As a founder of a business that processes online transactions, PCI compliance is mandatory, irrespective of the size and type of your organization. Compliance must be maintained year-round and validated annually, as required by credit card companies and outlined in network agreements.
The PCI Standards Council (SSC) develops and maintains these standards to secure payment card transactions.
If you are wondering if now is the right time for your organization to become PCI DSS compliant? Then, this article is for you. It walks you through the nuances of why PCI DSS standard regulations, its importance, the costs of non-compliance, and includes PCI compliance guidelines to help you become PCI compliant.
- PCI DSS compliance is aimed at protecting cardholder information and contains 12 industry requirements and 250+ security controls.
- Becoming PCI DSS compliant involves understanding its requirements and PCI level, analyzing and fixing gaps, conducting internal risk assessment, mapping and monitoring controls, and filling out the respective SAQs.
- PCI DSS compliance groups include PCI SSC, Merchants, Service providers, Card issuers and merchant banks, QSAs, and ASVs.
What is PCI DSS?
The Payment Card Industry Data Security Standard, PCI DSS for short, is a security standard designed to protect cardholder data and ensure secure payment transactions.
The PCI Security Standards Council (SSC), founded by major payment brands like Visa, MasterCard, and American Express, oversees the development and maintenance of PCI DSS.
The standard outlines best practices and protocols for organizations using payment systems, such as implementation of strong access controls, encryption of sensitive data, and periodical monitoring systems. This helps businesses demonstrate their commitment to protecting customer payment information and maintaining trust. Organizations must validate their compliance annually through audits or self-assessments.
What is PCI DSS Compliance?
PCI DSS (Payment Card Industry Data Security Standard) compliance is a global information security standard for protecting cardholder data during transactions. PCI SSC (Security Standard Council) established its security protocols.
PCI compliance minimizes breach risks for organizations that handle payment card information. It protects against cybercriminals that target cardholder data, which can lead to credit card fraud, identity theft, financial losses, and reputational damage.
PCI DSS was established in 2006 by major credit card companies (American Express, Discover, JCB International, Mastercard, and Visa) and financial institutions. It applies to merchants, vendors, and service providers to ensure secure transactions and protect customers’ information.

PCI DSS 4.0 April 2024 Update
Some of the requirements of the PCI framework procured a few changes in the PCI DSS 4.0 update:
- Requirement 3: Clarifications for issuers and those supporting issuing services, with added flexibility for organizations using specific cryptographic methods to secure PANs.
- Requirement 6: Returned to v3.2.1 language focusing on patching critical vulnerabilities; clarified managing payment page scripts.
- Requirement 8: Noted exceptions for non-admin access into cardholder data environment (CDE), allowing phishing-resistant authentication for user accounts.
- Requirement 12: Updated notes on customer-TPSP relationships for clarity.
For more information on the update, watch the video below.
Components of PCI DSS Compliance
PCI compliance process involves four key components aimed at ensuring the security of cardholder data. This helps in assessing your systems to identify cardholder data and potential vulnerabilities.
- Handling card data securely: Ensuring sensitive card details are collected and transmitted in a secure manner using secure transmission methods (e.g., HTTPS).
- Secure storage of card Data (minimum standard): Adhering to the 12 security domains of PCI DSS for securely storing cardholder data.
- Annual validation of security controls: Validation includes self-assessment questionnaires (SAQs), external vulnerability scanning, and third-party audits.
- Maintaining PCI compliance: Continuously maintaining compliance with PCI DSS standards by implementing and adhering to security policies, procedures, and controls outlined by the PCI Security Standards Council.
Why do organizations need to be PCI DSS Compliant?
PCI DSS compliance is important to protect your customer’s sensitive card data from physical and digital breaches. PCI DSS standard will lay the framework for you to deploy new admin access and technical systems (and upgrade existing ones) required to instil trust in your customers about the safety and integrity of their sensitive card data.
