The Health Insurance Portability and Accountability Act (HIPAA) is a US federal law that mandates healthcare organizations, including their vendors, with access to PHI to implement standard best practices to protect patient data (such as medical records) and other personal health information.
This law extends to cloud-hosted tech firms that use software applications to process electronic Protected Health Information (ePHI), and hence, such companies must ensure their software is HIPAA compliant.
Any instance of non-compliance can come with severe repercussions ranging from severe financial penalties to legal trouble.
In this article, we dwell on how to make your healthcare application comply with HIPAA and, more importantly, why you need to do so. We’ll also discuss the best practices of being a HIPAA compliant software.
HIPAA Brass Tacks
Before we go any further, let’s quickly understand some important terms you need to know about HIPAA.
Protected Health Information (PHI): As per HIPAA regulations, PHI is 1) identifiable demographic or genetic information related to health, 2) information on the physical or mental condition of an individual, or 3) payment or financial information related to healthcare.
Covered Entities: Healthcare providers, health plans, and healthcare clearinghouses that conduct transactions electronically and generate, store, transmit and handle PHI. Business Associate: Service providers, vendors, and entities that work on behalf of HIPAA-covered entities that involve the use or disclosure of PHI.
What is HIPAA-compliant software?
A HIPAA-compliant software is a software that has been designed to meet the requirements of the Health Insurance Portability and Accountability Act (HIPAA), ensuring the protection of Protected Health Information (PHI). It incorporates security and privacy controls, such as data encryption, access controls, audit logs, and secure data transmission, to safeguard PHI from unauthorized access or breaches.
HIPAA-compliant software includes the following features to protect PHI and meet HIPAA’s Privacy, Security, and Breach Notification Rules:
Supports user training and documentation to promote compliance awareness.
Encrypts data at rest and in transit to prevent unauthorized access.
Implements role-based access controls to restrict PHI access to authorized users.
Maintains audit logs to track and monitor PHI access and modifications.
Ensures secure data transmission using protocols like TLS/SSL.
Enforces automatic logoff after inactivity to protect unattended sessions.
Provides backup and disaster recovery mechanisms to ensure data availability.
The main goal it aims to achieve is to talk about sensitive patient health data without the risk of exposing the chats to malicious actors or personnel who are not supposed to have access to the chat.
Note:
However, note that the term HIPAA compliant software is misused. Usually, the meaning behind the term is that software that is well adjusted to make you, your employees, and your company HIPAA compliant (like the example, HIPAA compliant chat).
Why do you need to be HIPAA compliant?
Any software that handles electronic Protected Health Information (ePHI) must adhere to HIPAA standards to ensure the confidentiality, integrity, and availability of that data. Failure to comply invites heavy regulatory penalties, reputational damage, and exposes sensitive patient information to exploitation.
Key reasons why HIPAA compliance is critical:
1. Legal Requirement: Software dealing with ePHI must comply with HIPAA—it’s enforced under federal law, not a best practice or industry guideline.
2. Severe Penalties for Non-Compliance: Organizations can face fines up to $1.5 million per violation per year, as well as civil and even criminal liability.
3. Rising Threat of Healthcare Data Breaches: Healthcare data is among the most targeted by cybercriminals and is often sold for fraud or identity theft.
4. Security and Privacy of PHI: The HIPAA Privacy and Security Rules set standards to protect identifiable health information, whether stored, transmitted, or accessed digitally.
5. Trust and Competitive Advantage: HIPAA-compliant software earns trust from providers, insurers, and patients, essential for adoption in the healthcare ecosystem.
6. Insurance and Cost Containment: Data breaches and fraud drive up insurance costs across the board. Securing PHI protects not only patients but the system as a whole.
If you want a handy checklist for quick reference, download it below:
Download Your HIPAA Certification Checklist
Certain organizations do not have to follow HIPAA rules, and do you fit into that group?
Many organizations hold data that falls under the category of PHI as defined by HIPAA. However, since they are not classified as covered entities under HIPAA, they are not mandated to comply with its regulations.
