In the age of cloud computing, information is vulnerable. Bad actors are always on the lookout for their next target. They scope for vulnerabilities in an organization’s ISMS (Information Security Management System) and exploit them.
This often disrupts business activities.
Employees are the weakest security link, which is why ISMS awareness training is essential. An automated security training platform helps deliver role-specific training modules and track completion across the entire organization.
The first step toward a secure ISMS is acknowledging that every employee is a potential target. Security vulnerabilities often enter through human error, which is precisely why ISMS awareness training reduces organizational risk exposure more directly than most technical controls can. Upon acknowledgment, organizations can convert their employees into their first line of defense.
In this blog guide, we will discuss the importance of ISMS awareness training and how you can develop an effective ISMS training program. Let’s get right in it!
What is ISMS Awareness Training?
ISMS awareness training ensures all employees have the required skills to handle the ISMS effectively. Organizations that know how to build a compliance program treat this training as an embedded control rather than a last-minute pre-certification activity.
ISMS awareness programs introduce employees to information security and its associated risks. Also, the roles of every employee are made clear concerning the ISO/IEC 27001 so that everyone understands what is expected of them.
What does ISO 27001 talk about the ISMS awareness training?
Information security training is an essential ISO 27001 requirement under Clause A.7.2.2. Before budgeting for these programs, understanding your ISO 27001 certification cost helps allocate resources across training, tooling, and audit preparation. Clause 7.2 states that organizations should determine the competence of people involved in implementing and working the ISMS.
Clause 7.3 requires employees to understand the information security policy and their role in the ISMS. Using standardized ISO 27001 policy templates ensures these policies are clearly documented and accessible for training purposes. This is why organizations establish a culture of information security to keep the ISMS processes streamlined.
How to develop and implement an effective ISMS Training Program?
Developing an effective ISMS training program is important to efficiently maintain your information security management system. Here are a few things you should consider while developing the training program.

- Define Your ISMS Objectives & Scope
The first step before developing your ISMS awareness and training program is to clearly understand your goals and the people you want to reach. ISMS objectives should align with your risk assessment report. Risk management software helps connect these objectives to quantified risk scores, ensuring training priorities match the organization’s actual threat landscape. The ISMS scope should mention all the relevant information assets and processes related to the ISMS.
- Develop a Security Culture
Once you define these, you will clearly understand your target audience, their expected roles/responsibilities, their learning needs, and the topics/courses you must cover.
Security culture in the organization influences how employees and partners look at ISMS and its potential issues to act on. By developing a security culture, you will understand your organization’s current security posture and what needs to be done to achieve a better framework with security-driven values and beliefs.
This step is crucial as it helps you align your security awareness program with the organization’s culture and goals. Moreover, a culture of information security in the organization is the key to the effectiveness of ISMS. - Use Multiple Awareness & Training Techniques/Materials
To keep your employees engaged, you need to have a range of formats and techniques for your ISMS awareness training program. While some prefer online learning courses, others might look for old-school training methods such as seminars and hands-on workshops.
So, use a variety of formal and informal ways such as workshops, quizzes, e-learning courses, seminars, webinars, posters, newsletters, simulations or try to use an ebook templates Being interactive in your approach with a combination of text, image, video, audio, and other elements goes a long way. - Personalize Your Training Program Content & Delivery
Customization of your content and its delivery is crucial for employees from various departments to easily grasp the concepts of ISMS. To make the awareness program more effective, you can divide your employees into different groups per their roles, responsibilities, locations, access levels, and more.
For different groups, you can tailor your content and delivery accordingly. This means using a different approach, a different set of examples, maybe different languages, and more to keep the training sessions fun and effective.
You can also include stories, case studies, emotions, and humor to connect with the employees personally. This way, they can better understand what is expected from them. - Analyze, Evaluate, and Improve your Program
Regular evaluation and improvisation are the key elements for developing a successful ISMS awareness program. To measure your program’s impact and value, you need to collect data and feedback from employees and stakeholders and analyze it.
