TL;DR
| The most effective VRM tools enable organizations to systematically discover vendors, tier them based on actual exposure, execute thorough due diligence, and maintain an audit-ready decision trail. |
| Tools covered in the article: Sprinto, Vanta, UpGuard Vendor Risk, ProcessUnity, Venminder, Panorays, SecurityScorecard, BitSight, RiskRecon, OneTrust Third-Party Management, ServiceNow Vendor Risk Management, Archer |
| Treat audits and questionnaires as point‑in‑time artifacts; choose a tool that supports continuous oversight between review cycles. |
While it has become easier for your team to add new vendors to your stack, Vendor Risk Management has gotten equally harder. The quick adoption of AI tools and the rise of embedded AI capabilities in existing vendors have not helped either.Before long, you’re trying to answer basic questions like which vendors touch customer data, who approved them, and what they still have access to using spreadsheets, inbox archaeology, and tribal knowledge.
When your vendor risk process isn’t built for how work actually happens, the failure mode is predictable. Risks stay hidden too long, due diligence turns into guesswork, and you end up doing last-minute cleanup when an audit, renewal, customer security review, or incident puts you on the spot. The gaps usually appear in areas such as vendor discovery, authorization, and decision logging.
Vendor risk has become a never‑ending visibility problem. A win for your team is to reduce chaos and create defensible visibility, not perfection.
In this guide, I’ll share a list of 13 vendor risk management (VRM) tools and a practical buyer’s guide to help you pressure-test demos. Let’s begin by outlining the tools featured in the article, then move into the buyer’s framework.
12 best vendor risk management tools
VRM tools are software solutions that help you identify, assess, monitor, and reduce risks stemming from vendors, particularly those with access to sensitive systems or data. The terms VRM (Vendor Risk Management) and TPRM (Third-Party Risk Management) are often used interchangeably; VRM typically focuses on risks from IT and SaaS vendors, while TPRM may encompass a broader set of third-party relationships.
Now that you know what to look for before picking a tool, here are the vendor risk management solutions we’ll explore in the article:
| Tool | Best fit | Known for | Watch for |
| Sprinto | First-time, fast-growing, mid-market | Compliance automation and trust ops | Needs integrations and internal ownership to hit full value |
| Vanta | Fast-growing, mid-market | Compliance-led trust workflows that also cover vendor reviews | May feel prescriptive if you want deeply custom vendor lifecycle steps |
| UpGuard Vendor Risk | Fast-growing, mid-market | Monitoring-first posture visibility with assessments | Signals still need a workflow layer for approvals and exceptions |
| ProcessUnity | Mid-market, enterprise | Configurable workflows, reporting, and structured program design | Admin overhead can grow with customization |
| Venminder | Regulated orgs | Platform plus services for consistent due diligence | Platform changes can require support involvement |
| Panorays | Mid-market, enterprise | Automated questionnaires paired with continuous monitoring | Data accuracy disputes and vendor participation can slow outcomes |
| SecurityScorecard | High vendor counts | Cyber risk ratings and portfolio monitoring | False positives; often needs a workflow layer for governance |
| BitSight | High vendor counts | Ratings and outside-in monitoring with portfolio visibility | Scoring disputes and alert tuning needs can create friction |
| RiskRecon | High vendor counts | Monitoring and shareable vendor reporting | Often paired with a workflow tool for decisions and exceptions |
| OneTrust Third-Party Management | Enterprise | Broad governance ecosystem and configurable workflows | Reporting and alert fatigue show up in feedback |
| ServiceNow Vendor Risk Management | Enterprise ServiceNow shops | VRM inside the ServiceNow IRM ecosystem | Value increases with broader ServiceNow adoption |
| Archer | Mature enterprise IRM | Deep customization across multiple risk domains | Cost, complexity, slower time to value |
It’s worth saying out loud that spreadsheets aren’t dead. They’re still one of the fastest ways to slice data and build custom views. What breaks at scale isn’t the grid, it’s the workflow around it (ownership, reminders, evidence freshness, approvals, and a defensible decision trail). The right VRM tool should preserve the visibility you like about spreadsheets while removing the manual follow-up and audit panic.
How this list is organized: I’m starting with tools that tend to work well when you’re building your first repeatable VRM program, then moving toward platforms used for enterprise TPRM and IRM use cases.
1. Sprinto
Sprinto is an Autonomous Trust Platform. It centralizes trust obligations (such as regulations, policies, contracts, and vendor requirements) and automates recurring tasks to help you stay compliant and manage risks, including vendor risk, access, and privacy.
