Over the years, stringent laws have come into effect, along with the introduction of most advanced threat detection and prevention technologies. However we continue to encounter familiar breach stories—employees using weak passwords, opening malicious emails, misusing too many permissions, etc. No matter the geography, hackers worldwide have been playing on human behaviors, attitudes, cognition, and beliefs to exploit vulnerabilities.
A strong company culture for security addresses this. It equips employees to respond and adapt to risk while allowing them to develop strong security practices. It empowers them to identify potential threats and react proactively to address them with a sense of responsibility. A report by CISCO backs states that organizations that foster a culture of security see a 46% increase in resilience.’
Read on to learn how to build a culture of security in the organization, the strategies that will help you, and how Sprinto can be an enabler in this journey.
What is security culture?
Security culture is a set of values, beliefs, and behaviors that exhibit security consciousness in the organization’s day-to-day operations. The element of culture helps organizations take a security-first approach and get measures in place to handle security-related matters with the intention of minimizing risk and cyber incidents.

Why is security culture important in every organization?
Creating a company culture centered around security is foundational in achieving long-term security goals and improving organizational maturity. Employee understanding, principles, and conduct are key determinants of the organization’s ability to protect itself from vulnerabilities and breaches.
Here are 4 reasons why security culture is important:
Long-term benefits
Building a culture of security is a long-term approach with continued benefits because of changes in attitude and behavior. For example, a security-conscious employee will automatically lock a device when not in use to prevent unauthorized access out of habit.
Reduces human error
Human error is often considered the most common cause of cybersecurity attacks. Verizon report attributes 82% of breaches to human error. A security culture framework ensures that security practices are incorporated into daily operations, ensuring that security risks are kept to a minimum.
Increases adaptability
When cyber security culture is made part of routine tasks, it reduces any friction caused by the advancing threat landscape. Employees readily accept any changes in existing practices or new initiatives to stay abreast of the evolving digital environment.
Enhanced customer confidence
A strong company culture for security is often visible to client during interactions. It can be a key differentiator and unlock better business opportunities. It enhances customer trust by putting security best practices in action while maintaining data in accordance with the CIA triad, namely confidentiality, integrity, and availability.
Get Compliant Ready Without Any Hassle with Sprinto, Talk to Our Experts Now
Steps to creating a company culture for security
Building a company culture for security has impacts across three fronts—people, processes, and technology. It often involves discarding outdated technology, processes, and ideas and aligning the company with the new directives and policies that put security at the base of everything they do. But this is easier said than done.
There are six steps to creating a security-first company culture:
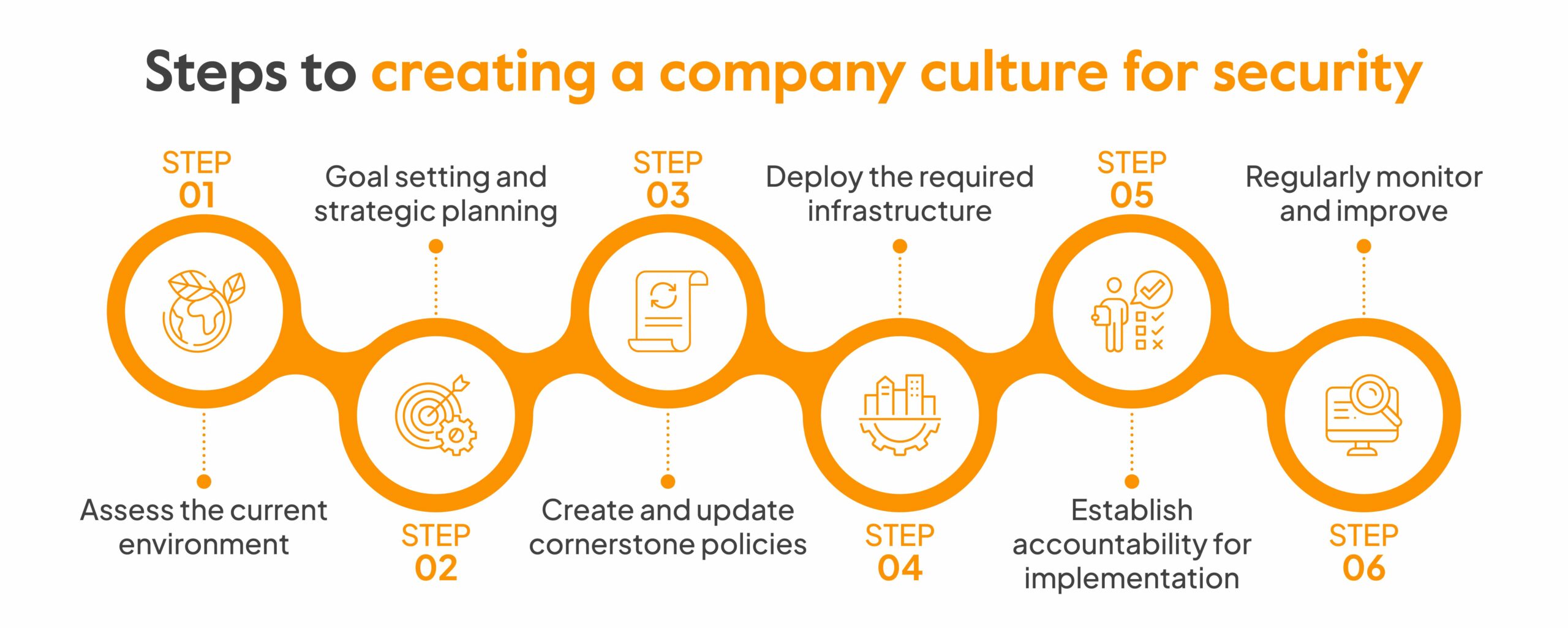
Assess the current environment
Take stock of the present situation and assess current practices. This must begin with a documentation review to understand the loopholes in policies. Next, gauge the effectiveness of controls in place with data and metrics. These may include security incident reporting and response rates, the number of people with overly permissive settings, vendor due diligence, etc. Additionally, conduct interviews and surveys to understand the challenges faced by security teams.
