ISO 27001 is the internationally recognized standard for information security management, covering the protection of information in any form, digital, physical, and beyond. It defines the requirements for establishing, implementing, maintaining, and continually improving an Information Security Management System (ISMS), while Annex A provides a set of reference controls that organizations can apply based on their risk assessment and treatment decisions.
The ISO 27001 report is a crucial document that every organization looking to get an external audit requires. The report addresses components such as the scope of the audit, areas of non-conformity, vulnerabilities, and issues. The ISO 27001 report essentially indicates how audit-ready your organization is.
What is an ISO 27001 report?
An ISO 27001 report is like a report card for the organization’s Information Security Management System (ISMS). It reflects how the organization handles and protects their data assets and the potential vulnerabilities that currently exist.
The report helps in getting a clear overview of the organization’s compliance with the ISO 27001 requirements so that the reliability and resiliency of the ISMS systems can be maintained. It is a part of the ISO 27001 internal audit process and helps the organization prepare for the external audit. It also assures the stakeholders that their data is safe.
Why is the ISO 27001 report required?
The ISO 27001 report is a reliable tool and a crucial document that allows you to track and manage the capabilities of an organization’s ISMS in accordance with ISO 27001 requirements.
Here are some more reasons why an ISO 27001 report is required.
- The ISO 27001 internal audit report helps demonstrate conformance with the ISO 27001 standard by documenting the findings of the internal audit process.
- The report helps the organizations address the non-conformities and vulnerabilities identified in the internal audit. This helps in identifying the areas of improvement to boost the organization’s security posture.
- While the internal audit report is typically an internal document not shared externally, the findings feed directly into the external certification audit. It is the resulting ISO 27001 certificate and certification report issued by the accredited certification body that serves as external assurance for customers, business partners, and stakeholders that your organization meets the standard’s requirements.
Here is a template for the internal audit:
Download Your ISO 27001 Internal Audit Template
What does the ISO 27001 compliance report include?
The ISO 27001 compliance report includes detailed information about the internal audit and its results so the stakeholders and the ISMS team can take further steps.
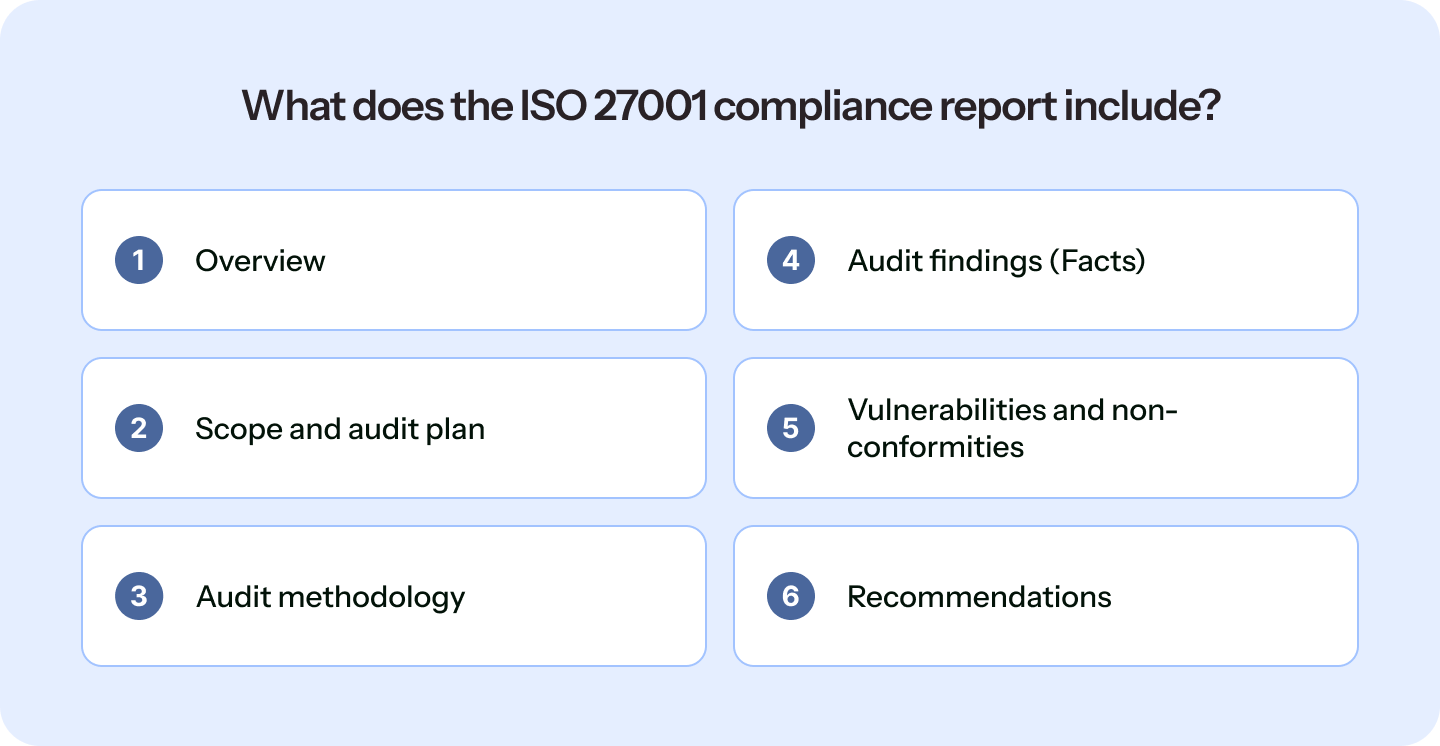
Let’s look at the different sections of the ISO 27001 report:
1. Overview + executive summary
This section provides an overview of the ISO 27001 report and contains an executive summary that stakeholders and senior management can quickly refer to for understanding the findings of the internal audit.