In a VRM context, it brings your vendor discovery, risk tiering, due diligence workflows, continuous monitoring, and audit-ready tracking into one place. With Sprinto AI, you can speed up reviews by validating vendor evidence and moving assessments forward with less back-and-forth.
Key features:
- Automated vendor discovery: Connect your systems to the platform to identify vendors automatically and map their access to sensitive data.
- Contextual risk scoring: Use AI to evaluate each vendor based on sensitivity, criticality, and exposure, producing a data-backed risk profile.
- AI-assisted due diligence: Sprinto AI scans vendor documents, highlights missing clauses or controls, and suggests follow-up questions to speed up vendor reviews.
- Smart evidence validation: Detect missing or outdated documents so stale evidence does not slip through.
- Continuous monitoring and reporting: Tracks vendor breaches, certification expiry, and control changes in real time, then generates inspection-ready reports for auditors and leadership.
- AI-powered questionnaires and trust workflows: Reduce back-and-forth by recommending questions and drafting responses from existing context.
Pros:
- Reviews often emphasize fast, hands-on support, reducing friction during onboarding and ongoing audits.
- Customers often describe Sprinto as a central system of record that reduces the need to chase information across tools and spreadsheets by consolidating tasks, evidence, and status into a single place.
- Reviews cite automation and integrations as time-savers for keeping evidence current and staying audit-ready without manual effort.
- Simple evidence uploads and reminders for when due diligence reviews are due.
- Several reviews suggest Sprinto can help bridge internal security expertise gaps by providing structured guidance and visibility into what needs to be done and when.
Cons:
- A few users mention that exports and reporting outputs can be less self-serve than they would like, including requests for cleaner CSV-style export options.
- Reviews note that some integrations may require more manual setup than expected, depending on your tooling stack.
- Could do with minor product polish; some users request a more modern UI experience.
Pricing: Quote-based (varies by scope and requirements).
Best for: If you are a fast-growing or mid-market team looking to run VRM as a repeatable workflow within a broader trust program, then Sprinto is a good fit. It helps discover vendors continuously, assess them in context, use AI to accelerate due diligence, and keep a decision trail you can defend later. It is especially great if you value strong implementation support as much as product capability.
“Having all our vendors in our IdP, the Sprinto platform makes it way easier to assess the risk of each vendor and make sure it’s all taken care of.”
~ Dragos D, IT Support Engineer (Company size: 51–200 employees)
2. Vanta
Vanta is best known for compliance automation and trust management, but it also appears in vendor risk conversations because it combines third-party risk workflows with the same evidence, monitoring, and trust artifacts. In a VRM context, Vanta positions its third-party risk management capabilities around AI-assisted security reviews, vendor questionnaires, and continuous monitoring, with a Trust Center to reduce repetitive exchanges during vendor assessments and customer security reviews.
Key features:
- AI-powered security reviews: Summarize and extract signals from vendor evidence to reduce manual reading time.
- Continuous monitoring: Move vendor review from point-in-time to ongoing oversight.
- Trust Center: Publish a structured trust hub to reduce repetitive back-and-forth during security reviews.
- Vendor questionnaires and tracking: Send questionnaires, track responses, and assess vendor risk in a centralized workflow.
- Integrations and evidence automation: Use integrations and automated evidence collection to reduce grunt work and keep compliance and risk posture visible.
Pros:
- Can help reduce tool sprawl by tightly linking vendor reviews to compliance and trust workflows.
- Trust Center can cut repeat requests for the same evidence, especially in sales-driven environments.
Cons:
- Pricing tends to scale with the scope of programs and modules.
- Some reviewers describe Vanta as prescriptive, with limited deep customization and a learning curve when tailoring policies, workflows, or non-standard requirements.
Pricing: Typically quote-based.
Best for: Fast-growing teams that already run compliance and trust work in Vanta and want vendor reviews to live in the same operational rhythm, especially when security questionnaires and evidence sharing are constant. It may not be ideal if you need highly bespoke vendor lifecycle workflows or want vendor management to include deeper coverage (contracts, renewals) without maintaining a second tool.
3. UpGuard Vendor Risk
UpGuard Vendor Risk is a third-party risk platform built around continuous monitoring and vendor assessments. From a VRM perspective, you may opt for a tool like that when you want faster visibility into vendor security posture changes, a structured way to run questionnaires, and a portfolio view that helps prioritize follow-ups without building a heavyweight IRM program.
Key features:
- Vendor security ratings and monitoring: Continuously evaluate vendor security posture using external signals and alerts you when posture changes.
- Questionnaires and assessments: Send vendor questionnaires and track completion so that due diligence is more structured than email threads.