In a nutshell, PCI compliance management helps implement a wide range of technical safeguards to protect cardholder data, including strong access control measures and password management, physical security controls, and documentation of the existing security program’s policies. It lays down 250+ essential controls applicable to merchants and service providers that use card information to remain PCI compliant.
In fact, 30% of small businesses report that they don’t know the penalties for non-compliance with PCI DSS 4.0. This is common because the documentation contains almost 2000 pages. It would take you more than three days to read it!
To see where you are in terms of getting PCI framework, first check your eligibility. Download the questionnaire below:
Download your PCI DSS Self Assessment Questionnaire
What do I need to be PCI compliant?
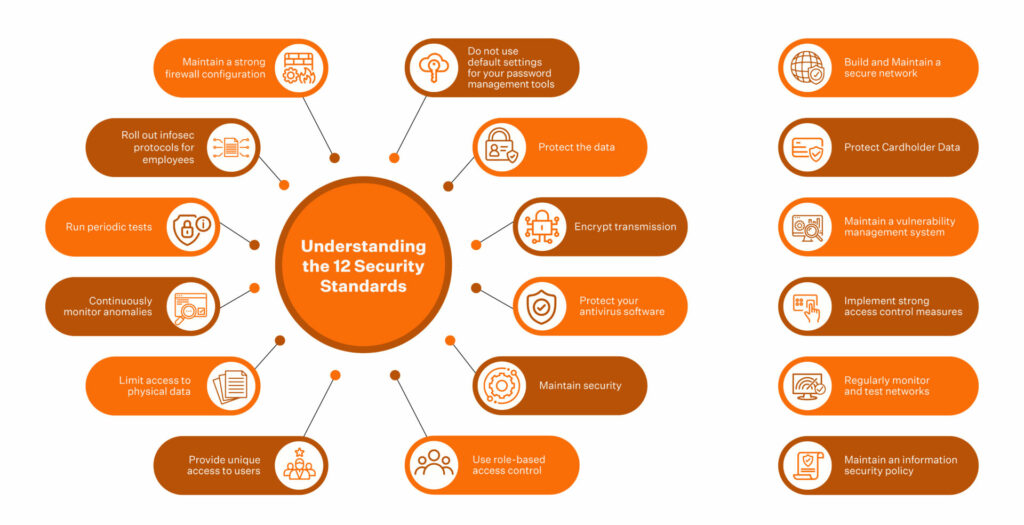
To be PCI compliant, your business must meet the 12 core PCI DSS requirements, including securing networks, encrypting cardholder data, using anti-virus software, restricting access, and maintaining a vulnerability management program. The most effective way to limit the systems that all 12 requirements actually apply to is PCI DSS network segmentation, since a well-designed segmentation strategy isolates the CDE and shrinks the audit footprint dramatically.
How to become PCI DSS Compliant?
Getting PCI compliance for your business doesn’t have to be daunting! Start by understanding the 12 PCI compliance requirements, which cover everything from securing networks to protecting cardholder data.
Next, assess your current security posture to identify gaps, fix those vulnerabilities, and implement robust security measures. Finally, establish and monitor compliance policies to ensure your payment environment remains secure and ready for assessment.
Here are the steps to get PCI compliance for your business:
Step 1: Understand the PCI DSS requirements
If you’re a business that handles card information, you are expected to comply with all the 12 PCI standards.
Here’s a list of the PCI DSS requirements in brief:
- Install and Maintain a Firewall Configuration to Protect Cardholder Data
- Do Not Use Vendor Supplied Default Passwords
- Protect Stored Cardholder Data through Encryption
- Encrypt Transmission of Cardholder Data Across Open, Public Networks
- Use and Regularly Update Anti-Virus Software
- Develop and Maintain Secure Systems and Applications
- Restrict Access to Cardholder Data by Business Need-to-Know
- Assign a Unique ID to Each Person with Computer Access
- Restrict Physical Access to Cardholder Data
- Track and Monitor All Access to Network Resources and Cardholder Data
- Regularly Test Security Systems and Processes
- Maintain an Information Security Policy
Step 2: Define your level of PCI compliance
The scope of PCI DSS certification is defined by the volume of transactions your organization processes annually. A merchant or business can fall into one of the four categories and then determine the compliance level and requirements.