If you want to know whether your company falls under the purview of HIPAA, you need to answer the following questions:
- Who is the end user of your software application? Is it a Covered Entity or a Business Associate?
- What data will it handle? Will your software be privy to PHI in any form?
If your software doesn’t interact with PHI in any form, you needn’t worry about HIPAA compliance. But if it does, you must make all efforts to ensure you comply with HIPAA.
In HIPAA parlance, you are a Business Associate if you are a health tech firm that builds and sells software applications that will interact with PHI.
Aside from the mandatory requirement, following HIPAA compliant software requirements ensure you implement some of the global best practices in information security that dovetail with other compliance frameworks.
Fastrack HIPAA through automation. Speak to our experts
How to make your software HIPAA-compliant?
To make software HIPAA-compliant, implement robust security measures like data encryption, role-based access controls, and audit logging to protect Protected Health Information (PHI). Here’s a list of 11 things you must do to ensure you are on the right side of HIPAA:
1. Evaluate risks based on the type of data
You must first understand the type of data your software application will be privy to and list the potential risks against them. Know that risk assessment must be an exhaustive audit of all the risks that can impact the confidentiality, integrity, and availability of ePHI in your environment.
Conduct the risk assessment diligently as it lays the foundation for identifying and implementing security controls and safeguards that comply with the HIPAA Security Rule standards.
A thorough risk analysis should help you assess whether the controls you have implemented are reasonable and appropriate. Training employees on HIPAA is one security measure you must implement.

A. Collect data: Identify how the PHI enters your Business Environments (BE), where it is stored, and to whom it is transmitted. Identify and document possible threats that can result in unauthorized access or leakage.
B. Assess existing security measures: Assess and document existing security infrastructure. Ensure that those get configured or implemented correctly.
C. Determine the impact of threat: Analyze how critical the risks are to the PHI in your HIPAA compliant software. Using qualitative or quantitative methods, measure the potential impact on your business in case of a data breach.
D. Determine the risk level: Assign a level of risk for each security gap. You can do this by assigning a number based on how damaging the impact could be.
E. Finalize document: Document the result of your risk assessment. No specific format is defined for this. The idea is to compare historical data and create a log of the same.
F. Evaluate continuously: Risk assessment is a continuous process. HIPAA Security Rule doesn’t specify how frequently you should do it, as this depends on the covered entity. For instance, the type of risk your solution faces could change when you deploy a new technology to develop the application, face a security incident, or replace key individuals responsible for maintaining compliance.
Did you know that Business Associates must conduct risk assessments periodically (typically once a year)? Failure to do so can attract fines from the Office for Civil Rights (OCR) for noncompliance, and penalties can range from $100 to $50,000 per violation up to a maximum of $1.5 million per year for each violation.
The Sprinto way:
Sprinto introduces a fully integrated risk assessment feature within its platform. It intelligently identifies and maps out your organization’s risks, allowing you to select the appropriate risk assessment measures.
Your identified risks are seamlessly integrated into the system, requiring only minor adjustments to align with your organization’s specifics. Also, Sprinto provides industry-specific risk parameters to guide your risk assessment process in HIPAA further.
Related: A Comprehensive HIPAA Compliance Checklist
2. Secure ePHI data on servers
The server (on-prem or cloud) you store your ePHI must also be HIPAA compliant. You must sign a Business Associate Agreement (BAA) with them to ensure that. Typically, large cloud storage servers such as AWS, Google Cloud Platform, or Microsoft Azure offer HIPAA-compliant servers for data storage.
HIPAA encourages data minimization as a security best practice. So, ensure you only collect data that are an absolute must for the smooth running of your application and nothing more.
2. Encrypt data to avoid data breaches
While the HIPAA Security Rule doesn’t mandate encryption, it’s good security practice to implement one when dealing with ePHI. Even so, your risk assessment should help you determine whether you need one.
That said, even if the risk assessment doesn’t conclude using encryption as an appropriate risk mitigation measure, here’s some food for thought. If there is a potential breach, the onus of explaining your decision to the OCR of why you didn’t use encryption falls on you.
