TL;DR
| A strong compliance program turns fragmented compliance efforts into predictable, scalable systems your compliance team can actually manage. |
| For SaaS companies selling to financial institutions, meeting strict compliance requirements is the cost of entry—not a nice-to-have. |
| Effective operational risk management helps prevent the silent failures that audits miss but incidents expose. |
As your SaaS company grows—with more customers, more data, and more moving parts—the weight of expectation grows too. A missed log, a delayed patch, or an unclear process can break the trust you’ve spent years building. That’s where operational compliance comes in. Operational compliance is the practice of aligning your company’s everyday operations with all relevant regulations, standards, and internal policies.
In practice, it involves integrating compliance within business processes, so functions like handling customer data, deploying code, and managing internal workflows in a controlled, compliant manner.
What is operational compliance?
Operational compliance is the framework that ensures your day-to-day operations continually meet all relevant legal, security, and industry standards. In other words, it means ensuring that every process, from data security measures to employee workflows, adheres to legal requirements and industry frameworks without compromising business goals.
In practice, it keeps systems aligned, surfaces non-compliance early, and enables teams to act fast—so operations remain smooth, secure, and audit-ready.
For a mid-market SaaS firm, operational compliance involves building compliance into the DNA of the organization so that meeting standards (like SOC 2, ISO 27001, GDPR, etc.) becomes a natural part of daily work rather than a one-time box-ticking exercise.
Why is compliance operations important?
Compliance operations are crucial because they safeguard your business and enable growth. First, a strong compliance program protects your company from legal penalties, security breaches, and operational disruptions by ensuring you follow laws and best practices. Second, it builds trust and credibility – demonstrating to customers, investors, and partners that you handle data securely and operate ethically.
Components of compliance operations
To manage operational compliance, several core components must work together. Key elements include:
- Risk assessment and management: At its core, compliance is a risk discipline. That means looking at your operations—tools, vendors, workflows, people—and asking: Where could this break? Where are we exposed? Where are we relying too much on good intentions instead of process? Done well, risk assessments are uncomfortable. They surface contradictions: the security measure that slows deployment, the financial process that no one follows, the tool everyone bypasses.
- Policies and controls: Policies should reflect how your company actually works—not how a lawyer or auditor wants it to work. The best compliance programs translate complex requirements into everyday behaviors: how engineers manage credentials, how customer data is accessed, how approvals flow. Controls are where this comes to life. They’re not just documents—they’re constraints and rituals that reduce ambiguity.
- Monitoring & auditing: Compliance isn’t set-and-forget. Things break. People leave. Tools change. That’s why constant monitoring matters—not to catch people out, but to catch drift before it becomes failure. Audits give structure to that feedback loop. Whether internal or external, they pressure-test the system: Are controls being followed? Are they still relevant? Are the right people accountable? The goal isn’t perfection. It’s responsiveness.
- Governance & accountability: Compliance doesn’t belong to one team. But it does need ownership. Strong governance means roles are clear, responsibilities are defined, and escalation paths exist. A Security Officer without authority is a liability, not a safeguard. More importantly, compliance has to be culturally reinforced. That means leadership talks about it without deferring it. Teams understand that non-compliance isn’t just a risk—it’s a blocker to growth, reputation, and customer trust
Together, these components create a robust operational compliance framework: you assess and mitigate risks, implement policies and controls, educate your people, monitor continuously, and enforce accountability.
Get operationally compliant faster with automation
A step-by-step process of implementing operational compliance
Compliance can’t be an afterthought—it needs to be operational by design. But for many mid-market SaaS teams, knowing where to start is often the most challenging part. The gap between “we need to be compliant” and embedding it into daily workflows can feel broad and unclear.
Here are the 6 steps:
Step 1: Identify applicable requirements
Start by figuring out which regulations and frameworks actually apply to your business—not in theory, but based on how you operate, who you serve, and what kind of data you handle. If you’re collecting personal data from users in the EU, GDPR isn’t optional—it’s table stakes. If you process payments directly, PCI DSS kicks in.
And if you’re selling into large enterprises or regulated industries, chances are they’ll ask for a SOC 2 report or ISO 27001 certification before they even get to the second sales call.
