With increasing compliance requirements and cyber-attacks on the rise, organizations see the need to give their security posture reinforcement. It’s no wonder that 84% of organizations believe that they would benefit from a cloud-native SIEM (Security Information and Event Management).
A SIEM tool is a crucial tool in the organization’s security arsenal but can be invaluable in identifying, investigating, and responding to all types of security threats in real-time.
TL;DR
SIEM tools centralize logs and security events from across your environment so you can detect threats faster and investigate from one place.
The best SIEM tools help teams spot anomalies in real time, reduce alert noise, and speed up incident response with correlation rules, analytics, and automation.
SIEM tools also support compliance by maintaining audit trails, ensuring log retention, and providing ready-to-export reports for standards such as SOC 2, ISO 27001, HIPAA, and PCI DSS.
Cloud-native SIEMs are usually easier to scale with modern stacks; open-source SIEMs can be cost-effective but often require more hands-on setup, tuning, and maintenance.
This article covers the top 15 SIEM tools and contains tips to help you pick the right one for your business.
What are SIEM Tools and how do they work?
SIEM tools are software solutions that gather, normalize, and correlate data from various sources within an organization’s network to respond to threats in real-time and enhance security posture.
SIEM tools work by using predefined rules and behavioral analytics to analyze the data collected from firewalls, servers, endpoints, and applications and spot any anomalies that indicate threats. These tools then generate alerts for security teams to respond to events before they escalate
Why is SIEM Software Important?
SIEM tools are crucial because they offer real-time visibility into security posture, enhance threat detection and incident management capabilities, centralize security data, and support compliance reporting.
Here are some of the benefits of a SIEM tool:
- SIEM tools track the virtual footprints of a cyber threat actor to help you understand when, how, and why a past attack/event happened.
- They can help you identify the origin of past attacks so that you can find and apply a suitable remedy.
- SIEM tools can effectively differentiate between legitimate system usage and malicious activity. This helps in safeguarding data and systems from incidents.
- As SIEM tools help with log management, they help you with auditing activities and help the organization comply with various compliance standards like SOC 2, HIPAA, PCI, etc.
- They help you protect your business reputation by helping you keep your IT infrastructure secure and avoid regulatory fines and penalties.
What are the common capabilities of SIEM tools?
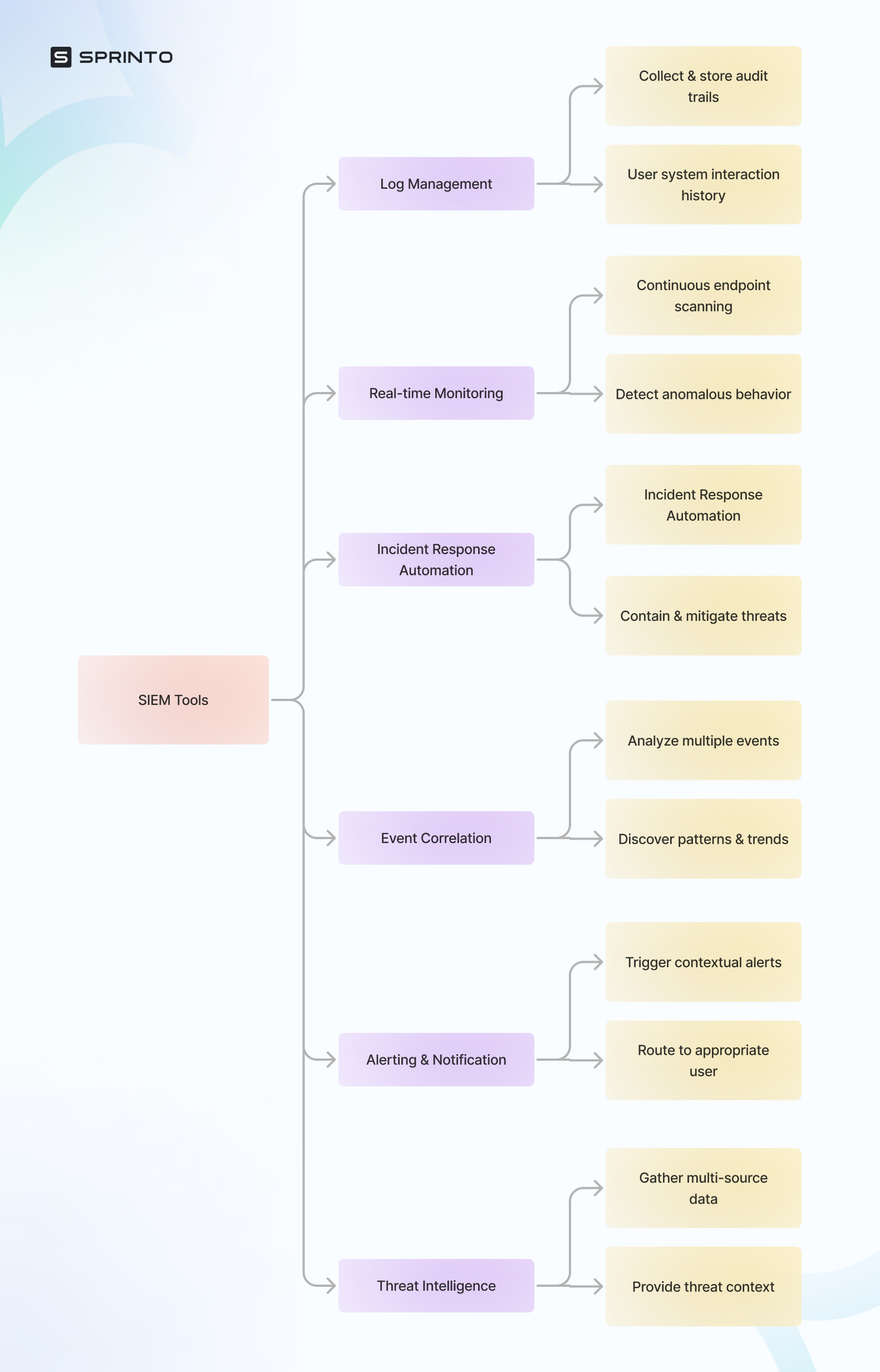
All Popular SIEM tools offer these basic features:
- Log management: Automatically collect and store audit trail for user system interaction to help investigate threats.
- Event correlation: Analyze multiple events to discover patterns and trends that may help to understand the broader context