- Attack surface discovery: Identify and monitor exposed internet-facing assets tied to vendors to support ongoing oversight.
- Remediation and risk acceptance workflows: Track findings, follow-ups, and risk waivers so exceptions are documented rather than buried in approvals.
- Reporting and portfolio views: Provide dashboards and reporting to summarize risk across many vendors for stakeholders.
Pros:
- Automation helps scale assessments as vendor count grows.
- Users frequently highlight fast setup and ease of use in public reviews, especially compared to more complex GRC suites.
- Reviews often mention helpful, responsive customer support.
- Users commonly value the combination of monitoring signals and assessment workflows, which helps keep vendor oversight from becoming purely annual and reactive.
Cons:
- Reviews consistently show that false positives and asset attribution issues can still require human verification, especially at scale.
- Users report friction in portfolio management, including issues with bulk actions and workflow inefficiencies when managing many vendors.
- Pricing is a recurring concern, especially for teams that want broader coverage without enterprise budgets.
- Some reviewers note gaps in certain integrations or the depth of findings, depending on the environment and the specific monitoring signals required.
Pricing: Publicly available information suggests that pricing for Vendor Risk plans starts at $1,599 per month (Starter, billed annually) and $3,333 per month (Professional, billed annually), with higher tiers typically sold via quote.
Best for: Fast-growing and mid-market teams that want vendor monitoring and assessments to scale with vendor sprawl, especially when the immediate need is visibility and prioritization. It’s best suited when you have enough internal process maturity to operationalize alerts into decisions and follow-ups, rather than treating monitoring as a passive dashboard.
4. ProcessUnity Third-Party Risk Management
ProcessUnity is a dedicated third-party risk management platform focused on building repeatable workflows: intake, tiering, assessments, evidence collection, monitoring, remediation, and reporting. From a VRM perspective, it is often considered when you want configurable workflows and dashboards, but within a platform purpose-built for vendor risk rather than a broad IRM suite.
Key features:
- Configurable vendor lifecycle workflows: Supports intake, routing, approvals, and reassessments that can be tailored by vendor tier and risk type.
- Vendor portal and questionnaires: Provide vendor-facing workflows for questionnaires, evidence uploads, and clarification cycles.
- Evidence and documentation management: Centralize documents and review artifacts to reduce ‘where is that SOC report’ churn.
- Issue management and remediation tracking: Track findings through to closure with owners, due dates, and audit history.
- Dashboards and analytics: Provide reporting views for risk leadership and operational teams, including program status and workload.
Pros
- Review analysis indicates strong appreciation for configurability, especially when organizations need workflows and questionnaires tuned to their environment.
- Users highlight dashboarding and analytics as a strong point, including visibility into program health and vendor status.
- Some reviewers describe the platform as supportive of scaling a structured program when vendor volume increases.
Cons
- Performance issues such as slowness or timeouts can become a real adoption blocker for both internal teams and vendors.
- Users often describe notification setup and workflow administration as cumbersome, sometimes requiring more admin involvement than expected.
- Customization power comes with a tradeoff: some reviewers imply that misconfiguration is costly to unwind and requires experienced admins.
Pricing: Pricing is typically quote-based and depends on scope, vendor count, and modules.
Best for: Mid-market and enterprise programs that need a configurable VRM engine and have the bandwidth to design and maintain the workflow. It is best suited if flexibility is high up on your priority list, but you want to get there without moving all the way to an enterprise IRM platform.
5. Venminder
Venminder is a VRM platform that combines software with optional services and frequently appears in regulated industries that require consistent due diligence execution and documentation hygiene. From a VRM perspective, you can use the platform to standardize vendor lifecycle oversight, track contracts and reviews, and support ongoing monitoring through platform capabilities and service support.
Key features
- Vendor lifecycle management: Supports onboarding, periodic reviews, renewals, and offboarding to ensure continuous vendor oversight.
- Questionnaires and due diligence workflows: Get structured workflows for collecting vendor responses and tracking review status.
- Document and evidence management: Centralize artifacts such as SOC reports, policies, and review outputs for audit readiness.
- Contract management: Track contracts and key attributes to connect vendor risk decisions to agreements and renewal timing.
Pros:
- Users frequently value having a single place to manage vendor records and oversight, reducing operational sprawl.
- Reviews suggest Venminder is particularly useful when teams want process consistency, not just a repository of documents.
- Some customer feedback emphasizes that the platform helps make vendor risk workflows repeatable across business units.
Cons:
- Navigational clarity can be a challenge for newcomers, especially given the extensive information the platform offers.
