Companies today see the move to cyber risk management from the traditional risk avoidance approach as a strategic imperative. They are actively looking for methods to bypass the long-term costs of a security incident—loss of business, legal action and fines, etc.
Cyber risk management platforms have the risk intelligence needed to uncover advanced risks and assess likelihood and impact. They provide an understanding of various risk scenarios for CISOs which enables them to tighten cybersecurity controls. So if you are an organization looking to minimize the impact of security incidents, a cybersecurity risk management tool is something you must consider.
This article explores the best cyber risk management platforms, their key features, and other crucial details that can aid in your decision.
What is cyber risk management?
Cyber risk management is the structured process of identifying, evaluating, and addressing cybersecurity threats that could impact an organization’s digital assets, systems, or operations. It involves assessing existing security controls, identifying vulnerabilities, estimating the likelihood and impact of potential attacks, and implementing appropriate risk mitigation strategies – often using specialized cyber risk management platforms.
A cyber risk management platform is a digital solution that helps manage security risks by streamlining workflows, automating assessments, and helping gather reports pertaining to security controls that are passing or failing security parameters. The platform also assists compliance teams in ensuring adherence to regulatory frameworks and industry standards.
Why is cyber risk management important?
Cyber risk management is vital to safeguard sensitive information from theft, unauthorized access, and cyber attacks. Organizations bear a greater responsibility towards data protection, considering the increasing volume of sensitive data stored on the cloud. We live in the age of zero-day attacks and other advanced persistent threats contributing to rising security complexities.
Cyber risk management enables strong guidelines and protocols on how to identify, prioritize, prepare, communicate, and respond to security incidents. It also raises employee awareness on cyber security best practices and helps with compliance mandates.

The Top Cyber Risk Management Platforms
Shortlisting the right cyber risk management platform requires multiple rounds of research, feature analysis, and careful consideration of pros and cons. The breadth of functionalities must align with long-term cybersecurity strategies.
We have curated a list of what we think are the best cyber risk tools in the market and weighed their pros and cons to help you decide.
Here are seven leading platforms for cyber risk management.

Here are the top 7 Cyber Risk Management Platforms:
Sprinto
Sprinto is a cyber risk management and compliance automation platform that is purpose-built to provide centralized risk visibility and streamline compliance. It helps track risks granularly and identifies opportunities to strengthen organizational security.
Continuous control monitoring and integrated risk assessments help pinpoint gaps and generate real-time insights for improvement. The risk dashboard features a risk matrix that visually interprets the cyber risk exposure.
Other capabilities include:
Risk library: Sprinto’s risk register/library has a list of risk categories to choose from and add as per applicability quickly. The categories range from control health, infrastructure risks, endpoint risks to data security and access control risks.
Automated quantitative risk assessments: The risk dashboard provides industry-benchmarked risk likelihood and impact scores. This quantitative risk assessment method is widely accepted and scalable across frameworks like ISO 27001 and PCI DSS.
Remediation steps and how-to-fix guides: The mitigation plans showcase proactive steps that are available as a pre-populated list on Sprinto. There are also ‘how-to-fix’ guides for corrective actions that need to be initiated outside the platform.
Bird’s eye view of risk profiles: The platform facilitates quick and easy management review of risk assessment processes by providing a quick snapshot of risk profiles. This enables swift identification of high-risk areas for focused next steps.
Automated evidence collection: As organizations implement controls for risk reduction, evidence is automatically collected by Sprinto. It is also presented to the auditor on an independent audit dashboard in an audit-friendly manner for easy interpretation.
Vendor risk management: The platform helps maintain a list of all vendors and calculates vendor risk based on the data access type. Vendor due diligence and risk assessment reports can also be managed centrally through the dashboard.
While these features highlight how Sprinto effectively manages cyber risks, the platform’s capabilities extend beyond this. Sprinto has roles-based access controls, vulnerability and incident management modules, pre-built policy templates, endpoint device management capabilities and other security solutions

Explore Sprinto features here.
