Whether you are a covered entity or a business associate, receiving a communique from the Office of Civil Rights can be stressful. Hearing from the enforcing authority of HIPAA, one of the most stringent healthcare regulations in the world, sure isn’t what your dreams are made of.
But on the off chance you do get selected for a HIPAA audit, what should you do? For starters, don’t panic. We have put together this guide on what you must do and how you could prepare for a HIPAA compliance audit.
Let’s dive in.
📋 Quick Summary in 60 Seconds
Why a HIPAA Compliance Audit Matters:
- Ensures your organization securely manages Protected Health Information (PHI).
- Avoids costly OCR penalties and reputational damage.
- Demonstrates proactive compliance and data protection maturity.
Key Steps to Prepare:
- Appoint a HIPAA Security and Privacy Officer.
- Conduct staff training and regular risk assessments.
- Review policies, perform internal audits, and maintain recovery plans.
Audit Cost & Time Frame
- HHS-led HIPAA audits are typically free, as the government covers auditor costs.
- Voluntary internal HIPAA audits often cost around $8,000 and take 4–6 weeks, depending on scope, organization size, and documentation readiness.
Challenges:
- Limited prep time (10 days) once OCR selects you.
- Managing compliance documentation manually.
How Sprinto Helps:
- Automates HIPAA monitoring, training, and documentation.
- Keeps you continuously audit-ready to avoid last-minute panic.
- Stay compliant, confident, and audit-ready with Sprinto — book a demo
What is HIPAA compliance audit?
A HIPAA compliance audit is an annual exercise conducted by the US Health and Human Services (HHS) Office for Civil Rights (OCR) to examine how covered entities or business associates handle their protected health information (PHI and ePHI). PHI is any health information that identifies an individual (such as name, address, and health conditions), and is maintained or exchanged electronically or in hard copy.
Why do you need to undergo a HIPAA compliance audit?
Short answer: you don’t have much choice if you get picked for an audit! The OCR periodically selects organizations for audits to ensure compliance with federal law. Note that if selected for an audit, you will have just 10 days to respond to the OCR.
For example: In 2019, Anthem Inc., one of the largest health insurers in the US, was required to pay $16 million after failing a HIPAA compliance audit due to a security breach. And Anthem is just one among the many organizations that have paid severely for their oversights in HIPAA certification.
How to conduct HIPAA compliance audit?
The key to passing your HIPAA audit with flying colors is to be HIPAA ready always. And so, the best time to prepare for an audit is before you’re in one.

Here are the 6 steps to complete HIPAA Compliance Audit in 2023:
- Appoint a HIPAA Security and Privacy Officer
- Conduct HIPAA Training for Employees to Make Them Understand HIPAA Guidelines
- Create a Risk Management Plan and Conduct a Risk Analysis
- Implement Periodic Review of Policies and Procedures
- Conduct an Internal Audit
- Create an Internal Recovery Plan
1. Appoint a HIPAA security and privacy officer
HIPAA mandates organizations to appoint a HIPAA security and privacy officer. In the past, it was commonly assumed that your company’s IT manager would be responsible for security and privacy by default. However, this is no longer the case, as overseeing these areas has become a much larger responsibility.
So, who should you appoint as a HIPAA privacy and security officer? The assigned individual(s) will take charge of handling all HIPAA-related issues, including protection of. ePHI and PHI.
The primary responsibilities of a HIPAA privacy and security officer include:
- Develop and oversee your organization’s privacy policies and procedures
- Ensure that your security policies and procedures are adequate to protect the company’s PHI, and develop new policies and procedures where needed
- Annually train and monitor your organization’s workforce on HIPAA regulations
- Investigate possible breaches where ePHI or PHI may have been compromised
- Establish policies and procedures to protect PHI when privacy policies do not adequately address the issue
When appointing a candidate for this role, consider their experience, technical expertise, and ability to interact effectively with staff and executives. Remember, this officer(s) will be responsible for liaisoning with OCR during the audit.
Also check: Top 5 Components of HIPAA
2. Conduct HIPAA training
You must train your employees on HIPAA regulations, its many nuances and the implications of noncompliance. Comprehensive training ensures that all employees in your organization are up to date with the recent updates in the law as well as the best practices to ensure security of the PHI.
The first step to achieving this goal is to provide education and training materials to all employees, covering topics such as the rights of patients and how to handle confidential information. Ideally, every employee should get trained soon after their joining.
Here is a checklist of what your HIPAA training must accomplish.
