Getting your PCI DSS ducks in a row requires a good understanding of the compliance requirements, their relevance in your business environment, and the controls that can help you bolster the protection of cardholder data.
The Payment Card Industry Data Security Standard (PCI DSS) is designed to protect the entire payment card value chain and, therefore, applies to all businesses that process, store or transmit cardholder data (CHD) and/or sensitive authentication data.
It is touted as the global data security standard by payment card brands. Did you know PCI DSS also applies to organizations that have accepted, transmitted, or stored a single cardholder’s data?
In this article, we will talk about the 12 PCI DSS requirements in relation to the list of controls and their objectives that you need to be aware of.
Bonus: A downloadable list of PCI DSS Requirements list
What are PCI DSS controls?
Organizations must map the controls based on inputs from the IT, security teams and other functions that come in contact with cardholders’ data.
PCI DSS controls are the security measures you must implement across the many potential touchpoints for cardholders’ data in their business environment to ensure data safety.
And you must pay due attention to defining suitable security configurations and protocols while implementing the PCI DSS controls.
List of PCI DSS controls
- Maintenance of secure network and systems: Establish robust digital defenses to prevent unauthorized access.
- Protection of cardholder data: Utilize encryption to conceal and safeguard crucial cardholder information.
- Establishment of a vulnerability management program: Regularly assess and address weaknesses in digital systems for resilience against potential threats.
- Implementation of strong access control measures: Control access to cardholder data by assigning unique IDs to individuals with computer access.
- Observation of monitor and test networks: Continuously observe digital activities, conduct regular tests, and promptly address any identified issues.
- Maintenance of information security policies: Establish and adhere to clear digital security guidelines to ensure overall safety.
What’s the importance of PCI DSS controls?
PCI DSS controls are important because they ensure that all organizations handling credit card information, including payment processors, service providers, and those involved in the payment card value chain, maintain secure systems. Implementing these controls safeguards the access and transmission of cardholders’ data, reducing the risk of security breaches and potential penalties for non-compliance in case of a breach.
Proper implementation of PCI DSS controls can help organizations:
- Establish a security standard
- Secure cardholder data
- Protect clients from fraudulent actions
- Prevent security breaches
- Avoid fines and lawsuits
- Reduce the cost of a data breach
- Inspire customer confidence

The 12 PCI DSS requirements offer a solid foundation to achieve all this and much more.
Here’s the list of PCI DSS controls
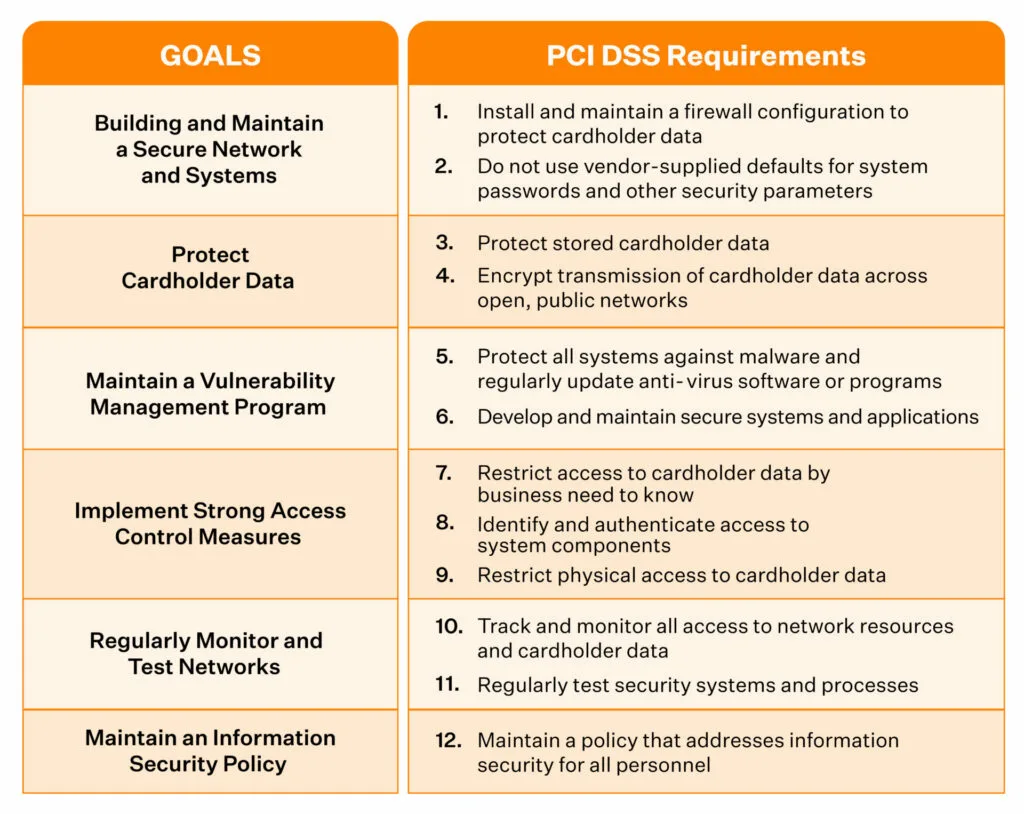
PCI DSS organizes its requirements into six control objectives, encompassing 12 key requirements that stem from global best practices for data protection. These standards apply to any business that processes, stores, or transmits credit card information, regardless of size or transaction volume.