- Real-time monitoring: Continuously run scans across the endpoints to detect irregularities or anomalous behavior
- Alerting and notification: Triggers alerts to the right user with relevant context of a threat to ensure quick resolution
- Threat intelligence: Gathers data from multiple sources like security feeds, research, and analysis to offer context into new threat events
- Incident response automation: Contain, mitigate, and remove the threat upon its detection. Prevent it from spreading to other systems
These features enable a variety of SIEM use cases, such as detecting insider threats through log analysis, identifying brute-force attacks through event correlation, flagging anomalous behavior in real time, and automating responses to contain malware. SIEMs are also widely used to streamline compliance audits by maintaining detailed logs and generating reports.
Top 15 SIEM Tools
Just like most cyber security and compliance tools, there is no one-size-fits-all SIEM tool for any organization. There are a lot of examples of SIEM tools in the market, and picking the right one for your business should be based on your goals and requirements.
Here are the top 15 SIEM software you need to be aware of:
1. Sprinto (Editor’s Choice)
Sprinto is a smart compliance automation platform that helps you establish strong SIEM practices in your organization. The cloud-based solution is perfect for all industries and helps you monitor security data and systems in real time to manage incidents effectively.
The tool helps your organization monitor and gather useful information to notify about threats as soon as they are detected and log them. It enables gap and risk analysis at an entity-level while automating security checks to help you meet security and compliance requirements.
As a compliance automation platform, Sprinto supports workflows for different compliance frameworks such as SOC 2, ISO 27001, HIPAA, GDPR, PCI DSS, NIST, and more. Sprinto also offers an intuitive real-time health dashboard that displays the compliance and security status of the organization. With such features, Sprinto is a great SIEM solution for organizations looking to implement and monitor security controls to shorten the time needed to gain compliance.
Features
- Comprehensive risk library for qualitative and quantitative risk assessment
- Automated log monitoring and auditing features
- Insightful and comprehensive audit-ready reports for auditors and stakeholders
- Compliance automation features to meet different regulatory requirements
- Event and incident management with incident response capabilities and systematic escalations
| Pros | Cons |
| Real-time threat monitoring and real-time threat detection Intuitive interface with easily navigable features Automated evidence collection to prove compliance Seamless integration with different cloud setups Serves all industries and has exemplary customer support | Analytics can be improved |
2. SolarWinds Security Event Manager
SolarWinds is a powerful SIEM tool that helps you monitor security threats in real-time. With comprehensive log management and reporting features, SolarWinds helps you with incident review and response as well as automated threat remediation.
