Payment Card Industry Data Security Standards or PCI-DSS requires organizations to encrypt credit card information stored in their database while ensuring data remains secure when shared outside the company.
For all organizations that process, transmit, or store payment and credit card data information, as established by the Payment Card Industry’s (PCI) Data Security Standards (DSS), sufficient encryption complexities remain a compliance necessity. Organizations must implement measures to protect cardholders’ sensitive information, including using the latest security methods and cryptographic algorithms.
This article dives deep into the PCI encryption requirements mandatory for demonstrating compliance.
What is PCI encryption?
PCI DSS encryption requires protecting cardholders’ sensitive information and encrypting data shared across public networks. PCI DSS encryption compliance demands complex cryptographic algorithms or other ways of encryption that render primary account numbers (PANs) unreadable.
This encryption process can take place through one of the following methods:
- One-way hash functions
- Strong cryptography
- Truncation
- Securely stored data pads and Index tokens
Do organizations need PCI DSS encryption?
The PCI DSS Security Standards require businesses to encrypt credit card account numbers saved in their databases as well as ensure that data remains secure when being transferred outside the company.
Businesses storing, processing, or transmitting payment and credit card data information have to abide by PCI-DSS regulations and fulfill encryption requirements as outlined.
Need help with your data encryption
What are the PCI DSS encryption requirements?
The PCI DSS encryption requirements outline five primary methods to secure cardholder data during transmission or storage.
Before you get into understanding the requirements, do take a look at the PCI DSS SAQ eligibility checklist below:
Download Your PCI DSS SAQ Eligibility Checklist
Here are the 5 steps you can take toward PCI DSS encryption:

One-Way Hash Functions
Also known as a hashed index, one-way hash functions within the databases (where sensitive information is securely stored) only show index data used to locate records. The “one-way” descriptor touches on the fact that the encryption is virtually impossible to reverse or invert.
Truncation
Truncation is sensitive data displays where some sections have been removed to safeguard the true value. Although cardholder data may be masked when shown to protect sensitive information (while authorized personnel can still digitally access it), truncation changes the actual stored value.
Stored Pads and Index Tokens
Stored pads and index tokens provide a combination encryption algorithm that utilizes both a one-time-use key and sensitive plain text data. The key is also known as a “pad.”
Strong Cryptography
The PCI Security Standards Council (SSC) details strong cryptography that fulfils their PCI DSS encryption requirements “as per industry-tested algorithms, together with key lengths that offer a minimum of 112 bits of effective key strength as well as proper key management practices.” Cryptography includes both non-reversible, one-way hashing and reversible encryption.
The SSC considers the following algorithms and standards as acceptable for fulfilling PCI DSS encryption requirements:
- AES (128-bit or higher)
- RSA (2048 bits or higher)
- TDES/TDEA (i.e., the Triple Data Encryption Algorithm)
- DSA/D-H (2048/224 bits or higher)
- ECC (224 bits or higher)
For more information on industry-accepted algorithms and cryptographic key strengths, the PCI SSC glossary suggests visiting the National Institute of Standards and Technology.
AES Encryption
Originally known as “Rijndael,” the Advanced Encryption Standard (AES) is a NIST-accepted block cypher specification used to encrypt electronic data. Selected by the U.S. National Security Agency, AES provides secure encryption for classified data up to the “SECRET” level and for non-classified data as well. With widespread NIST approval and industry adoption, the use of AES fulfills PCI DSS encryption requirements.
AES implements symmetric key cryptography, as per NIST’s development requirements listed in their initial call for algorithms, as a block cypher with minimum support for block sizes of 128-bit and key sizes of 128, 192, and 256-bit.
How to encrypt PII data?
PII or Personal Identifiable Information is used to identify an individual’s identity, such as name, Passport Number, Health Records, biometric records, Bank Account Number, and Social Security Numbers, among others.
PCI DSS takes into consideration only the PIIs that are related to payment cards, and the scope includes merchants, service providers, and processors, as well as all the entities that process, store, and transmit payment card data.