- PCI Level 1: Businesses processing over 6 million transactions per year
- PCI Level 2: Businesses processing 1 million to 6 million transactions per year
- PCI Level 3: Businesses processing 20,000 to 1 million transactions per year
- PCI Level 4: Businesses processing less than 20,000 transactions per year
Here’s a detailed guide on PCI DSS levels
Step 3: Conduct an Internal Risk Assessment
Risk analysis helps identify risks related to information systems and decide how they will be controlled and managed. As a result of this analysis, primary and permanent (inherent) risks are evaluated, and prolonged or residual risks (secure configuration and change controls or not using processes, etc.) are examined.
To do:
- Draw a line between production and non-production systems
- Make an inventory of the critical systems and internal controls
- Identify business risks, assign a likelihood and impact to each of them
- Deploy policies and procedures to mitigate them
What not to do:
- Run security risk sweeps only when you are asked to produce a risk assessment report
- Keeping the risk assessment inhouse and not including external experts for an unbiased outcome
- Work in silos without communication among your teams
Step 4: Analyze and Remediate Gaps
PCI DSS Gap Analysis helps organizations streamline their journey to achieve PCI framework. This assessment will help them determine where they are currently standing, giving them direction toward achieving Compliance.
This assessment helps you understand your compliance status and prepares you for the on-site assessments required to achieve Compliance.
A gap analysis exercise aims to identify deficient controls that could lead to a failed audit report.
The next step after identification is to remediate said controls or deploy new ones to ensure the PCI DSS compliance requirements are met.
Usually, a PCI gap analysis is performed by an assessor who maps the critical information processes and technical infrastructure to determine the PCI controls required to be implemented. And this process usually takes between 5-7 days to complete.
Sprinto, at its core, is designed to seek gaps in the compliance framework and enable you to work towards closing any future gaps.
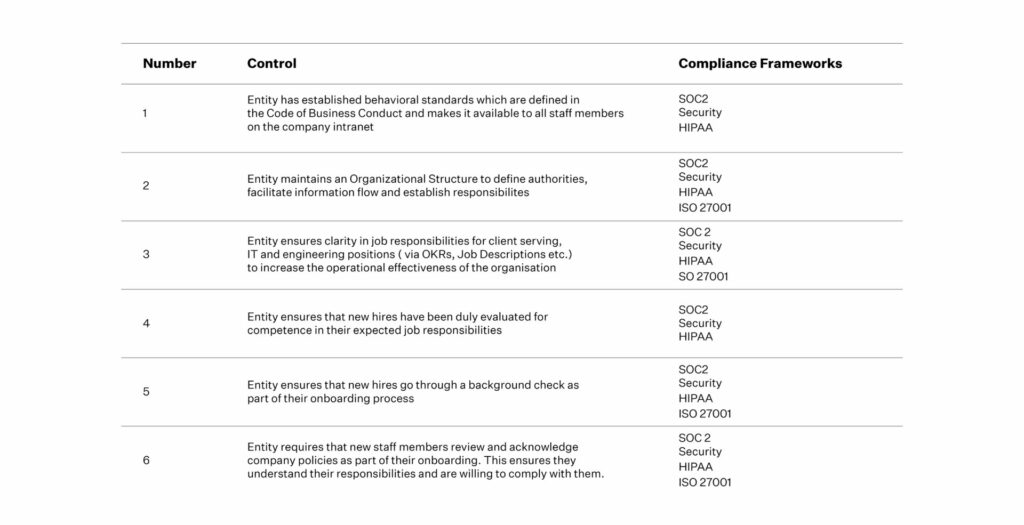
Step 5: Map policies and controls to the PCI framework
The next step is to map your internal controls to PCI DSS goals and protect points where card data enters, gets stored, and exits the organization. Also, identify and eliminate out-of-scope items (with justification for each) to ensure a bloat-free audit preparation period and a lean-mean audit SAQ for the Auditor to review.
