- Cybersecurity protects organizations from financial losses, operational disruptions, and reputational damage caused by threats like malware, phishing, DDoS, and brute force attacks – with breaches costing businesses heavily (remote work alone added $137K to average breach costs).
- Key business benefits include safeguarding sensitive data and IP, maintaining customer trust and brand loyalty, ensuring regulatory compliance, improving workforce productivity by preventing downtime, and enabling secure remote work.
In the age of the internet, organizations are heavily relying on IT infrastructure to keep them safe from cyberattacks. As more and more organizations are adopting digital transformation, the risk of cybercrime is increasing at a rapid rate; so is the importance of cybersecurity.
Cybersecurity has become the knight in shining armour. Strong cybersecurity policy and infrastructure work together to secure computer systems and networks from an unauthorized attack or access. Businesses, individuals, and governments are investing heavily to reap the benefits of cybersecurity in protecting their assets and data against hackers. For any business to survive in today’s competitive world, it requires the right tools and cyber security strategy.
What is cybersecurity?
Cyber security is the practice of securing computer systems and networks against unauthorized access or being otherwise damaged or made inaccessible by mitigating information risks and vulnerabilities. Information risks include unauthorized access, interception, use, disclosure, or data destruction.
What is the purpose of cyber attacks?
The purpose of Cybersecurity serves as a shield to safeguard devices and services from malicious attacks orchestrated by hackers, spammers, and cybercriminals. Organizations employ this crucial practice to shield themselves against various threats, including phishing schemes, ransomware attacks, identity theft, data breaches, and potential financial losses.
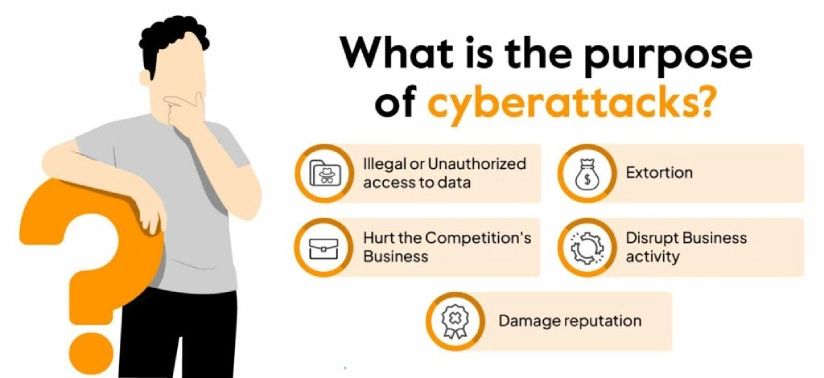
The purpose of cyber attacks can be:
Illegal or Unauthorized access to data
The aim of a cyber attack is to gain unauthorized access to sensitive data. Hackers employ various techniques to infiltrate systems, seeking to either destroy or manipulate critical data. The motive behind such intrusions can range from causing chaos to exploit a vulnerability for strategic gain.
Extortion
Sometimes, cybercriminals may resort to extortion tactics by illegally obtaining sensitive information and threatening the victim. These threats could range from information exposure to data manipulation with a ransom in exchange. This attack places organizations in a precarious position, emphasizing the need for robust cybersecurity measures to prevent such coercive actions.
Hurt the Competition’s Business
Hackers target trade secrets and valuable information like intellectual property. They aim to inflict significant damage on a competitor’s business by stealing and exposing these proprietary assets. Releasing trade secrets can lead to losing a competitive edge, affecting profitability and market standing.
Disrupt Business activity
Some cyber attacks focus on disrupting an organization’s regular operations. This could involve tactics like Distributed Denial of Service (DDoS) attacks, which aim to overwhelm systems and networks. The objective is to create chaos, impede business activities, and potentially cause financial losses. Cybersecurity measures are essential to mitigate such disruptive threats.
Checkout: Cyber Hygiene Checklist: Break Free from Complacency
Damage reputation
Breaches lead to a loss of trust among an organization’s customer base.