When you use encryption, remember to do so for data-at-rest as well as in transit. Store your decryption tools at a separate location per NIST standards. You can also consider Advanced Encryption Standard (AES) to protect online data transfer and Transport Layer Security (TLS) to transfer data via HTTPS safely.
Sprinto Advantage
To steer clear of data breaches, you need to follow the recommended HIPAA controls outlined in the HIPAA Security Rule. These controls cover administrative, physical, and technical safeguards, helping you beef up your cybersecurity to protect sensitive health information.
However, you must team up with a HIPAA compliance advisor for efficiency, and this can be expensive. This is where Sprinto comes in; it helps you simplify the control implementation process. With Sprinto you maximize the value of your investment in being a HIPAA-compliant medical software at multiple levels.
Sprinto helps you monitor internal and external security risks related to HIPAA controls with ease. Its intuitive dashboard notifies you of any anomalies in your system and helps you to minimize these risks with the help of HIPAA subject matter experts who will guide you every step of the way.
4. Backup data and implement disaster recovery
The HIPAA Security Rule lays out guidelines on data backup and disaster recovery. You must institute a policy for the same. The policy should account for when, where, and how often to back up the PHI your software interacts with.
Your data backup policy must also dwell on how to retrieve and maintain ePHI in its original form if an incident occurs (breach, theft, neglect, and more). You must also have a disaster recovery plan outlining what needs to be done during an incident.
To stay compliant, here are some measures you can implement.
- Back up data as frequently as needed: You can automate this task or enable privileged access to handle it manually.
- Create multiple backup copies in encrypted form: Use robust encryption systems like AES-256 and enable two-factor authentication for additional security.
- Facilitate real-time auditing solution: Implement real-time monitoring of backed-up data, continuously test the restoration processes, and track changes made to PHI to identify unauthorized access and audit event logs based on user roles.
- Create a disaster management feature: To limit the business risks in case of a mishap, create a recovery process for business continuity in case of a disaster, and determine which systems to restore first.
5. Dispose of old data
You must have procedures to dispose of ePHI permanently such that it isn’t recoverable or accessible to the public. Your software must include the feature to dispose of old data when needed safely.
- Encrypt the data before deleting it to prevent its decryption
- Overwrite sensitive data with non-sensitive ones
- Exposes the data to strong magnetic fields to destroy the recorded data
Ensure data deletion happens across all devices and in all forms (physical, electronic, and backup).
6. Provide authorized access only
Your software must implement access management to limit the access of PHI to only those authorized to see or use it. Maintain activity logs to identify unauthorized access or attempts.
Some of the best practices that you should incorporate into your application are

Sprinto advantage:
Traditional access management methods are inefficient, expensive, and prone to human error. While prioritizing convenience over compliance may seem tempting to maintain productivity, you’ll definitely face the brunt later on in the form of increased risks, security vulnerabilities, and potential audit failures.
Sprinto offers access management that’s easy to track and helps you implement zero-trust security while you ensure HIPAA compliance. It automatically assigns users to critical systems and adapts access policies based on factors like roles, reducing the likelihood of unauthorized access.
Sprinto also monitors role changes and alerts you to any irregularities. This way, you can enhance your security and compliance.
Interested? Speak to our experts to know more about how Sprinto can automate your HIPAA compliance.
7. Authenticate user accounts
User authentication ensures that only authorized users gain access to the ePHI in your environment by preventing unauthorized users from gaining access. User authentication checks for the identity of a user trying to access your software or sections.
You could consider any of the following based on the risks identified for the ePHI in your system:
- Password-based authentication
- Multi-factor authentication
- Certificate-based authentication
- Biometric authentication
- Token-based authentication
In the past few years, companies like Adobe, Equifax, and Yahoo have suffered significant data breaches because they failed to secure user authentication processes.
8. Ensure integrity and audit
HIPAA-compliant software must incorporate technical and administrative safeguards to ensure ePHI integrity, such as access control, MFA, encryption, and more.
The software must also enable covered entities to track and audit the activities in the system that are exposed to ePHI to protect it from unauthorized access or attempts.
Integrity controls prevent improper ePHI alteration or deletion. Audit controls reduce the risk of inappropriate access, unauthorized tracking, and disclosure of PHI.