Goal setting and strategic planning
List the outcomes you want to achieve and the desired cyber security culture you wish to build. Then, reverse engineer these outcomes to set goals for every function and resource. For example, if the outcome is improving network security, then goals for different functions can be:
- IT team: Regular updates of network devices and services, network segmentation, vulnerability assessments, implementing IDS/IPS, etc.
- Legal team: Periodic assessments to check if network security compliance requirements are met, staying abreast of changes, etc.
- Non-technical Employees: Complete security training, report suspicious activities, enable strong passwords, MFA, etc.
Top 3 recommendations for companies to effectively convey their security posture?
Communication transparency: Companies must be able to demonstrate that they have been keeping customers in the loop at the time of events
Third-party audits: Compliance with regulations like ISO 17001 involving third-party audits instills greater trust in security posture
An Information security statement or a Trust Center where customers can find information about controls, compliance status, documentation etc.
Ayman Elsawah (vCISO,) Sprinto
Great advice adds up. Get more from the brightest minds in GRC — Subscribe to our newsletter
Create and update cornerstone policies
You can either scrap or update existing policies to accommodate changes based on the objectives and desired goals set for every function. Draft new policies for fresh initiatives and subject them through stakeholder review for consent/approval before starting with the implementation phase.
Deploy the required infrastructure
The next step is to make security investments that align with the above objectives and goals. A budget must be set out and reviewed by the top management. Some must-have technologies to build a cyber security culture include intrusion detection systems, firewalls, encryption tools, etc.
You can also go for a comprehensive solution like Sprinto and get access to all these advanced technologies like incident management, endpoint detection etc. at one place.
Learn how you can do it here.
Establish accountability for implementation
Establish clarity in defining roles for various security functions like access reviews, network security, awareness training, etc. Finalize an implementation timeline and key performance indicators for accountability. Performance reviews at the end of the stipulated time will then clarify security successes achieved.
Regularly monitor and improve
After the implementation phase, the only goal is to iterate and improve to maintain a sustainable security culture. Regularly monitor the progress on the execution front. Analyze logs, policy adherence, documentation management, evidence collected, etc. to identify remaining gaps and provide recommendations.
Now that you’ve learned how to create a company culture for security let us look at some strategies to help you.
Automate Your Compliance Journey with the Help of Sprinto. Talk to Our Experts Now
Strategies for building a strong security culture
While selecting various strategies to build a security culture, remember that the objective is to make employees understand that security is a shared responsibility. The tactics should shift their attitudes, beliefs, and behaviors toward becoming a human layer of defense against breaches.
Here are 6 strategies that will aid you in creating a company culture for security:

Let leaders start
Commitment begins at the top. The CISCO report we mentioned above also suggests that Organizations with poor support from top executives have 39% lower security resilience scores than those with buy-in from the top.
Leaders should both ”show” and ”tell” the employees that they are dedicated to prioritizing security. They must lead by example, addressing security concerns while making key decisions, participating in training, and establishing processes around security (like reporting culture).
