The National Institute of Standards and Technology’s (NIST) Cybersecurity Framework (CSF) is one of the most helpful and adaptable frameworks for organizations looking to effectively manage cybersecurity risk. The framework is designed on the basis that it remains flexible and adaptable for companies of all sizes.
It brings policy, business processes, and technology within a single fold to identify, prioritize, and mitigate the impacts of cybersecurity risks.
There are three major components to NIST framework; core, profiles, and tiers. The tiers help your organization understand how well its cybersecurity practices align with its risk management strategies and goals. You can use the tiers to gauge your organization’s current state and make informed decisions about improving its cybersecurity posture.
In this article, we will take a deeper dive into NIST implementation tiers and how to align your security framework with them.
What are the NIST Cybersecurity Framework implementation tiers?
The NIST CSF implementation tiers describe how an organization sees cybersecurity risk and the processes in place to mitigate it. Tiers reflect an increasing degree of expertise in cyber risk management practices. They help in understanding how business requirements influence a company’s overall risk management procedures and cybersecurity risk management.
Although tier 1 organizations are urged to think about advancing to tier 2 or above, Tiers do not indicate maturity levels. Progression to higher tiers is recommended when a cost-benefit analysis (CBA) shows a viable and cost-effective decrease in cybersecurity risk.
Automate NIST compliance effortlessly
Why are NIST implementation tiers important?
The NIST implementation tiers seek to guarantee the security of essential IT infrastructure. The goal is to convince businesses to treat cybersecurity threats with the same level of importance as they do operational, financial, industrial, and human security issues.
NIST compliance is required for every business doing business with the US government. This covers U.S. government organizations as well as businesses and people that the government may employ to carry out project work. Since implementation tiers are essential components of the framework, they hold significant value in this regard.
List of NIST implementation tiers
NIST implementation tiers are unique to every organization. Narrowing down on the right implementation tier depends largely on its security posture, risk management processes, maturity of the risk management program, and the extent of external participation. Primarily, there are four tiers as explained below:
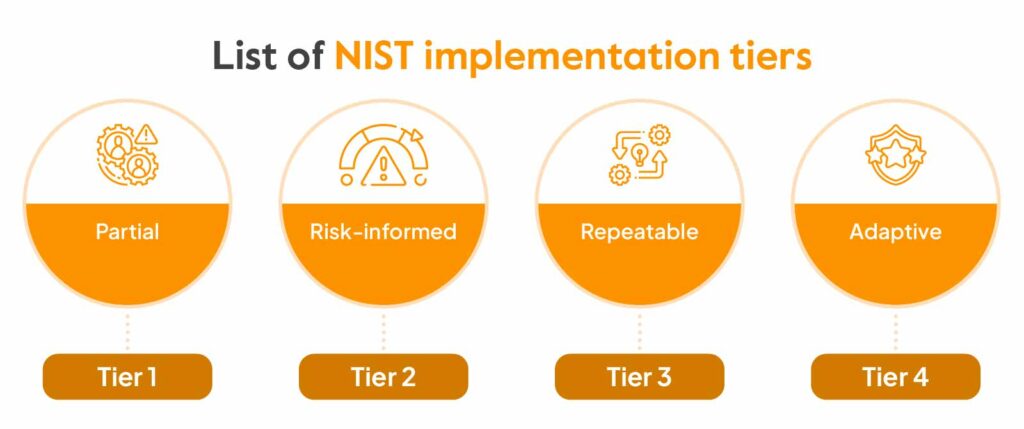
Tier 1 – Partial
This tier includes companies with on-demand or no security procedures. Businesses in Tier 1 are categorized as having very little awareness of cybersecurity risk. They frequently fail to prioritize cybersecurity measures properly.
Companies at this level must take steps to comprehend and effectively handle cybersecurity concerns. Tier 1 applies to your organization if you lack the time to commit to risk management processes, staff, or financial resources to implement a security program.
Tier 2 – Risk-informed
The majority of corporate executives are now aware of the main threats they face, including malware, state-sponsored attacks, and other bad actors. Additionally, they most likely have policies in place to stay safe against and mitigating such risks. Although tier 2 organizations have a fair amount of knowledge, they often lack a coordinated strategy and uniform departmental rules.
Similarly, they could also be aware of the threats to their supply chains and assets, but they lack the authority to take effective governance measures to address such threats.
Tier 3 – Repeatable
The third tier is for companies with risk management and cybersecurity best practices that have received executive approval. Businesses in this category are often more equipped to deal with vulnerabilities, cybersecurity risks, and threats.
Businesses in tier 3 devote more effort to measuring themselves against their competitors and working together with other businesses in their sector to guarantee best practice alignment.