As per PCI-DSS requirements, PII data needs to be encrypted in the following stages:
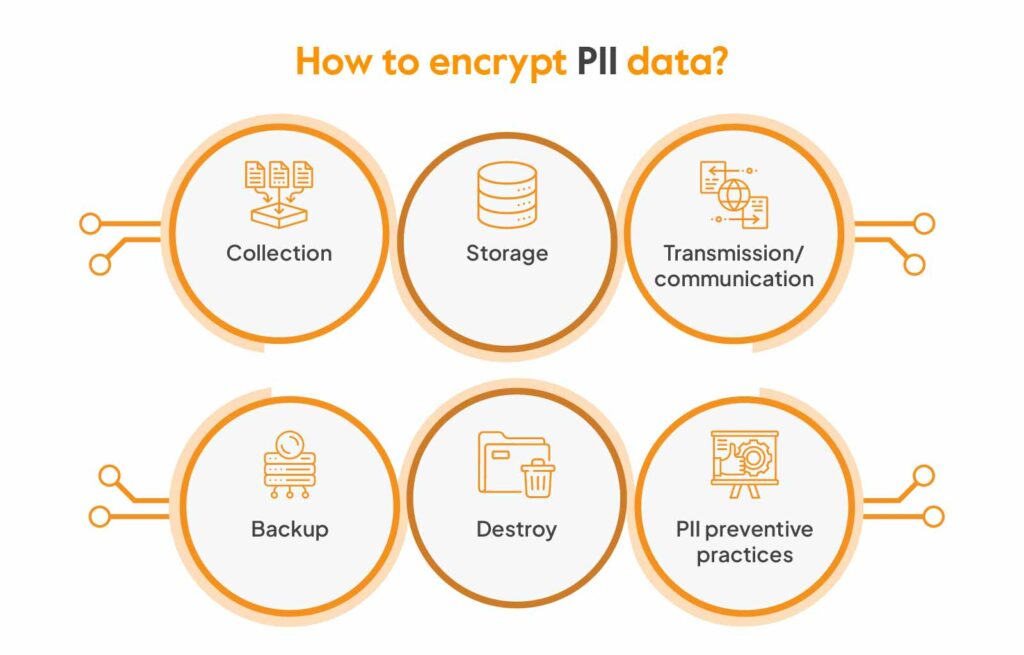
Collection
The first stage involves the collection of PII data from the end user. This involves the secure collection of PII data through Websites, physical Service providers, Point of Sale, etc.
PCI DSS clearly dictates the use of a secure channel between the end-user and the website using technologies like IPsec, TLS, etc., for Point of Sale (POS) systems as well as POS monitoring technologies while establishing certain standards for third-party service providers that access cardholder data.
Storage
Some of the requirements that clearly define once Cardholder data is inside the system, how it should be handled:
- Mask PAN when displayed such that only authorized personnel can see the full PAN.
- Render PAN unreadable wherever it is stored (including on portable digital media, in logs, and backup media) by using any of the following approaches:
- One-way hashes based on strong cryptography,
- Index tokens and pads
- Truncation
- Strong cryptography
- Never send unprotected PANs using end-user messaging technologies (for example, e-mail, instant messaging, chat, etc.).
- After authorization, do not save sensitive authentication data(even if encrypted). Render all data unrecoverable on completion of the authorization process If sensitive authentication data is received.”
Transmission/communication
PCI DSS also requires securing the transmission of confidential data to other providers and channels.
- During transmission over open, public networks, use strong cryptography and security protocols (for example, IPSEC, SSL/TLS, SSH, etc.) to safeguard sensitive cardholder data, including the following:
- Only trusted certificates and keys are accepted.
- The protocol in use only supports secure configurations or versions.
- The encryption strength is acceptable for the encryption methodology in use.
Backup
As per PCI DSS certification standards, any system that contains the cardholder data falls under PCI DSS scope. The cardholder data, for backup also, must be stored in a secure form like tokenized, encrypted, etc.
Additionally, the physical access to the backup systems with cardholder data must be monitored and have strict access controls built around them. The same security policies must be implemented for these backup systems as involved in the usual cardholder data environment.
Destroy
PCI DSS clearly says, instead of destroying the data, to store only data having a business purpose. Moreover, PCI does not permit storing card authentication information.
When data is moved to production, organizations are required to have processes in place that delete the actual data as well as the samples used in testing.
PII preventive practices
Some of the best PII best preventive measures include:
- Create cybersecurity awareness
- Identify the kind of PII that is being stored, collected, and processed.
- Make sure that the entities storing, collecting, as well as processing PII are governed as per compliances/regulations and are secure.
- Restrict access to PII only to authorized personnel and need-to-know basis.
- PII must be stored in encrypted form.
- Deploy an automated monitoring solution specific to the PII environment.
- Do not store the PII if you do not need the PII.
What is the best encryption as per PCI?
Strong cryptography, as defined by the PCI DSS, is cryptography based on accepted and industry-tested algorithms and proper key management techniques, and effective key lengths.
