If you’ve ever wondered about the magnitude of power cyber threats hold, this one’s for you.
May 8, 2022. The Costa Rican president had to declare a national emergency because of cyber attacks by the Conti Ransomware Group. The world was caught unaware.
Cyber crimes can put an individual, organization, or a whole country at risk. The costs associated with data breaches can cause havoc. So prioritizing cyber security becomes a non-negotiable.
But in order to do so, you first need to understand the ultimate goals of cyber security. Next, we’ll hop on to the tools you can count on to achieve those goals.
What are Cyber Security Goals or Objectives?
The goal of cyber security is to ensure secure storage, control access, and prevent unauthorized processing, transfer, or deletion of data. It safeguards the confidentiality, integrity, and availability of information.
A number of cyber security measures are put in place to protect networks and computer hardware from unwanted threats and damages. Organizations draft security goals and policies based on the cyber security standards they are required to uphold.
What are the Three Pillars of the CIA Triad?
CIA triad stands upright on three pillars–Confidentiality, Integrity, and Availability. People, Processes, and Technology come together to attain these objectives of cyber security and ensure effective security systems.

Confidentiality:
Collecting, storing, and sharing data in the digital space have made us prone to cyber attacks. Confidentiality states that only authorized people should be able to access sensitive information.
Any Personal Identifiable Information (PII) that can help recognize a person, any financial information such as transaction details made on e-commerce sites is supposed to be kept confidential.
Integrity:
Ever remember clicking on a checkbox that says ‘I declare that the information provided is correct and accurate to my knowledge? This is essentially a declaration of integrity.
Integrity maintains the dependability of information and ensures that it has been in its original form throughout and is exact. Stored data or data disseminated or used should not be altered at any time unless authorized by a licensed individual or system
Availability:
Availability ensures the accessibility of information to authorized personnel at the right time. They should be able to process data whenever the need arises.
Also check out: Best Practices of Cybersecurity
Stay Ahead with Automated Continuous Compliance
What tools can help you achieve CIA triad goals?