Tier 4 – Adaptive
The topmost tier requires the greatest time and money to deploy, but it is essential in heavily regulated industries like banking, healthcare, and critical infrastructure. High-tech solutions are incorporated into adaptive information security, such as security incident and event management (SIEM), adaptive policies and procedures, and machine learning-powered detection and response capabilities.
These organizations contribute to the community’s broader awareness of risks by acknowledging their function, dependencies, and dependents within the larger ecosystem.
Also, check out a complete guide to NIST compliance
Get A Real Time View Of Risk
Functions related to implementation tiers
Apart from implementation tiers, there are two other major components of the NIST framework— Core and Profiles.
NIST framework Core:
The NIST Cybersecurity Framework core comprises functions, categories, subcategories, and useful informative references.
Functions provide an organization with an overview of best practices and safety measures to help it manage cybersecurity risk. This is done by organizing information, simplifying risk management actions, mitigating threats, and learning from past experiences.
A function is further divided into categories, which is a collection of cybersecurity outcomes tightly related to programming requirements and activities. A few examples of categories are detection processes, asset management, identity management and access control.
A category is further divided into subcategories or outcomes that stem from managerial and/or technical activities. While not exhaustive, they offer a collection of findings supporting the accomplishment of each category’s objectives. Examples of subcategories are checklist items that cover devices within the organization and external data systems.
Informative references are guidelines that explain ways to accomplish the objectives outlined in each subcategory.
Here are the key functions of NIST CSF core:
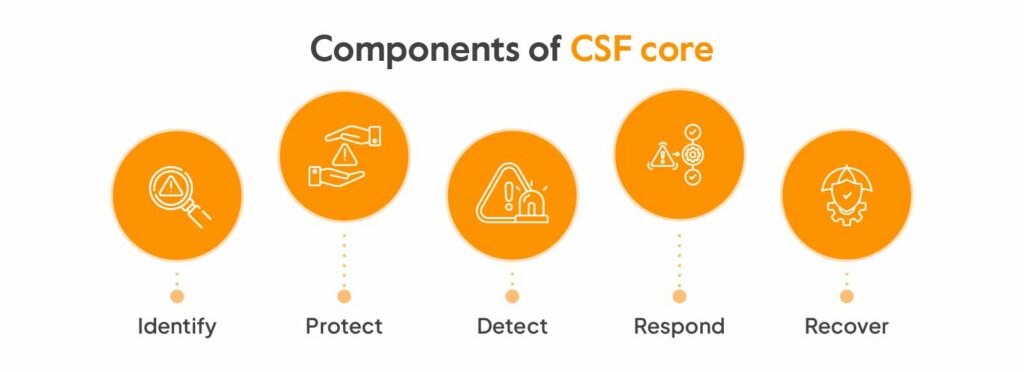
Identify:
The objective of the ‘Identify’ function is to build an organizational understanding of cybersecurity risk, which can affect people, assets, and capabilities, and its management. As a result, it’s easier for an organization to concentrate and structure its philosophy, thought process, and efforts in accordance with its risk management plan and operational requirements.
This function is divided into six categories—asset management, business environment, governance, risk assessment, risk management strategy, and supply chain risk management.
Protect:
The ‘Protect’ function covers most of the technological and physical security controls for creating and executing suitable safeguards and defending critical infrastructure. It lays emphasis on the ability to minimize or mitigate the effect of a possible cybersecurity incident.
This function is divided into six categories—identity management and access control, awareness and training, data security, information protection processes and procedures, maintenance, and protective technology.
Detect:
The ‘Detect’ function puts into place safeguards that warn a company of cyberattacks. It also involves monitoring your security systems and environments at frequent intervals to ensure faster detection of threats.
This function is divided into three categories—anomalies and events, security continuous monitoring, and detection processes.
Respond:
The ‘Respond’ function ensures that organizations respond to cyberattacks and security events sufficiently. Developing incident response and mitigation strategies are critical steps in implementing the ‘Respond’ function and requires a significant understanding of mitigation strategy and protocol.
This function is divided into five categories—response planning, communications, analysis, mitigation, and improvements.
Recover:
The ‘Recover’ function defines the best course of action to restore normalcy and regain any functionality that was lost as a result of a cybersecurity incident. The ‘Recover’ function starts once response and mitigation is complete and concludes when the effects of a cybersecurity incident die down completely.
This function is divided into three categories—recovery planning, administering improvements based on the reviews of existing strategies, and communications.
NIST framework profiles:

Profiles are the specific ways in which organizations align their organizational needs, goals, risk tolerance, and resources to produce the results specified in the Framework Core. By juxtaposing a “Current” profile with a “Target” profile, it becomes easy to find areas that need strengthening. Implementing profiles can also pinpoint weaknesses at the evaluation stage, and ensure they are addressed sufficiently. The most important thing to keep in mind while using profiles is optimization.