Features
- Advanced log filtering and forensic analysis
- Real-time monitoring to flag suspicious activities
- Centralized log collection to maintain records
- Historical analysis to identify threat patterns and more
- Real-time system alerts to report breaches
| Pros | Cons |
| Wide range of integrations Easy log filtering Comprehensive dashboard Integrated compliance reporting tools | Steep learning curve |
3. Fusion SIEM
Fusion by Exabeam is a comprehensive solution that features SIEM and XDR (Extended Detection and Response) functionality for complete security coverage. The cloud solution offers intelligent threat investigation and log management with the help of behavior analytics to help you tackle cybersecurity with ease.
Features
- Automation features to reduce threat response times
- Detailed compliance reporting and rapid search options
- Report builder to easily generate comprehensive reports
- SOAR feature for advanced threat detection and response
- Pre-packaged workflows, response checklists, and automated playbooks
| Pros | Cons |
| Secure, off-site installation Automated threat responses to shut down attacks Smart alerts help reduce false positives for identified threats Advanced search options Helps you with compliance mandates | No free trial Complex for small organizations |
4. Graylog
Graylog is a log management and analysis tool for your security operations. The tool captures log messages from different systems and applications for complete security analysis. Graylog helps mitigate risks and security issues effectively with anomaly detection and user entity behavior analytics.
Features
- Advanced data collector for in-depth log collection
- Pre-written templates for SIEM functions
- Automated responses in case of threat detection
- Data visualization features for more visibility
- Comprehensive trends and metrics
| Pros | Cons |
| Ad-hoc query tool Easy and comprehensive reporting Adaptable SIEM functions Historical threat analysis | Not available for Windows Interface can be better |
Find out how Sprinto can help you manage security complaince
5. Datadog Security Monitoring
Datadog is a full-stack SIEM system that monitors live logs and collects log file entries. It analyzes all captured files and triggers alerts in case of any security incidents. With the automatic updation of threat detection rules, Datadog helps with security monitoring, log management, and audit trails to help you effectively strengthen the company’s security posture.
Features
- Real-time security event detection
- Advanced reporting and analytics
- Pre-configured threat detection rules
- Activity capturing from cloud systems and on-site applications
- Advanced alerting and notification features
| Pros | Cons |
| 500+ integrations Advanced threat detection User-friendly dashboard Real-time log monitoring | Can be complex for small organizations |
Recommended: List of best compliance monitoring tools.
6. LogPoint
LogPoint is an SIEM cloud platform that uses machine learning processes for activity tracking and threat detection. The AI-driven software easily detects manual intrusion and zero-day attacks using anomaly-based threat-hunting techniques.
Features
- UEBA module for activity tracking
- Threat intelligence feed for threat analysis
- Account takeover detection
- GDPR reporting to demonstrate compliance evidence
- Indicators of Compromise (IoCs) database to identify typical attack strategies
| Pros | Cons |
| Smart threat detection rules Insider threat detection Easily integrates with other tools Suitable solution for businesses that operate multiple sites | No free trial Limited compliance reporting features |
7. ManageEngine Log360
Log360 by ManageEngine is a great SIEM tool for threat detection and risk mitigation. The tool constantly monitors your files, folders, and logs and sends you real-time alerts in case of concerning changes. Log360 also features a compliance reporting module to help you with GDPR, PCI DSS, HIPAA, GLBA, and more.
Features
- Smart threat intelligence feed for threat analysis
- Integrates with over 700 applications
- Risk scoring system for users and entities
- Machine-learning-based threat detection
- Custom templates to create and set internal security policies
| Pros | Cons |
| Automated threat detection File integrity monitoring to identify breaches Manual data analysis tool Compliance management and log management | Not supported on LinuxUI is outdated |
8. Fortinet FortiSIEM
FortiSIEM is an enterprise-level SIEM tool that leverages behavioral analytics to quickly detect and respond to threats. With a built-in configuration management database, FortiSIEM easily builds your asset inventory and tracks each asset continuously to help you gain real-time visibility into your security status.
Features
- AI-driven behavior anomaly detection capabilities
- Automated threat response and remediation
- Compliance reports generation
- Real-time security analytics and insights
- Integration with other applications using robust APIs
| Pros | Cons |
| Security implementation across virtual networks Machine learning-based threat intelligence Streamlined workflows with built-in playbooks Self-learning asset inventory | Expensive than other tools in the segment |
9. LogRhythm
The LogRhythm NextGen SIEM platform is a solid asset for organizations to get comprehensive insights into their security posture to quickly prevent incidents. By automating threat detection and other labor-intensive repetitive work using LogRhythm, you can gain wider visibility into your entire IT infrastructure.