- Ensure employees understand the importance of HIPAA and why it’s necessary to protect PHI
- Reviews the basics of HIPAA law and how it applies to your company
- Outlines the specific procedures and controls employees should follow when handling patient Information
- Explains the consequences of violating HIPAA rules
- Ensure employees are always updated on the latest changes to HIPAA law through regular training
3. Create a risk management plan and conduct a risk analysis
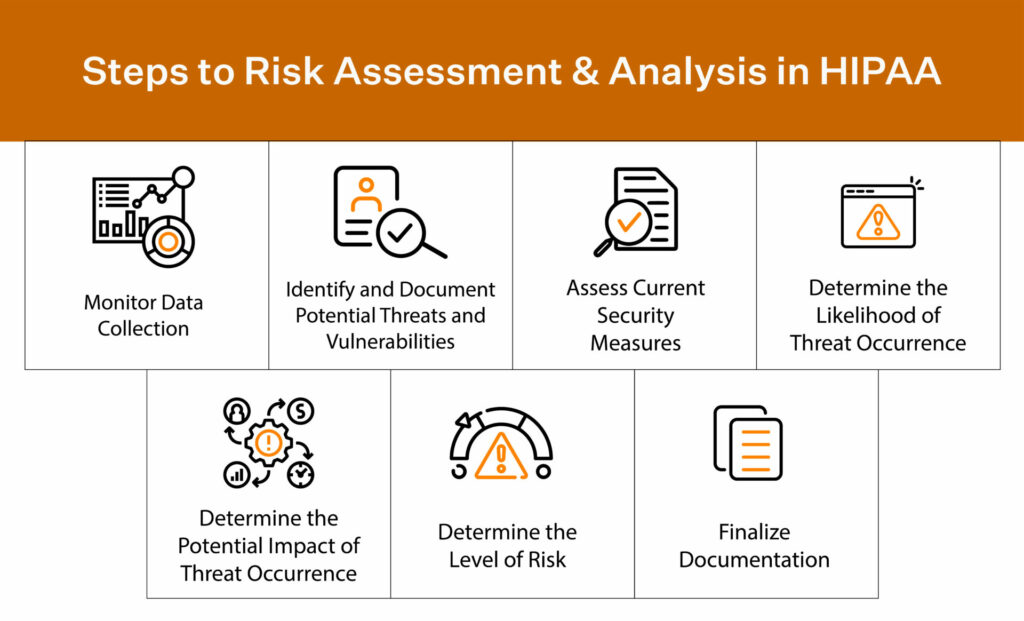
Performing a security analysis is the next step in identifying any vulnerabilities. Each organization is different and its risk assessment processes vary in order to accommodate size, risks, and business needs. That’s why there is no “one-size-fits-all template” readily available.
Note: you need to maintain sound documentation that you have conducted your organization’s risk assessments and HIPAA risk analysis to produce during the audit.
So, here are five steps you can take to conduct a risk assessment:
- Map how your PHI flows and where it is created and transmitted. What happens to PHI in the system, how is it stored, and how does it leave the environment?
- Identify threats, risks, and vulnerabilities in your system, applications, and processes. Hackers, weak passwords, and disgruntled employees are all threats to your business.
- Decide and analyze your HIPAA risk level. To properly rank risks, consider both the probability of a threat occurring and its potential impact.
- Create a risk management plan and test your environment with vulnerability scans, penetration tests, and gap analysis.
- Document and outline everything.
By proactively managing risks, you will ensure the safety and security of your patient’s sensitive information stored in HIPAA-compliant software. That you will clear your HIPAA audit is a happy incident.
Based on your risk analysis, you must implement the required safeguards and consider implementing the addressable ones.
4. Implement periodic review of policies and procedures
As with any aspect of a successful business, it’s not enough to simply establish policies and procedures – you must also regularly review and refine them for maximum efficiency.
You can achieve this by implementing periodic reviews of policies and procedures. The OCR will review how your policies are being implemented and see how you’ve created a progression plan. This way, the OCR knows when progress is being made towards achieving the goal of new programs or policies.
For example, a company reviews employee training materials and tools annually to check for understanding of HIPAA policies and procedures.
By taking proactive steps to review and update policies regularly, organizations can show their dedication to maintaining HIPAA compliance and avoid any possible penalties during an audit.
5. Conduct an internal audit
An internal audit allows you to identify and address potential risks or instances of non-compliance saving you both time and money. You can perform a security risk analysis to determine weaknesses in your internal audit process.
For example, do your employees know how to report a HIPAA violation?
An internal audit is conducted to identify areas where answers are needed and procedures can be updated. Some areas for review include technical safeguards for the protection of ePHI and the physical security of paper files, among others.
Checkout: Top 10 HIPAA Consultants you need to know in 2024
6. Create an internal recovery plan
A crucial part of HIPAA auditing is having a plan for further steps in case of a data breach or other violation. This internal recovery plan should outline specific steps to address and rectify the breach as well as prevent future occurrences.