Key aspects of PCI DSS compliance include:
- Technical and operational standards for securing credit card data
- Guidelines for protecting cardholder information during processing transactions
- Requirements that overlap with other frameworks like GDPR, HIPAA, or SOC 2
Here are the 12 requirements as per the six PCI DSS controls:
- Install and maintain a firewall configuration to protect cardholder data
- Do not use vendor-supplied defaults for system passwords and other security parameters
- Protect stored cardholder data
- Encrypt transmission of cardholder data across open, public networks
- Protect all systems against malware and regularly update anti-virus software or programs
- Develop and maintain secure systems and applications
- Restrict access to cardholder data by business need to know
- Identify and authenticate access to system components
- Restrict physical access to cardholder data
- Track and monitor all access to network resources and cardholder data
- Regularly test security systems and processes
- Maintain a policy that addresses information security for all personnel
These security requirements for PCI DSS v3.2.1 stem from global best practices for protecting sensitive data for any business. And if you comply with other frameworks such as GDPR, HIPAA, or SOC 2, you may find much overlap in control measures.
Here are the 12 requirements as per the six PCI DSS controls:
1. Install a security firewall
Meeting the PCI DSS security firewall requirement is the first step towards PCI DSS compliance. As cloud-hosted companies that handle credit card data, a strong firewall and router (if applicable) can help you maintain a secure network.
When properly configured, a firewall can monitor incoming and outgoing network traffic based on different criteria and rules and help determine the type of traffic that’s allowed and those that aren’t.
What should you do?
The security controls you implement to ensure this requirement must help you achieve the following:
- Document and implement security policies and operational procedures for managing firewalls
- Restrict public access to infra assets
- Disallow unauthorized outbound traffic from the cardholder data environment to the Internet
You can also track whether a personal firewall is enabled on critical laptops and desktops (employee workstations).
Calculate Compliance Effort:
Sprinto meets these requirements by regularly helping customers review network firewall rule sets and CHD network configuration standards. It also helps review and restrict public access to infra assets and monitor and review access to critical systems, ensuring secure configurations for credit card transactions.
How to calculate your compliance efforts? Learn more.
2. Don’t use security parameters provided by vendors
Organizations must change default passwords and vendor-supplied security parameters for servers, network devices, POS terminals, or software applications. As logical as it may sound, the second requirement doesn’t always get followed.
It also encourages implementing only one primary function per server to prevent functions requiring different security levels from co-existing on the same server. For example, web servers, database servers, and DNS should get implemented on separate servers.
What should you do?
- Maintain documentation for your configuration security hardening procedures
- Encrypt all administrative access using strong cryptography
- Maintain an inventory of system components in the scope for PCI DSS
Sprinto’s compliance automation solution ties these requirements to security controls and checks, such as review of encryption keys used to protect cardholder data, validation of the list of infrastructure assets, critical system users and their MFA status, among others.
3. Protect cardholder data
PCI DSS’ most critical requirement is the protection of CHD. To protect CHD, you first need to know the types of credit card data your organization will store, where it will get stored (location), and for how long (retention period).
What should you do?
- Create and maintain a data retention and disposal policy
- Limit CHD storage amount and retention time
- Define processes for secure deletion of CHD when no longer needed
- Develop a process to identify and securely delete CHD if it exceeds the defined retention
- Store only data elements as required for business (avoid storing full contents of any track)
- Restrict access to cryptographic keys
- Encrypt CHD using industry-accepted algorithms and security keys
Sprinto breaks down the requirement into easy-to-implement and -track security controls.
From creating mandatory and critical security policies, monitoring employee acceptance of those, reviewing how CHD is stored and displayed, and reviewing methods to secure CHD and encryption keys, Sprinto can automate it all.
4. Encrypt cardholder data
This requirement is similar to the third requirement but applies to CHD in transit via open, closed, private, or public networks. You must know where the CHD is coming from and going to and encrypt it before transmission.
What should you do?
