TL;DR
| Small businesses can complete a SOC 2 Type 1 in ~2–3 months; Type 2 typically takes 6–12 months due to the observation period |
| Type 1 validates control design; Type 2 verifies controls operate effectively over time |
| Total cost usually ranges from $20K–$70K depending on scope, auditor, and tooling |
| The process includes scoping, implementing controls, readiness assessment, and a formal audit; automation significantly reduces time and overhead |
For small businesses selling to enterprise customers, security questions are almost inevitable during sales conversations. Prospects and partners will want to know how you protect their data, who has access to it, and what controls you have in place. A SOC 2 audit report provides independent, auditor-verified assurance of your security controls, giving enterprise buyers a credible and standardized reference point, though it does not replace all due diligence activities such as security questionnaires or customer-specific reviews.
Investing in SOC 2 readiness helps small businesses identify and address control gaps, demonstrate security maturity, and build the kind of trust that accelerates enterprise deals, making it a strategic business decision as much as a compliance one.
In this blog, I’ll break down why SOC 2 matters for small businesses, what the process looks like, how long it takes, and what it costs.
SOC 2 audit for small business: An overview
A SOC 2 audit is an independent evaluation of an organization’s internal controls to ensure the protection of customer data or any sensitive information. The AICPA’s five trust service categories (security, availability, confidentiality, processing integrity and privacy) serve as the foundation for conducting SOC 2 audits.
Any medium or enterprise client entrusting its data with a small business would still want a validation of a robust cybersecurity system in place. Therefore, SOC 2, while typically associated with larger organizations, is highly recommended even for small businesses.
The SOC 2 audit for small business is mostly like that of larger organizations. However the differences are in scope, resources, security maturity and third-party relationships that must be considered.
The audit process for small businesses includes in-depth planning, meticulous implementation, formal audit and reporting. The business can seek SOC 2 Type 1 or Type 2 reports depending upon the requirements and duration.
Get Our Practical SOC 2 Guide;
Yours at No Cost

Why does SOC 2 matter for small businesses? (And not just enterprises)
A SOC 2 report provides an audited assurance of a formal information security policy and tight security controls implemented by businesses to protect customer data from distortion or unauthorized access.
SOC 2 audit is essential for small businesses that handle sensitive data and need to meet regulatory requirements. These can include cloud service providers, SaaS providers, payment processors, electronic health record providers etc. Additionally, it helps build market credibility and tighten internal security controls.
Here’s why a small business must undergo a SOC 2 audit:
Elevates customer & partner satisfaction
To ensure repeat business, higher sales, reduced costs and build brand reputation, it’s crucial to maintain the trust of existing clients and partners. Getting a SOC 2 audit demonstrates the effectiveness of controls implemented by an organization and helps retain already established customers for long-term success.
Unlocks enterprise acquisition opportunities
Pitching to an enterprise client means getting showered by questions like: “How do you ensure data security?” “Are you SOC 2 compliant?”. Nevertheless, these questions are justified because every business wants its sensitive information to be protected.
Getting a SOC audit helps gear up for enterprise readiness and unlocks new opportunities.
Helps address internal control weaknesses
A SOC 2 audit process is comprehensive and requires rigorous identification and addressing of gaps in internal controls. This helps in tightening the security stance of the organization and reduce risk of cyber incidents and data breaches.
Reduces vendor questionnaire burden
A number of small businesses have to undergo a time-consuming and resource-intensive exercise of filling lengthy security questionnaires from vendors. A SOC 2 report significantly reduces the burden of vendor questionnaires by providing a standardized, auditor-verified reference for your security controls. While it may not replace all due diligence activities, enterprise customers often still conduct their own reviews; it substantially streamlines the vendor onboarding process and accelerates security conversations.
Sprinto helps you move faster.
👉 See how →
SOC 2 Trust Services Criteria: Do you need them all?
SOC 2 is built around five Trust Services Criteria (TSC). You don’t need to include all five in your audit. Just focus on the areas that matter to your business.
The five Trust Services Criteria are:
- Security (required): This is the foundation of every SOC 2 audit. It covers how you protect your systems against unauthorized access. This includes firewalls, encryption, access controls and incident response.
- Availability: This one is concerned with uptime. You’ll want to include this if your customers depend on your service being accessible around the clock
- Processing Integrity: Your system should process data accurately and completely. This criterion matters if you handle transactions or calculations that customers rely on.