- Users note friction in workflows where there is not enough automatic carryover between similar questions, which can create duplication in reviews.
- Some teams may need to invest in enablement and internal process design to achieve consistent execution.
Pricing: Pricing is typically quote-based and packaged by tier and capabilities.
Best for: Regulated mid-market and enterprise organizations that value consistency, documentation quality, and the ability to lean on structured workflows to keep due diligence from becoming ad hoc. It is especially relevant if you have frequent renewals and audits and need a program that runs predictably across teams.
6. Panorays
Panorays is a third-party cyber risk management platform that helps you scale vendor risk reviews by combining external security ratings, vendor questionnaires, and continuous monitoring. From a VRM perspective, you can use it to add structure to assessments, reduce spreadsheet-driven follow-ups, and keep vendor posture up to date between scheduled review cycles.
Key features:
- Cyber posture ratings and attack surface monitoring: Combine outside-in monitoring with contextual risk signals to help evaluate vendor security posture and prioritize what matters.
- Centralized vendor inventory and risk dashboards: Get one place to store vendors, view risk by category, and monitor posture over time.
- Continuous monitoring and alerting: Monitor vendors continuously and surface alerts on posture changes and security gaps to support ongoing oversight.
- AI-driven questionnaire workflows: Automate sending, tracking, and management of vendor questionnaires, with tooling to reduce manual exchanges.
- Remediation tracking and stakeholder reporting: Track remediation tasks and produce reporting outputs (including executive-style reports) for internal stakeholders and vendor-facing conversations.
Pros:
- Reviews frequently highlight ease of use and a more structured process.
- Several reviews frame Panorays as a lean-team enabler.
- Some users value the combined model of an automated posture score paired with a questionnaire because it speeds up the process.
Cons:
- User reviews feature regular requests for more flexibility in reporting and exporting outputs.
- Notifications and workflow tuning can require effort, particularly as programs scale or become more complex.
- Many highlight limitations in administrative controls, such as role granularity, which matter more in larger organizations.
Pricing: Pricing is typically quote-based and packaged by tier and capabilities.
Best for: Mid-market and enterprise security teams that need to scale third-party cyber risk management through continuous monitoring. It’s most effective when your vendor volume makes manual reviews unrealistic.
7. SecurityScorecard Platform
SecurityScorecard is widely used as a cyber risk ratings and monitoring platform for third-party oversight. From a VRM perspective, it is commonly adopted when your primary problem is prioritization across a large vendor portfolio and leadership expects an objective way to track posture trends, with workflows and questionnaires layered in where needed.
Key features:
- Cyber risk ratings and factor breakdowns: Score vendors using external signals and show drivers behind the rating.
- Portfolio monitoring and alerting: Track posture changes across multiple vendors and surfaces, highlighting key shifts for review.
- Questionnaires and assessment workflows: Support structured vendor assessment workflows to complement external monitoring signals.
- Remediation collaboration: Helps teams engage vendors on issues and track remediation progress over time.
- Reporting for stakeholders: Produce summaries that help communicate vendor posture and program status to leadership.
Pros:
- User reviews highlight clear visibility into vendor risks.
- Analysis revealed that teams find SecurityScorecard helpful to prioritize deeper diligence, focusing effort on vendors with meaningful signals.
- Some reviewers describe the platform as strong for communicating risk, both externally and internally, because ratings are easy to explain.
Cons:
- False positives and scoring disagreements may create vendor friction and require internal verification.
- Some users report UI limitations in dashboards, where drill-down and workflow actions do not always behave the way teams expect.
- Reviewers note friction in assigning and managing questionnaire work, which can slow operational execution at scale.
- Ratings-first tools often require strong internal workflow discipline for approvals, exceptions, and audit trails.
Pricing: Pricing is typically quote-based and is commonly influenced by vendor count and module scope.
Best for: Mid-market and enterprise teams with high vendor counts where continuous visibility and prioritization are the primary constraints. It is most effective when you already have a defined process for acting on alerts and turning monitoring signals into documented decisions and vendor follow-ups.
8. BitSight
BitSight is a cyber risk intelligence and security ratings platform that gives teams an outside-in view of third-party security posture. In a VRM context, you can use it to continuously monitor large vendor portfolios, spot meaningful security changes earlier than periodic reviews, and communicate vendor cyber risk to leadership using consistent metrics and trend reporting.
Key features:
- Security ratings with risk-factor detail: Produces a security rating and supporting findings to help teams understand what is driving a vendor’s posture and where issues are concentrated.
- Assessment workflows: Get AI-assisted assessment and summarization as a speed layer for reviews.