However, manually mapping 250+ controls for the 12 security parameters is not an option. Consider automating the PCI compliance process to have a unified view of your controls and policies.
Sprinto is a compliance automation platform that lets you automate the process of getting compliance. You can map your controls to the specific requirements of the PCI framework and rest easy. The platform provides a live status where your controls stand, making monitoring effortless.
With an integrated audit dashboard, the auditor can access all your controls along with your compliance health report. This way, you’ll avoid missing out on submitting essential critical evidence to the Auditor during an audit.
Step 6: Monitor continuously
The next step is to map internal controls to PCI DSS goals and protect points where card data enters, gets stored, and exits the organization. Also identify and eliminate out-of-scope items (with justification for each) to ensure a bloat-free audit preparation period and a lean-mean audit SAQ for the Auditor to review. Mapping controls for the 12 security standards and its 251 sub-sections can be daunting.
But that’s where PCI automation saves the day. Having a singular view of the mapping & evidence for policies and security measures ensures that you do not miss out on submitting essential critical evidence to the Auditor during an audit.
Step 7: Continuous Monitoring
Continuous monitoring and assessing the compliance posture is imperative in your compliance journey. Being compliant is not a one-time task. To remain compliant over a period of time, you must constantly monitor the controls you have in place to ensure data security while continuously assessing ways to implement new effective models while reducing costs.
Most monitoring and assessment models can be automated. Automating this function empowers your business to move away from the cyclic/periodic monitoring model to a more hands-on version triggered with every new instance.
For example:
Protecting secure passwords is one of the critical security requirements of PCI compliance management. For this, a good trigger automatically runs the control every time a new user is added. A check can also be triggered in the subsequent follow-up instance to see if the password requirements are met.
At Sprinto, we automate the monitoring and assessment process to ensure that you have the visibility you need to remain PCI compliant throughout the year and fix patches that need fixing when patches show up.
Step 8: Fill out the Self-assessment Questionnaire (SAQ)
The next step for Level 2, 3, and 4 businesses is filling out the Self-Assessment Questionnaire (SAQ) and submitting a report on Attestation of Compliance (AOC).
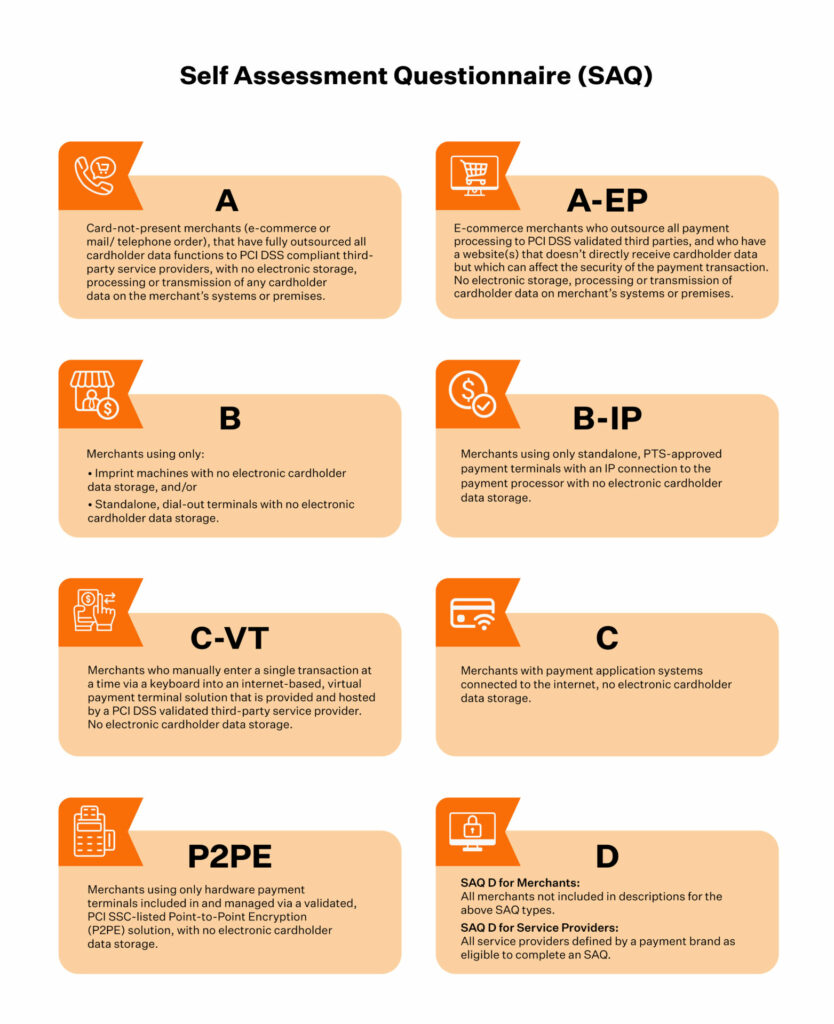
Level 1 businesses must fill the PCI DSS Self-Assessment Questionnaire, an AOC, and get a Security Assessor’s Report on Compliance (ROC). This assessor should be from the list that the PCI framework recommends.
Download your PCI DSS Requirements List
Benefits of implementing PCI DSS Compliance