The mistake a lot of SaaS teams make is assuming “compliance” means chasing every certification under the sun. In reality, your compliance scope should be driven by your customer promises, your product features, and your market footprint.
Step 2: Perform a gap analysis
Once you know what frameworks apply, the next step is brutally simple: figure out where you’re falling short. This isn’t a theoretical exercise—it’s a deep dive into how your business actually runs. You’re not just asking, “Do we have a policy for this?” You’re asking, “Does this policy work, and is it being followed?”
Start with a basic inventory: What controls do you already have in place? How is data stored and accessed? Who approves vendor tools? How are engineers onboarded—and just as importantly, offboarded? You’ll probably find a few things that look great on paper but fall apart in practice.
Maybe MFA is technically required but not enforced. Maybe there’s a DLP policy floating around in Notion, but no one remembers the last time it was reviewed. Or maybe a critical process—like incident response—relies entirely on tribal knowledge and Slack messages.
This is your gap analysis. You’re comparing what’s required to what’s real.
Step 3: Develop policies and controls
Policies aren’t just paperwork. They’re how you translate expectations into behavior. When you find a gap—say, engineers are still using personal devices for production access—it’s not enough to say “don’t do that.” You need a policy that defines what’s acceptable, and controls that make it real.
This is where you operationalize intent. If your gap analysis showed loose access management, you don’t just write a policy saying “we enforce least privilege.” You build the system that enforces it—automated provisioning and deprovisioning, routine access reviews, and alerts for privilege escalations. If customer data isn’t being encrypted properly, the fix isn’t “add a line to the policy doc”—it’s setting up a control in your infrastructure that ensures encryption at rest is enabled by default.
Step 4: Assign and train staff
Policies without owners are just suggestions. And in compliance, suggestions don’t scale. Once you’ve written your policies and defined your controls, the next critical step is assigning clear, accountable ownership. This isn’t just naming a point of contact—it’s operationalizing who’s responsible for making sure things actually happen.
Conduct access reviews. Who’s responsible for verifying that former employees don’t still have active accounts? Is it the IT lead, the security team, or someone in HR? If you’re relying on shared assumptions, you’re already exposed.
The same goes for things like incident response. Who coordinates if production data is leaked? Who talks to legal? Who documents the timeline for audit purposes? If those roles aren’t explicitly assigned and cross-functional responsibilities aren’t clarified, the whole system breaks down when stress hits.
Step 5: Continuously monitor
Once the policies are live and responsibilities are assigned, you need systems that keep everything in check—continuously. Compliance isn’t a one-time setup. It’s a moving target. Things break. People forget. New tools get added without security reviews.
Start by automating what’s easy to miss manually: alert if a server spins up without encryption, if admin access is granted outside of policy, or if a new hire skips mandatory security training. These aren’t edge cases—they’re the kind of routine slip-ups that become audit findings (or worse, breach postmortems).
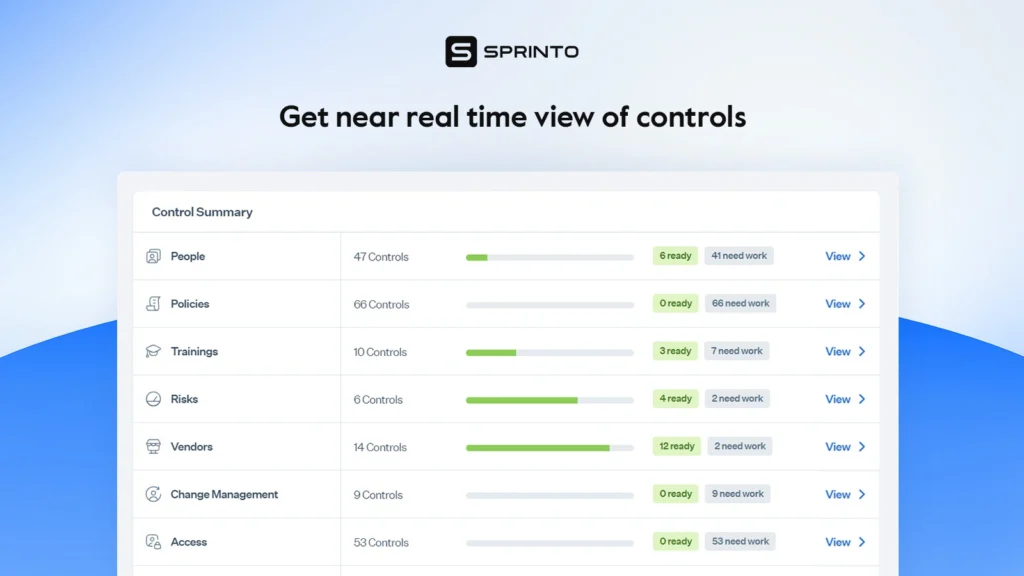
Dashboards also play a key role. You want to see, at a glance, how compliant you are today—not how you were three weeks ago. Real-time visibility keeps compliance from being something you only think about during audit season. It becomes a constant signal—a system that quietly reinforces everything you’ve built.