Features
- Log file management features
- Artificial intelligence-based threat detection system
- Deployment manager to configure your security settings
- Customizable dashboard to view the organization’s overall security status
- Immediate results with advanced search options
| Pros | Cons |
| Highly customizable, intuitive interface Uses machine learning for behavior analysis Beginner-friendly log management features Data visualization tools | No trial version Lacks cross-platform support |
10. Splunk Enterprise SIEM
Splunk is one of the leading names in the SIEM industry that helps you monitor logs and security data in real-time to identify and report potential vulnerabilities. Splunk Enterprise Security SIEM responds quickly to threats and allows security teams to create their own automated defense rules, threat-hunting searches, and more.
Features
- Automated workflows for quick threat response
- Event sequencing features
- Alert management capability to notify users of different threats and events
- Asset investigator to identify and list all apps and digital assets
- Risk scoring and remediation
| Pros | Cons |
| Highly visual and customizable user interface Enterprise-focused SIEM Uses behavior analysis to detect threats Easy event prioritization | Not cost-efficient for small businesses as compared to larger businesses Steep learning curve |
11. Rapid7 InsightIDR
InsightIDR is a two-in-one scalable platform that features both SIEM and XDR. The tool integrates agents on your cloud services to easily collect, upload, and analyze activity data. It is one of the best security solutions that offers endpoint protection with the help of a threat intelligence feed to detect and respond to threats.
Features
- Network security scanning to detect anomalies
- User and entity behavior analytics
- Centralized log management
- Insight Agents for endpoint detection and asset discovery
- Advanced threat alerting system
| Pros | Cons |
| SOAR functionality Automated threat detection and response Action Logging for audits Uses deception technology utilities | Limited to securing systems that are connected to the Internet (can’t protect offline systems) |
12. IBM Security QRadar
IBM Security QRadar is an industry-leading SIEM tool that is visual-heavy and provides security monitoring of your complete IT environment. It helps you with event correlation, threat detection, log data collection, Intrusion Detection System, and more. The software utilizes a built-in risk management solution and vulnerability databases to identify and prioritize security alerts.
Features
- Behavioral profiling technology to identify threat patterns
- Presets and workflows for different use cases
- Integrations with different security applications
- Out-of-the-box functionality to mitigate critical incidents
- Smart reporting features
| Pros | Cons |
| Visually appealing and highly customizable interface Easy use case building and rules creation Comprehensive log and event collection Strong threat intelligence | Search queries feature can be improved |
13. Trellix Helix
Trellix Helix is a modern cloud-based SIEM system that deploys agents on the organization’s network to collect and monitor data from different devices and endpoints. After detecting threats, Helix sends remediation instructions to the relevant security applications for a streamlined security process.
Features
- Threat intelligence feed
- Integrates seamlessly with third-party tools
- Anomaly-based security analysis
- Advanced log management to crawl network activity records
- SOAR functionality with pre-built playbooks
| Pros | Cons |
| Guided threat investigation UEBA functionality Advanced security analytics Integrated security insights from different applications | Reporting can be better |
14. Sumo Logic Cloud SIEM
Sumo Logic Cloud SIEM is a deep security analysis tool that improves visibility into your on-premise, multi-cloud environment, and hybrid infrastructure. It helps you understand the context and origin of the attacks. With streamlined workflows, Cloud SIEM automates threat detection and triage alerts to mitigate risks.
Features
- Built-in automation and playbooks
- Insight Engine to help you understand threats
- Intelligent log management
- User and Entity Behavior Analytics (UEBA) features
- Automated report generation
| Pros | Cons |
| Advanced search options Single, collaborative SIEM platform Automates core analysis tasks Powerful actionable insight and reporting | Integrations can be better Pricing is a bit expensive |
Also, check out: List of best cloud monitoring software
15. Elastic Security
Elastic Security is a SIEM system built on top of an open-source Elastic Stack. This tool helps in detecting and mitigating threats with the help of cloud monitoring, endpoint security, and real-time threat hunting. You can use Elastic Security for historical data analysis to visualize security-related data from different apps and a range of devices.
