Identifying documents for ISO 27001 demands meticulous attention to detail. Overlooking critical documents or including unnecessary ones are common scenarios with far-reaching consequences.
Adding a layer of complexity to the process are the various formats—digital files, physical records, screenshots, emails, time stamps, evidence catalogue, etc.
The stakes are high, as gaps in documentation could lead to non-compliance or involve a lot of back and forth with the auditor to get things done.
Especially if an organization has a complex structure, document identification across departments can be challenging. So, we’ve curated the ultimate ISO 27001 mandatory documents checklist for you to be on top of your compliance game.
Read on to ace the ISO 27001 documentation for your next audit.
What are ISO 27001 mandatory documents?
ISO 27001 Mandatory Docs Checklist
With pre-filled policies and templates, Sprinto helps you get ISO 27001 compliant 3X faster.
ISO 27001 mandatory documents are a collection of documents that organizations must create, adapt and maintain to comply with ISO 27001. Some of these documents include ISMS Scope statement, information security policy, risk treatment plan, etc.
Note: As part of the process of implementing ISO 27001 within an organization, conducting a gap analysis is a crucial step. A gap analysis helps identify the current state of your organization’s information security practices compared to the requirements outlined in the ISO 27001 standard.
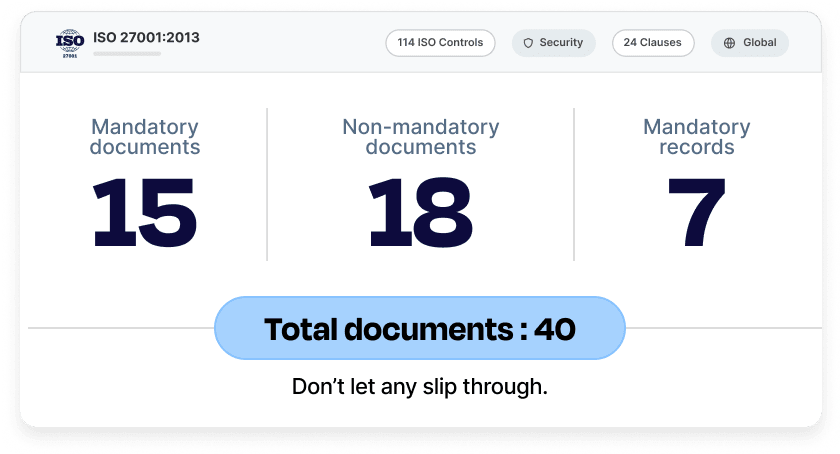
List of ISO 27001 mandatory documents
The decision about implementing ISO 27001 Annex A controls should be based on your risk profile, compliance obligations, and stakeholder’s demands. In such a scenario, the definition of ‘necessary information’ becomes discretionary.
However, the following documents are considered mandatory ISO 27001 documentation and considered during the audit:
| Mandatory documents | ISO 27001 Clause/Annex | Required Records | ISO 27001 Clause/Annex |
| Scope of the ISMS | Clause 4.3 | Records of training, skills, experience, and qualifications | Clause 7.2 |
| Information security policy | Clause 5.2 | Monitoring and measurement results | Clause 9.1 |
| Risk assessment and risk treatment process | Clause 6.1.2 | Internal audit program | Clause 9.2 |
| Statement of Applicability | Clause 6.1.3 | Results of internal audits | Clause 9.2 |
| Risk treatment plan | Clauses 6.1.3, 6.2, 8.3 | Results of the management review | Clause 9.3 |
| Information security objectives | Clause 6.2 | Results of corrective actions | Clause 10.2 |
| Risk assessment and treatment report | Clauses 8.2 and 8.3 | Logs of user activities, exceptions, and security events | Annex A 8.15 |
| Inventory of assets | Annex A 5.9 | ||
| Acceptable use of assets | Annex A 5.10 | ||
| Incident response procedure | Annex A 5.26 | ||
| Statutory, regulatory, and contractual requirements | Annex A 5.31 | ||
| Security operating procedures for IT management | Annex A 5.37 | ||
| Definition of security roles and responsibilities | Annex A 6.2, A 6.6 | ||
| Definition of security configurations | Annex A 8.9 | ||
| Secure system engineering principles | Annex A 8.27 |
Note: This update is as per ISO 27001: 2022 version. This version mandates fewer documents when compared with the ISO 27001: 2013 version. No additional documents are required for the 11 new controls specified in the latest update.
The ISO 27001 mandatory documents are central to achieving the comprehensive set of requirements laid down in the standard. Let’s delve into each of these documents understanding the purpose:

1. Scope of the ISMS
Specifies the boundaries and extent to which ISMS applies and the areas, processes, assets etc. that are included.
2. Information security policy and objectives
Outlines the information security goals of the organization and the security protocols for achieving those protection commitments.
3. Risk assessment and risk treatment methodology
Presents the approach, tools, methods and criteria for identifying and scoring risks as well the plan of action for risk treatment as per the severity.
4. Statement of Applicability
Provides a description of selected and implemented controls along with the justifications for any exclusions.