- Document security policies and operational procedures for encrypting transmissions of CHD
- Ensure the policies are known to and acknowledged by all affected parties
Sprinto offers you a comprehensive list of editable infosec policies that you can pick and choose from and customize to your organization’s needs. These policies are then made available to your employees in-app for easy access and tracking.
Sprinto also offers staff security training on PCI DSS that helps strengthen your security posture by educating and empowering your staff to form a strong line of defense.
PCI DSS Security training worth > $10,000 included
5. Install and update antivirus software regularly
To protect the CHD from all types of malware, it’s essential to regularly install and update antivirus software across assets, such as servers, laptops, workstations, and smartphones.
The antivirus software must run actively and generate logs that can get audited if needed.
What should you do?
- Deploy antivirus software on all systems commonly affected by malicious software
- Perform periodic evaluations of systems that aren’t commonly affected by malicious software to identify and evaluate evolving malware threats
Using Sprinto, you can evaluate whether antivirus has been installed on staff devices and conduct an antivirus compliance review. Sprinto’s subscription comes bundled with an MDM, Dr Sprinto, that helps you do this and much more.
Cost Calculator:
To explore how Sprinto can optimize your compliance journey within budgetary considerations, check out our PCI DSS Compliance Cost Calculator.
6. Develop and maintain secure applications and systems
The sixth PCI DSS requirement focuses on implementing a process to identify and classify all security vulnerabilities using reputable external sources. You must then assign a risk ranking (for example, as ‘high’, ‘medium’, or ‘low’) to the newly discovered security vulnerabilities.
Risk rankings should be based on industry best practices and consider potential impact. Additionally, vulnerabilities may be considered ‘critical’ if they pose an imminent threat to the environment, impact critical systems, and/or result in a potential compromise if not addressed.
Critical systems may include security systems, public-facing devices and databases that store, process, or transmit cardholder data.
Organizations must also deploy critical patches in all systems in the credit card data environment, including:
- Operating systems
- Application software
- Databases
- Firewalls, routers, and switches
- POS terminals
What should you do?
- Define and implement a development process that comprises security requirements in all stages of the development
- Install critical security patches
- Ensure the test environment is kept separate
- Review custom code before release to production or customers
- Document it all
Using Sprinto’s platform, you can ensure peer review verification gets enabled in control systems and track it, enable vulnerability scanners, upload evidence of external scans, conduct VAPT using Sprinto partners, and much more.
7. Block access to cardholder data
As per the seventh requirement, organizations must implement high-level access control measures. Doing this can help them to allow or disallow access to CHD.
Organizations are also encouraged to adopt role-based access controls (RBAC), such that access to CHD can be given on a need-to-know basis.
For instance, implementing RBAC will ensure that your HR department has no access to CHD and that your system administrators have the necessary access.
What should you do?
- Document all users who need access to CHD with their designated roles
- Document access control policies and procedures
- Review and update the records regularly
With Sprinto, you can automate the timely review of access to critical systems, implement automated periodic management reviews, and set up a role-based access control matrix.
All the review logs and evidence are collected and maintained automatically within the app.
8. Assign unique identification
Every authorized user with access to CHD should have a unique identification; instead of group user identities and passwords. Having this helps trace and attribute accountability in the event of an internal breach.
Unique IDs also reduce vulnerability and help organizations respond quickly to data compromise. To strengthen this further, PCI DSS recommends employing two-factor authentication.
What should you do?
- Document and communicate authentication policies and procedures to all users
- Assign all users a unique ID before allowing them to access system components or CHD
- Limit repeated access attempts by locking out the user ID after not more than six attempts
- Set the lockout duration to a minimum of 30 minutes or until an administrator enables the user ID
- Require the user to re-authenticate to re-activate the terminal or session if a session was idle for more than 15 minutes
- Use strong cryptography and render all authentication credentials unreadable during transit and storage on all system components
- Establish strong password requirements
- Incorporate MFA
That’s a lot of ToDos, and it is only a sample of all you must do to abide by this requirement. Automating your PCI DSS compliance with Sprinto helps you validate users of each critical access system and their MFA status.
You can also review access authentication mechanisms, create and communicate a robust password policy, track the health of staff devices using DrSprinto (MDM), review access to critical systems, and revoke access to offboarded staff.
9. Block cardholder data’s physical access
This requirement entails physical security of access to system components, such as servers, paper files or workstations that store or transmit cardholder data.
You can implement security measures, such as maintenance of visitor logs, video surveillance, and shredding CHD.
The requirement, however, isn’t relevant to cloud-hosted firms.
10. Track and monitor cardholder data and network resources
PCI DSS requires all network systems to be protected and monitored. As a result, organizations must maintain network activity logs on CHD and review them daily for anomalies and suspicious activities related to access to network resources.
You can consider Security Information and Event Monitoring (SIEM) tools for this.