If continuous monitoring is your thing, as it should be, Sprinto is built for exactly this. It plugs into your existing stack—AWS, GitHub, Okta, GSuite, you name it—and gives you a live dashboard of your compliance posture. It flags issues in real time, auto-collects audit evidence in the background, and makes it dead simple to stay on top of dozens of controls without manual tracking.
Step 6: Test and iterate
Don’t wait for the annual audit to tell you what’s broken. By then, it’s too late—it’s reactive, expensive, and stressful. Schedule internal reviews quarterly. Not just to tick boxes, but to pressure-test what you’ve built. Are access reviews actually happening? Are controls still relevant as your team scales or your infrastructure evolves?
Go one step further: simulate failure. Run an incident response drill. Pick a weekday, surprise your team with a mock breach, and see what happens. Who responds? Who fumbles? What gets documented? It’s not about catching people out—it’s about uncovering weak points before they cost you.
Each step builds on the previous one, creating a loop of improvement. Over time, this process will integrate compliance deeply into your operations, making it “business as usual” to comply with requirements rather than a fire drill when an external audit looms.
Benefits of being operationally compliant
Being operationally compliant is about building a business that’s trusted, efficient, and ready to scale.
First, yes—compliance protects you from the obvious: regulatory fines, lawsuits, breach fallout. When your controls are solid and your policies are enforced, you’re far less likely to land in hot water over a data mishandling issue or a failed audit.
Here are some other benefits:
- Customer trust and retention: Strong compliance practices prove to customers and partners that you take security and privacy seriously. This builds a positive reputation and trust in your brand.
- Operational efficiency: When compliance is woven into everyday operations, it often leads to more structured and efficient processes. Standardized procedures (like regular audits, documentation, and approvals) minimize errors and oversights. In striving to meet compliance criteria, companies frequently end up streamlining workflows and improving overall operational discipline.
- Competitive advantage: Being compliant can open doors to new business. Many large companies and regulated industries require their SaaS vendors to have certain compliance attestations (e.g. SOC 2 reports or ISO certifications) before signing a deal.
In essence, ignoring operational compliance is an invitation to both immediate troubles and long-term setbacks. The adage “if you think compliance is expensive, try non-compliance” holds true—the costs of reacting to failures far exceed the investment needed to prevent them.
“Compliance can be fun. The biggest discussion always is that compliance is only a checklist. Yeah, if you make checklists out of it, sure. But if you understand how to analyze risks and what needs to be done from a security perspective, then it is fun because the expert tries to go deeper and understand which controls help mitigate the risk.”
Fabian Weber (vCISO and ISO 27001 auditor) in discussion with Sprinto
Best practices for successful compliance operations
Building a successful compliance operation requires not just one-time effort, but ongoing good habits. Here are some best practices mid-market SaaS companies should follow to keep compliance on track:
- Leadership commitment and culture: Ensure tone from the top supports compliance. Leadership should communicate the importance of ethical, compliant operations and allocate necessary resources. Equally important, cultivate a culture of compliance at all levels—not just in memos, but in day-to-day decision-making.
- Stay up-to-date with regulations: The regulatory landscape for SaaS (data privacy laws, cybersecurity requirements, etc.) is constantly evolving. Assign someone (or a team) to monitor relevant laws and industry standards. Regularly review and update your policies in light of new rules or changes in frameworks.
- Implement strong security controls: Since many compliance obligations in SaaS revolve around data protection, invest in robust security measures. Follow best practices like encryption of data at rest and in transit, strict access controls (principle of least privilege), multi-factor authentication, regular vulnerability scanning, and firewall/IDS monitoring.