Pros
- 100+ integration options with other platforms
- Sprinto automatically suggests which systems should be a part of the critical systems list for risk management
- Ability to mark assets as production/non-production for an efficient scoping exercise
Cons
- Frequent updates and UI changes
- In case of third-party dependency, the implementation timeline can be disrupted
ZenGRC
ZenGRC is a cybersecurity risk management solution offered by RiskOptics (previously Reciprocity) that helps streamline risk and compliance management. The platform is also called ROAR because it aids with Risk Observation, Assessment, and Remediation, enabling businesses to make risk-informed decisions.
Features
Consolidated view of risk and compliance: The platform provides a single pane of glass to view high-risk items impacting business and adherence to frameworks. This helps with comprehensive reporting and better insights.
Real-time risk scores: The platform has various optics that provide details of risks over time, the percentage of risk mitigated, and the current financial exposure of the business. This provides real-time visibility and helps initiate quick actions.
Third-party risk assessments: ZenGRC also provides risk scores for third-party service providers and clarifies the impact of risk on business. This helps in managing a wide range of risks related to external partnerships.
Automated evidence collection: The tool supports integrations with various cloud providers, HR, CRM systems, and more to collect evidence automatically. The evidence can also be reused for different frameworks.
Operational reports: The solution helps communicate the impact of risk to various stakeholders by providing audit reports, summaries for board members, and other tactical reports. These reports quantify the risk impact for actionable insights and better understanding.
Pros
- User-friendly and flexible tool with a range of customizable attributes
- Risk and control mapping to multiple frameworks
- Responsive support team
Cons
- Limited reporting and visualization capabilities
- Documentation and UI uses product-specific technical jargon
- Bulk actions require manual intervention
Cura Enterprise Risk Management
Cura provides a range of solutions for managing enterprise risks, business continuity risks, and incident management. These solutions can be availed as standalone applications or can be integrated with GRC software to facilitate holistic management.
Features:
Supports multiple frameworks: The platform supports various risk management frameworks and standards like COSO, Sarbanes-Oxley, and more. It can adapt to the varying needs of all these regulations efficiently.
Integrated risk assessments: The solution helps identify various risks impacting business and provides a comprehensive view of risk profile. There’s real-time risk visibility that proves instrumental in decision-making.
Risk exposure analysis: CURA uses bowtie analysis (risk analysis methodology) and other analytic capabilities to give deeper insights into risk exposure.
Proactive alerts for remediation: The tool sends alerts for any tasks, actions, and escalations related to the risk environment. These involve alerts for control testing as well as initiating remediation measures.
Interactive dashboards and reporting: Visualization of reports and graphical assessments are supported for a quick and thorough understanding of risk events. The self-service dashboards provide the flexibility to create charts, graphs etc.
Pros
- Self-explanatory and easy-access tools
- The reports are visually interactive
- Continuous vulnerability assessment throughout the project lifecycle.
Cons
- Unclaimed profile and no reviews on G2
- The UI design feels bulky and information processing is slow
- Inefficient support
Resolver
Resolver is a governance, risk, and compliance management platform that helps interpret the business impact of risks across departments. The platform also provides insights into high-risk areas concerning regulatory compliance and streamlines the internal audit process.
Features
Consolidated risk registers: The platform supports consolidated risk registers with insights into various functions that carry risk. This facilitates smooth collaboration and communication across teams.
Streamlined risk assessments: Resolver sends automated alerts and notifications across teams for risk assessments and initiating remediation measures. This ensures proactive actions to minimize potential threats.
Built-in customizable best practices: The solution incorporates built-in best practices that serve as a baseline for implementation. It can also be tailored to suit every business’s unique approach and adaptability.