- Fourth-party visibility: Surfaces indirect dependencies and product usage signals.
- Third-party vulnerability detection and response: Supports response workflows for major vulnerabilities and zero-day events, including vendor outreach and tracking remediation progress across impacted third parties.
Pros:
- The outside-in view can highlight blind spots that internal controls do not catch.
- Portfolio-level visibility helps explain vendor posture to stakeholders at scale.
- Reviewers consistently value alerts and trend visibility, especially the ability to see score trends and get notified when a vendor’s score drops significantly.
- Multiple reviews emphasize clear, executive-friendly reporting, where the rating serves as a simple way to communicate the third-party risk posture to leadership.
Cons:
- Scoring clarity and vulnerability finding interpretation can trigger debate and vendor friction.
- False positives and lagging updates are recurring themes in reviews.
- Some users describe parts of the platform functioning like separate tools.
- Alerting configuration and response expectations need to be set early to avoid noise.
Pricing: Quote-based (varies by scope, vendor count, and modules).
Best for: Mid-market and enterprise teams with high vendor volume that need continuous, objective monitoring signals to decide where scarce review time should go, especially when leadership expects a defensible metric and trend line.
9. RiskRecon
RiskRecon by Mastercard focuses on outside-in, continuous monitoring and reporting of third-party cybersecurity posture. From a VRM perspective, you can use it as a monitoring layer to identify issues, prioritize follow-ups, and generate vendor-facing reporting that you can then use to advance remediation conversations.
Key features:
- External security assessment reporting: Produce detailed vendor security reports across multiple IT security categories.
- Continuous monitoring: Check vendor posture signals over time to catch meaningful changes between review cycles.
- Risk-prioritized findings: Helps teams focus on issues that matter most rather than treating all alerts as equal.
- Vendor reporting and sharing: Generate reports that can be shared with third parties to support remediation discussions.
- Integration support: Can integrate outputs into broader governance workflows and tools.
Pros:
- Detailed reporting capabilities that cover a wide range of IT security issues.
- Review feedback suggests it can make background checking and posture visibility easier for teams with limited time.
Cons:
- Public review volume is relatively limited compared to larger platforms, so trends are less statistically strong than with more widely reviewed tools.
- As a monitoring-focused product, it may not cover the full workflow needs for questionnaires, approvals, and exception logging without a companion system.
- Teams may need to invest in internal process clarity so that monitoring outputs reliably turns into action.
Pricing: Pricing is typically quote-based, commonly influenced by vendor count and depth of monitoring.
Best for: Mid-market and enterprise teams that want continuous vendor posture monitoring and vendor-facing reporting, especially when your vendor portfolio is large and annual-only reviews are no longer sufficient. It is a strong fit when you already have a workflow system for approvals and exceptions, and need a high-signal monitoring layer.
10. OneTrust Third-Party Management
OneTrust Third-Party Management is a workflow-centric platform for managing vendor and third-party risk across the lifecycle, often connected to broader governance programs such as privacy, security, and data governance. From a VRM perspective, you can shortlist it if you need configurable assessments, a strong workflow design, and a centralized repository that supports multiple risk domains beyond IT security.
Key features:
- Central third-party inventory: Maintain a repository of vendors with profiles, tiering, and lifecycle status.
- Configurable questionnaires and templates: Create and run vendor assessments with conditional logic and reusable templates.
- Workflow automation: Route reviews, approvals, and follow-ups to the right owners with status tracking.
- Evidence and documentation management: Store documents and artifacts needed for audits and customer requests.
- Reporting and integrations: Support stakeholder reporting and connect to other systems to enrich assessments.
Pros:
- Reviews frequently highlight flexibility in building questionnaires and templates, including dynamic assessment logic.
- Users often cite good performance and reliability once set up, especially in enterprise environments.
- Review patterns suggest teams value using OneTrust when vendor risk needs to align with broader governance programs rather than living in a silo.
- Some reviewers appreciate the level of integrations available, particularly when tying in external risk signals.
Cons:
- Reviews indicate the tool can feel confusing at times, especially around what needs to be filled out and how to find submissions.
- Users report searchability and UI clarity issues that can become a day-to-day productivity drag.
- Some reviewers describe a learning curve and admin overhead, particularly when heavily customizing workflows.
- User feedback suggests poor support responsiveness.
Pricing: Pricing is typically quote-based and modular, often influenced by purchased modules and scale.
Best for: Enterprise organizations that need vendor risk management tied to broader governance workflows and are willing to invest in configuration and change management. It is a good fit when the program must support multiple risk types, complex workflows, and cross-functional stakeholders.