- Integrate policies into product and engineering: The biggest compliance failures often happen because teams treat it as “someone else’s job.” Embed compliance early in product lifecycles and development sprints. Involve legal and security in architectural decisions. Automate policy enforcement wherever possible—CI/CD checks, data handling guidelines, role-based access controls.
- Operationalize audit readiness: Don’t treat audits as one-off events. Build audit readiness into your regular cadence—weekly control checks, quarterly reviews, real-time dashboards. Automate evidence collection where possible, and ensure documentation is always within reach. Being “always audit-ready” isn’t about perfection. It’s about removing chaos when scrutiny arrives.
By following these best practices, compliance operations become more effective and sustainable. Think of them as habits of highly compliant organizations—they keep you ready for whatever changes or challenges come, without constant firefighting.
Implementing and managing all the above can sound daunting—but this is where leveraging the right technology can make a world of difference.
Improve operational compliance with Sprinto
Sprinto is a compliance automation platform designed specifically to help SaaS companies streamline their compliance operations. It acts as a force multiplier, handling much of the heavy lifting so you can stay compliant with less effort.
- Sprinto automatically gathers the evidence you need for audits and control verification – logs, screenshots, access records, cloud configuration snapshots, and more – so you no longer have to chase down proof manually
- Sprinto helps maintain an audit-ready state at all times. It maps your internal controls to standard frameworks (like SOC 2, ISO 27001, PCI, HIPAA) and tracks your progress on each.
- Sprinto supports multi-framework compliance with a unified approach that helps companies meet overlapping requirements efficiently—without duplicating effort. Its controls and policies come pre-mapped to common standards like ISO 27001 and SOC 2, giving teams a strong starting point.
- But compliance isn’t one-size-fits-all—Sprinto allows you to adapt these policies to reflect your unique business context. And with a broad integration library, it fits seamlessly into your existing toolstack.
Operational compliance isn’t a finish line—it’s a way of running your business. For mid-market SaaS teams, especially those scaling fast, it’s what turns reactive firefighting into proactive confidence. It’s what makes audits less terrifying, onboarding less chaotic, and enterprise deals less elusive. And more than anything, it’s what signals to the outside world—and to your own team—that you’re serious about doing things right.
The companies that win in the long run aren’t just the ones who build fast. They’re the ones who build with intention.
Get operationally compliant faster with automation
FAQs
Operational compliance is the practice of aligning your day-to-day workflows with regulatory standards, compliance rules, and internal controls. It ensures that each business unit operates in a way that meets legal compliance obligations—without disrupting productivity or slowing down growth. In today’s complex business landscape, it’s not optional; it’s a prerequisite for trust, efficiency, and scale.
A well-run compliance management program isn’t just about passing audits—it’s about enabling growth. By embedding controls that align with your business objectives, you reduce friction across teams, speed up procurement cycles, and enter regulated markets with confidence. When compliance is operationalized, it becomes a business enabler, not a blocker.
Depending on your industry, geography, and customer base, you may need to comply with a range of regulatory requirements—from GDPR and HIPAA to SOC 2, ISO 27001, or PCI DSS. These requirements vary, but the goal is the same: protect data, manage operational risk, and prove you can be trusted with sensitive information.
Failure to meet regulatory standards can lead to fines, lawsuits, reputational damage, and loss of business. But beyond the obvious, the potential risks include broken internal processes, data leaks, and missed sales opportunities—especially with customers in tightly regulated industries. Non-compliance isn’t just a legal issue; it’s a business liability.
Start by aligning your compliance management efforts with the realities of each business unit—their tools, workflows, and risk profiles. Operational compliance isn’t one-size-fits-all. The key is to create shared accountability, automate where possible, and build a program that adapts with your evolving business landscape while staying rooted in legal compliance best practices.
Raynah
Raynah is a content strategist at Sprinto, where she crafts stories that simplify compliance for modern businesses. Over the past two years, she’s worked across formats and functions to make security and compliance feel a little less complicated and a little more business-aligned.
Explore more
research & insights curated to help you earn a seat at the table.





