5. Risk treatment plan
Details the risk treatment options chosen i.e. mitigation, transfer, acceptance and avoidance for each of the identified risks along with timelines, resources etc.
6. Risk assessment report
Includes information about methodology, information assets covered, identified risks, probability of occurrence and findings to give insights about the risk profile.
7. Definition of security roles and responsibilities
Clarifies the roles and responsibilities of various individuals and teams in control implementation, system administration, monitoring etc.
8. Inventory of assets
Consists of a record of hardware, software, networks, databases, human assets and other resources that are crucial for protecting sensitive information.
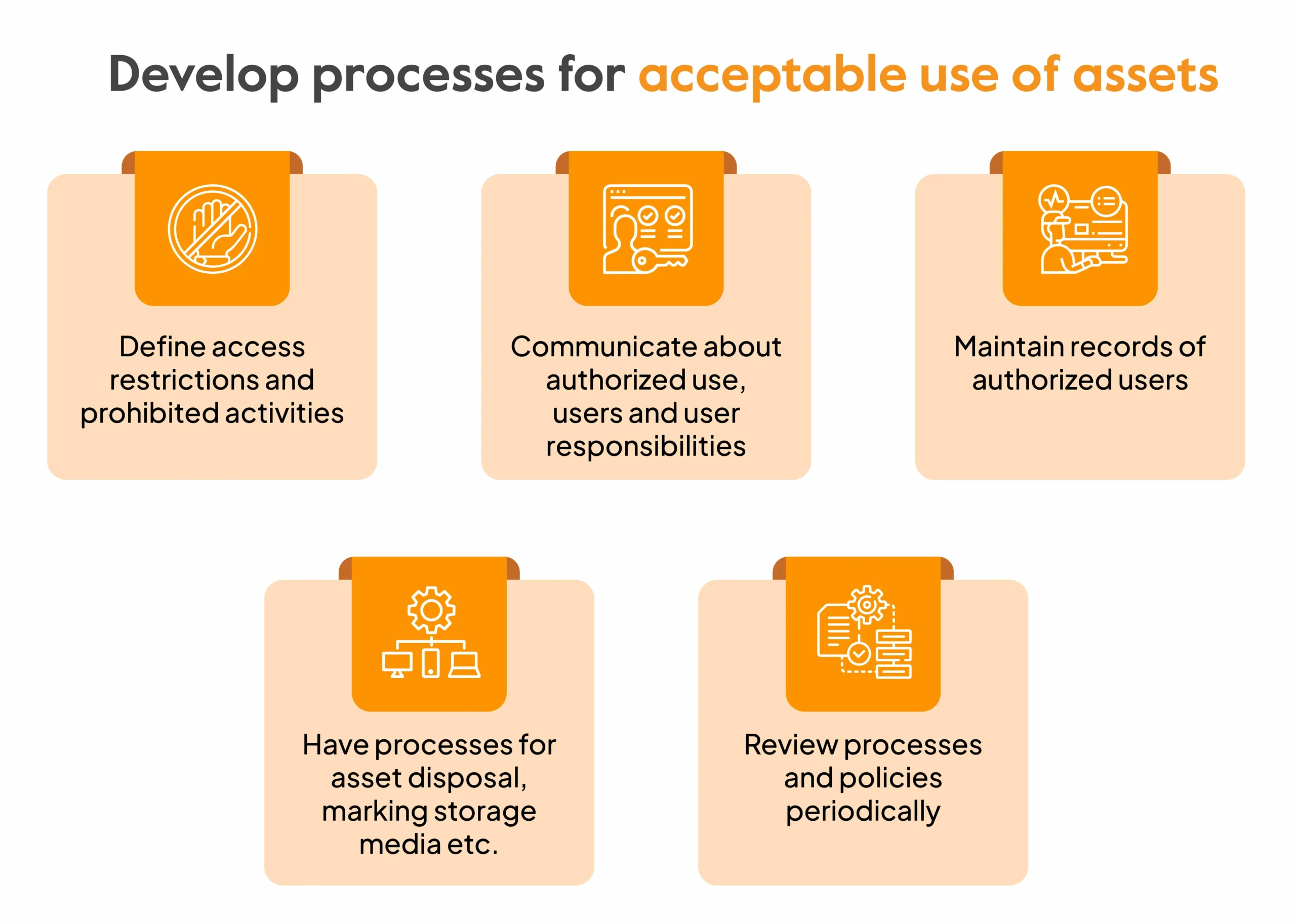
9. Acceptable use of assets
Sets guidelines for fair and responsible use of assets like IT resources, systems, networks, physical assets etc. and defines acceptable behavior.
10. Access control policy
Covers the rules and guidelines related to control of access to information assets for protecting their confidentiality, integrity and availability.
11. Operating procedures for IT management
Serves as a reference document for IT staff to manage operations like incident response, system monitoring, backups, vulnerability detection and communication etc.
12. Secure system engineering principles
Comprises basic principles related to designing, deploying and implementing secure systems and practices for an effective ISMS. This can include guidelines on design frameworks, coding practices, testing mechanisms etc.
13. Incident management procedure
Describes the sequential procedure for incident management from identifying to escalating, containing or treating, documentation and post-incident steps.
14. Business continuity procedures
Addresses the plan of action that must be initiated to restore normal business operations in case of an emergency/crisis/disruption.

