategic call. - Governance culture
Software can track accountability. It can’t create it. A real culture of security and compliance starts at the top and shows up in everyday behavior.
With vs. without automation
To give you a fair idea of how automation comes into the picture, we have created a table below. This table shows how each task is performed with and without automation.
| Task | Without | With |
| Evidence collection | Manual | Auto-logged |
| Control mapping | Redundant | One-to-many |
| Vendor reviews | Spreadsheets | Built-in workflows |
| Audit prep | Weeks of work | Continuous readiness |
Compliance framework maturity model
As organizations evolve, their approach to compliance also evolves. This maturity model outlines the typical stages that companies go through in building, managing, and optimizing their compliance programs. Understanding where you stand can help set realistic goals and identify the investments needed to move to the next level.
| Level | Characteristics | Team Size | Tooling | Readiness |
| Initial | Ad hoc, undocumented | 0–1 | None | Low |
| Repeatable | Basic policies | 1–2 | Spreadsheets | Medium |
| Defined | Controls in place | 2–4 | GRC tool | High |
| Optimized | Continuous monitoring | 4–6 | Automation | Always ready |
Real-world examples
Compliance frameworks are easier to grasp when you see how real companies use them to solve operational challenges. Whether in SaaS, healthcare, or fintech, teams often struggle with unclear requirements and manual work until a structured framework brings order and clarity. These examples from Sprinto customers demonstrate how organizations transform compliance from a last-minute scramble into a predictable and scalable process.
SaaS startup doing SOC 2
SaaS companies often pursue SOC 2 when enterprise prospects begin asking more pointed questions about security posture. The challenge is usually twofold: unclear requirements and uncertainty around what “audit-ready” really means. For many first-time teams, mapping systems, documenting controls, and gathering evidence feel overwhelming, especially when they need to balance customer work and product delivery.

Case study example — Kin Analytics
Kin Analytics, a data-driven SaaS firm, needed SOC 2 compliance to unlock enterprise deals but lacked the structure and dedicated resources to manage a comprehensive audit cycle. After integrating Sprinto, the team gained instant visibility into their control health, quickly closed gaps, and increased their readiness from ~65% to ~90% within a week. Most impressively, their SOC 2 Type 1 audit—which was initially scoped for three weeks—was completed in just three days.
— Rafael Urgilés, Chief IT-S Consultant, Kin Analytics
Healthcare provider using HIPAA
Healthcare organizations operate under strict privacy and PHI handling rules, making HIPAA one of the most demanding frameworks. The challenge is less about technical controls and more about operational discipline: clear policies, consistent staff training, tight access controls, and the ability to detect PHI-related drift across systems and vendors. For many teams, HIPAA becomes manageable only when processes are centralized and continuously monitored.

Case study example — Kodif
Kodif, a healthcare technology provider, used Sprinto to translate HIPAA’s broad legal requirements into actionable safeguards across people, processes, and systems. Sprinto’s templates, risk assessments, and continuous monitoring helped the team maintain strict audit readiness—consistently staying above the 95% compliance threshold.
— Norm Usenakanov, CTO, Kodif
Fintech aligning PCI DSS & ISO 27001
Fintech companies face intense scrutiny from customers, regulators, and auditors due to the sensitivity of financial data. Many organizations must juggle multiple frameworks, including PCI DSS for handling payment data and ISO 27001 for broader information security management. The difficulty lies in minimizing duplicated work, maintaining a single source of truth, and ensuring controls satisfy overlapping requirements.