- Confidentiality: This covers how you protect sensitive business information like contracts, intellectual property or financial data.
- Privacy: This focuses specifically on personal information and how you collect, use, store and dispose of it.
For most small businesses, security alone is enough to start. It complies with the baseline requirements and addresses what enterprise buyers care about most. As your business grows or your product handles more sensitive data, you can add criteria like Availability or Confidentiality.
SOC 2 Type 1 vs Type 2: Which one’s relevant for small businesses?
One of the first decisions you’ll face is choosing between SOC 2 Type 1 and SOC 2 Type 2. Both show your commitment to security, but they serve different purposes.
Here’s how they compare:
| SOC 2 Type 1 | SOC 2 Type 2 | |
| What it evaluates | Design of controls at a single point in time | Design and operating effectiveness of controls over time |
| Observation period | None (snapshot audit) | 3 to 12 months |
| Time to complete | 2 to 4 weeks | 3 to 12 months |
| Cost | Lower | Higher |
| Buyer confidence | Moderate | High |
| Best for | First-time certification | Ongoing assurance |
When Type 1 makes sense
If you’re a small business pursuing SOC 2 for the first time, Type 1 is often the smarter starting point. It validates that you’ve designed the right controls without needing months of evidence collection. This gets you certified faster, so you can start closing deals that require compliance proof.
Type 1 also works well when you’re racing against a sales deadline or need something to show prospects while you work toward Type 2.
When buyers expect Type 2
Enterprise buyers and heavily regulated industries typically want SOC 2 Type 2. It proves your controls aren’t just designed well but actually work over an extended period.
If you’re selling to banks, healthcare organizations, or large tech companies, expect Type 2 to come up in procurement conversations.
The typical upgrade path for small businesses
Most small businesses follow a straightforward progression:
- Get Type 1 first: Establish your baseline and demonstrate commitment to security
- Start your observation period immediately: Once Type 1 is complete, begin collecting evidence for Type 2
- Complete Type 2 within 12 months: This shows buyers you’ve matured beyond a point-in-time snapshot
This approach lets you take advantage of sales opportunities quickly with Type 1 while building toward the stronger assurance that Type 2 provides. You don’t have to wait a full year to show prospects you take security seriously.
Steps to prepare for SOC 2 audit for small business
An audited assurance for a rock-solid compliance posture is not an easy feat. It’s an arduous process that requires sifting through numerous documents, some painstaking implementation, and an ever-vigilant eye for ensuring things are moving right.
Here are the detailed steps for preparing for a SOC 2 audit for small business:
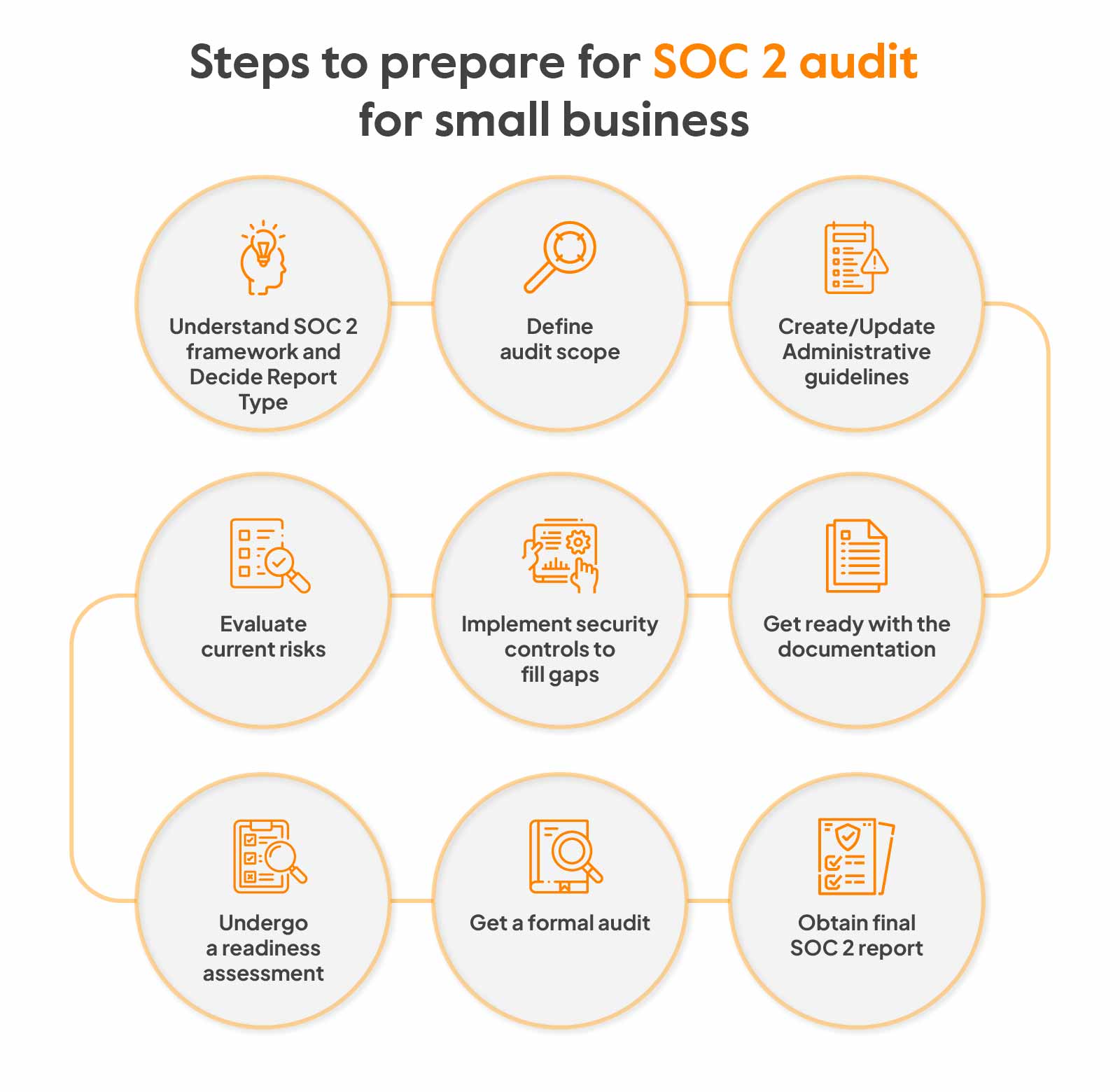
Step 1: Define audit scope