9. Implement the right security policies
Having HIPAA-compliant software doesn’t guarantee compliance. It is up to the users to ensure the software gets used in a HIPAA-compliant manner.
Your Business Associate Agreement with the covered entities would list the security measures and protocols required of you to ensure the integrity, security, and confidentiality of PHI don’t get violated.
HIPAA mandates covered entities to only work with accountable business associates with whom they have signed agreements towards protecting PHI.
You must implement security policies as outlined in your BAA. Typically, these would include:
- 2FA or MFA
- Automatic session kills
- Encryption and decryption
- Intrusion detection
- Staff training on HIPAA
- Password security
10. Implement a remediation plan
You must have a remediation plan to address potential breaches and limit the damage they can cause. The remediation plan should help detect the cause and trigger an automated kill process.
It must put processes in place to solve the root issue(s) and implement mitigation solutions to get your operations back on track.
Also check out: A Complete Guide on HIPAA Certification
11. Implement continuous monitoring
Implementing continuous HIPAA compliance monitoring is simpler with Sprinto. It seamlessly connects entities and streamlines your compliance journey.
Get a consolidated view of security and privacy risks associated with HIPAA controls and robust mitigation strategies to minimize these risks.
What are the other benefits of Sprinto?
Sprinto also facilitates effortless assessment of your internal and vendor risks and helps create foolproof Business Associate Agreements to ensure compliance.
You can also offer security and privacy awareness training to your employees, so your teams can confidently tackle data breaches and security challenges.
Moreover,
- With Sprinto, you can avoid toggling between tools by streamlining evidence gathering through API-driven collection
- Real-time monitoring of systems enables proactive detection and mitigation of anomalies while receiving timely risk alerts to help stay ahead of potential issues
- You can track controls in a centralized location and ensure nothing slips through the cracks, thus avoiding costly penalties and ensuring the safety of ePHI
- Partner with a team of compliance experts to further enhance confidence in achieving HIPAA compliance through guided platform implementation
Case Study: How Happay boosted compliance efficiency with automated alerts and workflows
HIPAA rules for healthcare software
Every organization (and its employees) that works with PHI is supposed to be HIPAA compliant. And, healthcare software is no exception either.
Here are the five rules every healthcare software provider must adhere to as per HIPAA:
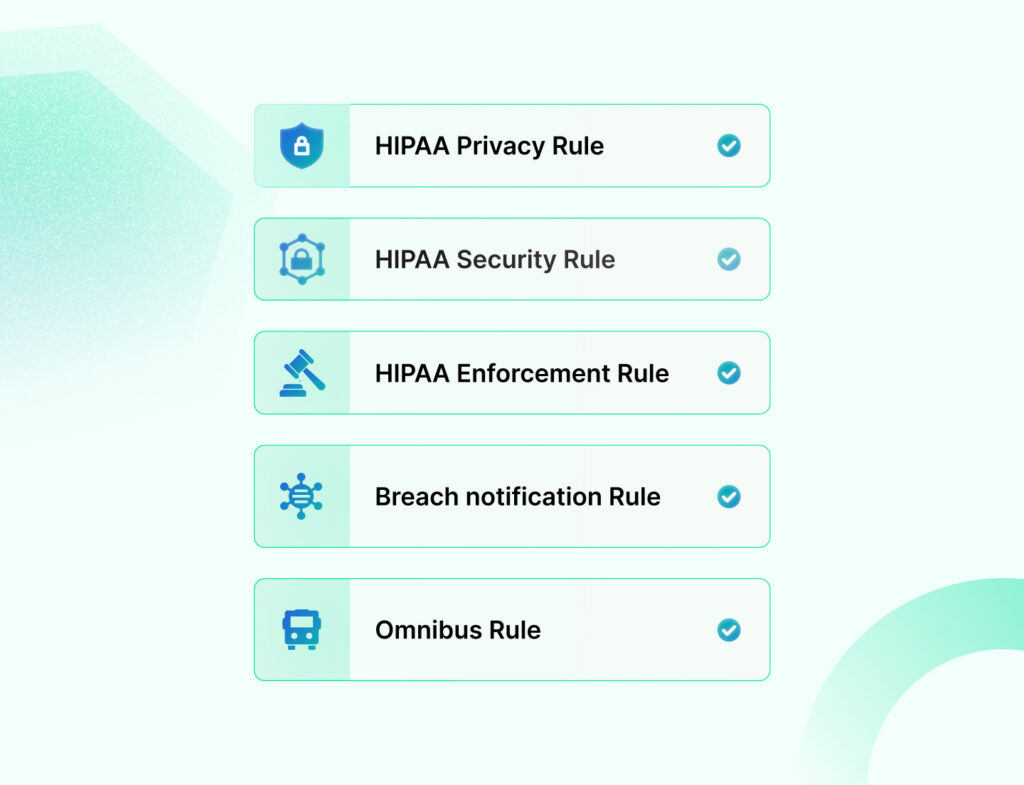
1. HIPAA Privacy Rule
By law, the HIPAA Privacy Rule applies only to covered entities, and most of the Privacy Rule provisions don’t directly apply to Business Associates.