For example, the plan may include steps for notifying affected individuals, reporting the incident to necessary authorities, conducting a risk assessment, implementing additional security measures, and providing staff training on compliance protocols.
Developing an effective internal recovery plan can mitigate damage in the event of a HIPAA violation and demonstrate an ongoing commitment to compliance during audits.
What happens when a HIPAA compliance audit comes knocking on your door?
Well, typically, the OCR first sends questionnaires to the selected organizations and decides to audit them based on the answers it receives. Then, the OCR auditors thoroughly investigate your organization to ensure your compliance with applicable HIPAA rules. The audit includes a review of your current policies regarding the confidentiality, integrity, and availability of PHI.
The audit report documents your efforts and may identify gaps or weaknesses in your existing system. At the end of the audit, the OCR will send you its draft findings. You must develop and revise your policies and procedures within 60 days and revert to the HHS. Once your corrective action plan is approved, you have 30 days to implement the updated policies.
Failure to verify or comply with any of the rules can result in hefty financial penalties against your organization. Your best bet is to consistently review and update your HIPAA policies and procedures, train staff on security measures, and promptly address any reported issues.
Must Check: HIPAA Certification Cost [Updated 2024 + Free Checklist]
How much does a HIPAA audit cost?
HHS covers the cost of the on-site auditors. It is safe to note that neither covered entities nor their business associates bear the costs of a HIPAA audit.
But if you want to conduct an internal audit (by an external auditor) to review your HIPAA compliance, it could set you back by about $8000 over a four-six week period. Again, the cost of this audit can vary greatly depending on several factors. For example, a larger company with multiple locations and a complex network may require a more thorough audit, resulting in a higher cost than an individual practitioner’s office.
How long does it take to complete a HIPAA audit?
It takes roughly about a month to complete the HIPAA audit. As per OCR, organizations that get selected for audits, will have 10 business days to review and return written comments, if any, to the auditor. The auditor will complete a final audit report for each entity within 30 business days after the auditee’s response.
Post this, OCR will share a copy of the final report with the audited entity.
Though onsite audits will be more comprehensive, the timeline for reviewing investigation findings and submitting comments is the same.
Types of HIPAA violations that can cause HIPAA audit
There are many types of violations in HIPAA, but here are some of the most common violations that you need to be aware of:
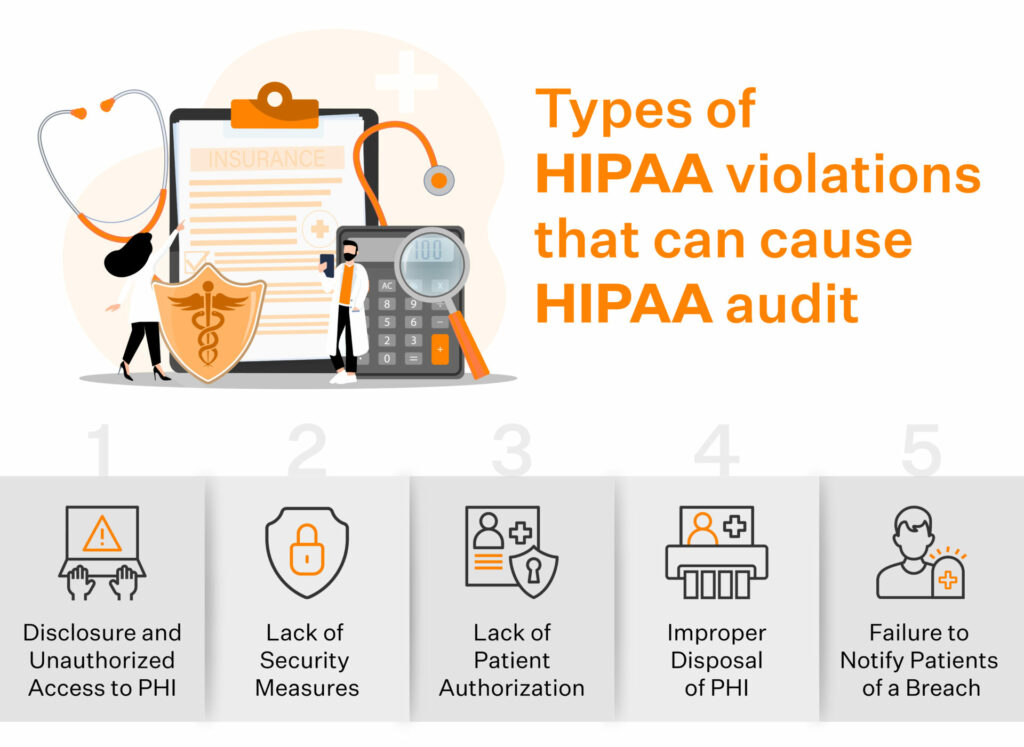
Disclosure and unauthorized access to PHI
A frequent HIPAA infringement is unauthorized access or revelation of PHI. HIPAA requires business associates and covered entities to ensure that authorized people have access to PHI.