Visualization and user-friendly dashboards: Resolver provides the option to choose from various reporting styles, dashboard formats, and visualization options. This helps in presenting data in an easy-to-comprehend manner.
Vendor risk management: The vendor risk management solution helps understand the severity of risks posed by vendor relationships. This helps make critical decisions relating to such partnerships and reduces the actual business risk to acceptable levels by suggesting mitigation measures.
Pros
- The solution can be tailored to fit business needs
- It makes data collection and visualization fairly simple
- The employees can submit their observations freely with an anonymous portal
Cons
- The analytics function is hard to understand
- Limited product training material
- The dashboard encounters frequent technical glitches
LogicGate
LogicGate is a cloud-based risk and compliance management platform that helps businesses associate cyber risks with business impact. This provides context-rich information to make key business decisions and helps build resilient organizations.
Features
Automated risk assessments: The platform automates cyber risk assessments and helps tie the insights to the business context. This ensures well-planned response actions from key stakeholders.
Risk quantification: LogicGate features’ Risk cloud quantify’ to interpret risk into financial loss exposure and communicate the results in a manner that the teams understand. It uses Monte Carlo simulations (a mathematical technique) for enhanced risk analysis.
Near real-time insights: The solution provides up-to-the-minute insights on high-risk assets for deciding priorities. This helps initiate quick remediation actions and enhances incident preparedness.
Evidence collection: The cyber risk management tool automates the evidence collection process across different compliance frameworks. This facilitates easier management of risk and compliance programs.
Reporting dashboards: The reporting dashboards can be customized to align with business priorities. Risk is interpreted (qualitatively and quantitatively) for key business units to enhance stakeholder understanding.
Pros
- Flexibility to create visual reports
- Seamless creation and integration of risk acceptance forms into workflows
- Highly customizable dashboards with the option to download them in various formats
Cons
- The platform has a steep learning curve
- Any changes cannot be tested in a sandbox (isolated testing environment) before making them LIVE.
- No educational material for using customized solutions
StandardFusion
StandardFusion helps systematically navigate risk and compliance environment challenges to identify and treat risks while ensuring adherence. The cloud-based GRC application ensures organizations conform to industry best practices and build a security-first culture.
Features
Integrated threat library: The platform uses an integrated threat library to identify key risks that can impact high-priority assets. The risk registers feature these risks for quick tagging and tracking.
Built-in risk methodologies: The solution provides both quantitative and qualitative risk assessment methodology options. Businesses can also upload their calculations for a tailored experience.
Risk treatment: StandardFusion also enables establishing a relationship between risks and mitigation strategies and viewing them on heatmaps or reports. This mapping facilitates informed decision-making processes.
Analytics: Risk analytics help in understanding the evolving nature of risks over time. Any trends, patterns, correlations, etc. can be drawn to prepare the organization for future challenges.
Reporting: The platform supports reporting styles tailored to audience needs. Summaries can be generated for board-level reporting, and exhaustive reports can be downloaded for teams.
Pros
- Lets businesses upload custom guidelines for risk and compliance management
- Makes multiple standards tracking easier
- A good number of integration options with other tools are available
Cons
- Limited flexibility in reporting functionality
- Less intuitive UI
- Some key features (like SSO) are available only in the enterprise package
SureCloud
SureCloud is a cyber risk management and compliance governance platform that helps organizations streamline workflows. It automates various parts of risk identification and mitigation and tracks and manages regulatory adherence.
Features
Risk tracking and remediation: The cloud-based platform supports risk identification, assessment, and treatment activities. This is done through a collaborative approach that also fosters team collaboration.
Specialized workflows: The platform helps manage risks with streamlined workflows that can be configured as per business requirements. These workflows add a structured approach to the program and are time and cost-effective.
Centralized dashboards: The consolidated dashboards present data for risk exposures, remediation status, control weaknesses, and other relevant areas. This single source of truth is a quick snapshot of progress from risk and compliance efforts.
