Personal Health information and cardholder information are two of the most susceptible types of data. Although they serve different purposes, it becomes important to have measures in place to ensure safety. PCI and HIPAA have quite a few parallels and getting compliant with both frameworks will help you build unparalleled market credibility.
This blog will help you understand the distinctions and overlaps between HIPAA and PCI DSS so you can kickstart your compliance efforts.
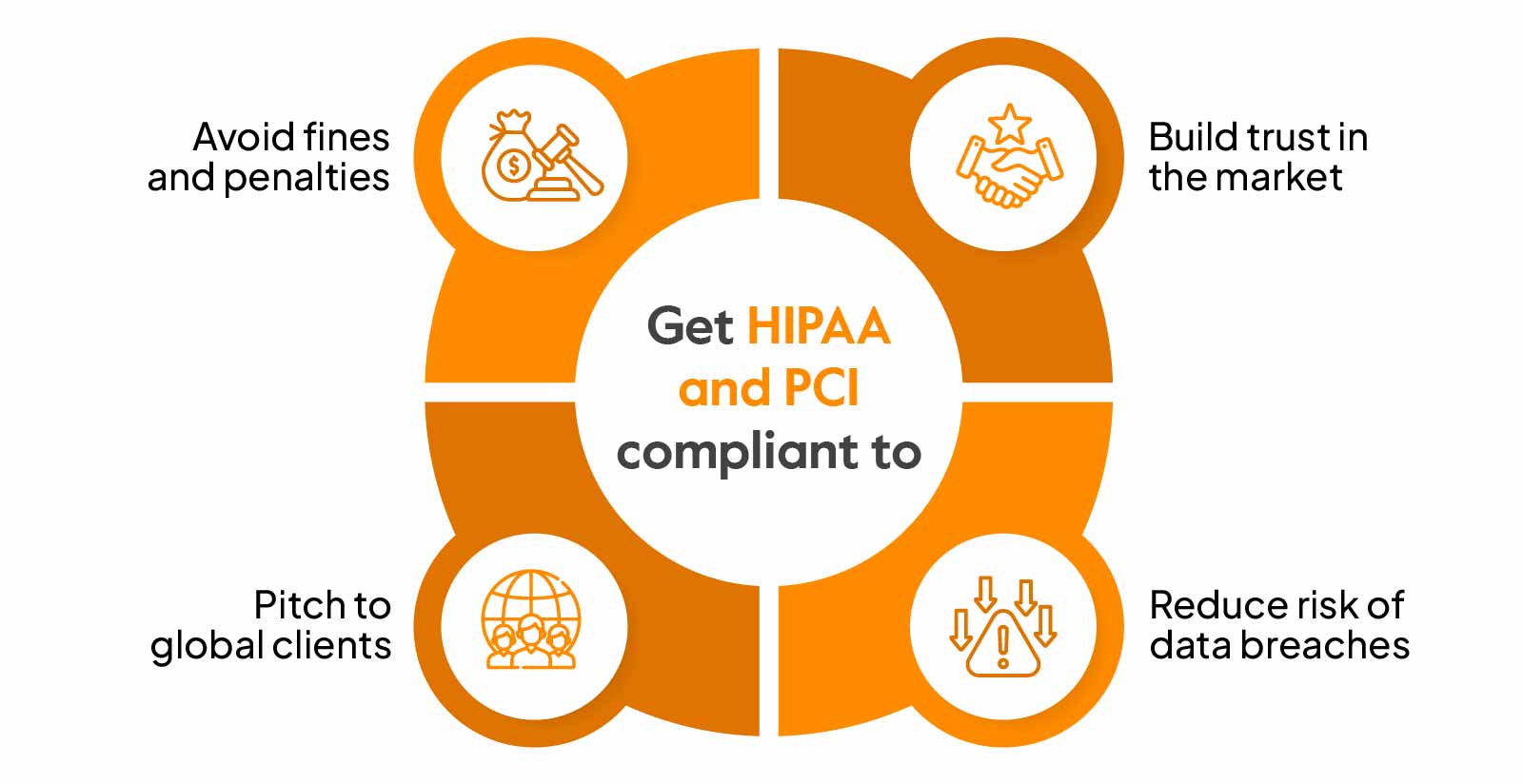
Why get HIPAA and PCI compliant?
PCI DSS and HIPAA Compliance are two very different compliance standards with the general purpose of protecting sensitive data.
HIPAA (Health Insurance Portability and Accountability Act) as a federal law (1996) has mandated the creation of administrative, physical, and technical safeguards to protect PHI (patient health information) from data breaches. These safeguards must be implemented by healthcare organizations and include security awareness training, access controls, biometric scanners, antivirus software, etc.
HIPAA has established several rules for protecting patient information’s privacy, security, and confidentiality—Privacy rules, Security rules, Breach notification rules, Omnibus rule, etc. It has also granted specific rights to patients to ensure control over their sensitive information.
The PCI data security standard protects cardholder data from theft, loss, or unauthorized access. It ensures that entities that accept, process, or transmit cardholder data follow a set of requirements and best practices to prevent breaches and maintain a secure CDE (cardholder environment). It covers 12 detailed requirements to ensure safe credit card transactions with various security controls like network security, access controls, encryption, etc.