Case study example — CellPoint Digital
CellPoint Digital, a global payment orchestration platform, adopted Sprinto to consolidate PCI DSS and ISO 27001 controls. Sprinto’s automated checks identified real-time risks across its infrastructure, enabling the company to run over 7,000 compliance checks daily and maintain continuous alignment. The clarity around mapped controls and incremental audit readiness drastically reduced effort and improved audit confidence.
— Frederic Lauret, Security Architect, CellPoint Digital
How Sprinto turns compliance into a growth enabler
Compliance frameworks are foundational to building trust, scaling securely, and unlocking new revenue opportunities. But without the right systems, they quickly become a source of friction—manual, repetitive, and endlessly reactive. Choosing the proper framework is just the start. The real challenge is maintaining continuous compliance in a fast-changing business and regulatory environment.
That’s where Sprinto comes in. Purpose-built for fast-growing tech companies, Sprinto replaces spreadsheet sprawl and siloed tools with a centralized, automated compliance engine that maps risks and controls across 30+ frameworks—such as SOC 2, ISO 27001, and HIPAA—and continuously monitors them through 250+ integrations. With out-of-the-box policies, automated evidence collection, and a dedicated audit console, it eliminates the grunt work so your team can move faster, not slower. Layered on top, Sprinto AI transforms static GRC into a living, self-improving system by embedding intelligence into every layer of compliance operations. So you don’t just react to audits, you stay ahead of them.
What Sprinto and Sprinto AI unlock for your team:
- Autonomous GRC agents to automate evidence collection, vendor risk reviews, and gap detection
- Continuous monitoring of controls, policies, and risks with proactive alerts before audits break down
- Instant onboarding of new frameworks using AI-powered control and policy mapping
- Ask AI, Security Questionnaire Assistants, and in-app extensions to democratize compliance knowledge across teams
- Scalable compliance operations that cut cost, reduce fatigue, and keep every framework in sync
Ready to replace audit anxiety with always-on assurance? Book a custom demo and experience what AI-native, scalable compliance looks like in action.
FAQs
A compliance framework is a structured system of policies, procedures, and controls that helps organizations meet legal, regulatory, and industry-specific standards. It provides a consistent foundation for managing risk, ensuring ethical operations, and maintaining audit readiness across the organization.
There’s no universal number. The correct number depends on your industry, geographic footprint, customer requirements, and regulatory exposure. A SaaS company selling to U.S. and EU markets may need to comply with SOC 2 and GDPR, while a healthcare provider in the U.S. would prioritize HIPAA and potentially HITRUST.
Implementation timelines vary based on the selected framework, internal readiness, and whether automation tools are used. SOC 2 or ISO 27001 may take 2–3 months with strong tooling and support, but more complex or high-stakes frameworks, such as FedRAMP, could stretch to 12+ months.
Most compliance frameworks are updated every 1–3 years to reflect evolving threats, technologies, and regulatory expectations. Organizations must monitor these updates and revise their controls and documentation accordingly to stay current.
The consequences of skipping a formal framework include increased risk of data breaches, audit failures, regulatory fines, contract losses, and reputational harm. Frameworks serve as a safeguard and a signal of maturity to regulators, customers, and partners.
Compliance automation tools streamline evidence collection, map overlapping controls across frameworks, provide real-time monitoring, and reduce the overall burden on teams. They help maintain continuous compliance and significantly shorten audit timelines.
Costs range widely based on the framework, organization size, complexity, and whether you use consultants or automation platforms. Budget anywhere from $10,000 to $100,000+, factoring in tooling, auditor fees, internal time, and control remediation.
A framework is a structured set of best practices or guidelines that help organizations build a compliance program (e.g., SOC 2, ISO 27001). A regulation is a legal obligation (e.g., HIPAA, GDPR) that companies are required to follow. Frameworks can help prove compliance with laws, but they are not interchangeable.
Author
Bhavyadeep Sinh Rathod
Bhavyadeep Sinh Rathod is a Senior Content Writer at Sprinto. He has over 7 years of experience creating compelling content across technology, automation, and compliance sectors. Known for his ability to simplify complex compliance and technical concepts while maintaining accuracy, he brings a unique blend of deep industry knowledge and engaging storytelling that resonates with both technical and business audiences. Outside of work, he’s passionate about geopolitics, philosophy, stand-up comedy, chess, and quizzing.Explore more
research & insights curated to help you earn a seat at the table.