The significance of cyber security in today’s digital age cannot be understated. A single security breach has severe consequences in today’s interconnected world, resulting in heavy financial losses and data loss, as well as hurting its reputation.
For instance, in 2017 Equifax breach exposed the personal identification information of over 145 million people. In 2018, the breach at Marriott leaked the personal information of over 500 million people.
As our dependence on IT and technology grows, so do the volume and sophistication of cyberattacks. Cybersecurity helps to secure systems and networks against these threats.
Also check out this video on cyber security:
Importance of cyber security
Cybersecurity is important because it protects organizational assets and services from malicious attacks and safeguards all types of data, including but not limited to sensitive data, protected health information (PHI), and personally identifiable information (PII) from theft and loss.
Obtaining a cybersecurity certification can help you protect yourself against fraud and online assaults!
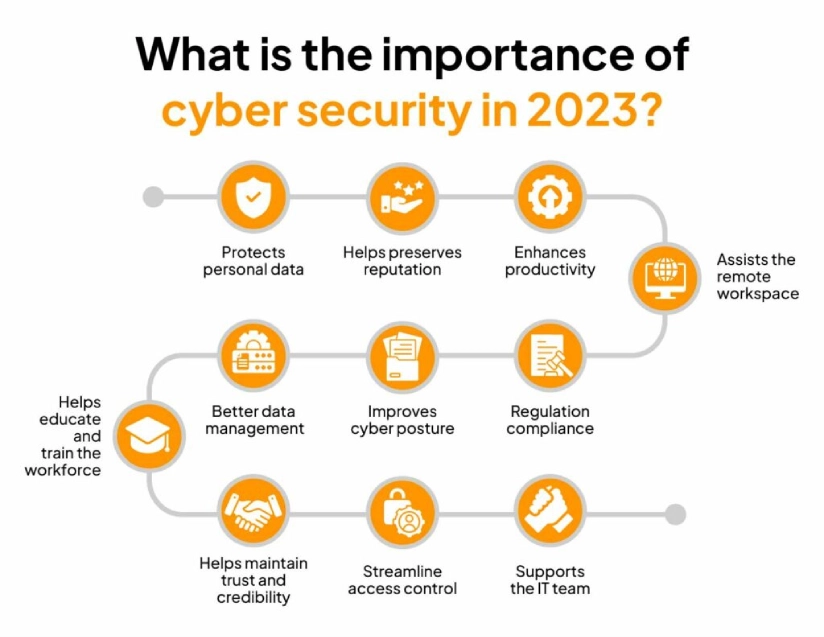
Here are the 11 key advantages of cyber security for businesses:
1. Assists the IT team
Cyber-attacks attract fines from regulators and customers’ claims, resulting in low sales and revenue, affecting crucial aspects of continuity. Additionally, cybercrimes can halt daily operations.
With the advancement of technology, sophisticated hacking practices have evolved. The IT team should stay up to date with the rapidly evolving changes in cyberspace.
A skilled IT team equipped with tools, techniques, and assistance, as well as comprehensive knowledge, can skillfully handle even the most advanced cybercrime.
Embracing advanced solutions like Sprinto offers Security Operation Centers a means to surmount these IT challenges. Sprinto’s automated workflows enhance the audit process by supporting multiple frameworks, streamlining assessments, and accelerating compliance timelines. By seamlessly mapping standard controls across diverse security frameworks, it cuts short your compliance journey from months to weeks.
See Sprinto in action. Talk to our experts today.
2. Safeguards personal data
Personal data is one of the most valuable assets for individuals as well as business owners. However, malware and viruses can access your personal information and may jeopardize employees, customers’ privacy, or organizations.
Cybersecurity protects data against internal as well external threats, whether accidental or with malicious intent helping employees access the internet as and when required without cyber attacks threats.
3. Boosts productivity
As technology evolves, cybercriminals are employing sophisticated ways to breach data.
Viruses negatively impact productivity by affecting networks, workflows, and functioning. The organization may come to a standstill due to the firm’s downtime. With measures such as automated backups and improved firewalls, firms can improve their productivity, making it one of the most promising cybersecurity benefits.