Built-in best practices: The solution features a library of best practices as an implementation baseline for IT teams. They can also quickly deploy preventive controls for achieving the desired security maturity.
Real-time reporting: The user-friendly real-time reporting dashboards make data interpretation easier. Stakeholders can quickly access the business’s risk exposure and compliance status at any given time.
Pros
- The assessment configurations can be customized
- Highly approachable customer support team
- Built-in templates for risk and third-party management are out-of-the-box
Cons
- The deployment process is time-consuming
- Delayed responsiveness in case of multiple task switching
- Limited integration options
How to select the right cyber risk management platform?
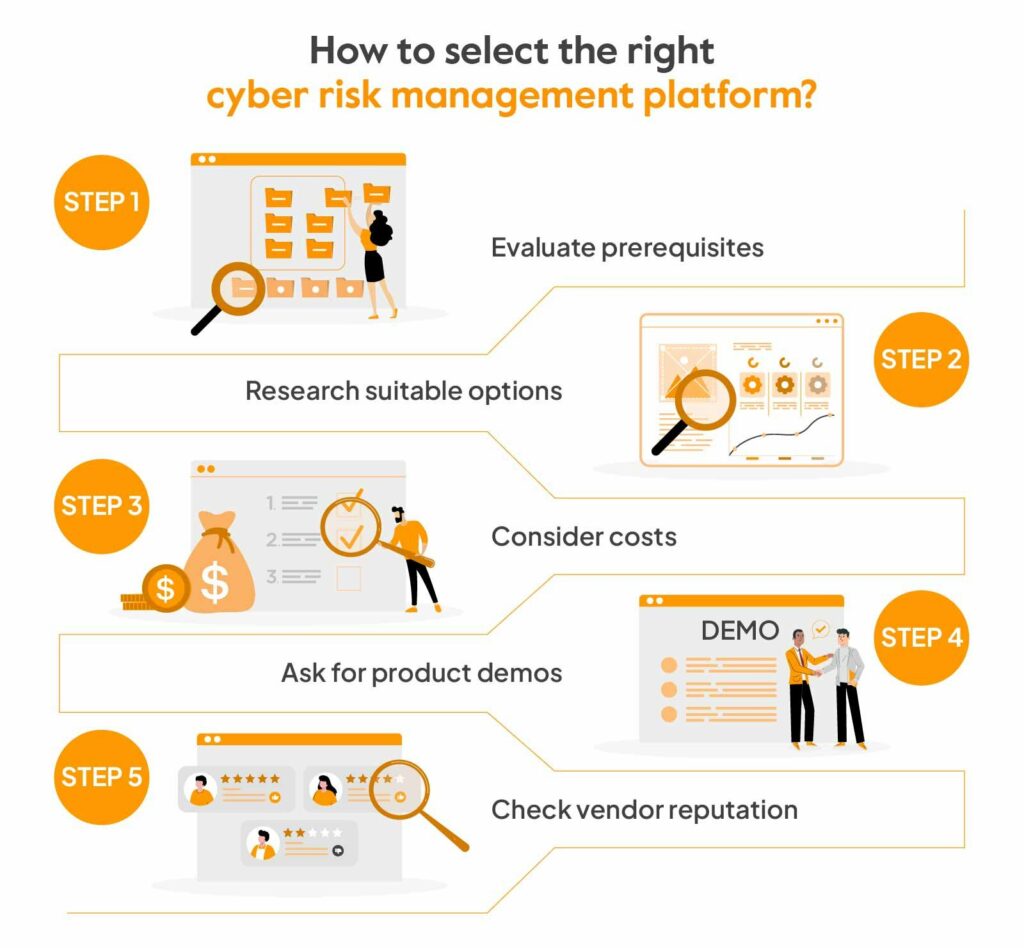
To choose the right cyber risk management platform for your business, start by bringing together internal stakeholders to identify key pain points and long-term risk goals. Focus on solutions that can scale, work well with your current systems, and meet your regulatory and operational needs. After that, check your shortlist using demos, trials, and peer input.