From enhancing overall security posture and protecting from data breaches to saving the business from customer attrition and financial repercussions, implementing PCI compliance guidelines offers a range of benefits.
- Employing strong security controls with strong cryptography and best practices builds an optimised security stance and enhances operational efficiency. It also helps manage risks proactively and fosters a compliance culture.
- A number of large enterprises seek PCI compliant vendors. So, it helps unlock corporate expansion for business.
- Customers find it easy to mortgage their trust with the business with compliance confidence. They know their data is safe and handled securely.
Financial ramifications associated with non-compliance or breaches like fines, penalties, lawsuits etc. can be avoided.
What are the types of PCI Compliance groups?
There are 6 groups involved in PCI DSS Compliance namely the council, merchants, service providers, card issuers and merchant banks, QSAs (Qualified Security Assessors) and ASVs (Approved Scanning vendors).
PCI SSC
Formed by major credit card brands Visa, Mastercard, American Express, Discover and JCB, the council is responsible for establishing and maintaining standards for protection of cardholder data.
Merchants
Businesses or organisations that collect, store or process cardholder data and are responsible for PCI DSS adherence are merchants.
Service providers
Organisations that handle cardholder data on behalf of merchants are service providers. These can be hosting service providers, managed security service providers, cardholder data storage services etc.
Card issuers and merchant banks
Card issuers/ card brands issue payment cards to customers while merchant banks are financial institutions that facilitate payment acceptance on behalf of merchants.
QSAs
Qualified security assessors are certified PCI compliance assessors who conduct assessments for merchants or service providers.
ASVs
Approved scanning vendors are organisations qualified by PCI SSC for conducting vulnerability scans for merchants or service providers.
How much does PCI Compliance cost?
Implementing PCI compliance regulations and achieving compliance (with certification) can cost anywhere from $5000 to $20000 for small to medium size businesses and for large organisations can range from $50,000 to $200,000.
Note that the costs of PCI compliance depend on a lot of factors like merchant level, organisation size, current compliance levels etc.
Different compliance specialists charge differently depending upon the comprehensive requirements of the organization.
These costs can be reduced by 80% if you switch to automation with Sprinto. (Calculate PCI compliance cost with Sprinto Now!)
What happens when you are not PCI DSS Compliant?
The cost of non-compliance is steep, with monetary fines ranging from $5000-$100,000 (depending on the nature of non-compliance). In terms of non-monetary aspects, your access to promote card-based technology transactions on your business platforms could be rescinded too.
