According to a report by Forbes, data breaches have surged by over 72%. The issue? Threats are outpacing security measures in terms of evolution, and volume. In a landscape where each vulnerability can lead to an exploit, cyber security monitoring can help you assess your security posture in real-time, and help you plug gaps for better, stronger resilience.
Shifting the mindset from protection to building resilience requires a new, deep perspective at an organizational level. It’s no longer about “this is how we’ll respond to an attack” and more “let’s assess what kind of risks could possibly persist in the first place”.
Investing in cyber security monitoring plays a crucial part by adding a proactive approach when integrating resilience into overall organizational cybersecurity strategy. It brings new attack vectors into light, helps build strong defenses, and identifies areas for fine-tuning.
This blog delves into the importance and examples of cybersecurity monitoring, along with actionable implementation steps.
What is cybersecurity monitoring?
Cybersecurity monitoring is a continuous practice aimed at observing a computer network or system to effectively identify and respond to threats and cyber attacks. The process employs tools like intrusion detection systems, firewalls, and antivirus software to detect and respond to security threats in real-time.
It plays a crucial role in proactively recognizing and mitigating potential threats and suspicious activities by continuously scrutinizing network traffic, activity logs, endpoint devices, servers, and other components.
Why cybersecurity monitoring is crucial for organizations?
Cybersecurity monitoring helps identify potential security vulnerabilities and protect mission-critical data across cloud environments, remote setups, and on-premise infrastructure. It provides a comprehensive view of an organization’s attack surface exposure, thereby reducing downtime and upgrading cyber resilience.
Here’s why you shouldn’t think twice when investing in cybersecurity monitoring:
Threat actors are progressing fast
With zero-day exploits, hackers today have started exploiting vulnerabilities not known to the developers. The rise of multi-stage and intricately planned attacks necessitate the need for swift detection and robust restoring capabilities. Cybersecurity monitoring acts as a watchful eye and an early warning system for the organization against evolving threats.
Response turnaround time must be expedited
Early threat detection and real-time alerts help in containing security incidents rapidly, minimizing prolonged threat repercussions and downtime. Cybersecurity monitoring acts as a business continuity enabler ensuring smooth operations and resolving events quickly.
BYOD policies are increasingly popular
While remote working and BYOD policies offer advantages such as cost savings, flexibility, and employee satisfaction, they also introduce security complexities. Additional endpoints become susceptible to malware infections, access from insecure environments, incidents of device loss or theft, etc.
Cybersecurity monitoring helps with better endpoint management, unauthorized access identification and deviations from normal behaviour patterns, enhancing data protection.
Compliance management has to be proactive
Cybersecurity monitoring enhances visibility into IT infrastructure and assists with threat detection, incident reporting, log management and other security activities.
The constant emphasis on maintaining a secure environment facilitates improves policy enforcement and active cybersecurity compliance management.
The constant emphasis on maintaining a secure environment facilitates improved policy enforcement and active compliance management.
Preventing breaches requires preemptive measures
IBM highlights that 51% of organizations are planning to increase security investments. Adopting a pre-emptive approach to data breach prevention, incident response (IR) planning, employee training, and threat detection.
Cybersecurity monitoring tackles this security stress by regularly implementing user behavior analytics to catch anomalies and help patch vulnerabilities. This helps organizations proactively protect data from the pressing implications of a data breach.
Talk to our experts now to learn more.
Sprinto has helped firms like Sensiba LLP, an audit and assurance firm, build resilient security practices and continuous compliance readiness with automated, continuous control monitoring. See how.
How does cyber security threat monitoring work?
Cyber threat monitoring ensures real-time network surveillance, by detecting unusual or malicious activities before they escalate into security incidents. This proactive approach involves continuously surveilling diverse elements within an IT environment, including network traffic, system logs, endpoint devices, and applications.
Here’s a comprehensive breakdown of how cybersecurity monitoring works and what it covers:
Endpoint monitoring
Endpoints, including laptops, desktops, smartphones, cell phones, and IoT (Internet of Things) devices, have their behavior analyzed. Endpoint monitoring enables the IT team to detect and prevent threats based on unusual, suspicious, or malicious behavior.
Network monitoring
Networks facilitate communication and information sharing among different devices. Network monitoring involves tracking and analyzing network behavior. Any anomalies, such as overloaded components, frequent crashes, or sluggish performance, can indicate potential cyber threats, making the system vulnerable. Diagnostic tools continuously assess components, maintaining logs of results. If any disturbance or threat is detected, automatic notifications are sent to the IT team through various channels, allowing them to address and resolve issues promptly.