Consider usability, integration, and the level of support each vendor offers. The shortlisting conversation lands more cleanly when the team has agreed on which IT risk management frameworks the platform needs to align with, since that single decision narrows the field by half before any vendor demo gets booked.
Here are the exact steps for cybersecurity platform selection:
- Evaluate prerequisites
Make a list of critical systems and classify the protected data types. Next, assess the specific risk management goals of the business. These could be automating manually managed systems, ensuring regulatory compliance, addressing third-party supplier risks, etc.
- Research suitable options
Research cyber risk management tools that fit the business case and compare their capabilities. Good cyber risk management software need to be easy to use and flexible while being able to integrate with critical systems, automate assessments, and compile actionable reports. Among these capabilities, ongoing risk monitoring is the one most teams underestimate during selection, since the difference between a tool that fires alerts and one that builds a coherent risk picture only becomes visible after a few months of production use.
- Consider costs
Budgeting is a key consideration, so analyze the return on investment. Consider licensing fees, implementation costs, ongoing maintenance, and other relevant costs. Compare these with long-term benefits like cost-saving, scalability, and other future needs to make the right choice.
- Ask for product demos
Free trials and demos are great ways to validate ease of use and core functionalities. It is important to check for compatibility, performance, and speed and understand the training and support required for the team. If there are any pilot offers, exploring these can aid in a confident final decision.
- Check vendor reputation
Consider online reviews, testimonials, case studies, peer referrals, and other sources to evaluate whether they align with your expectations. Research whether vendors have experience with business use cases that suit yours and visit websites like G2 to understand the vendor’s expertise and weak points.
Manage cyber risks and compliance with Sprinto
Effective cyber risk management is vital to developing a security-mature organization and building long-term resilience. A cyber risk management platform like Sprinto takes the manual burden off this process by automating tasks, enhancing accuracy, and fostering greater collaboration.
Sprinto ensures that cyber risk management and security compliance works hand in hand. The platform streamlines the entire risk assessment and review cycle while automating vital processes.
Features like real-time control monitoring, centralized document management, workflow automation, and automated evidence collection make it a comprehensive solution for businesses looking for impenetrable security compliance as the default state.
FAQs
Cyber risk assessments should be conducted regularly based on the organization’s requirements. At the very least, annual assessments are recommended, along with when significant infrastructure changes occur.
Cyber risk management platforms help with risk assessments, gap identification, testing controls, report preparation, and evidence collection. They also support compliance efforts by integrating with other tools to track and alert security drifts and ensure adherence.
The cybersecurity risk management process involves identifying critical assets, assessing the risks involved, scoring the likelihood and impact, and suggesting mitigation measures. This is a cyclical process to ensure continued improvement.
Cyber risk management helps address threats like data breaches, ransomware attacks, insider threats, third-party risks, and misconfigurations. It ensures proactive detection and mitigation before these risks cause significant damage.
Cyber risk management is a cross-functional effort. While CISOs or security teams typically lead the process, it also involves IT, compliance, legal, and even department heads to ensure risks are identified and addressed across the business.
No single provider is best for every company. Strong regulator-ready platforms usually offer risk registers, control mapping, evidence trails, remediation tracking, executive reports, and audit-ready documentation. Platforms like Sprinto, ServiceNow IRM, Archer, MetricStream, and Hyperproof are commonly used depending on company size and regulatory needs.
Author
Payal Wadhwa
Payal is your friendly neighborhood compliance whiz who is also ISC2 certified! She turns perplexing compliance lingo into actionable advice about keeping your digital business safe and savvy. When she isn’t saving virtual worlds, she’s penning down poetic musings or lighting up local open mics. Cyber savvy by day, poet by night!Explore more
research & insights curated to help you earn a seat at the table.