But as a Business Associate, you would still be liable to protect the privacy of PHI in your environment as outlined in your BAA with the covered entity.
HIPAA Privacy Rule gives individuals certain rights over their medical information, such as the right to access data, make corrections, and file complaints if data is misused or shared without consent.
As a Business Associate, you must understand the Privacy Rule requirements and apply it to your healthcare software. You must also be aware of any additional limitations the covered entity may have imposed on itself through its notice of privacy practices or agreements with individuals.
Typically, these get covered in the BAA.
2. HIPAA Security Rule
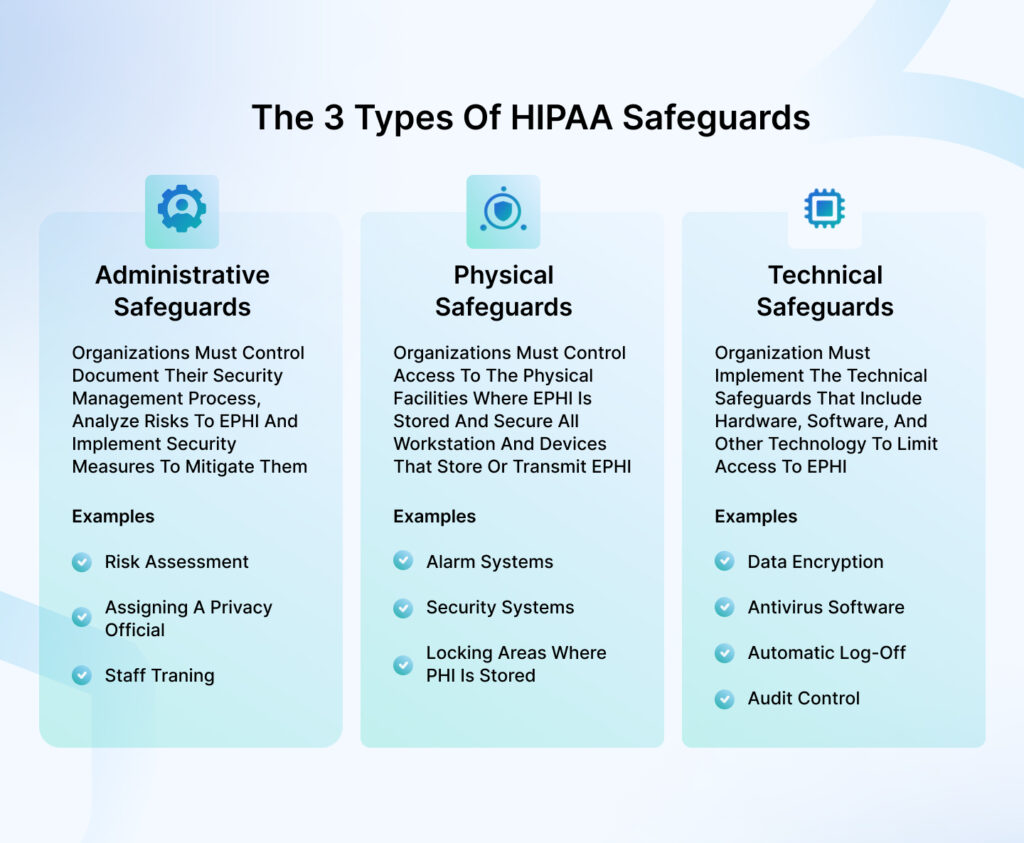
If the HIPAA Privacy Rule deals with PHI, the HIPAA Security Rule deals with ePHI. Broadly speaking, the Security Rule requires a Business Associate to implement three types of safeguards to adhere to the HIPAA compliant software requirements.