audit-ready?
Sprinto can help you get certified in
4 easy steps.
15. Statutory, regulatory, and contractual requirements
Gives details about the applicable laws, regulations, standards and contractual agreements that are adhered to by the organisation
List of Records
The following records are required to be created, updated and maintained:
16. Records of training, skills, experience, and qualifications
Helps assess competency, identify skill gaps or training needs and take future decisions for workforce development.
17. Monitoring and measurement results
Serves as a track record of surveillance activities as well as qualitative and quantitative metrics for identifying improvement areas.
18. Internal audit program
Demonstrates conformance of ISMS with ISO 27001 requirements and the commitment of organisation to maintain compliance.
19. Results of internal audits
Showcases audit findings, documentation reviews, interview summaries with staff, follow-up actions, etc.
20. Results of the management review
Ensures a formal review of ISMS performance by the top management and provides a tangible proof of decisions, recommendations and actions, enhancing progress visibility.
21. Results of corrective actions
Act as an evidence of improvement measures implemented over a course of time for enhancing security processes.
22. Logs of user activities, exceptions, and security events
Become a valuable source of investigation and root cause analysis in case of events.

Non-mandatory documents
The non-mandatory documents are not critical but are demand-driven and good-to-have. These may be required as per specific nature and risk-profile of an organization.
| Non-Mandatory documents | ISO 27001 Clause/Annex |
| Procedure for document control | Clause 7.5, Annex A 5.33 |
| Controls for managing records | Clause 7.5, Annex A 5.33 |
| Procedure for internal audit | Clause 9.2 |
| Procedure for corrective action | Clause 10.2 |
| Bring your own device (BYOD) policy | Annex A 7.8, 8.1 |
| Mobile device and teleworking policy | Annex A 6.7, 7.8, 7.9, 8.1 |
| Information classification policy | Annex A 5.10, 5.12, 5.13 |
| Password policy | Annex A 5.16, 5.17, 8.5 |
| Disposal and destruction policy | Annex A 7.10, 7.14, 8.10 |
| Procedures for working in secure areas | Annex A 7.4, 7.6 |
| Clear desk and clear screen policy | Annex A 7.7 |
| Change management policy | Annex A 8.32 |
| Backup policy | Annex A 8.13 |
| Information transfer policy | Annex A 5.14 |
| Access control policy | Annex A 5.15 |
| Supplier security policy | Annex A.5.19, A.5.21, A.5.22, A.5.23 |
| Disaster recovery plan | Annex A.5.29, A.5.30, A.8.14 |
| Encryption policy | Annex A 8.24 |
Some implementation tips for maintaining documents for ISO 27001
- Establish protocols for managing documents throughout their lifecycle
- Clearly communicate ownership and access controls
- Have a document audit when running internal audits and update as per requirements
- Define document retention and disposal procedures
- Make use of standardized templates for keeping things easy and consistent
- Present information in a clear and understandable manner. Use process flowcharts, organization structure diagrams etc. and other visual aids for promoting clarity.