2. Scope and audit plan
This section contains three important aspects of the ISO 27001 audit:
- The scope of the audit (areas that are covered in the audit, locations, staff, business processes, etc.)
- The name of the auditor(s) that conducted the audit.
- The date and time plus locations of the audit.
3. Audit methodology
This section describes the techniques and methodologies used for the audit, such as sampling procedures, vulnerability assessment processes, penetration testing methods, and more. It helps in understanding the process followed in conducting the audit.
4. Audit findings (Facts)
This section includes the findings for each area of the audit. It includes evidential samples (if possible) for the facts mentioned. It only contains the facts relevant to the ISMS and its compliance with the ISO 27001 standard and should not include any opinions based on assumptions from trends.
5. Vulnerabilities and non-conformities
This section documents the audit findings in terms of how well the ISMS controls and processes conform to ISO 27001 requirements. It typically includes:
- Major non-conformities: Significant gaps where a requirement of the standard has not been met and must be addressed before certification can be granted
- Minor non-conformities: Isolated gaps or weaknesses that do not prevent certification but require corrective action within an agreed timeframe
- Opportunities for improvement: Areas where controls are functioning but could be strengthened further
- Observations: Early indications of potential issues that do not yet constitute a non-conformity but warrant monitoring
6. Recommendations
This section contains any recommendations or feedback, or remediation steps from the auditor(s). Generally, the auditor suggests best practices and measures the organization can take to address both minor and major non-conformities to be ISO 27001 audit-ready.
Recommended: Automate ISO 27001 compliance
How to Prepare for ISO 27001 Report?
Before creating and documenting the audit report, you first need to carry out the internal audit to document the findings in the report.
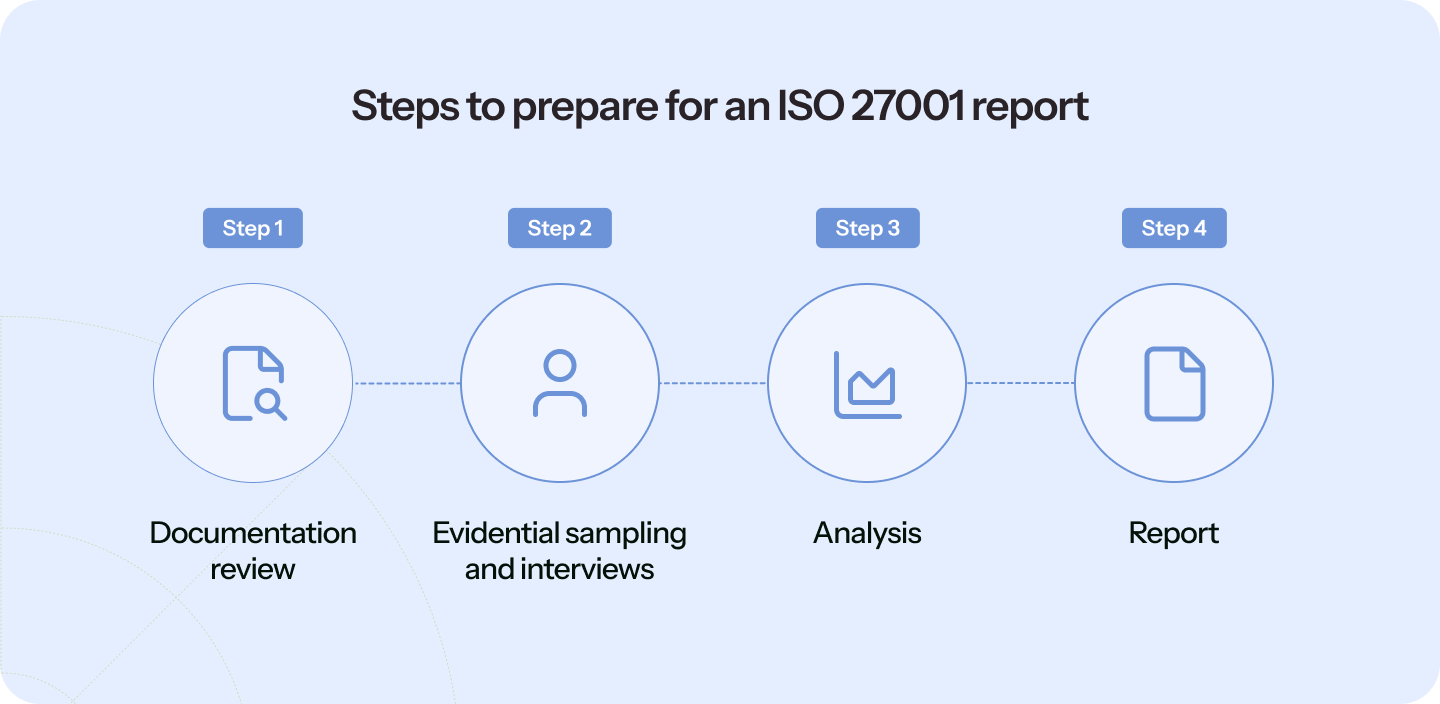
Let’s quickly go through the steps involved to help you prepare for the ISO 27001 report.
