Glossary of Compliance
Compliance Glossary
Our list of curated compliance glossary offers everything you to know about compliance in one place.
SOC 2 Section 3
SOC 2 Section 3, also known as the “system description,” is a requirement of the SOC 2 standard. The system description, which is included in Section III of a SOC 2 report, provides important details about the personnel, processes, and technology that support your product or service.
It is a summary of your organization and its systems. It should also include information on how the organization’s systems are monitored and tested, as well as any third-party service providers that are used to support the organization’s systems.
Additional reading
List of Examples of HIPAA Violations
SOC 2 Controls Simplified: A Guide To Staying Compliant
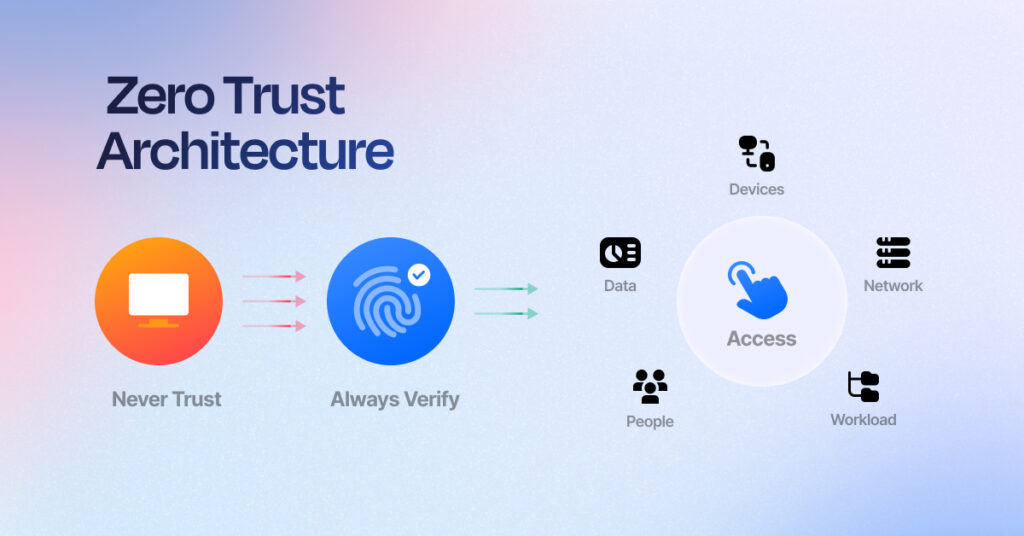
Rethinking Trust: How Zero Trust Architecture Redefines Cybersecurity

Sprinto: Your growth superpower
Use Sprinto to centralize security compliance management – so nothing
gets in the way of your moving up and winning big.