Understanding cybersecurity objectives isn’t always easy. But achieving CIA triad goals is possible with a little commitment, structural enhancements, and regular surveillance.
Talking about tools, here’s the list you need:
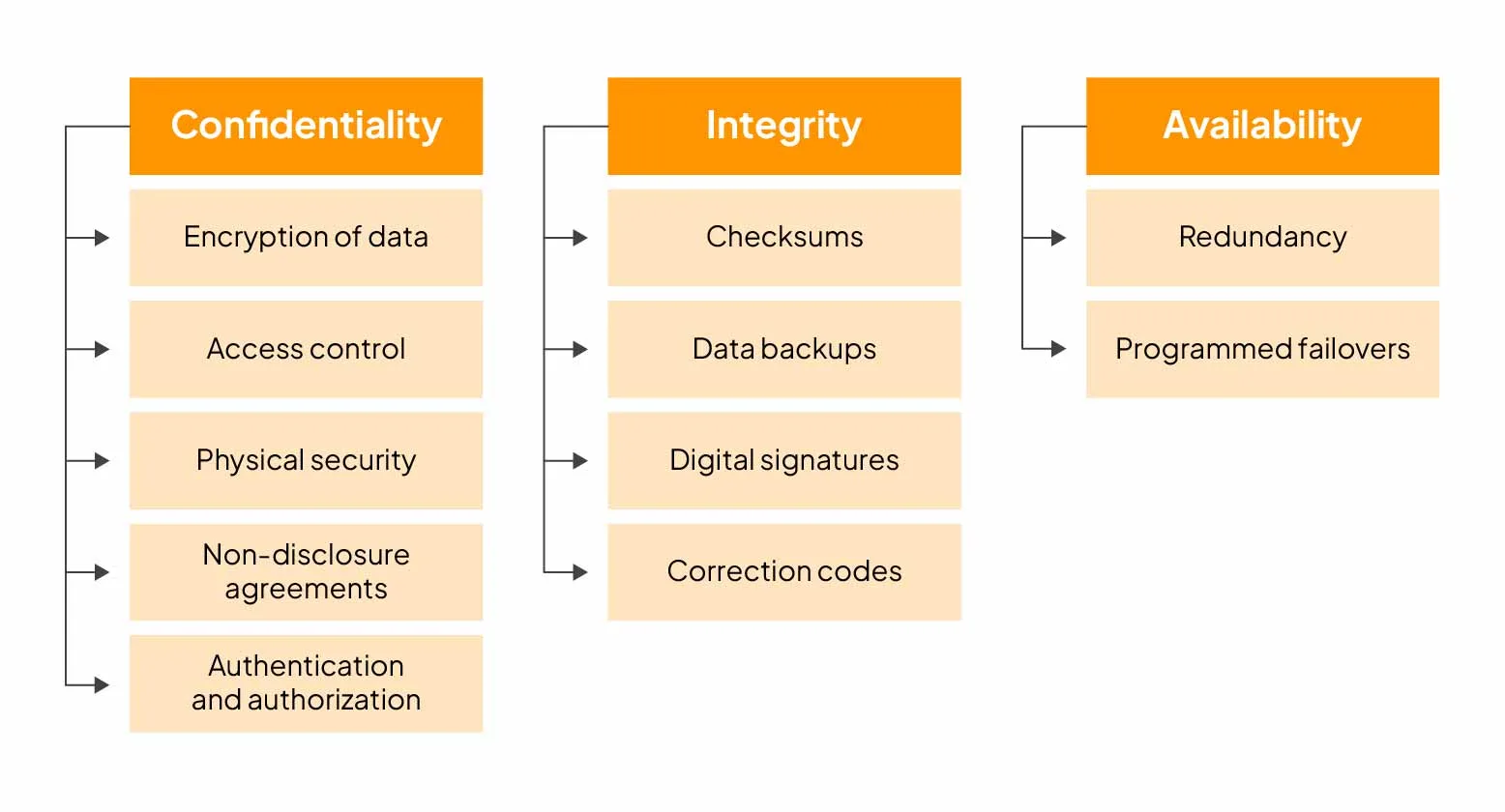
Achieving Confidentiality
The confidentiality of information that is stored or transmitted needs to be maintained. Identify the information that is sensitive and employ the following tools or methods for achieving confidentiality:
1. Encryption of data
An unencrypted email from the U.S. Marine Corps Forces Reserve was leaked. It contained confidential information about 21426 marines, sailors, and civilians and put them at considerable risk.
Sensitive information such as personal or financial data needs to be encrypted to maintain confidentiality. Encryption, by definition, is the modification of simple information into a coded format to prevent unauthorised access or use. Encrypted data can be decoded by an encryption key and only those who have the key and the authority can view the data.
2. Access control
The information access to the personnel should be functional minimum. People should have permission and access to data on a need-to-know basis. This is known as Role-Based Access Control (RBAC). Sprinto supports RBAC for proactively segregating duties on the basis of defined roles.
In a digitally complex architecture with local, hybrid or multiple cloud networks, following a zero trust security discipline becomes imperative. Zero trust security suggests that when it comes to security matters, organizations should verify everyone irrespective of who it is. So there should be strict access controls verified through login credentials or multi-factor authentication.
3. Physical security
Physical security includes a wide range of measures that prevent unauthorised access to electronic information assets. This protection is ensured from both natural and environmental hazards and any kind of intentional encroachment.
Installing security cameras, fire safety systems, biometric access controls, etc. are some methods employed for ensuring physical security.
4. Non-disclosure agreements
Every cyber security plan should include the element of non-disclosure. Employees and vendors should safeguard confidential and proprietary information. One way of doing this is by getting employees to sign non-disclosure agreements (NDAs). NDAs enforce the legal use and consequence of exchanging confidential information and enable businesses to share it with credence.