- Technical safeguards are policies and procedures that ensure sufficient access control, integrity controls, and security for data transmission
- Administrative safeguards entail organizations documenting their security management process, analyzing risks to ePHI, and implementing security measures to mitigate the risks
- Physical safeguards are related to measures and policies that protect PHI on electronic devices, systems, equipment, workstations, and buildings
3. HIPAA Enforcement Rule
HIPAA Enforcement Rule establishes the directives for compliance, investigation, and penalties for HIPAA violations.
It details the procedures and monetary fines for imposing civil penalties based on the investigation conducted by the OCR to determine if the Covered Entity or the Business Associate complies with the HIPAA compliant software requirements.
OCR-led investigations typically get triggered due to a complaint or a data breach.
Effortless HIPAA compliance round the clock. Speak to our experts
4. Breach Notification Rule
HIPAA Breach Notification Rule requires Business Associates to notify of a PHI breach within 60 days of becoming aware of the breach.
The notice must include all the details the covered entity needs for breach reporting, such as a comprehensive description of the breach, the type of data compromised, measures the affected individuals should take, and more.
That said, look for specifics on this in your BAA. Covered Entities may require a faster notification of a breach and could incorporate the same in your BAA.
5. Omnibus Rule
The HIPAA Omnibus Rule updates the previously passed HIPAA rules on Security, Privacy, Enforcement, and Breach Notification.
It comprises changes concerning Business Associates and their subcontractor liability and makes them more accountable for PHI use, disclosure, and security.
Business Associates and their subcontractors are liable to face HIPAA enforcement actions following violations of the HIPAA Security Rule and specific provisions of the Privacy and Breach Notification Rules.
As a Business Associate, you are liable for the following:
- Impermissible uses and disclosures of PHI
- Failure to comply with HIPAA Security Rule
- Failure to provide access to PHI to the Covered Entity
- Failure to provide an accounting of disclosures
- Failure to provide Breach Notification to the Covered Entity
- Failure to enter into BAAs with subcontractors that create or receive PHI
- Failure to take reasonable steps to address a material breach of BAA by subcontractors
- Failure to make reasonable efforts to limit the request, use, or disclosure of PHI to the minimum necessary
- Failure to disclose a copy of ePHI to the covered entity, the individual, or the individual’s designee to enable the covered entity to comply with the patient’s right to access
- Retaliating against individuals for filing a HIPAA complaint, participating in an investigation
- Failure to disclose to the Department of Health and Human Services (HHS) as required
- Civil Money Penalties for HIPAA violations
The problem with managing HIPAA manually for healthcare software is that it is prone to error and increased risk of non-compliance with data breaches. Also, managing the vulnerabilities and breaches becomes more difficult, and you may miss the 60-day HHS reporting deadline.
This is where Sprinto helps you navigate the compliance process and implement all the five rules mentioned above in your healthcare software.
In simple terms, Sprinto relieves you from the stress and exhaustion of navigating the complexities of HIPAA compliance. Once implemented, the secure platform provides you with a ready-to-go HIPAA compliance program.
This program is built on pre-established security and privacy controls, automated workflows, and continuous monitoring and evidence-collection features. These components collectively simplify the process of demonstrating and ensuring HIPAA compliance for your healthcare software, making it effortless for you.
Continuous HIPAA compliance made easy. Speak to our experts
How to become HIPAA compliant as a software company?
