Glossary of Compliance
Compliance Glossary
Our list of curated compliance glossary offers everything you to know about compliance in one place.
ISO 27001 Data Destruction
ISO 27001 Data Destruction is an integral component of the overall framework that deals with data management when disposing of your organization’s sensitive and personal data.
The standard specifies that the data you collect should be erased when it is no longer serving its purpose and should never be recovered. Here is what goes into the destruction of physical documentation in ISO 27001:
- Shredding – Destruction of physical documents with the help of industrial shredders
- Pulverization – Reducing physical data to tiny particles with the help of (used for CDs, hard drives, flash drives), etc
- Degaussing – Erasing data from physical media with the help of powerful magnet fields like tapes, hard drives, etc
Destruction of digital data –
- Secure erasure – Covering data with multiple random patterns so that it cannot be retrieved
- Data wiping software – Using special software for clearing data on computing and storage devices
- Cryptographic erasure – encrypting data and disposing of the decryption keys
The data destruction process includes sorting out the irrelevant information in terms of sensitivity and destroying it accordingly to ensure it is out of reach.
This ensures that these types of sensitive information do not fall into the wrong hands and evade data leaks, data breaches, or any misuse of personal data that could lead to reputation damage, financial losses, etc.
Therefore, having a proper data destruction practice in your organization can help protect customer privacy and maintain a strong security front.
Also, read more about ISO 27001 Compliance
Additional reading
PCI DSS Certification Process: A Complete Guide
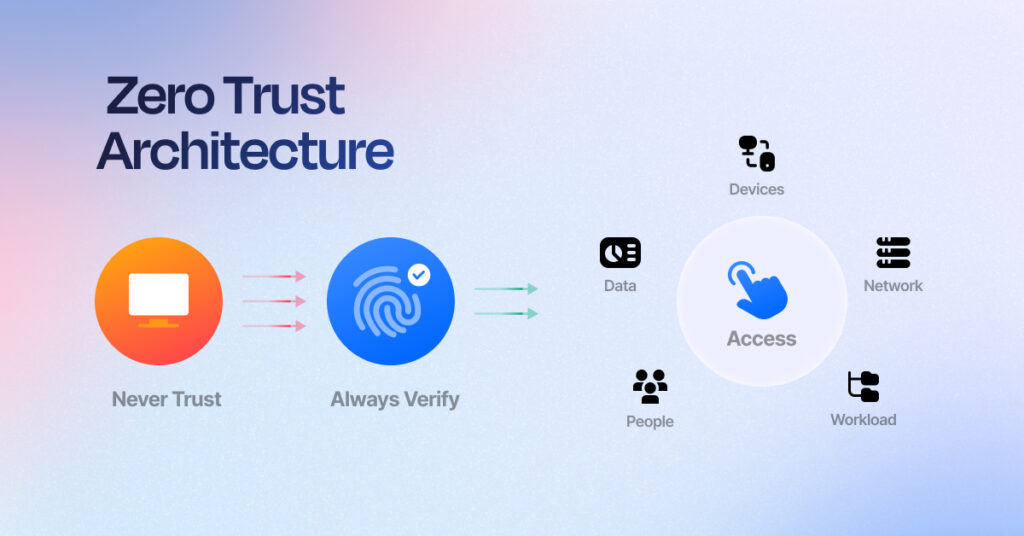
Rethinking Trust: How Zero Trust Architecture Redefines Cybersecurity
GRC System: Definition, Core Functions & How to Implement

Sprinto: Your growth superpower
Use Sprinto to centralize security compliance management – so nothing
gets in the way of your moving up and winning big.