The audit scope sets the audit limits. It establishes clarity on the systems, processes and controls that need to be audited. This decision can be based on a number of factors like overall business objectives, regulations that apply, processes, reliance on third-party vendors, information assets etc.
Step 2: Create/Update Administrative guidelines
Administrative policies and standard operating procedures (SOPs) as per business size, structure, workflows and operations must be created or updated. These policies must establish clear guidelines on people, processes and technology within the scope of audit. This can include policies related to user access, risk assessments, security roles and responsibilities, training timelines, etc.
Step 3: Evaluate current risks
It is pretty normal for small businesses to not have a dedicated security staff and people with other primary job functions carrying out such tasks. So there are edge cases & risks to handle and implementation gaps to fill. Running a risk assessment to evaluate current risks and compliance level helps understand the risk profile and prioritize them accordingly under the remediation plan.
How to run a risk assessment?
- Identify the critical components: Data, IT infrastructure, people, procedures
- Include risk factors that exist: For example, data retention and disposal processes, third-party risks, network and system vulnerabilities etc.
- Categorize them into internal and external threats and score them based on criticality using a risk scoring methodology that reflects your business context and risk appetite
- Note down the current processes in place for mitigating the identified risks
Additional tips:
- Also perform fraud risk assessment as it is often considered as part of evaluation during the audit. This includes financial fraud, misconduct by employees, bribery acts etc.
- Include vendor risks as part of assessments and request their SOC 1 and SOC 2 reports issued by their CPA firms
Step 4: Implement security controls to fill gaps
The next step is to implement administrative, technical and physical security controls on the basis of identified risks and gaps. These can include:
- Access controls
- Network security controls
- Encryption
- Incident response
- Surveillance systems
- Application security controls etc
There can also be system reconfigurations in accordance with industry best practices. For example, reconfiguring firewalls or backup systems.
Step 5: Get ready with the documentation
Documentation is the tangible evidence for the implemented controls and forms an important part of the SOC 2 audit. SOC 2 preparation is a cross-functional effort. While an experienced engineering or security team member can coordinate technical documentation and evidence collection, successful audit preparation typically requires active involvement from HR for workforce-related controls, legal for policy and contract review, leadership for governance and risk oversight, and operations for process documentation. Assigning clear ownership across these functions early prevents bottlenecks during the audit.