Your compliance efforts must include more than ensuring HIPAA compliance for software development. It would help if you made efforts to remain HIPAA-compliant post-development too.
Here are some critical measures you must implement to ensure continued compliance.
1. Regular audits
Regular audits help you track who, when, and from where PHI gets accessed. It’s a good practice to keep track of details like
- Use wise access to data
- How much and what data can they edit
- Record of which data got accessed, the date, and the device’s IP address
- Date updation and deletion details
You must record and review audit logs for consistent HIPAA compliance and safeguarding of all ePHI.
Compliance automation platforms such as Sprinto help you stay on top of all this by ensuring your audit trail is maintained and accessible in-app.
2. Plans for remediation
As mentioned earlier, a remediation plan can help you investigate breaches effectively and limit the damage. An auto-remediation program that can respond to several ‘what if’ scenarios can help here.
A comprehensive remediation plan will help you:
- Immediately remove all unauthorized access to PHI and change passwords
- Contact your compliance officer to help you take appropriate actions
- Investigate the breach in detail to understand the severity of the damage. Confirm details like who was affected and how much.
- Document your investigation and notify the affected parties
- Implement appropriate measures to avoid a similar incident in the future
3. Documentation processing
Like all compliances, HIPAA is heavy on documentation too. So, at every step, thoroughly document policies, procedures, incidents, and training modules.
The documents should be comprehensive, easy to understand, and well-structured. Remember, these documents serve as proof of compliance and accountability – if something isn’t documented, it implies it isn’t done.
4. Management of business relationships
To remain compliant, you must ensure that a BAA binds your vendors and subcontractors with access to PHI. You will likely have multiple BAAs signed with several Covered Entities.
Ensure you sign a BAA with Covered Entities only when you have access to PHI and fully understand the liabilities and obligations under the BAA.
5. Security
Aside from what’s already been covered, here are some other measures you can take to ensure the security of the PHI in your business processes.
- Log users out following a specific period of inactivity
- Push notifications or pop-ups should not contain PHI
- Role-based PHI access
- Intrusion detection
6. Access controls
Access controls refer to the rights and privileges granted to users for accessing and carrying out tasks using various systems, applications, programs, or files. These controls allow authorized users to access only the information required for their job responsibilities.
In the context of HIPAA-compliant software, it’s important to emphasize authentication methods. Implementing multi-factor authentication and automatic log-off features and encouraging the use of complex passwords are advised.
As mentioned above, Sprinto helps you simplify and automate critical systems access reviews at scale.
7. End-to-end encryption
End-to-end encryption is a must-have for HIPAA-compliant software, ensuring that PHI is encrypted when it’s stored. The industry standard is 256-bit AES encryption, so choose a solution that offers this level of security.
It also involves using encryption technologies like TLS version 1.2 or higher and IPsec VPNs to ensure that PHI is adequately protected while it’s being transmitted over a network.
8. Integrity
It’s essential to ensure that the data you collect, store, and share remains unchanged and protected from any unwanted alterations.
What you can do as a first step is to have a system in place that can quickly detect and report any unauthorized changes. In healthcare software development, this is achieved by digitally signing and verifying every piece of data using methods like PGP or SSL.
9. Physical storage security
Physical storage security is a key aspect of HIPAA-compliant software. You need to store data in a secure environment, and this involves considering where the data is physically stored.
To protect against unauthorized access, security measures like biometric authentication or other forms of authentication are essential for safeguarding servers. This helps prevent malicious actors from gaining physical access to the system and ensures the security of the stored data.
10. Disposal of data
Disposal is important in maintaining healthcare software and meeting HIPAA compliance requirements. Once data is backed up or archived, it needs to have an expiration date and be permanently disposed of. You need to have decryption keys as well.
However, do consider that any location where data is transmitted might also be making backups or copies. When you’re no longer using a server, properly dispose of the data to ensure its security and comply with HIPAA regulations.
11. Business Associate Agreement
The last element to being HIPAA-compliant software is where you host your ePHI. Remember to host it on servers provided by a company with whom a BAA is signed or on secure in-house servers.