Each non-compliance instance is flagged as a security violation and this could cause significant reputational damage too.

Here’s a list of the repercussions you could face for being non-compliant:
1) Penalties
Both credit card companies and banks charge fines – of $5,000 to $100,000+ per month. And suppose a business gets fined and continues to ignore its PCI compliance requirements, it can even be removed from the credit card processing network. As a result, the organization would no longer be payment processors for its customers. This could be devastating for businesses that rely on credit cards for their sales.
2) Bad Actor Instance
PCI DSS compliance doesn’t make your business breach-resistant. But when a PCI DSS-compliant business becomes the victim of a security incident, the penalty amount is significantly reduced – the organization can show it did everything required by the framework, which materially shrinks the PCI DSS fines the card brands and acquiring banks ultimately assess.
Besides, a security violation adds to the financial burden of a business as they will need to do the following:
- Hire an investigation team to identify the source of the breach
- Conduct mandatory credit monitoring for customers whose data was compromised
- Deal with lawsuits, if any
- Handle loss of revenue driven by merchants cancelling partnerships (when your business is non-compliant consistently)
The average cost of dealing with each recorded victim is $150. When multiplied by the number of people affected by a breach, this value can get quite expensive.
3) Lawsuits
In case of data breaches, businesses are typically sued by vendors and customers. For example, Target had to pay a fine of $18.5 million when sensitive information related to 40 million accounts was made public following a breach.
4) Impact on the Revenue and Brand
When sensitive information is put at risk, the client’s trust in the organization nosedives, leading to negative word-of-mouth publicity and loss in brand equity. In addition, a bad reputation makes it harder to attract new customers or retain existing customers, directly affecting future profits.
How Sprinto helps you achieve PCI DSS Compliance?
Sprinto is purpose-built to offer a ‘unique-to-you’ PCI compliance solution. At its core, Sprinto is powered by an automation engine that automates most of the legwork that goes into getting your business compliance validated.
Every business entity is monitored at a granular level for controls and checks to ensure a seamless audit. Any edge cases are marked and evidences automatically catalogued and submitted to the auditor through Sprinto Auditor dashboard.
The dashboard gives the Auditor a single view of an audit report with precise segmentation for controls set in place, documentation for people processes, and so on.
How we simplify the PCI Compliance DSS journey for your business
Sprinto is purpose-built to offer a ‘unique-to-you’ compliance solution. At its core, Sprinto is powered by a proprietary automation engine that automates most of the legwork that goes into getting your business compliance validated.
Step 1: Entity-level Mapping for a More Robust Security Posture
Any compliance aims to strengthen the security posture of an organization. The templated approach is rigid and approaches Compliance from a ‘checking a box’ perspective. Sprinto understands that securing individual entities checks multiple boxes and is time and cost-efficient.
Mapping controls to compliance requirements also ensure that as you grow your business, your future compliance requirements are addressed seamlessly with Sprinto.
To simplify this:
For almost every compliance framework Sprinto does for you, it makes you future-ready by paving a path for your subsequent Compliance needs by upwards of 75%
The 12 PCI DSS requirements are mapped to 6 key goals of PCI DSS compliance and broken down into entities. Each entity is then individually addressed to ensure that your business has all the controls and checks to ensure a seamless audit.
Step 2: Implementing Edge Cases
Edge cases are not uncommon. An edge case could lead to an exception of Compliance in your report, and a templated approach towards Compliance does not account for these occurrences.
An edge-case could be as simple as one of your employees being away from work for maternity/paternity leave and hence not being able to encrypt their laptops or update their operating systems. You could encounter 100 more edge cases like these in your compliance journey.
In the templated approach towards Compliance, because the employee mentioned above could not complete their device encryption, this case would be marked as an exception in your report.