ISO 27001 audit!
See how Sprinto expedites
audit-preparedness to just weeks.
How many mandatory clauses are there in ISO 27001?
ISO 27001 comprises two sections: clauses and annexure. The first part includes 11 clauses from 0 to 10, with clauses 4 to 10 being mandatory. Each clause serves a specific purpose and provides a framework to ensure that the ISMS is effectively established, implemented, and maintained.
- Clause 4 context of the organization ensures that organizations understand the internal and external environment to define ISMS scope.
- Clause 5 emphasizes on securing leadership commitment for information security
- Clause 6 helps plan for risks and objectives and any changes to ISMS
- Clause 7 aims to ensure support, resources and management for ISMS implementation
- Clause 8 provides guidance on managing operational controls and processes
- Clause 9 helps evaluate performance
- Clause 10 focuses on continuously improving ISMS
The second section lists controls in Annex A. While the 2013 version had 114 controls, the latest version ISO 27001:2022 has 93 controls. Organizations can choose these controls based on the specific risks they wish to address.
Consequences of missing ISO 27001 mandatory documents
In an ISO 27001 certification audit, the auditor records any major non-conformities, minor non-conformities, and opportunities for improvement. Not having ISO 27001 mandatory documents is a major non-conformity.
Usually non-conformities hinder the certification process and will require you to revisit the exact documentation obligations and submit the missing pieces to the auditor, before the certification can be granted. This can extend your timelines by 1-4 weeks depending on the time you take to gather/recreate the evidence and catalogue it before submitting it to the auditor for review.
Additionally, missing ISO 27001 documentation can lead to ineffective risk management. Although ISO 27001 does not directly impose fines and penalties, non-compliance with ISO 27001 can impact compliance with related frameworks such as GDPR. GDPR requires strict protection of personal information and ineffective risk management due to ISO 27001 non-conformity can lead to data breaches. The fines and penalties for a GDPR breach can go up to €20 million or 4% of annual turnover whichever is higher.
Download your ISO 27001
Gap Analysis Template Now!

Get ISO 27001 ready with Sprinto
Use the lists above to ensure all required documents are organized and easily accessible for your auditor. While auditors may review only a subset of them, having everything indexed and ready makes the audit process far smoother.
But documentation is only one part of the ISO 27001 journey. Implementing and maintaining the required controls across systems, teams, and vendors can quickly become complex, especially when done manually.
Traditionally, compliance programs rely on multiple stakeholders across the organization to collect evidence, monitor controls, and keep processes aligned with the framework. This often pulls leadership and functional teams into repetitive compliance tasks instead of focusing on building and scaling the business.
That’s where Sprinto comes in.

Sprinto is an AI-powered autonomous trust platform that connects with your cloud infrastructure, identity systems, and security tools to run compliance continuously in the background. It tracks live configurations, verifies controls, and automatically collects audit-ready evidence so your ISO 27001 program always reflects the real state of your environment.
Read why Axslogic loved 30% faster evidence collection and single view compliance management provided by Sprinto. Talk to our experts today and get ISO 27001 compliant 10x faster.
FAQS
The Statement of Applicability is a mandatory document in ISO 27001. It lays down the controls that are applicable to the organization from Annex A and provides justification for inclusion or exclusion of controls. It helps demonstrate to the auditor that the organization has addressed the information security risks as per the ISO 27001 standard.
The ISMS manual is not explicitly required as a mandatory document for ISO 27001. However, many organizations choose to have an ISMS manual as a reference document to guide the creation and implementation of an effective ISMS.
The ISO 27001:2022 lists 93 controls. However, it is not mandatory to implement all controls. The organizations must conduct a risk assessment to identify the specific information security risks and determine the controls to mitigate these risks.
ISO 27001 requires information security policy, access control policy, information classification and handling policy, remote working policy, business continuity policy, supplier security policy, network security policy and physical and environmental security policy.
The ISO 27001 risk assessment report essentially contains information about methodology and approach used for risk assessment, the information assets that were evaluated, the identified risks, risk analysis with likelihood and impact and the risk treatment options along with selected controls.
Author
Payal Wadhwa
Payal is your friendly neighborhood compliance whiz who is also ISC2 certified! She turns perplexing compliance lingo into actionable advice about keeping your digital business safe and savvy. When she isn’t saving virtual worlds, she’s penning down poetic musings or lighting up local open mics. Cyber savvy by day, poet by night!Explore more ISO 27001 articles
ISO 27001 Overview & Requirements
ISO 27001 vs Other Frameworks
ISO 27001 Audit & Certification Process
ISO 27001 Management & Assessment
ISO 27001 Implementation & Automation
ISO 27001 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.