1. Documentation review
Get started with the documentation part, such as the ISO 27001 scope statement, Statement of Applicability, Information Security Policies & Procedures, Risk Assessment & Treatment Plans, and more. Also, list the people who built the ISMS and the internal auditors. This way, auditors can ask the control owners to resolve any queries.
2. Evidential sampling and interviews
As discussed above, the audit report contains the sampling of evidence. It also includes interviewing the staff, control owners, partners, and more. Some other sources of evidential sampling are policy documents, instructions documents, previous audit reports, data summaries, external surveys, performance indicators, databases, and so on.
3. Analysis
After data gathering, the auditor will analyze the findings to identify the non-conformities and areas of improvement. To prepare for this, you need to understand the three categories of findings: major non-conformity, minor non-conformity, and opportunity for improvement.
It also includes positive points where the organization has demonstrated good security practices, as well as Opportunities for Improvement (OFIs): observations that highlight areas where the ISMS could be strengthened, without necessarily indicating a non-conformity.
4. Report
Once the auditor analyzes the findings, the internal audit report is finalized and shared with senior management and relevant internal teams — not external stakeholders. It feeds directly into the management review process, where leadership evaluates the ISMS performance and makes decisions about resources, improvements, and corrective actions. Control owners and relevant teams should be prepared to address identified non-conformities and implement corrective actions within agreed timeframes before the external certification audit.
Also, check out the breakdown of ISO 27001 certification cost
Conclusion
ISO 27001 report is a crucial document for the stakeholders and helps you prepare for the external certification audit. And while you’re looking for ways to simplify your ISO 27001 journey, consider a compliance automation solution like Sprinto.
Sprinto’s compliance automation platform can help you put most compliance processes on auto-pilot. The platform helps you automate crucial tasks such as evidence collection and helps you speed up the path to getting audit ready. You can also monitor controls and risks in real-time from within a single dashboard.
Want to learn more? Speak to our experts today.
FAQs
To write a good ISO 27001 report, you need to focus on the basics such as executive summary, audit plan, audit process, results, non-conformities, and corrective actions. When you follow the structure, you will be able to draft a good and comprehensive ISO audit report.
ISO 27001 is an international standard for establishing and maintaining an ISMS, providing a structured approach to managing information security risks across people, processes, and technology. On the other hand, SOC 2 is an attestation standard based on the AICPA’s Trust Services Criteria, in which an independent CPA firm evaluates and reports on the effectiveness of an organization’s controls for security, availability, processing integrity, confidentiality, and privacy. While both address information security, ISO 27001 results in a certification and SOC 2 results in an attestation report, and they serve different audiences and purposes.
While ISO 27001 does not prescribe a specific report format, Clause 9.2 requires organizations to conduct internal audits and retain documented information as evidence of the audit results. In practice, this means an internal audit report or equivalent documented record is effectively required to demonstrate conformance with the standard. The format is flexible, but the documentation of audit findings, non-conformities, and follow-up actions must exist and be available for review during the external certification audit.
Cyber security is a part of ISO 27001 as the standard guides organizations to take a holistic approach to information security by vetting people, technologies, and policies. The ISMS implemented by following ISO 27001 requirements is an efficient tool for cyber resilience, risk management, and more.
Common control gaps found in ISO 27001 audits include incomplete risk assessments, poor access controls, outdated security policies, insufficient evidence of control implementation, and weak incident response plans.
Author
Sucheth
Sucheth is a Content Marketer at Sprinto. He focuses on simplifying topics around compliance, risk, and governance to help companies build stronger, more resilient security programs.
Reviewer
Swapnil Tripathi
Swapnil Tripathi is a seasoned Governance, Risk, and Compliance (GRC) professional with deep expertise in information and payment security. Certified as a PCI-DSS Qualified Security Assessor (QSA), ISO 27001 Lead Auditor (LA) and Lead Implementer (LI), he specializes in compliance frameworks essential for secure operations.Explore more ISO 27001 articles
ISO 27001 Overview & Requirements
ISO 27001 vs Other Frameworks
ISO 27001 Audit & Certification Process
ISO 27001 Management & Assessment
ISO 27001 Implementation & Automation
ISO 27001 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.