With PCI compliance solutions like Sprinto, you can mark these instances as edge cases with supporting evidence when submitting your audit report. In addition, the custom auditor dashboard we’ve built enables Auditors to review these edge-cases and consider why something was not done.
Step 3: Cataloging Evidence Automatically
Sprinto is built to automatically collect and catalogue the evidence required for a compliance audit. This saves our users (founders, CTOs, VP engineering, VP-Product) hundreds of hours in taking screenshots, documentation, assortment, creating and sharing 100s of drives in the pre and post-audit process.
We want clients to be able to focus on developing their next world-changing idea and not hustle through the intricacies and nuances of the compliance process.
Step 4: Submitting an Audit Report or SAQ
The scope of becoming PCI DSS certified will be defined by the volume of transactions your organization processes annually.
At Sprinto, we understand that you’d need the most hand-holding in the initial phase of your compliance journey. We’re here with global, 18-hour customer support coverage when you need us.
Talk to our experts today to get started on your PCI DSS compliance journey
What you need to know: The Myth Busters.
Most common myths about PCI DSS
1) PCI DSS doesn’t apply to small merchants who process just a few transactions yearly.
In reality: You need to be compliant even if your business processes one credit card transaction. You wouldn’t need an audit, but you still have to comply. Refer to the PCI compliance guidelines for more details.
2) PCI DSS applies to e-commerce companies only.
In reality: Every business that stores, processes, or transmits cardholder information has to be PCI DSS compliant. So even if your business occasionally processes transactions through POS devices, you’d have to be compliant.
3) If I’m 80% compliant, I’m good to go!
In reality: Unlike SOC 2, you cannot choose which TSCs apply to you. With PCI DSS, you must comply with all the six principles and 12 security standards. So, being 80% compliant is not being compliant.
4) I don’t process credit card data. My business only deals with ATM debit card data. I probably don’t need to be compliant
In reality, many debit cards can be used on credit card network segments, which puts them under the purview of PCI DSS.
And so on.
These are a few questions your Auditor could ask when you file your PCI DSS Self Assessment Questionnaire (SAQ). But, of course, as a business owner, you might not know these nuances, and that’s where we aim to be of assistance.
FAQ
What are the six PCI DSS compliance groups?
There are 6 PCI DSS compliance groups. They are:
- Secure Network Requirements:
- Cardholder Data Requirements:
- Vulnerability Management Requirements:
- Assess Controls Requirements:
- Monitoring and Testing Requirements.
- Security policy Requirements.
Is PCI DSS compliance mandatory?
The official PCI compliance guidelines clearly state that PCI DSS compliance is not mandatory; however, it is a means to ensure that your business can process card transactions without paying expensive transaction rates to financial institutions and payment industry giants. By being PCI DSS compliant, you also ensure trust in your users and potential business partners that your organization has the protocols and measures to protect data.
To whom does PCI compliance apply?
PCI compliance applies to any organization that processes, stores, or transmits credit or debit card information, regardless of size. By complying with PCI DSS, businesses demonstrate their commitment to protecting customer payment information and maintaining trust
What are the PCI DSS compliance levels?
PCI DSS compliance levels are categories that define the level of compliance regulations that an organization must implement when becoming PCI DSS compliant. These levels are based on the volume of transactions, nature of the risk involved, and the organization’s historic record of security breach scenarios.
How much does the PCI DSS compliance process cost?
The PCI DSS compliance cost ranges between $5000-$200,000. The cost varies on a case to case basis and the common factors that affect the cost are procuring new software, updating existing tech, training cost, VAPT engagement, risk assessment costs, auditor fee, and consultant fee.
Author
Anwita
Anwita is a cybersecurity enthusiast and veteran blogger all rolled into one. Her love for everything cybersecurity started her journey into the world compliance. With multiple certifications on cybersecurity under her belt, she aims to simplify complex security related topics for all audiences. She loves to read nonfiction, listen to progressive rock, and watches sitcoms on the weekends.Explore more
research & insights curated to help you earn a seat at the table.