Here’s the list of documentation that will be required:
- Management assertion: This compromises of operational objectives, internal control processes, system requirements and physical security arrangements
- Technical security documents: Log management policy, password requirement policy, data retention and destruction policy, backup logs etc.
- Operational documents: Physical office diagram, risk management plan, vendor agreements etc.
- Human resource documents: Organizational chart, security awareness training logs, onboarding policies, evaluation of employees etc.
- Privacy and compliance documents: Notice of Privacy practices, confidentiality policy etc.
- Third party and vendor contracts and other complementary user entity controls (SOC 2 controls performed by your service provider)
Note: You will also require administrative policies and cloud infrastructure certifications as part of evidence production, along with these documents.
Step 6: Undergo a readiness assessment
A readiness assessment helps understand the organization’s preparedness for an actual audit through a preliminary view. More often than not, small businesses do not have an internal audit team so this is performed by a service auditor. The existing controls are mapped to the Trust Service Criteria to spot any misfires and corrective actions are recommended so that final audit takes lesser time, energy and resources.
Step 7: Conduct a formal audit
Next step is to find an auditor (tips on that in the later section) and get a walkthrough of the process.
The audit process can require you to start with a security questionnaire followed by gathering evidence and documentation of controls. The auditor then understands the security practices and business processes through observation, inspection and consulting responsible employees for each process.
There can be a lot of moving back and forth for evidence collection and corrective actions (not with Sprinto though) and it can be a rigorous exercise.
Sprinto has automated evidence collection and auditors are added to the dashboard to see a single-shot view of compliance evidence.
Step 8: Obtain final SOC 2 report
The final SOC 2 report summarizes the auditor’s findings and includes an opinion on how well your controls are designed and, in the case of a Type 2 report, how consistently they operated over the audit period. SOC 2 audits don’t result in a simple pass or fail, but not all opinions carry equal weight:
- Unqualified opinion: Your controls are suitably designed and operating effectively. This is the outcome you’re aiming for and what enterprise customers expect
- Qualified opinion: A specific area of concern exists, but it is not a critical deficiency; most customers will still accept this, though it warrants prompt remediation
- Adverse opinion: Material gaps exist that significantly impact the reliability of your controls. This can seriously undermine customer confidence and may affect your ability to close deals
- Disclaimer of opinion: The auditor could not gather sufficient evidence to form an opinion. This effectively means the audit did not achieve its intended purpose
While you technically can’t “fail” a SOC 2 audit, receiving anything other than an unqualified opinion can have real business consequences. If your opinion falls short of unqualified, treat it as a prioritized remediation exercise, address the identified gaps, strengthen your controls, and re-engage your auditor.
Also check out: A Guide to SOC 2 for startups
What’s different for small businesses vs enterprises in terms of implementing SOC 2?
SOC 2 compliance looks very different depending on the size of your organization. What works for a 500-person company with a dedicated security team won’t make sense for a 20-person startup. Here’s how the experience typically differs
1. Scope and complexity
Enterprises deal with larger infrastructure, multiple business units and complex data flows. Their SOC 2 audits often include dozens of systems and hundreds of controls.
Small businesses usually have leaner tech stacks and simpler operations. This means fewer controls to implement and less documentation to manage.
2. Resources and bandwidth
Large companies have compliance teams whose entire job is managing audits. Small businesses rarely have that luxury.
You’re likely managing SOC 2 alongside product development, customer support and a dozen other priorities. That’s why automation tools matter so much at this stage.
3. Budget constraints
Enterprises can absorb six-figure compliance costs without much thought. For small businesses, every dollar counts. The good news is your simpler scope means lower audit fees and faster timelines.
4. Flexibility in approach
Here’s where small businesses actually have an advantage. You can move faster, make decisions quickly and implement controls without layers of approval. Enterprises often get slowed down by internal bureaucracy.
SOC 2 audit timeline for small businesses
For small businesses, the answer depends on your current security posture and which report type you’re pursuing.
| Phase | What happens | Duration |
| Readiness assessment | Identify gaps and understand requirements | 1 to 2 weeks |
| Control implementation | Build policies, configure systems and train employees | 4 to 8 weeks |
| Type 1 audit | Auditor evaluates control design | 2 to 4 weeks |
| Observation period (Type 2 only) | Collect evidence of controls operating effectively | 3 to 12 months |
| Type 2 audit | Auditor reviews evidence and tests controls | 4 to 6 weeks |
For Type 1: Most small businesses can go from zero to certified in 2 to 3 months if they stay focused and use the right tools.