Plan training sessions
The training programs can be designed for different levels of awareness. There can be security training during onboarding and periodic refresher awareness programs. The topics must be pre-planned and updated periodically to align with the evolving cybersecurity environment.
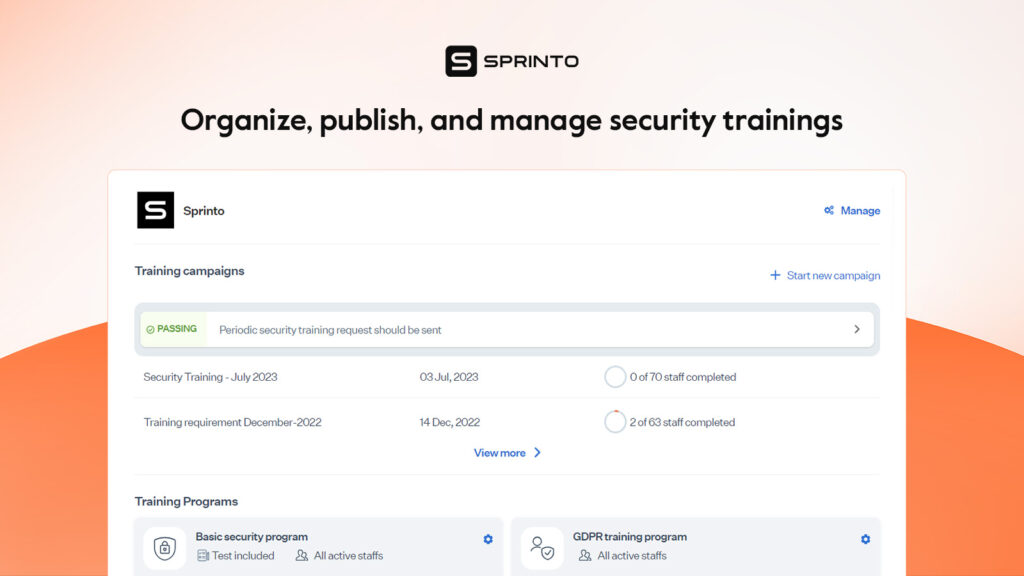
How Sprinto can help here:
We have in-built security training modules that can be automatically published across the organization and maintain a log of training completion. Alerts for due and overdue training are also emailed to employees until completed.
Acknowledge and offer incentives
Completion of security certifications, reporting of a phishing email, quick first response to an incident, etc., must be celebrated. Appreciate these security successes and milestones using a mix of public acknowledgments and monetary rewards—cash prizes, gift cards, bonuses etc. It can motivate employees to push themselves and ensure better org-wide security.
Secure Software development lifecycle
A secure software development lifecycle indicates that security is at the forefront. It integrates practices like security testing, vulnerability assessments, code reviews, etc., and addresses them at the development stage. The risks are taken care of at the design phase, saving costs and time while weaving security as an inherent part of the process. This plays a vital role in establishing the importance of security consciousness throughout the organization.
Conduct regular security audits
Making regular security audits and assessments as a mandate sends a clear message across the organization that their actions will be monitored and evaluated periodically. This establishes accountability and responsibility and pinpoints security gaps that must be fixed to ensure continued improvement.
Seek professional help
Implementing a culture of security can be challenging in practice. It will require several policy and procedural changes, automation of tasks, regular assessments, and comprehensive reporting. The best way out is to seek professional help and reap long-term benefits.
How Sprinto can be an enabler here:
We ensure security and compliance become your default state with out-of-the-box policy support, continuous control monitoring, real-time reporting, proactive alerts, and automation-led workflows.
The tasks are broken down into simple human terms and our experts hand-hold you through the implementation phase. There is no loss of unnecessary bandwidth by employees while ensuring no loose ends in security and compliance.
The security culture framework can also greatly help if you are just starting out. Let’s deep dive into what this is.
What does the security culture framework include?
Security culture framework (SCF) is an open framework that provides a baseline for organizations to elevate employee security consciousness. Businesses struggling to build a security culture from scratch can use these guiding steps to initiate and make progress.
The 4 steps in the framework are:

Defining key metrics
Elaborate on what the ideal security-conscious culture looks like for your organization. Then, take a data-driven approach to define the key metrics for achieving the desired state. The performance indicators could be training completion rates, phishing email reporting rates, incident response effectiveness percentage, etc. These are subjective and will depend on your organization’s key goals and outcome objectives.
Involving stakeholders
Businesses often need to be more aware of involving only IT teams in cybersecurity. A security culture is, however, built at the organizational level and requires collaborative efforts. For example, implementing strong passwords and enabling MFA is everyone’s responsibility. Involving all key stakeholders brings this sense of ownership, commitment, and accountability.