Protecting keys using hardware security modules is one method of protecting data and includes both hashing (irreversible) and encryption (reversible). The following are some examples of key lengths and standard algorithms:
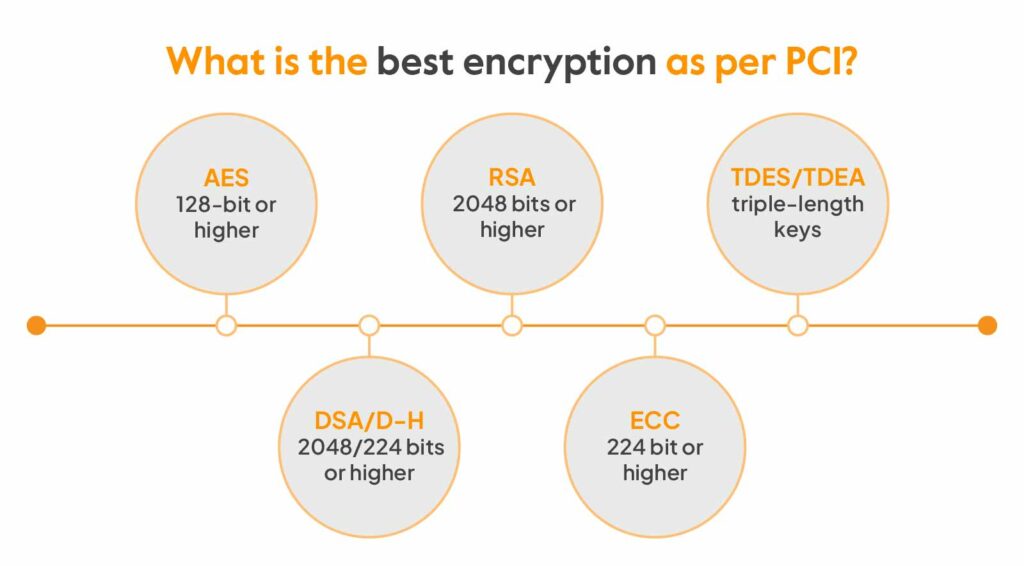
- AES – 128-bit or higher
- RSA – 2048 bits or higher
- TDES/TDEA – triple-length keys
- DSA/D-H – 2048/224 bits or higher
- ECC – 224 bit or higher
Over the network, according to PCI DSS, all management access must be encrypted using strong encryption to prevent a hacker from gaining access to important operational or administrative information such as passwords or administrator IDs.
PCI DSS requires only strong encryption, regardless of the security protocol applied, when sharing cardholder data between networks as well as additional mechanisms such as trusted certificates.
After you understand PCI encryption requirements, map where cardholder data actually moves
Encryption requirements only become useful when you know exactly where cardholder data is collected, stored, transmitted, and backed up.
Your next step is to map that flow end-to-end:
- Trace collection points, storage locations, transmission paths, and backups
- Identify where PAN is displayed, stored, or shared with vendors
- Review whether tokenization or a hosted payment flow can reduce scope
- Validate how keys, certificates, and management access are protected
- Make sure logs, backups, and admin workflows are not creating accidental exposure
Most teams do not fail PCI because they never heard of encryption. They fail because one in-scope path, backup, admin workflow, or vendor handoff gets missed.
If you want the full Req 3 + Req 4 picture before designing: Sprinto auto-discovers where cardholder data flows across your cloud, validates encryption configurations in real time, and flags drift before it shows up in a QSA finding, so your architecture choices stay defensible after launch.
Work through the PCI DSS checklist with us before your assessment →
FAQs
The PCI Encryption/Decryption Controller is pre-installed in the motherboard and is responsible for keeping data safe while preventing hackers from stealing your data. To ensure that no third-party source can access the sensitive data, it continuously encrypts/decrypts data during transmission.
Browsers fulfilling the following requirements support PCI DSS encryption:
– AES – 128-bit or higher
– DSA/D-H – 2048/224 bits or higher
– RSA – 2048 bits or higher
– ECC – 224 bit or higher
– TDES/TDEA – triple-length keys
AES is the preferred encryption method for PCI-DSS, specific government privacy rules, and HIPAA. Data is secured to the highest standards by encryption methods approved and certified by the National Institute of Standards and Technology (NIST).
No, email files containing cardholder data cannot be used as PCI DSS evidence because PCI standards strictly prohibit sending unprotected PANs or sensitive authentication data via email.
Payment card data has 2 classifiers, namely:
Cardholder data:
– Permanent Account Number(PAN)
– Service Code
– Card Expiration Date
– Cardholder Name
Sensitive Authentication Data:
– Full data in chip or magnetic strip
– CVC/CVC2 etc.
– Card PIN/Card PIN blocks
Author
Ayush Saxena
Ayush Saxena is a senior security and compliance writer. Ayush is fascinated by the world of hacking and cybersecurity. He specializes in curating the latest trends and emerging technologies in cybersecurity to provide relevant and actionable insights. You can find him hiking, travelling or listening to music in his free time.Explore more
research & insights curated to help you earn a seat at the table.