For Type 2: Expect 6 to 12 months total. The observation period is what takes the longest since you need to demonstrate that controls work consistently over time.
There are a few factors that affect your timeline
- If you already have basic security practices in place, you’ll move faster.
- SOC 2 stalls when key people are too busy to participate.
- If you’re using a good compliance automation platform that can reduce your audit prep time. (Sprinto can get you audit-ready in days with minimal bandwidth.)
- If you’ve booked an auditor early. Their availability can add weeks to your timeline if you wait (Sprinto can handle that too.)
Pro tip: Don’t aim for perfection before starting. Get the fundamentals right and refine as you go. Waiting until everything is “ready” often means never starting at all.
What cost margins can small businesses expect for a SOC 2 audit?
Let’s talk numbers. SOC 2 audit costs can vary widely based on your scope, approach and the tools you use.
Here’s what small businesses typically spend:
| Cost component | DIY/Manual approach | With automation platform |
| Readiness assessment | $5,000 to $15,000 | Often included |
| Gap remediation | $10,000 to $30,000 | $5,000 to $15,000 |
| Compliance platform | $0 | $10,000 to $25,000/year |
| Auditor fees (Type 1) | $10,000 to $25,000 | $7,500 to $20,000 |
| Auditor fees (Type 2) | $20,000 to $50,000 | $15,000 to $35,000 |
| Total (Type 1) | $25,000 to $70,000 | $20,000 to $50,000 |
| Total (Type 2) | $35,000 to $95,000 | $30,000 to $70,000 |
Where does the money go?
- Auditor fees make up a big chunk. These vary based on scope and the auditor’s reputation.
- Tools and software for evidence collection, monitoring and policy management.
- Internal time spent by your team. This hidden cost often gets overlooked.
- Remediation work to fix gaps identified during readiness assessments.
How to choose the right auditor for a small business?
Higher costs, compromised engineering bandwidth and disrupted operations are the biggest nightmares of a small business. That is why it is so crucial for them to find the right auditor and navigate through the compliance process with ease.
Here’s how you can go about selecting the right auditor as a small business:

1. Check experience and credentials
The auditor must be a Certified Public Accountant firm and should have experience in SOC 2 audit for small business. To find a good personal fit, also enquire about experience in SOC 2 audit for a firm with a similar security maturity level and look for reviews.
2. Clarify the scope of services
It is always advisable to get clarity on the scope of services that will be included in the SLA (service level agreement) before selection. Questions like what types of controls will be evaluated, will there be recommendations for improvements etc. must be addressed. As a small business these little things matter for strengthening internal controls.
3. Learn about the methodology
Make sure to enquire about the approach used by the auditor for conducting the SOC 2 audit. This includes methods used for risk assessments, evaluating controls, reporting and ensuring the quality of audit. Additionally, ask if the auditor uses automation tools for performing the audit.
4. Enquire about costs
Get accurate cost estimates before final selection because there’s less financial flexibility and tighter budgets for small businesses. Seek details about total costs, breakdown of cost components and any hidden/additional costs to strike the right balance between value and costs.
Additional questions that must be asked:
- What all will not be included in the SLA and how much will it cost additionally to get that service?
- How are contingencies or unexpected events handled during the audit?
- What will be the timeframe for the audit?
- Will there be any ongoing support services or annual follow ups?
- How many people will be needed from the organization for helping with the audit process?
How to prepare faster (and more cost-efficient) as a small business?
Finding the right auditor is a small part of the SOC 2 process. How you prepare for the audit will decide how smoothly and affordably the process goes.
Small businesses that walk into audits unprepared end up paying more in auditor fees; they waste engineering hours on back-and-forth requests and extending timelines unnecessarily.
The smartest way to cut costs is to come audit-ready. You need to document your controls, organize evidence and find gaps before the auditors begin their review.
Platforms like Sprinto make this really easy. The platform automates evidence collection, flags missing controls and gives you a real-time view of your compliance status.