Features
- Live and historical data analysis
- Package of other security tools in the Elastic Stack
- Automated threat detection and response
- Environment-wide ransomware and malware protection
- Simplified reporting options to gain insights
| Pros | Cons |
| Customizable dashboard with drag-and-drop fields Intuitive user interface Effective log file management Unique, out-of-the-box threat hunting | Set-up is a bit complex |
Also, check out: Security audit checklist
Best open source SIEM tools in 2026
If you are looking for a basic solution to support a limited number of systems, open-source SIEM tools are the right choice. Here are some of the best tools you can consider:
AlienVault OSSIM
AlienVault OSSIM is an open-source SIEM tool that helps gain visibility into malicious hosts in real time. It offers a wide range of capabilities like event collection, normalization, asset discovery, vulnerability assessment, intrusion detection, and event correlations. It caters to risk managers, security administrators, tech consultants, and analysts. The tool runs on Windows and Linux OS.
MozDef (Mozilla Defense Platform)
MozDef automates the process of security incident management by detecting security events, analyzing the events, and facilitating real-time collaboration between threat handlers. It offers SIEM capabilities like accepting log events, strong events, enabling searches, and log management.
The architecture is built on open-source technologies like Nginx, RabbitMQ, uWSGI, bottle.py, Elasticsearch, Meteor, MongoDB, and Firefox. It runs on Mac and Linux.
Wazuh
Wazuh is a free and open-source platform that combines SIEM and XDR (extended detection and response) capabilities for endpoints and cloud-hosted systems. It aggregates and analyses telemetry in real-time to facilitate efficient threat detection. Users can conduct log analysis, configure assessments, and detect vulnerabilities by using data collected from endpoints, networks, cloud workloads, and applications. The platform is supported on Linux.
Prelude OSS
Prelude OSS enables users to collect, correlate, normalize, and aggregate security log events on small environments. The system triggers alerts upon detecting an intrusion in the network by using real-time logs and flow analyzers. Users can conduct forensic reporting on large volumes of data to discover weak signals as well as APT (advanced persistent threats). It runs on Linux and NIX.
Sagan
Sagan leverages AI and machine learning to protect cloud environments by continuously learning to identify credible and incredible threats. Its log analysis system is designed to support SOC operations.
Sagan’s centralized dashboard provides a quick overview of the operation status and security threats in real time. It displays security events on an Attack Map to help users gain visibility into all attack vectors. The tool offers custom reporting capabilities, domain tracking system, malware extraction, and packet analysis.
Difference between open source and enterprise SIEM tools
Open-source tools are not for advanced users and do not support complex systems. These are usually low maintenance, offer limited support, and are budget-friendly. Users get basic features like log monitoring and event data collection. If you are a growing company, consider switching to an enterprise-grade SIEM tool, as open-source systems are not built to process large volumes of data or are scalable.
Enterprise-grade SIEM tools charge annual or bundled subscription costs. These are built to process large volumes of data seamlessly, scale as you grow, and add more tech stacks to your system, and provide customer support. These tools offer customizable and advanced features like user behavior analysis, AI-based threat detection, signatureless malware identification, and more.
Benefits and drawbacks of using SIEM tools
Modern cybersecurity relies heavily on SIEM tools, which deliver multiple advantages. The tools deliver decisive benefits, including better visibility and regulatory compliance, yet their implementation requires complexity and financial commitment.
Organizations must know the positive and negative aspects of using SIEM tools to decide whether these solutions match their security needs. Let’s explore these in detail.
- Researchers can quickly analyze security data through pre-built and adaptable reports found in SIEM tools to identify patterns and detect abnormal activities while performing deep investigations of suspect operations.
- Organizations need SIEM systems to satisfy GDPR, HIPAA, and CCPA compliance requirements through reporting that explains data protection methods and reveals user and location details.
- SIEM simplifies searching and managing raw and parsed data by centralizing log file data and information from multiple systems.
- SIEM supports troubleshooting, enhancing security programs, and meeting audit and compliance reporting needs.
Drawbacks
- Setting up SIEM can take 90 days or longer, depending on the network size, and it requires seamless integration with existing security controls and infrastructure.
- Simply purchasing and installing a SIEM tool isn’t enough. Its effectiveness depends on proper setup, configuration, and continuous monitoring to ensure valuable insights.
- SIEM implementation requires a significant investment in time and expertise, and the initial costs can reach hundreds of thousands of dollars.
- While SIEM centralizes network activity data, it can become overwhelming and less effective if not contextualized and aligned with organizational goals.
How to Select the Right SIEM Software?