Automated incident response
Upon detecting suspicious activities or potential threats, the system generates alerts and triggers automated incident response measures. This ensures swift containment and mitigation of the impact of identified threats.
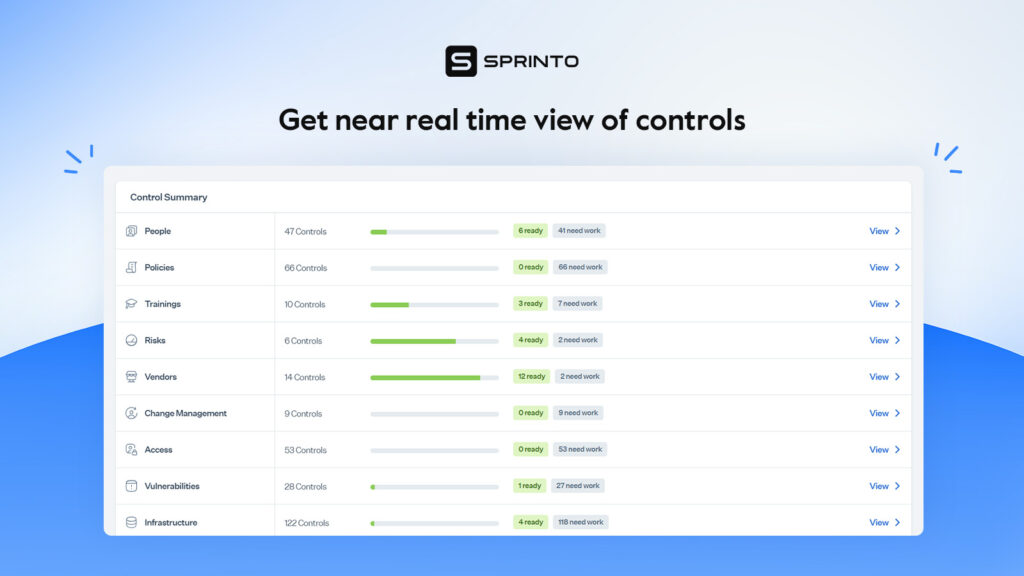
Experience the Sprinto advantage: Sprinto’s smart compliance automation solution enables you to get a comprehensive analysis of your current cyber security posture, continuously monitor cyber risks, run compliance checks to consolidate potential risks, and maps entity-level controls.
Check out How NitroPack fast-tracked compliance with Sprinto
How to implement cyber security monitoring?
Cybersecurity monitoring is implemented in four phases: identification, preparation, execution, and review. These phases encompass the identification of monitoring objectives, selection of the right tools, drafting policies, deployment of monitoring infrastructure, training of the workforce, and review of progress against threat detection.
Here are the 6 implementation steps you need to take:

Determine risk-specific security goals
While some organizations may look for a quick-patch, the longer, more structured method may prove more beneficial in the long run. High-risk assets and security priorities vary for businesses and that’s where risk-focused security goals come into the picture. To understand what an organization precisely needs from cybersecurity monitoring, it must:
- Assess the current threat landscape
- Align security and business objectives
- Foster collaboration amongst multiple stakeholders
- Score risks based on criticality
- Set measurable security goals
This helps chalk out a strategic plan tailored to your unique cyber protection needs.
Also check out: Cyber security goals
Source and vet the right tools
Your cybersecurity monitoring efforts can be supported by a range of tools-Security information and event management tools, intrusion detection systems, network traffic analysis tools, endpoint detection systems and more.
Base your decision on the fundamental risks identified and choose a tool that:
- Is compatible with the organization’s specific needs – check features and functionalities
- Fits the security budget – calculates real return on investment
- Integrates with other internal cybersecurity tools – look for faster setup and deployment
- Is intuitive – validate ease of navigation and user interface
- Has market reputation – check vendor reviews
You can pick a single tool to solve specific-problems, a combination of these, or a comprehensive tool like Sprinto that takes care of cybersecurity monitoring as well as security compliances.
Outline policies and procedures
A cybersecurity monitoring policy functions as a strategic compass, directing the team’s next steps. It must include purpose and scope, monitoring objectives, procedures and tools, roles and responsibilities, training, policy enforcement, and violations etc.
There should be a communication plan for the policy, any exceptions should be notified and all supporting documentation must be attached.
Experience the Sprinto Advantage: Sprinto, a compliance automation solution, helps you create cyber security monitoring for different compliance requirements with customizable policy templates. It helps you monitor your IT environment for security vulnerabilities, collect evidence, and recommend ways to remediate security gaps.