You can conduct surveys, tests, interviews, audits, assessments, focus groups, and more to gather metrics and evaluate the program’s effectiveness.
Based on the results, you can identify what is going right and what is going wrong so that you can make the necessary changes to improve your ISMS awareness training program over time.
What Does the ISMS Training Program Include?
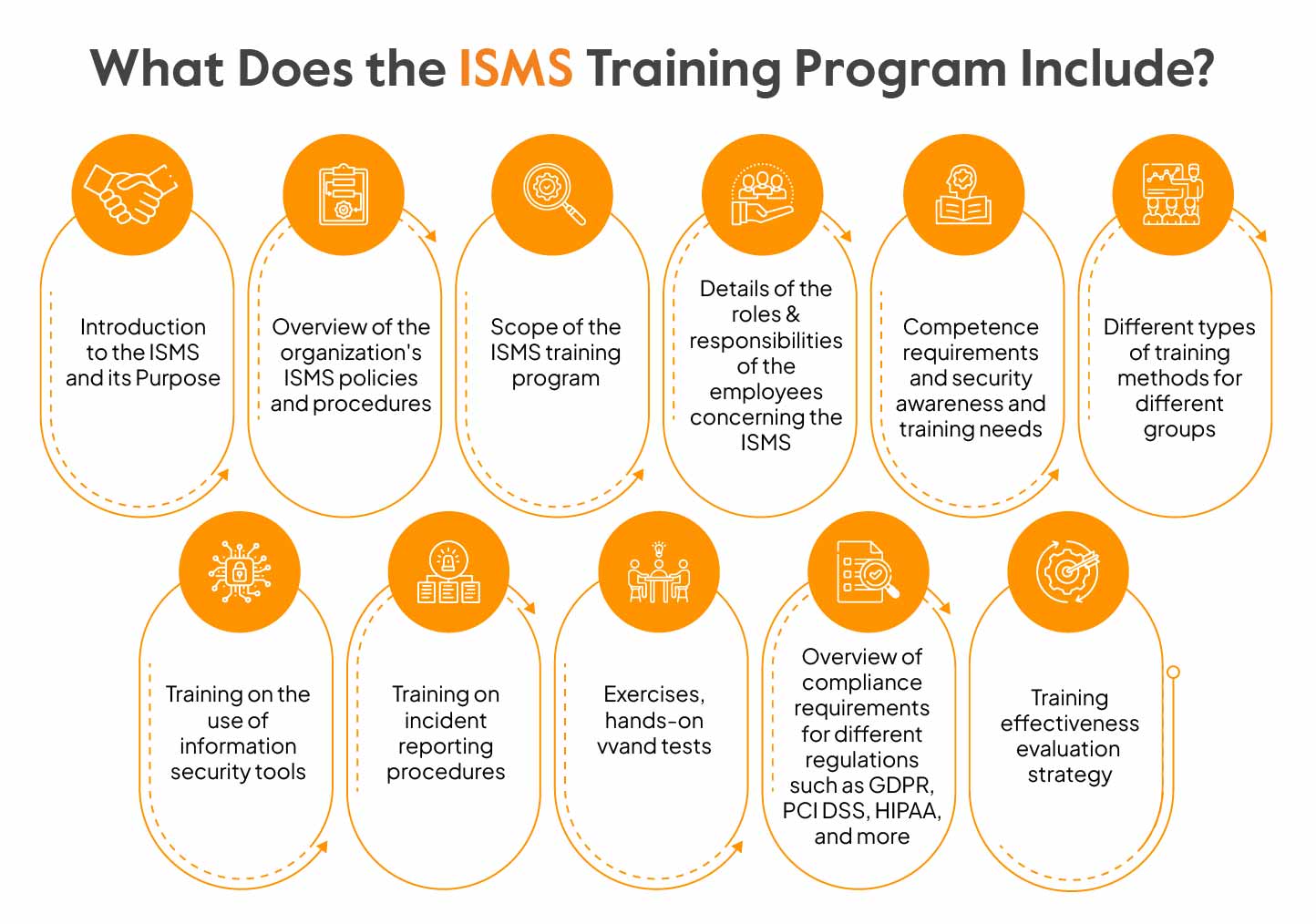
Now that we know all about developing an ISMS awareness program let’s outline the elements that you need to include in your program. The ISMS training program generally includes the following elements:
- Introduction to the ISMS and its Purpose
- Overview of the organization’s ISMS policies and procedures
- Scope of the ISMS training program
- Details of the roles & responsibilities of the employees concerning the ISMS
- Competence requirements and security awareness and training needs
- Different types of training methods for different groups
- Training on the use of information security tools
- Training on incident reporting procedures
- Exercises, hands-on workshops, and tests
- Overview of compliance requirements for different regulations such as GDPR, PCI DSS, HIPAA, and more
- Training effectiveness evaluation strategy
When you create your ISMS awareness training program policy or document, you need to define the above-mentioned elements to streamline your program.