What should you do?
- Document how data flows into your organization
- Implement audit trails for all user log in, unsuccessful login attempts, and changes such as creation and deletion of system-level objects
- Limit view of audit trails
- Review all security events and logs of all system components (that handle CHD), critical system components, and servers that perform security functions, such as firewalls, intrusion prevention systems, authentication servers, and more.
Sprinto’s compliance solution can help you review whether the audit logs get collected for servers, network devices, applications, and databases, enable and integrate a threat detection system onto the platform, and track and investigate suspicious/reported incidents based on severity.
11. Test all security systems and processes
Cybercriminals are constantly on the lookout for vulnerabilities. Organizations, therefore, must regularly test all security systems and processes to ensure the security of CHD.
What should you do?
- Conduct internal vulnerability scan quarterly
- Conduct application penetration and network penetration tests on all external domains & IPs every year
- Conduct a quarterly wireless analyzer scan to discover all authorized as well as unauthorized wireless access points
- Scan external IPs and domains by a PCI-Approved Scanning Vendor (ASV)
12. Maintain information security policy
Organizations must implement and review the information security policy annually and distribute it to all relevant stakeholders, such as employees, contractors, and vendors.
Furthermore, this requirement also recommends performing the following activities for all cloud-hosted companies that process credit card data.
What should you do?
- Conduct user awareness training
- Implement an incident response plan
- Asses risks to identify essential assets, vulnerabilities, and threats
- Run employee background checks
As we mentioned, Sprinto allows you to create, distribute, and track acknowledgment of your organization’s various infosec policies from within the app. Staff security training, employee onboarding and offboarding, integrated risk assessments (including vendors), and more can be enabled, tracked, and evidenced for compliance.
Sprinto’s compliance experts work with you every step of the way to ensure that all PCI DSS requirements are met.
Also read: PCI DSS certification
Download your PCI DSS Requirements List
What are PCI DSS custom controls?
PCI DSS v4.0 offers another way to implement and validate PCI DSS requirements – the customized approach. Unlike the traditional method for implementing and validating PCI DSS controls, the customized approach allows organizations to develop their controls to comply.
The custom control processes or controls adopted under the customized approach can be different but must meet the stated security objective of the requirement.
Note that custom controls are different from compensating controls.
Compensating controls get used when an entity cannot meet a requirement due to legitimate technical or documented business constraints, such as a legacy system or process that cannot be updated to meet the requirement.
Also check out: PCI DSS checklist
How Sprinto enables PCI DSS compliance
In summary, PCI DSS compliance is critical in safeguarding sensitive cardholder data and ensuring the trust of customers and partners alike. While the path to compliance might seem intricate when approached independently, adopting a compliance automation solution can significantly streamline and fortify your efforts.
Ensuring the security of payment card information is not just a one-time task; it’s an ongoing commitment that extends beyond meeting regulatory requirements—it’s about building a secure environment that fosters trust and confidence. Sprinto supports this with an autonomous, AI-driven approach, continuously monitoring controls, collecting evidence in real time, and surfacing risks early so you can navigate audits smoothly and maintain compliance without constant manual effort.
Get PCI DSS compliant faster and smarter – Talk to a compliance expert today.
Streamline your path to PCI DSS Certification with Sprinto in 3 simple steps:
1. Schedule a demo session – Have your questions answered and explore tailored solutions.
2. Identify PCI Compliance gaps – Utilize detailed reports to map data permissions and access controls.
3. Automate and optimize PCI requirements – Implement efficient automation to enhance your compliance journey.
FAQs
What is cardholder data as per PCI DSS?
Cardholder data, according to the PCI Security Standards Council (SSC), comprises the full Primary Account Number (PAN) with any of the following elements:
- Cardholder name
- Expiration date
- Service code
It also includes Sensitive Authentication Data, which consists of full magnetic stripe data, CVV2, CID, PINs, and more.
The PCI DSS requires organizations to protect all cardholder data.
How many control objectives are there in PCI DSS?
PCI DSS has six compliance objectives. They are:
Control Objective 1: Build and maintain a secure network and systems
Control Objective 2: Protect cardholder data
Control Objective 3: Maintain a vulnerability management program
Control Objective 4: Implement strong access control measures
Control Objective 5: Regularly monitor and test networks
Control Objective 6: Maintain an information security policy

Author
Srividhya Karthik
Srividhya Karthik, is a Content Lead at Sprinto, she artfully transforms the complex world of compliance into accessible and intriguing reads. Srividhya has half a decade of experience under her belt in the compliance world across frameworks such as SOC 2, ISO 27001, GDPR and more. She is a formidable authority in the domain and guides readers with expertise and clarity.Explore more
research & insights curated to help you earn a seat at the table.