Every entry on this list comes with features and functionalities that suit organizations of every size and industry. However, selecting the best SIEM tool for your organization can be tricky.

Here are a few things you should remember while selecting the right SIEM software for your organization:
1. Evaluate your goals and requirements
Before selecting the SIEM software, evaluate your company’s specific goals and security requirements. Doing so will help you understand what exactly you want to achieve with the SIEM tool so that you can look for those particular functionalities.
2. Compare core features
The specific features and functionalities of the SIEM tool should address your security requirements. For that, you should evaluate core features and compare them. Some features like log data management, threat intelligence, regulatory compliance reporting, real-time analysis, etc can have a significant impact on your security operations and so, need to be evaluated carefully.
3. Look for user-friendliness
As the software becomes a crucial element of your security framework, it’s essential to ensure it comes with user-friendly features. A steep learning curve should stretch the implementation period significantly and may stand in the way of enhanced productivity.
4. Be budget-conscious
Finally, you need to consider the pricing of SIEM tools to choose the one that falls within your budget. Before deciding, attend a demo session or sit through a trial run to explore the extent of the SIEM tool’s features. A demo call also helps you clear any doubts about pricing, license and features that you may have.
Embrace continuous compliance with Sprinto
We took you through the journey of exploring the best SIEM tools in the market. Most of these tools and services follow a quote-based pricing model and may change as per your organization’s specific security requirements. However, if you are looking for a solution that can come with all the required features and add compliance certifications into the mix, Sprinto is just the option for you.
At Sprinto, we believe that both security and compliance are intertwined, and that’s why we help organizations build an unbreakable security stance through a continuous compliance framework.
Speak with our security experts, and we’ll get you started.
FAQs
SIEM tools collect and normalize security logs and events across your tech stack, then correlate them to surface suspicious activity. They give security teams a single view for monitoring, investigations, and reporting.
SIEM tools are commonly used to:
– Detect threats (e.g., brute-force attempts, unusual logins, privilege misuse, malware signals)
– Investigate incidents faster with centralized search and timelines
– Improve visibility across hybrid and multi-cloud environments
– Support threat hunting using historical log data
– Produce audit-ready reporting when compliance teams need proof of monitoring and logging
Many frameworks require logging, monitoring, and evidence of control operation. SIEM tools help by:
– Creating time-stamped audit trails (who did what, when, and where)
– Supporting log retention policies and consistent access to historical events-
– Generating reports that make it easier to demonstrate controls tied to frameworks like SOC 2, ISO 27001, HIPAA, and PCI DSS
They’re most effective when you also have a process to map SIEM outputs to specific controls and keep evidence consistently organized.
– SIEM focuses on centralized log/event collection, correlation, investigation, and compliance reporting.
– XDR (Extended Detection and Response) focuses on detection and response across security layers (endpoint, identity, email, cloud), often with strong native telemetry.
– SOAR (Security Orchestration, Automation, and Response) focuses on automating response workflows(enrichment, ticketing, containment steps).
In many environments, they work together: SIEM for visibility and reporting, XDR for detection depth, and SOAR for response automation.-
Look for SIEM tools that can prioritize and de-duplicate alerts, not just generate them. Helpful capabilities include event correlation, risk scoring, suppression rules, User and Entity Behavior Analytics (UEBA), and automated enrichment so teams spend less time on false positives.
Prioritize what reduces operational drag and improves outcomes:
– Integration coverage for your real log sources (cloud, identity, endpoints, SaaS, network)
– Fast search and investigation UX (your team will use it during incidents)
– Noise reduction (correlation, UEBA, tuning support)
– Retention and reporting that aligns with your compliance needs
– Automation hooks (playbooks, SOAR integrations, ticketing workflows)
– Transparent pricing that won’t surprise you as log volume grows
Pricing varies widely and is often driven by data ingestion volume, events per second (EPS), retention requirements, and add-ons such as UEBA, SOAR, or threat intelligence. Beyond licensing, factor in the real cost: implementation time, tuning, storage, and the people-hours needed to keep detections useful over time.
Author
Anwita
Anwita is a cybersecurity enthusiast and veteran blogger all rolled into one. Her love for everything cybersecurity started her journey into the world compliance. With multiple certifications on cybersecurity under her belt, she aims to simplify complex security related topics for all audiences. She loves to read nonfiction, listen to progressive rock, and watches sitcoms on the weekends.Explore more
research & insights curated to help you earn a seat at the table.