11. ServiceNow Vendor Risk Management
ServiceNow Vendor Risk Management is designed for organizations that want VRM embedded into the ServiceNow ecosystem, connecting vendor risk to integrated risk management and IT operations workflows. From a VRM perspective, you can consider it when vendor reviews, approvals, and remediation need to connect cleanly to ITSM processes, ownership models, and existing ServiceNow governance.
Key features:
- Third-party portal: Get a structured way for vendors to submit information and for teams to manage communications.
- Vendor onboarding, offboarding, and renewals: Track vendor lifecycle milestones so oversight is continuous and measurable.
- Assessment automation and scoring: Set up vendor tiering, risk-scoring models, and automated assessments aligned with your criteria.
- Ongoing monitoring and risk intelligence: Track changes in risk posture over time and support targeted reassessments.
- Dashboards and reporting: Get program metrics and portfolio views for operational teams and leadership.
Pros:
- Reviewers often highlight the structured portal experience and transparency, which helps reduce vendor and internal confusion.
- Users mention value in custom scoring models and automated calculations, especially when scaling to many vendors.
- Teams that already use ServiceNow prefer having VRM integrated within the same platform, so they can manage everything in one place.
Cons:
- Reviews indicate customization beyond default workflows can be constrained, and deviations may require more effort and time to implement.
- Users mention training needs and a learning curve, particularly if teams are not already comfortable in ServiceNow.
- Concerns around licensing costs are a recurring theme in user reviews.
- It can be a blocker if some teams are not on the ServiceNow ecosystem.
Pricing: Pricing is typically quote-based and depends on modules, scale, and existing ServiceNow footprint.
Best for: Large organizations that already rely on ServiceNow for IT and risk workflows and want VRM to be part of the same operational system. It is best suited when you need integration with IT ownership, incident and ticket workflows, and governance reporting at enterprise scale.
12. Archer
Archer is an integrated risk management platform that centralizes risk, compliance, audit, incident, and third-party risk programs. From a VRM perspective, Archer is usually chosen when you need deep workflow customization, rigorous approvals and exception handling, and enterprise-grade reporting that spans multiple risk domains beyond vendor risk alone.
Key features:
- Enterprise workflow customization: Configure intake, assessments, approvals, exceptions, and escalation paths to match your program.
- Third-party risk assessments: Enable structured vendor reviews with questionnaires, evidence capture, and audit history.
- Issue and remediation management: Track findings through to closure with ownership and deadlines.
- Dashboards and reporting: Provide stakeholder reporting and exportable outputs for leadership and audit requirements.
- Integrations and data intake: Connect to other systems to centralize risk signals and reduce manual aggregation.
Pros:
- Reviews often emphasize strong reporting capabilities and dashboards.
- Users highlight the depth of customization, which helps mature programs model complex third-party workflows.
- Review feedback suggests Archer works well when vendor risk needs to sit alongside other IRM programs, enabling cross-domain visibility.
Cons:
- High licensing costs are a recurring theme in reviews, and cost can be difficult to justify for smaller programs.
- Users commonly describe the UI as dated and ask for stronger automation and logic to reduce manual work.
- Reviews indicate that certain reporting or workflow needs may require additional configuration effort beyond what is ready out of the box.
- Integrations can be a friction point depending on your environment and the tools you need to connect.
Pricing: Pricing is typically quote-based and generally reflects the enterprise IRM scope and modules.
Best for: A mature enterprise risk program that needs a highly configurable IRM platform. You must have the necessary governance maturity, admin expertise, and budget to support it. Archer is most appropriate when VRM is one component of your broader risk operating model, not a standalone initiative.
Before you start shortlisting tools, define your VRM operating model, or your tool may become another spreadsheet. A tool can track vendors, but it can’t decide how your company decides. Firstly, ensure that you have clarity on the following:
- Who owns each vendor relationship: You should assign an internal vendor owner to each vendor relationship. They are accountable for explaining how we use the vendor, what data/workflows are involved, and for driving day‑to‑day vendor management, including escalating issues and chasing the vendor for answers, remediation, and commitments.
- Who approves exceptions: Your security team may recommend an exception based on a documented risk assessment and proposed compensating controls; however, only the Business/Risk Committee (or other designated risk-acceptance authority) may approve the exception. You should ensure that approved exceptions are time‑bound, include an owner, and state the risk being accepted and any required compensating controls.
- What triggers a re-review: You must re-review vendors at renewal and whenever a material change occurs, including: a security incident involving the vendor or our use of the vendor; a major outage or significant service degradation; any scope change (new product/module, new integration, new environment); any data change (new data types, increased sensitivity, new processing purpose, new regions); or when the vendor stops providing current independent assurance (e.g., SOC 2/ISO reports lapse, are withdrawn, or no longer cover the service in use).