How do you align your business as per these tiers?
If you want to align your company with the NIST implementation tiers, you will need a methodical approach to improving your cybersecurity posture.
Here is a broad road map to assist you in aligning your company with these tiers:
- Scope: Establish business goals, risk tolerance, and cybersecurity priorities for your organization. Specifying scope helps you define objectives, understand the overarching scope of the exercise, and chart a course to achieve them.
- Gap analysis: Perform a thorough gap analysis to find discrepancies between your present cybersecurity practices and the desired profile. Doing a detailed gap analysis helps provide clarity on the areas that need attention while enabling you to allocate resources, assess risk, and improve incident response.
- Evaluation: Determine which NIST implementation tier best matches your organization’s current situation by evaluating where it stands in terms of cybersecurity posture. Positioning yourself in the right tier is crucial to understanding the level of maturity of your security posture and what needs to be done to reach the next tier.
- Adaptation: Create a cybersecurity profile by adopting the NIST Cybersecurity Framework’s functions, categories, and subcategories that best suit your organization’s requirements. Making adaptations to your existing processes and aligning them with the NIST framework ensures a high level of risk effectiveness.
- Action plan: Make a thorough action plan that specifies the activities necessary to close the identified gaps. Double down on these activities by implementing necessary changes and ensure you have the right policies and protocols in place.
- Training: Train key stakeholders on the NIST cybersecurity framework and its implementation tiers. Implement mandatory training sessions, learning exercises, role-specific training within their day-to-day.
- Progressing: It’s important to ensure your organization is moving up to higher implementation levels along with improving your cybersecurity practices. Once you have the necessary steps in place, identify initiatives that help you align your organization with the requirements from the next tier.
Aligning your organization to NIST implementation tiers is a bit more than what meets the eye. Implementing NIST manually to your workflow requires a lot of resources and money. This is where Sprinto plays a big part in minimizing the resources and costs. Sprinto enables automated evidence collection, gap analysis, risk management, and control monitoring, allowing you to level up your implementation tier seamlessly.
How can NIST tiers help you improve security?
NIST implementation tiers can help organizations by giving context for how they approach cybersecurity risk management. The tiers help organizations determine the amount of robustness that is necessary for their cybersecurity program. The tiers can be used as a communication tool to talk about the importance of the objective, risk tolerance, and budget.
Here are a few other ways NIST implementation tiers can help you improve security:
Evaluation and benchmarking
Organizations can evaluate their present cybersecurity procedures and compare themselves to accepted norms using the NIST tiers. Organizations can pinpoint areas where they need to improve by knowing their current tier.
Customization
The NIST implementation tiers are adaptable and enable organizations to tailor their cybersecurity strategies according to their specific requirements and risk profiles as well as their specific objectives and resources.
Risk management
Tiers and risk management are related. Organizations become more proficient in identifying, evaluating, and successfully mitigating cybersecurity threats as they advance through the tiers. This reduces the possibility and severity of cybersecurity incidents.
From a security standpoint, NIST CSF is designed to help you manage risks and identify where your risks are. And as a business driver, if your clients are in the critical infrastructure space, all of them are going to have some requirements around the NIST standards
Steve Siedeman, Director of innovation, Prescient security
Great advice adds up. Get more from the brightest minds in GRC — Subscribe to our newsletter
Sprinto’s take on NIST framework
NIST implementation tiers were designed in light of increasing cyberattacks. These tiers are a great measure of the required activities needed to strengthen the security posture of your company and, in turn, help you in better business operations.
A compliance automation platform like Sprinto can provide you with the necessary tools to help you tackle the challenges that come with implementing frameworks like NIST. The platform enables you to streamline compliance activities and automate key tasks like security checks, profile creation, and evidence collection without having to exhaust your resources.
Looking to take a step into the next NIST tier? Talk to our experts
FAQ’s
How often should your implementation tier be assessed?
Reassessments can be carried out on a regular basis or if there are substantial changes to the cybersecurity environment affecting your organization. Your cybersecurity plan will stay current and successful with regular reviews.
Can we skip tiers and move right up?
Although it is possible to significantly improve and move up a tier, it is typically advised to take a progressive approach. Each tier builds on the basis of the one before it, and moving forward incrementally helps to assure complete cybersecurity maturity.
Are security controls included in NIST implementation tiers?
The tiers do not specify any particular security controls, but they do offer broad information on how developed an organization’s cybersecurity practices are. More detailed advice is provided in this respect by the core functions and categories of the NIST Cybersecurity Framework.
Author
Shivam Jha
Shivam is our in house cybersecurity sage with over six years of experience in cybersecurity under his belt. He is passionate about making the digital world safer for everyone and whipping up Indian delicacies on the weekend.Explore more
research & insights curated to help you earn a seat at the table.