You can prepare for a SOC 2 audit and understand the step-by-step process andSOC 2 audit requirements to know exactly what auditors will look for. When you show up prepared, audits go by faster, cost less and cause minimal disruption to your team.
Become SOC 2 compliant with Sprinto
The SOC 2 audit process relies a lot on documentation, evidence gathering testing and implementing controls. It can take hundreds of hours and still leave room for error when you do it manually.
That’s where you need a smarter approach, like one enabled by Sprinto.
Sprinto is an autonomous trust platform focusing on AI-native GRC workflows. It’s built to take you from zero to audit-ready in days. It connects to 300+ systems across your tech stack and uses intelligent automation to handle the heavy work so your team can focus on what matters.
Here’s the features you get when you rely on a platform like Sprinto:
- AI Playground: Build custom compliance agents without writing any code. Create purpose-built AI agents that work with your specific data and context.
- Ask AI: Get an always-on intelligent compliance assistant. Anyone on your team can ask questions like ‘do we encrypt PII at rest?’ and get instant, verified answers pulled directly from your policies and controls.
- AI-powered security questionnaires: Parse incoming requests, match questions to your documentation and draft accurate responses automatically.
- Infinite framework mapping: Use AI to auto-map controls across SOC 2, ISO 27001, HIPAA and other standards.
- Continuous monitoring: Flag compliance drift, find evidence gaps and detect issues before they become audit findings.
All of Sprinto’s AI capabilities are built with a human-in-the-loop architecture. The platform complies with ISO 42001 standards for ethical AI and never uses your data for model training.
Talk to our experts to see why 3,000+ companies trust Sprinto for predictable, stress-free audits.
FAQs
Yes, and often more so. If you’re selling to mid-market or enterprise customers, many buyers won’t even consider vendors without some form of security certification.
Smaller teams actually have an advantage here. You have fewer systems to audit, simpler data flows and less bureaucracy slowing you down. With the right automation tools, startups under 50 employees can get certified in a matter of weeks rather than months.
Absolutely. In fact, Type 1 is where most small businesses should start.
Type 1 checks whether you’ve designed the right controls at a specific point in time. It doesn’t require months of evidence collection like Type 2 does. This means you can get certified faster and start using it in sales conversations right away.
Once you have Type 1 in hand, you can begin your observation period for Type 2.
It depends on your target market. SOC 2 is generally more flexible. You choose which Trust Services Criteria to include and the scope can be personalized to your specific systems. There’s no formal certification body involved. Instead, a CPA firm issues your report based on their audit.
ISO 27001, on the other hand, asks you to build a complete Information Security Management System (ISMS) and go through a formal certification process with an accredited body. It’s more prescriptive and typically involves more documentation upfront
Yes, any small business that aims at unlocking big opportunities and win enterprise clients needs SOC 2 because it will be questioned about security at every step. Moreover, it gives compliance confidence and makes business scalability easy and secure.
Although it depends on the needs of the business, SOC 2 Type 1 is a good starting point for a small business new to the audit process. It can help identify areas of concern that can be addressed to prepare for SOC 2 Type 2. It is however worth noting that for greater assurance to customers and stakeholders, the business will ultimately require a Type 2 report.
In case of small business, a member from senior management or the owner can be the execute sponsor. Then an HR, an experienced engineering team member or somebody from IT staff and a legal team member will be required to support the audit.
The time your SOC 2 audit takes depends on the report type, your level of preparedness, and the scope of your audit.
A Type 1 audit typically takes 5 weeks to 3 months, but here’s the thing: getting ready for the audit almost always takes longer than the audit itself. Gap remediation, documentation, and control implementation need to happen before the auditor even walks in. A Type 2 audit adds an observation period on top of that, bringing the total timeline to 3 to 6 months or more.
The less mature your controls, the longer the prep. Don’t rush into an audit before you’re ready. It’s one of the most common and costly mistakes small businesses make.
Payal Wadhwa
Payal is your friendly neighborhood compliance whiz who is also ISC2 certified! She turns perplexing compliance lingo into actionable advice about keeping your digital business safe and savvy. When she isn’t saving virtual worlds, she’s penning down poetic musings or lighting up local open mics. Cyber savvy by day, poet by night!
Explore more SOC 2 articles
SOC 2 Compliance Overview
SOC 2 Preparation and Documentation
SOC 2 Audit and
Reporting
SOC 2 Differences and Similarities
SOC 2 Updates & Management
SOC 2 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.