Effortless, Efficient Risk Evaluation
5. Authentication and authorization
If you are a large and complex organization with hundreds of employees and multiple software solutions, you will appreciate the discipline of Identity access management (IAM). IAM establishes a centralized access control system and authentication and authorization are the two pillars on which it stands. The workflow inherently prevents unauthorized intrusions by verifying the user’s credentials at various stages.
Ensuring Integrity
Ensuring that the information stored or transmitted is reliable and accurate requires commitment from the organization along with the employment of the following methods:
1. Checksums
In order to ensure that the data is in its original form, checksums are used to detect transmission errors. A number sequence is assigned to the data by the sender and the same checksum function is used by the receiver to compare the values. A difference in the value signals error.
The employed algorithm helps discern any corrupted files that have been downloaded and checks overall integrity.
2. Data backups
Unexpected human errors, malware attacks and hardware issues can cause permanent data loss. Data backups help in moving a copy of master data to a secondary location so it can be used in emergencies.
Data backups and maintenance activities should be pre-scheduled and customers need to be notified of them to avoid disruptions.
3. Digital signatures
Digital signatures are a hallmark of authenticity that indicates that the data sent is original and valid. Behind the scenes, a pair of public and private keys work on authenticating digital signatures. The private key encrypts the sender’s signature while the public key helps in decryption and verification.
4. Correction codes
We all want data to be transmitted with precision and carrying no errors.
Data is transformed into bits during dissemination. As a result, there can be single-bit errors, errors in two or more bits or change in set of bits known as burst errors during transfers.
Error correction codes help in identifying and rectifying these errors throughout transportation.
Enabling Availability
In order to ensure that the right information is available to the right people at the right time, you can count on the following:
1. Redundancy
A redundancy plan helps understand when and how to duplicate components. It is usually created to avoid availability issues and in cases of server glitches or infrastructure failure. So in case of accessibility issues, you can directly hop on to the next source of information.
2. Programmed failovers
Programmed failovers and redundancies go hand in hand. Once you’ve duplicated data as a part of the redundancy plan, it’s important to understand how to automatically shift to a failsafe. A programmed failure helps seamlessly shift to a backup system without manual intervention or delays.
Also check out: 15 Best Cybersecurity Tools
Become security compliant with Sprinto
The implementation of CIA triad goals dictates the security culture of the organization. But it requires putting various practices into place like data encryption, multi-factor authentication, data backups, etc. as discussed above. Not only do security compliances tick off the boxes for better reputation, labor savings, and avoiding financial repercussions but they also keep data risk worries at bay.
Shield your organization’s data and meet the best security practices standards with Sprinto. As a comprehensive security automation platform, Sprinto eliminates the manual effort required to get your organization audit-ready. Learn how Scylla scaled their security and privacy with Sprinto.
FAQs
What are some cyber security goal examples?
Examples of cyber security goals include one-time passwords, use of biometrics, ATM receipts after withdrawal of cash, transaction history of mobile applications for payment, etc.
What are smart goals for cyber security?
Smart goals for cyber security stand for Specific, Measurable, Achievable, Relevant and Time-oriented goals. These goals should specify who, how and what needs to be secured. They should stand true to certain metrics, must be achievable, purposeful and be dealt with on time.
What are some examples of cyber security threats?
Distributed denial of service (DDOS) attacks, phishing, malware, password cracking, data tampering etc. are some examples of cyber security threats.
Author
Payal Wadhwa
Payal is your friendly neighborhood compliance whiz who is also ISC2 certified! She turns perplexing compliance lingo into actionable advice about keeping your digital business safe and savvy. When she isn’t saving virtual worlds, she’s penning down poetic musings or lighting up local open mics. Cyber savvy by day, poet by night!Explore more
research & insights curated to help you earn a seat at the table.