Organizations in the healthcare industry (healthcare professionals, healthcare clearinghouses etc.) accepting credit card payments are required to get PCI and HIPAA compliant. They are also looking to:
Avoid fines and penalties
HIPAA and PCI DSS are legal compliance obligations with severe fines and penalties for non-adherence. HIPAA violations can cost you anywhere from $127 to $250,000, and PCI DSS non-compliance fines can go from $5000 per month to $100000 per month.
Build trust in the market
Maintaining a security profile or a trust page with PCI DSS and HIPAA Compliance can enhance your market perception. Compliance confidence assures customers about the safety of their data and helps businesses gain a competitive advantage.
Reduce data breach risks
The healthcare industry is a lucrative target for criminals, making it an industry with the highest number of attacks and breaches. Stolen payment information is yet another popular breach case scenario. These security breaches impact customers and the organization with reputational and financial consequences. The average cost of breaches in both these industries can reach millions of dollars, and achieving compliance minimizes this costly risk.
Pitch to global clients
PCI is a globally recognized standard, while HIPAA is required for businesses handling the PHI of U.S. residents. Compliance with these regulations can fast-track the international expansion process and shorten the sales cycle.
Difference between PCI DSS and HIPAA Compliance
PCI and HIPAA are centered around protecting different kinds of information applicable to specific industries. The way these regulations need to be interpreted and enforced also varies.
Let’s look at the major differences between HIPAA vs PCI:

Scope of information protected
HIPAA and PCI DSS safeguard very different types of data.
- HIPAA aims to protect the confidentiality, integrity, and availability of PHI (protected health information) like medical records, treatment information, personal details, etc.
- PCI DSS ensures the safeguard of cardholder data such as credit card numbers, CVVs, etc. by controlling how data is accessed and processed.
Covered organizations
- HIPAA applies to entities in the healthcare sector. These include healthcare providers, health plans, and clearinghouses.
- PCI DSS standard applies to the payment card industry. Merchants, payment processors, and service providers that collect, process, or store sensitive cardholder information must adhere to PCI regulations.
Enforcement authority
- HIPAA is enforced by the Office for Civil Rights (OCR) under the U.S. Department of Health and Human Services (HHS), making it a regulatory law (since 1996).
- PCI DSS is not a government regulation and is rather enforced by the PCI Security Council (PSC) formed by major credit card brands. These include Visa, Mastercard, American Express, Discover Financial Services, and JCB International.
Control interpretation
- HIPAA contains 2 types of security measures-addressable and required. The addressable measures can be interpreted as per the organization’s context but must satisfy the objectives specified by HIPAA. Required controls are required to be implemented as mandated by HIPAA rules.
- Although the requirements have been specified in detail for PCI, these are not mandatory. If an organization cannot comply with a requirement, it can implement compensatory controls to mitigate the intended risks.
Certification process
- HIPAA does not have a formal certification process. However, the OCR or HHS can conduct audits and investigations to verify if the organization adheres to HIPAA rules. Organizations should, therefore, conduct frequent self-assessments to ensure HIPAA compliance.
- In the case of PCI DSS, smaller organizations are required to fill out a Self-assessment Questionnaire (SAQ). Larger organizations must undergo a Qualified Security Assessors (QSA) assessment and obtain a Report on Compliance (ROC).
Continual vs point-in-time assessment
- HIPAA is a continual assessment, which means in the case of an external party risk assessment, compliance is verified from year to year.
- For PCI DSS, the organization must comply with the standard throughout the year, but the assessment verifies the compliance at a specific time (for a particular period).
Similarities between PCI DSS and HIPAA Compliance
Even with differences in scope and applicability, the frameworks share a common purpose and some common compliance requirements.
Let’s have a look at these similarities:

Focus on data security
The primary goal of both standards is to protect critical and sensitive data. Both frameworks advocate conducting risk assessments and vulnerability scans to identify potential threats to ensure data security.
Non-compliance consequences
Non-compliance with these frameworks attracts serious repercussions—fines, penalties, lawsuits, increased scrutiny, and reputational damage. However, the degree of these consequences can differ based on the severity of violations.
Control overlap
There are several overlapping controls for both these frameworks. Check out the key requirements on common controls:
| Control | Common control for PCI and HIPAA? |
| Risk Assessment | Yes |
| Information System Activity Review | Yes |
| Access Control and Access Management | Yes |
| Security Roles & Responsibilities | Yes |
| Workforce Security | Yes |
| Entry & Exit Process | Yes |
| Awareness & Training Program | Yes |
| Protection from Malware | Yes |
| Log-in Monitoring | Yes |
| Account & Password Management | Yes |
| Incident Response Plan | Yes |
| Transmission Security | Yes |
| Contingency Plan | No, applies only to HIPAA |
| Evaluation Program | Yes |
| Third-Party Security | Yes |
| Physical Security | Yes |
| Device & Media Control | Yes |
| Policies and Procedures Documentation | Yes |
| Integrity Protection | No, applies only to HIPAA |
| Denial of Service | No, applies only to HIPAA |
| Workstation Security | Yes |
| Standard Operating Procedures | Yes |
Should you get PCI and HIPAA compliant together?