Deploy monitoring infrastructure
This is the next step in the preparation stage for seamless working of cybersecurity monitoring tools. Any server connectivity settings, configurations, backup mechanisms, and other infrastructure must be deployed. Since these components support crucial implementation efforts, they must be periodically tested and updated.
Train the Workforce
There are 3.5 million unfilled cybersecurity job vacancies in 2023 as per a report by cybersecurity ventures. The existing workforce has to battle the cyberthreat storm all managing juggling through various tasks and leading to frequent burnouts.
It is imperative to close knowledge gaps and empower the workforce with necessary resources for upskilling. Train them to identify and close vulnerabilities and let them earn those bug bounties!
Regularly review and improvise
To ensure continuous improvement, gather insights from incident response experiences, feedback from stakeholders and observations by surveillance teams. Also take into account industry trends and evolving threat patterns when collating these learnings and document the final summary as a trusted reference.
Cyber security monitoring tools and techniques
Cybersecurity monitoring tools are used to identify signs of malicious activities and other security risks and gain insights into network and systems behaviour. SIEMS, network traffic analysis tools, intrusion detection systems, endpoint management systems etc. are some examples.
Check out these cyber security monitoring tools with examples:

SIEM
Security information and event management tools help maintain a unified repository of security-logs in real-time. By gathering data from multiple sources, these tools enable event correlation and raise context-rich suspicious activity alerts.
SIEM’s extensive features also include automated responses as well as reporting and forensic analysis capabilities, making them a versatile tool for cyber monitoring.
Example: Exabeam Fusion
Exabeam Fusion is a cloud-first SIEM solution that is designed to help organizations with effective threat detection, investigation and response.
Core functionalities
- Centralized log Management with advanced search and filters
- Integrated threat intelligence for better threat detection
- Behavioural analytics and machine learning for identifying deviations
- Automated investigation for meaningful insights
Also read: Best practices of security compliance management
Intrusion detection systems
Intrusion detection systems serve as an early warning system for any unauthorized access, abnormal network behavior, malware infections etc. Network traffic is compared to baseline normal activities to identify any indicators of compromise and flag suspicious behaviour.
IDS help with proactive threat detection at initial stages thereby preventing them from becoming full-blown security events.
Example: Suricata
Suricata is an open-source intrusion detection and prevention system that uses a signature-based ruleset for identifying any malicious activity or abnormal network traffic behaviour.
Core functionalities
- Multi-threaded infrastructure for inspecting multi-gigabit traffic at high-speed
- Automated protocol detection for identifying malware
- Can capture and analyze data during TSL/SSL exchanges, HTTP connections and DNS activities for pinpointing any security compromises
- Network security monitoring for comprehensive visibility into potential issues.
Vulnerability scanners
Vulnerability scanners scan networks and systems to identify weaknesses or vulnerable points that can be exploited by hackers. These vulnerabilities include misconfigurations, weak passwords, suspicious applications and more.
By highlighting vulnerabilities and providing a detailed overview, vulnerability scanners facilitate swift patch management and guide other follow-up actions.
Example: Nessus
Nessus (developed by Tenable) is a vulnerability scanning solution with capabilities to assess both traditional IT assets and cloud infrastructure for any security weaknesses.
Core functionalities
- Comprehensive database of vulnerabilities for broader coverage
- Scans potential threats in cloud infrastructure before deployment for a reliable cloud environment
- Configuration auditing for identifying insecure configurations
- Remediation guidance after malware detection
Explore: List of Vulnerability scanning tools
Endpoint detection and response
Endpoint detection and response systems provide threat detection capabilities on endpoints like laptops, mobile devices, cloud, networks etc. These tools leverage machine learning, behaviour analytics and threat intelligence to identify any deviations in user behaviour, networks, processes and more.
EDRs raise contextualized alerts, reducing false positives and offer full-visibility into the endpoint while automating remediation.
Example: Carbon Black
Carbon Black is an endpoint detection system that provides instant visibility into endpoint devices, inside and outside corporate networks.
Core functionalities
- Incident triage for reducing downtime
- Tackles malware, non-malware (fileless attacks) and living-off-the-land attacks—the ones that can be bypassed by traditional security measures.
- Remote-shell access to endpoints for rapid troubleshooting and incident response
- Enhanced visibility from initial point of compromise to post-attack activities
Security compliance automation solutions
Security and compliance are inherently connected and so compliance automation solutions facilitate efficient cybersecurity monitoring. These tools give real-time visibility on security posture, evaluate effectiveness of security controls, escalate deviations while enforcing security policies.