Conduct quizzes, interviews and surveys to determine security awareness levels and take diverse opinions from employees to build the framework.
Determining topics for cybersecurity awareness
The topic selection can be divided into categories
- General cybersecurity awareness: Understanding of regulatory requirements, industry best practices
- How to spot indicators of compromise: identifying phishing attacks, compromised accounts etc.
- Response techniques: how to respond to incidents, reporting malicious emails etc.
This is a general wireframe but the topic selection can be customized based on the specialized needs of the organization’s security.
Drafting the final planner
The last step is to draft a planner that helps take the organization’s security from its current state to its desired state. It must contain information on policy updates and new SOPs aligned with conscious security practices. A review period must also be defined to measure progress and make iterative changes for further improvement.
What does the security design document include?
A security design document addresses aspects of information systems. The document is a blueprint of the design and implementation that must be followed from start to finish to ensure uncompromised security. The creation of a design document orients its company culture with security and includes the following sections:
Authentication systems: This requirement will lay down the authentication and authorization mechanisms needed for accessing critical systems and services.
External website security: This section will include all initiatives that protect the company website from external threats and hacking. For example, regular software updates, using SSL/TSL for secure connections, web application firewalls etc.
Internal website security: These websites are primarily used by employees and facilitate internal coordination. It is crucial to ensure their security because it contains sensitive information and key assets. Examples of recommendations on internal website security include access controls, webpage encryption, training, etc.
Remote access solution: Remote access solutions facilitate employees spread across different locations to work together and manage key resources. The document will specify the features that will ensure that the remote access solution is secure. For example, authentication and authorization, endpoint security, firewalls, intrusion protection systems etc.
Firewall and basic rules recommendations: This section specifies general firewall configuration recommendations. For example, firewalls must block all traffic by default and allow only permitted traffic. Then, there can be port-based rules allowing traffic on only specified ports.
Wireless security: This section discusses the security must-haves for wireless technologies—for example, network segmentation, strong encryption, intrusion detection etc.
VLAN configuration recommendations: Security protocols for using virtual LANs are laid down here. An example could be using a separate VLAN for guest devices.
Laptop security configuration: These security measures are expected from device users to ensure security. Strong passwords, antivirus, operating system updates, etc. are some examples that will be included in this section.
Application policy recommendation: These security measures will dictate the use of software applications. There must be procedures for installing new applications and removing unused applications, regular updates of applications, access permissions etc.
Security and privacy recommendation: This section will discuss how to ensure the safety and privacy of sensitive information. For example, revoking access to offboarded employees.
Intrusion detection and prevention: This section covers security actions to be initiated when an intrusion is detected. For example, network segmentation, penetration tests etc.
Collaborate with Sprinto to foster a security culture
Raising the bar on security is far from straightforward. It can face a lot of resistance from employees, cause difficulty in grasping technical details, and bring challenges during enforcement. Sprinto has the right strategies, guidance, and resources to help you with enablement.
At Sprinto we believe security and compliance are intertwined. Our platform doesn’t just incorporate best practices but puts security and compliance programs on autopilot. We help you enforce readymade security policies, monitor controls in real-time, report gaps, and automatically capture evidence to expedite corrective action. We help you implement effective security measures like risk assessments, vendor management, and access controls, and make it easier for employees to embrace security consciousness.
Talk to our security compliance experts today. See Sprinto in action.
FAQs
What are examples of a strong security culture?
Examples of a strong security culture can be having well-defined security policies, employees responsibly reporting incidents, granting minimum necessary access controls to critical assets, and regular security audits.
What are the 7 dimensions of security culture?
The 7 dimensions of security culture are attitude, behavior, cognition, compliance, communication, norms, and responsibilities. These are tied to human factors having a direct or indirect impact on the organization’s security culture and are reflected through feelings, beliefs, actions, etc.
How to build a culture of reporting security concerns?
There must be clear policies for reporting of security events. Employees must believe they can report security concerns without fear or retaliation. There can be anonymous reporting channels, online forms, emails etc. They must also be trained about the importance of timely reporting of security concerns.
Author
Payal Wadhwa
Payal is your friendly neighborhood compliance whiz who is also ISC2 certified! She turns perplexing compliance lingo into actionable advice about keeping your digital business safe and savvy. When she isn’t saving virtual worlds, she’s penning down poetic musings or lighting up local open mics. Cyber savvy by day, poet by night!Explore more
research & insights curated to help you earn a seat at the table.






