4. Maintains brand reputation
Customer retention and brand loyalty, for any organization, take years to build. The business reputation is severely damaged by data breaches. With a cyber security system in place, organizations can minimize unexpected breaches.
Technologies like network security and cloud security can strengthen access and authentication. This can open the pathway to future recommendations, ventures, and expansions.
5. Supports a remote workspace
The remote working model has led employees working from different locations to access multiple remote models for their workflows. It may be unsettling for organizations to circulate their sensitive data across the globe, where crimes against cyber and information security is able to occur through channels like personal devices, IoT devices, Bluetooth, WiFi, etc.
It is substantial for businesses to protect sensitive data as remote work has led to an increase in the average data breach cost by $137,000.
Sensitive data, strategies, and analytics are always vulnerable to being hacked and leaked. However, cyber security serves as a secure center to store data and can also protect home Wi-Fi from tracking users’ data.
6. Builds regulatory compliance
Regulatory bodies such as HIPAA, SOC, PCI DSS, and GDPR play a substantial role in protecting individual users and organizations. Failure to comply with these regulations attracts heavy penalties.
7. Improves data management
Data forms the crux of marketing and product strategies. Losing it to hackers or competitors may result in laying the groundwork from scratch, giving a competitive edge to other companies.
Hence, to ensure that data security regulations are implemented perfectly, organizations must consistently monitor their data. In addition to security, cybersecurity assists in operational efficiency as well.
8. Strengthens cyber security posture
Cybersecurity protects business data, secures digital services, and allows employees to use the internet safely. Online businesses must invest in secure, high-performance Magento hosting to maintain customer trust and protect sensitive information.
A sophisticated cybersecurity infrastructure monitors all systems in real-time through a unified dashboard with a single click. This strategic approach not only helps businesses mitigate security risks but also enables them to respond effectively to cyber-attacks with automation, ensuring smoother operations.
9. Sustains trustworthiness
Cyber security helps lay the foundation of trust and credibility amongst customers and investors. Breaches impact the reputation of an organization resulting in a dwindling audience base drastically. In contrast, the customer base increases when the organization has a history of safeguarding business and customer data.
10. Optimized access control
Organizations feel under control of all the tasks by controlling the internal and external processes.
Companies can focus on other meaningful tasks enabling them to establish accountability for strategic management. Access to systems, computers, and resources is streamlined, hence reducing cybercrime threats.
11. Provides training for employees
You can add a layer of safety to your organization’s daily operations by educating the workforce about potential risks such as ransomware, data breaches, spyware, and more.
The employees will be less vulnerable to phishing attacks and know the right course of action in case anything goes wrong. Also, check out: Cyber security compliance guide.
“Security is always going to cost you more if you delay things and try to do it later. The cost is not only from the money perspective but also from time and resource perspective“
Ayman Elsawah, vCISO, Sprinto
What are the disadvantages of cybersecurity?
While the benefits of cybersecurity are unparalleled, implementing it can be both costly and complex. There’s also a lack of skilled professionals which makes it challenging. Additionally, human errors make it difficult to achieve a robust security posture.

Regular updates
To counter sophisticated hacking practices that have evolved, organizations need to regularly update their hardware, software, and security strategy to be one step ahead of the attackers.
Needs continuous learning
The learning process is a continuous process as the threats are new and never-ending.
Complex to setup
For setting up security architectures and tools, specialized personnel needs to be employed as it is a complicated and time-consuming process.
Slower systems
Systems tend to become sluggish, as these security applications consume a lot of resources.
Constant monitoring
Real-time monitoring of the system and network is required to detect threats well in advance, enabling the security team to assess the threat level and have a cybersecurity strategy to counter the same.
Talent shortage
The number of qualified professionals is few compared to the requirements in the field of cyber security.
Expensive
Cyber Security is very expensive, requiring consistent learning and spending in a continuously ongoing fashion which can be a challenge for many small businesses.