These tools identify gaps and weaknesses in existing controls and also integrate with other tools like access management, vulnerability scanners etc.
Read how Sprinto helped Uncover, continuously monitor security gaps without additional infrastructure deployment and achieve compliance. We made sure security and compliance are ingrained to the organization’s core functions.
Benefits of cybersecurity monitoring services
The primary reason that businesses today are adopting CSM solutions is because of their ability for real-time threat detection, which helps organizations identify and prioritize security issues and other potential threats. There are other benefits associated with CSM; we have listed a few:
Facilitates risk management
Cyber risk monitoring is instrumental in offering valuable insights into potential risks and vulnerabilities. It equips businesses with well-defined response plans and protocols to handle crises in the event of a cyberattack effectively. This proactive approach enables organizations to deploy effective risk mitigation strategies, damage limitation, and expedited recovery to resume normal business activities promptly following an incident.
Improves visibility
Cyber security monitoring offers heightened visibility into your IT environment. This facilitates real-time monitoring of critical aspects such as network security and user access. By providing an overarching view of the security landscape, it enables the identification of vulnerabilities and the initiation of proactive measures for remediation and security event management.
Enables compliance
Compliance frameworks like ISO 27001, SOC2, HIPAA, PCI DSS, NIST, and GDPR necessitate continuous security monitoring. Organizations can ensure a perpetual alignment with the required security standards by seamlessly integrating Cyber Security Monitoring into their operational processes.
Elevate your security standards with Sprinto: Sprinto goes beyond automation; it orchestrates your chosen security frameworks, ensuring seamless alignment with diverse compliance requirements.
Helps avoid financial pitfalls
Cybersecurity incidents can lead to substantial financial repercussions, including expenses for addressing data breaches, the engagement of cybersecurity experts to investigate the events, legal proceedings costs, revenue loss due to disrupted production, and the implementation expenses of security measures to prevent future incidents. This underscores the importance of strategic investments in cybersecurity and threat monitoring, serving as a proactive approach to mitigate potential financial losses.
Automate Cyber Security Monitoring with Sprinto
In this complex digital landscape, every device, user, software and application are susceptible to vulnerabilities and that’s where cybersecurity monitoring precisely plays its part. However, the volume and complexity of data, latest attack patterns, round-the-clock monitoring requirements and skill and resource constraint call for automated solutions.
Sprinto uses adaptive automation capabilities for 24/7 monitoring and centralized visibility. It has in-built endpoint detection, templatized security policies and enforcement mechanisms as well as proactive alerting capabilities. There’s also automated evidence collection and auditor collaboration dashboard for painless audits.
Want to simplify cybersecurity monitoring and enhance your posture? Talk to our cybersecurity experts today.
FAQs
Cyber monitoring or cybersecurity monitoring refers to monitoring networks, systems, infrastructure, and human-driven activities to detect anomalies, system misconfigurations, unauthorized access, or other vulnerabilities in real-time or near real-time.
Key components of cyber monitoring include:
– Incident Response: Triggering alerts to help teams respond to detected threats in a timely manner.
– Network Monitoring: Observing network traffic for anomalies, intrusions, or unauthorized access.
– Endpoint Monitoring: Observing end-point devices (like computers and mobile devices) on the network to ensure their legitimacy.
– Log Monitoring: Collecting and analyzing logs from various systems and applications to identify security incidents.
– Threat Detection: Leveraging automation, continuous monitoring, and threat intelligence to identify potential risks early.
Automation reduces human effort and error by streamlining tasks like log management, data collection and analysis, round-the-clock monitoring, swift threat detection and response and compliance management. These solutions are scalable, handling large and complex data with ease and help organizations stay ever-vigilant.
Network traffic analysis tools track network activity and traffic in real-time. Any potentially malicious behaviour is detected after studying network data packets while supporting forensic investigations and incident response.
Some challenges in implementing cybersecurity monitoring include growing sophistication of threats, large volume of alerts and false positives, less trained personnel, budgetary constraints and maintaining visibility in remote environments.
It depends on your relationship with the vendor, the sensitivity of information being monitored and legal or contractual requirements.
Author
Payal Wadhwa
Payal is your friendly neighborhood compliance whiz who is also ISC2 certified! She turns perplexing compliance lingo into actionable advice about keeping your digital business safe and savvy. When she isn’t saving virtual worlds, she’s penning down poetic musings or lighting up local open mics. Cyber savvy by day, poet by night!Explore more
research & insights curated to help you earn a seat at the table.

