Here’s a tool to determine whether you’re a covered entity:
Download Your Covered Entity Decision Making Tool
For example, your employee may inadvertently mail a PHI to an incorrect recipient instead of the said patient. Now the incorrect recipient can access PHI without any authorization whatsoever. This is an example of the mishandling of medical records.
Lack of security measures
Another common HIPAA violation is a lack of security measures to protect PHI from unauthorized access or disclosure. Business associates and entities must implement physical, technical, and administrative security measures to protect PHI.
For example, a ransomware attack can infect your network servers by copying the patient record due to a lack of security measures. Or an employee may leave their laptop with PHI access open to public view, or a new employee might miss going through the HIPAA training.
Lack of patient authorization
HIPAA also requires obtaining patient authorization before using or disclosing PHI for most purposes. Authorization must be obtained from the patient in writing and the consent must specify the specific uses or disclosures.
Improper disposal of PHI
You are also required to take steps to ensure the proper disposal of PHI. PHI should be shredded, burned, or otherwise destroyed so that it cannot be read or reconstructed. However, HIPAA requires you to maintain all HIPAA-related documentation for six years.
Failure to notify patient of a breach
Under HIPAA, covered entities are required to notify patients if their PHI has been subject to a breach. A breach is defined as an unauthorized use or disclosure of PHI that compromises its privacy or security.
How can Sprinto help you with HIPAA compliance audit?
Ensuring compliance with HIPAA regulations can be a daunting task for any business associate. While your BAA would spell out the extent of your responsibilities, you must be ever vigilant and comply with HIPAA.
Sprinto is built to help cloud-hosted business associates get HIPAA compliant in an easy and effortless way. From editable policy templates to integrated risk assessments with in-app suggestions on the required safeguards for the identified risks, Sprinto’s compliance automation software packs a punch. The platform also offers HIPAA training modules for your employees, and updates the modules to reflect the most recent changes to the law.
Sprinto’s documentation trail with evidence collection and continuous real-time monitoring of your compliance posture sets you up to bring your compliance A-game every day.
Schedule a free demo to see how Sprinto can help you get HIPAA compliant and stay compliant.
FAQs
Why and when do HIPAA compliance audits come into the picture?
The OCR started conducting HIPAA audits in 2014. There are several reasons behind HIPAA compliance audits, and even if you are not involved in any breach, an audit might come knocking on your door.
More often than not, it is the large healthcare organizations that get picked for random HIPAA audits. That said, organizations can also be selected for HIPAA audits when a complaint of violation is filed against them (by a patient, whistleblower, or employee). It’s important to note that a complaint doesn’t always come in the form of a formal complaint.
What are covered entities & business associates?
HIPAA defines covered entities as healthcare providers, health insurance companies, and healthcare clearinghouses that conduct transactions electronically and generate, store, transmit and handle PHI. Business associates are service providers, vendors, and entities that perform activities that involve the use or disclosure of PHI.
How often is a HIPAA audit conducted?
OCR conducts the HIPAA audit annually; but companies are either chosen randomly or following complaints. The Health Information Technology for Economic and Clinical Health (HITECH) Act necessitates that the HHS regularly audit covered entities or business associates to ensure they comply with the HIPAA rules.
Remember that you can audit internally or hire an auditor to review your current procedures and policies related to safeguarding information before the OCR audit.
Who can perform a HIPAA audit?
HIPAA audits are conducted by the OCR. OCR is a division of the HHS responsible for enforcing HIPAA’s Privacy, Security, and Breach Notification Rules.
What does a HIPAA Compliance audit cost?
HHS-led HIPAA audits are free, since the government covers auditor fees. In contrast, voluntary internal HIPAA audits typically cost around $8,000, depending on the organization’s size and the scope of systems and data reviewed.
How long does a HIPAA compliance audit take?
Timelines vary, but voluntary internal HIPAA audits usually take 4–6 weeks. Duration depends on complexity, readiness, and how quickly documentation and evidence can be provided.
Author
Meeba Gracy
Meeba, an ISC2-certified cybersecurity specialist, passionately decodes and delivers impactful content on compliance and complex digital security matters. Adept at transforming intricate concepts into accessible insights, she’s committed to enlightening readers. Off the clock, she can be found with her nose in the latest thriller novel or exploring new haunts in the city.Explore more
research & insights curated to help you earn a seat at the table.

