What ‘red’ actually means: A Red rating means the vendor presents unacceptable risk without additional action. For Red vendors, you may pause onboarding and any expansion of use, escalate for Security and Legal review, and require either remediation and/or approved compensating controls before proceeding; if the risk cannot be reduced to an acceptable level within an agreed timeframe, you may replace the vendor or exit/terminate the relationship.
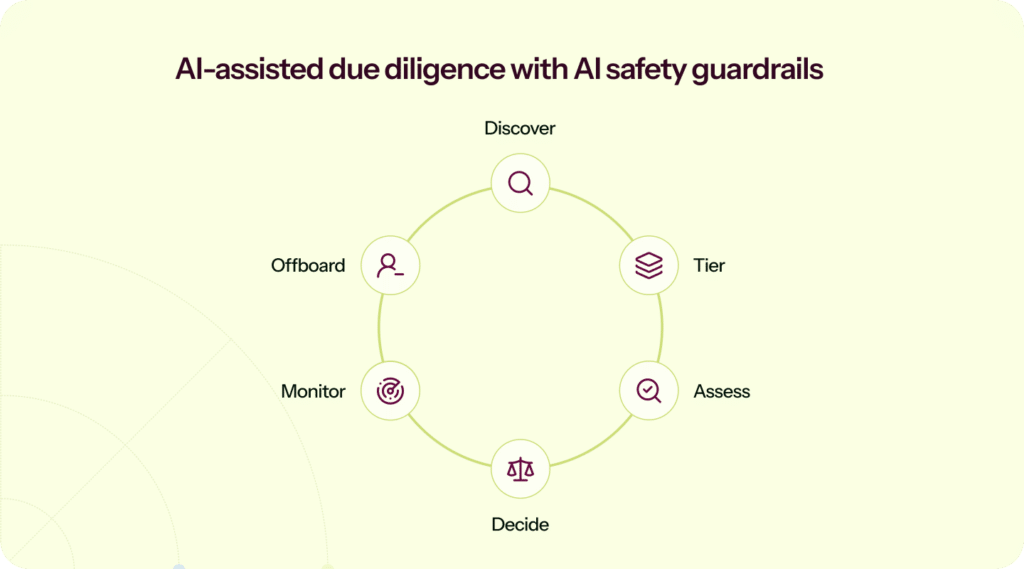
10. AI-assisted due diligence with AI safety guardrails
AI can genuinely help with VRM by speeding up document review, flagging missing clauses, and suggesting follow-up questions. It can also introduce new risks if governance is vague.
“Compliance analysts review AI outputs; high-risk actions require dual approval. Every automation action is logged, version-controlled, and validated for explainability.”
~ Jinay Sangani, Information Security PCI and Data Compliance Specialist, Finastra
What to look for:
- AI outputs that are reviewable and editable (not a black box)
- Clear answers on training, prompt retention, and access controls
- Protections against prompt injection, especially for tools that connect to sensitive systems
A demo checklist to keep in mind when evaluating vendor risk management tools
Use this as your “show me, don’t tell me” list during demos. The goal is simple: force the tool to prove it can handle your real-world friction points.
- Discovery: Where do vendor signals come from (SSO, spend, email, ticketing)? How are duplicates handled?
- Tiering: What inputs drive tiering? Can you override with a rationale and keep an audit record?
- Due diligence: Can vendors complete questionnaires in-portal, upload evidence, and respond to follow-ups cleanly?
- Evidence: How are expiry dates tracked? What happens when something goes stale?
- Monitoring: Show me how you prevent ‘assurance deluge’, how alerts are tuned, routed, escalated, and closed without drowning the team.
- Exceptions: Can you log risk acceptance with the owner, rationale, and review date, then export it cleanly?
- Access: How do approvals connect to provisioning and offboarding?
- Exports: Can you generate an auditor pack and a customer-friendly summary without manual assembly?
- AI: What data is stored, what data is used for training, and what controls exist around prompts and outputs?
“If the term’s not measurable, it’s not verifiable, then it can’t be enforced. So, you know, listen to what they’re saying with those words.” ~ Ryan Schoeller, Senior Manager, Security Trust & Assurance at Treasure Data, Inc. (Excerpt from Vendor & Risk Evaluation: How to Spot False Cyber Vendors webinar)
Action: When a vendor claims ‘continuous monitoring’ or ‘automation’, insist on seeing the metric, the workflow that produces it, and the report/export you’ll rely on during audits or incidents.