Benefits of ISMS Awareness Training
ISMS awareness training plays a crucial role in strengthening the security defense of any organization.

Here are a few benefits of the ISMS:
Awareness: Human errors are the leading cause of many cyber attacks. Through ISMS awareness training, you can drive cybersecurity awareness and teach employees to recognize and effectively respond to security threats.
Threat Reduction: With an ISMS awareness program, employees learn about the security best practices and technologies used in the organization. This helps them understand common social-engineering attacks like phishing and fraud calls. By conducting simulations, you can teach them how not to fall into such traps.
Avoid Downtime: When you give proper ISMS awareness training, you are less likely to face downtime, as employees will clearly understand their roles and responsibilities in dealing with ISMS incidents. This means that critical business operations will remain functional.
Maintain Compliance: An ISMS awareness training program ensures that all employees are well aware of the compliance policies. With adequate training, they will know how to handle sensitive data, which adds a layer of security to your organization and aids your compliance efforts.
Closing Thoughts
ISMS awareness training is the foundation for building a strong information security culture. It helps the organization power the first line of defense against ever-increasing cyber threats. Now that the importance and the process of ISMS awareness are evident, what’s next?
To strengthen your ISMS and align it with your ISO 27001 or other compliance requirements, compliance automation tools streamline the entire ISMS compliance process, including tracking training completion, managing policy acknowledgements, and surfacing gaps in employee awareness before an auditor identifies them.
Sprinto is a smart compliance automation platform that helps you achieve compliance quickly and effectively. Get in touch with our ISMS and compliance experts to learn more!
FAQs
The 3 ISMS security objectives are Confidentiality (ensuring that data can only be accessed by authorized people), Integrity (ensuring that data is accurate and complete), and Availability (ensuring that data can be accessed whenever required).
Any business that wants to protect its sensitive data from breaches, cyber threats, and unauthorized access needs ISMS. It helps ensure data confidentiality, integrity, and availability and is crucial to any organization’s risk management program.
The effectiveness of ISMS is measured by key performance metrics based on the ISO 27001 requirements. The KPIs are selected based on various factors such as the relevancy of business, integrated processes, critical vulnerabilities, risk management procedures, and more.
Additionally, ISO 27001 compliance software helps organizations measure the performance and effectiveness of the ISMS and its controls, including training completion rates and competency tracking as required under Clause A.7.2.2.
ISMS training should cover security policies, risk awareness, data protection practices, incident reporting, and employee roles and responsibilities. It should also include ISO 27001-aligned topics such as access control, phishing awareness, and compliance requirements.
Author
Gowsika
Gowsika is an avid reader and storyteller who untangles the knotty world of compliance and cybersecurity with a dash of charming wit! While she’s not decoding cryptic compliance jargon, she’s oceanside, melody in ears, pondering life’s big (and small) questions. Your guide through cyber jungles, with a serene soul and a sharp pen!Explore more ISO 27001 articles
ISO 27001 Overview & Requirements
ISO 27001 vs Other Frameworks
ISO 27001 Audit & Certification Process
ISO 27001 Management & Assessment
ISO 27001 Implementation & Automation
ISO 27001 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.