If you are a covered entity under HIPAA that accepts credit cards, you must be both HIPAA and PCI DSS compliant. Although there are some stark differences between the scope and requirements of the two, it makes sense to fast-track implementation with common controls. So, you should get PCI and HIPAA compliant together.
Here’s a tool to determine whether you’re a covered entity:
Download Your Covered Entity Decision Making Tool
Understanding requirements and identifying applicability
Read and understand the regulatory requirements of both frameworks. Make a list of controls and identify the common systems that fall under the scope of PCI and HIPAA.
Gap analysis
Conduct a risk assessment of the current security practices to identify compliance gaps. Highlight security gaps that need improvements for both HIPAA and PCI. For example, weak authentication measures can be a common miss and lead to unauthorized access to PHI or credit card information.
Preparing compliance plans
Create tactical compliance plans for both frameworks. These will include policies and procedures that need to be updated/created, security measures to mitigate risks, assignment of roles, training, etc. In the case of HIPAA, business associate policies will also be finalized. Similarly, the PCI compliance plan will include vulnerability scans and pen testing schedules.
Also, check: Top 10 Vulnerability scanning tools in 2023
Implementing controls
Start with implementing common security measures like firewalls, encryption, access controls, awareness training, data backups and recovery etc. There can also be a further segregation-begin with required controls first and then with addressable controls. This will reduce the time taken for oversights, testing, and assessments and get you to the readiness stage for both standards faster. You can pick the remaining specific controls in the second phase.
Pro tip: PCI has laid out the requirements explicitly, while HIPAA provides high-level guidelines. Start with PCI control implementation, and a lot of requirements for HIPAA will be taken care of.
Documentation
Get ready with the documentation—assessment reports, training records, business associate agreements (for HIPAA), VAPT reports (PCI) etc. Compliance records of vendors handling sensitive information must also be gathered. The documentation must be properly organized for easy access by the auditor or assessor.
Certification
You can conduct readiness assessments to verify compliance and initiate two branches in parallel:
- Self-assessments and external audits for HIPAA certification
- Self-assessment questionnaires and on-site assessments by QSA for PCI DSS certification.
How Sprinto can help here:
Sprinto helps you automatically identify common controls for frameworks to help organizations scale their compliance efforts. Many of our clients have made headway on multiple frameworks through this simple method.
Here’s case study on how HubEngage prepared for HIPAA, GDPR, SOC2, and ISO 27001 together.
Sprinto’s automated compliance solutions expedite the implementation process. Continuous control monitoring at a granular level helps you track if the right controls are implemented and if they are working as intended. You can also enable proactive alerts when there are deviations from compliance requirements or if controls are about to fail.
You can expand the scope of your compliance programs with the following:
For HIPAA:
- Integrated risk assessments and risk registers
- Business Associate Agreements
- Data breach management module
- Access management module
- Security incident tracking module
- HIPAA training
- Automated evidence collection and more
Check out our sweeping coverage here.
For PCI:
- Integrated risk assessments with VAPT support
- Editable policy templates
- PCI DSS training
- Audit dashboard + ASV vendor support and more
Get how we get you PCI compliant here
Final thoughts
Both HIPAA and PCI are complex frameworks to interpret and implement and require an ongoing commitment to demonstrate compliance. The intricacies of the requirements become even more demanding because of the sensitive information passing through multiple touchpoints. Turning to automation in such a scenario not only makes things easier but ensures you get to your desired state in as short time as possible.
A compliance automation tool like Sprinto can help you streamline security and compliance tasks and leverage automated checks to help you reach the> 90% mark in weeks rather than months.
Interested? Learn more here.
FAQs
How often are risk assessments conducted for HIPAA and PCI?
Risk assessments for HIPAA and PCI should be conducted at least annually or whenever significant infrastructure or business changes occur.
What is the difference in international implications of PCI and HIPAA?
HIPAA is a U.S. federal law. It applies to international businesses having access to or working with companies that have access to the PHI of U.S. residents.
PCI DSS is a global standard for any business handling sensitive cardholder data.
What is the difference between breach notification requirements of HIPAA and PCI DSS?
HIPAA has specific breach notification requirements. The covered entity must inform about the breach to affected parties by 60 days after breach discovery. If more than 500 individuals have been affected, the HHS must also be informed.
PCI DSS on the other hand has no specific breach requirements. The credit card brands have laid down their unique requirements in case of a breach and the PCI Council has specified guidelines for responding to a breach including timely and prompt notifications.
Author
Payal Wadhwa
Payal is your friendly neighborhood compliance whiz who is also ISC2 certified! She turns perplexing compliance lingo into actionable advice about keeping your digital business safe and savvy. When she isn’t saving virtual worlds, she’s penning down poetic musings or lighting up local open mics. Cyber savvy by day, poet by night!Explore more
research & insights curated to help you earn a seat at the table.