Conclusion
The right VRM tool is the one that fits your reality. You need a tool that lets you continuously discover vendors, tier them by real exposure, run due diligence without endless chasing, and preserve a decision trail you can defend later. Think of it like your ship’s manifest: you want a trustworthy inventory before you hit the asteroid field, not after. The goal isn’t more documents. It’s a defensible story about security posture that’s easy to consume and hard to misunderstand.
Most VRM platforms fall into two categories. They are either heavyweight platforms that take months to set up, or lightweight scanners that surface signals but need a lot of manual lift. Sprinto strikes the perfect balance, enabling a fast setup, built-in workflows that are easy to run, and AI-powered vendor assessments.
- Rapid, low-lift onboarding: Teams can onboard vendors quickly with automated vendor discovery, and also classify risk, send questionnaires, and request documents with just a click.
- Simplified audit workflows: Sprinto AI analyzes vendor questionnaires, identifies gaps, and helps you and your vendor remediate on time, thus ensuring secure onboarding and audit-ready vendor reviews. Framework-aligned assessments and automated evidence collection ensure every vendor review is mapped cleanly to SOC 2, ISO 27001, HIPAA, GDPR, NIST, or any custom framework the team follows. Continuous monitoring adds another layer of protection by highlighting changes in vendor posture as they happen.
- High customizability: Sprinto also avoids the rigidity of traditional VRM platforms. Risk scoring and descriptions, workflows, questionnaires, and vendor data fields are all fully customizable, and with AI Playground, teams can even create custom AI actions to automate vendor-specific analysis without requiring engineering support.
The result is a VRM program that drives real outcomes: faster audits, less busywork, better visibility into high-risk vendors, and stronger cross-team alignment across security, compliance, vendor procurement, and leadership teams.
Ready to replace vendor fire drills with a repeatable VRM workflow? Schedule a Sprinto demo and run one of your real vendor reviews end-to-end.
FAQs
Start small. Two to four tiers are usually enough, as long as each tier has clear criteria: data sensitivity, privilege level, integration depth, and business criticality. Auditors care less about the number of tiers and more about consistency: critical vendors get a deeper review, and you can prove you did it.
Tie cadence to tier. Many programs reassess critical vendors annually, medium vendors every 18 to 24 months, and low-risk vendors on a lighter schedule. Also trigger a reassessment for meaningful changes: new data types, expanded integration, incidents, renewals, or a subprocessor change.
For higher-tier vendors, a practical baseline includes: a SOC 2 Type II report or ISO 27001 certificate; security and privacy policies; a DPA; a subprocessor list; incident notification terms; and data retention or deletion commitments. For vendors with production access, add pen-test summaries and access-control details.
SOC 2 is strong evidence, but it is not a decision by itself. Validate scope (does it cover the service you use?), exceptions, complementary user entity controls, and contractual terms. Approval should reflect your environment, not just the vendor’s report. Think of SOC 2 as a trusted summary of a much bigger set of evidence. It’s valuable, but it’s still a proxy, and it can be out of date the moment you read it.
For critical vendors, use SOC 2 to gauge maturity, then validate scope (does it actually cover the service you use?) and decide what needs ongoing monitoring versus point-in-time assurance. If a claim matters to your risk decision, prefer evidence that’s independently validated rather than purely self-attested controls.
Ratings are useful as monitoring signals, but they do not tell you what data you share, what permissions you granted, or what contract terms you agreed to. Many teams use ratings as input, then store questionnaires, evidence, and decision logs in a workflow system. Ratings are useful for triage, but treat them like a smoke alarm, not a full inspection report. They can highlight issues early, but you should understand what the signal actually covers and have a way to annotate disputes or clarify context with the vendor.
Tier the vendor first. For low-risk vendors, alternative evidence may be acceptable. For high-risk vendors, ‘won’t provide evidence’ is a risk signal. Escalate: request equivalent documentation, add contractual controls, limit access scope, or consider alternatives.
Fourth-party risk comes from your vendors’ vendors (subprocessors and dependencies). You do not need to model every dependency, but for critical vendors, you should collect subprocessor lists, understand where data is hosted, and monitor for major changes.
Make access part of the lifecycle. Approve a scope of access, provision via SSO where possible, set review dates for privileged integrations, and require offboarding steps when the tool is no longer used. This is how you reduce authorization sprawl in practice.
Author
Sucheth
Sucheth is a Content Marketer at Sprinto. He focuses on simplifying topics around compliance, risk, and governance to help companies build stronger, more resilient security programs.Explore more
research & insights curated to help you earn a seat at the table.