We advise you to opt for cloud storage with reputable and trusted HIPAA-compliant providers such as Google Cloud Platform, Microsoft Azure, or Amazon Web Services, as they have robust security measures to safeguard.
12. Employee training
HIPAA training is necessary for employees of covered entities and their business associates. The Privacy Rule requires it and is an essential part of the Security Rule.
Luckily, Sprinto has made things easier for you by including a HIPAA security training module in its platform. When you choose Sprinto as your compliance platform, you can access updated security programs to educate and train your workforce.
How much does it cost to become a HIPAA-compliant software?
The cost of HIPAA-compliant software can start from $10000 and exceed $150000 depending on the nature and complexity of your company’s requirements. Keep in mind that several factors can affect the overall cost of achieving HIPAA compliance for your company.
Factors influencing the cost and complexity of achieving HIPAA compliance for software include:
| Size and type | The volume of patient data your healthcare software handles determines the security measures you need |
| Current compliance readiness | If your healthcare software already adheres to existing security frameworks and well-trained staff incur lower costs and effort to become HIPAA compliant |
| IT infrastructure | If you are maintaining up-to-date software and hardware. You will get compliant without incurring additional expenses |
| Employee training | Investing in staff training reduces the risk of security breaches and minimizes compliance-related costs |
| Approach to compliance | Opting for automated solutions like Sprinto will streamline the compliance process. It offers real-time monitoring and reduces overall costs. |
| Maintenance | Continuous monitoring and automation ensure ongoing compliance at minimal expense |
Note: The traditional manual and paperwork-based method for HIPAA compliance can lead to the violations mentioned earlier. Sprinto offers a solution by digitizing and automating the compliance process.
This helps your healthcare software achieve HIPAA compliance faster and enables you to maintain compliance over time. Companies using Sprinto to become HIPAA compliant can save up to 80% of their time, effort, and costs during the compliance process.
Save 80% of man hours spent on HIPAA. Speak to our experts
See how Sprinto guides you to achieve HIPAA compliance as a healthcare software provider
We understand it’s a lot to manage business growth on the one hand and ensure HIPAA compliance on the other. Sprinto is built to make complying with HIPAA effortless.
Sprinto enables you to adhere to the HIPAA rules, flag off alerts, train and track employee training, build security policies and ensure employee acknowledgment, maintain audit trails, and conduct annual risk assessments – from the comfort of its platform.
With minimal effort from your team, Sprinto automates evidence collection and documentation, ensuring repeatable tasks get done by themselves. Reviews of audit logs, compliance status, policies, and documentation can all be done within the Sprinto app.
Talk to us about how you can breeze through your HIPAA compliance.
FAQs
What is required for the software to be HIPAA compliant?
A lot of what is required for your software to be HIPAA compliant will be dictated by the Business Associate Agreement (BAA) you sign with the covered entities.
That said, based on the risk identified for the PHI in your environment, you can consider safeguards, such as data encryption, remediation plans, documentation, audit, and integrity controls, and MFA to protect the PHI and avoid penalties for noncompliance.
Why is it important that a software vendor understand HIPAA rules?
If your software interacts with PHI, it is essential to understand HIPAA rules and implement the required controls to protect PHI and avoid the financial and legal consequences of noncompliance.
Are apps subject to HIPAA?
If the healthcare app collects or maintains PHI data in any capacity, it is subject to HIPAA.
Are apps HIPAA compliant?
Even if your app initially collects only anonymous data not covered by HIPAA, if users decide to sharePHI with a doctor through your app, HIPAA compliance becomes necessary. Whether it’s an uncommon scenario or not, once PHI is involved, your app must adhere to HIPAA regulations.

Author
Srividhya Karthik
Srividhya Karthik, is a Content Lead at Sprinto, she artfully transforms the complex world of compliance into accessible and intriguing reads. Srividhya has half a decade of experience under her belt in the compliance world across frameworks such as SOC 2, ISO 27001, GDPR and more. She is a formidable authority in the domain and guides readers with expertise and clarity.Explore more
research & insights curated to help you earn a seat at the table.


