5 most common cyber attacks
In recent years, several businesses and individuals have been the target of high-profile cyberattacks with devastating consequences. These can result in the theft of social security numbers, credit card information, bank account details, and sensitive data leaks. These attacks have helped organizations realize the importance of having strong cybersecurity measures in place.

The following are the most common types of cyber attacks that individuals and organizations fall prey to:
Malware
This refers to all harmful software such as viruses, trojans, and worms which is code or program written with the intention to damage a computer system. Malware is available in several types like viruses, worms, ransomware, spyware, adware, and Trojans.
- Viruses: Just like their biological counterparts, they reproduce themselves and spread them to other computers. They can corrupt files, steal data, or even render your computer non-functional.
- Worms: Like viruses, these can spread from one machine to another but do not have to attach themselves to other files. Fast spread can be based on vulnerabilities associated with software.
- Trojans: After installing these applications that pretend to be genuine ones, these will go ahead and steal your data while installing other malware or spoiling your machine.
- Ransomware: It encrypts your documents so they can’t be seen by you again. The attackers then demand a payment of ransoms in return for keys used in decryption.
- Spyware: This type of software steals your personal information including browsing history, login credentials, and financial data.
Phishing
These types of social engineering attacks often involve tricking victims into revealing their personal information. They usually send emails or text messages that appear to have come from a known source, such as the bank you are banking with or your card issuer.
The emails or texts may have a link that looks like an authentic website when clicked. When you enter your details on the fake site, they will be stolen by criminals.
Man-in-the-middle (MitM) attack
During this kind of attack, the perpetrator eavesdrops on your communication with another person such as your bank. In addition, he can steal your personal information.
Denial-of-service (DoS) attack
Cyber-attackers use this method to make a website unavailable or reduce its performance by flooding it with traffic.
Password attack
This is an attempt to determine someone’s password by using various combinations of letters, numbers, and characters. It is possible for attackers to check millions of passwords within just a few seconds using automated tools.
Must check: 16 Best Cybersecurity Tools
Upgrade your security game with Sprinto

Cyber security solutions are evolving as rapidly as cyber threats. The first step towards a cybersecurity strategy is to understand where you stand today with a cybersecurity audit.
Cyber security audits enable you to get an independent, comprehensive analysis of your current cyber security posture. It can identify vulnerabilities, mitigate the risk of attacks, expose weaknesses and high-risk practices, and continue to foster trust and confidence with your key investors and customers alike.
Sprinto is an automated security compliance software that helps you to achieve air-tight security provider and seamlessly integrates with any cloud setup. It runs compliance checks to consolidate risk and maps entity-level controls to manage all aspects of compliance from a single dashboard.
G2 has consecutively recognized Sprinto as a Leader in Security Compliance, where it was rated #1 in Usability, ROI, User Adoption, and Ease of Implementation.
Get in touch with us now to learn more.
FAQs
What are the 5 advantages of cyber security?
Companies must implement strong cybersecurity measures to protect themselves against breaches:
- Avoiding legal Fines and Penalties
- Maintaining Employee and Customer Trust
- Safeguarding Business Operations
- Better cybersecurity posture
- Protecting organizations against paying a ransom
- Staying ahead of the competition
What 3 things does cybersecurity protect?
Cyber security covers collective methods, processes, and technologies to help protect the confidentiality, availability, and integrity of computer systems, data, and networks, against unauthorized access or cyber-attacks.
What are the features of cyber security?
Key features of cyber security:
- Protection against external threats
- Safeguarding against internal threats
- Adherence to security regulations
- Utilization of cloud-based security offerings
- Detection, prevention, and response to threats
- Integration of comprehensive security solutions
- Effective security analysis
Author
Ayush Saxena
Ayush Saxena is a senior security and compliance writer. Ayush is fascinated by the world of hacking and cybersecurity. He specializes in curating the latest trends and emerging technologies in cybersecurity to provide relevant and actionable insights. You can find him hiking, travelling or listening to music in his free time.Explore more
research & insights curated to help you earn a seat at the table.