TL,DR:
| An IT Risk Management Framework (RMF) provides a structured workflow that integrates privacy, security, and cyber supply chain risk management activities into the system development lifecycle |
| Originally established by NIST, the RMF serves as both a template and guideline for organizations of any size or sector to identify, eliminate, and minimize risks regardless of technology type |
| Five major frameworks to consider: ISO 27001/27002 (globally adopted ISMS standard), NIST CSF (flexible, suitable for all industries), COBIT (aligns IT with business goals), COSO ERM (integrates risk with strategy), and FAIR (quantitative risk analysis using financial terms) |
| ISO 27001 provides security control guidance for processing financial information, employee details, intellectual property, and third-party entrusted data. ISO 27002 provides implementation-level detail for those controls |
| NIST Cybersecurity Framework organizes risk management into 5 functions: Identify, Protect, Detect, Respond, and Recover, making it adaptable for organizations at any maturity level |
| Effective risk management frameworks provide tangible business benefits including easier access to capital, lower borrowing costs, improved long-term performance, and stronger confidence from investors, customers, and partners |
All organizations, irrespective of their size, face risk. Failure to address these risks could result in heavy monetary and reputational risks. Risk management allows organizations to have a system in place to counter external threats while keeping business continuity.
Effective risk management adds value to any organization and provides clients and customers with a sense of security.
An effective IT risk management framework allows an organization to scale while protecting its capital base and earnings. Other organizations, investors as well as customers are more likely to engage with companies having effective risk management frameworks. This generally results in easier access to capital for the firm, lower borrowing costs, and improved long-term performance.
What are IT Risk Management Frameworks?
An IT Risk Management Framework provides a workflow integrating privacy, security, and supply chain risk management. Risk compliance software operationalizes this workflow by connecting control performance to risk appetite in a single auditable system.
Originally established by the National Institute of Standards and Technology, the Risk Management Framework serves both as a template and guideline for organizations to identify, eliminate and minimize risks.
Effectiveness, efficiency, and constraints are considerations for the risk-based approach to control selection and specification as per applicable laws, directives, standards, Executive Orders, policies, or regulations.
Managing organizational risk is a priority for effective information security programs. Risk assessment tools provide the structured methodology for identifying, scoring, and tracking risks across the IT risk management framework’s control requirements. The Risk Management Framework approach is equally applicable to any type of technology or system (e.g., IoT, control systems), new and legacy systems, and within any type of organization regardless of sector or size.
Types of IT Risk Management Frameworks
The first step is choosing a framework that aligns with your requirements and industry standards. Once selected, a compliance audit checklist helps verify that implementation is meeting each control objective before external auditors review it. While one framework may not fulfill all your business requirements, cross-referencing competing frameworks can help you determine where you need to focus.
Here are five major IT risk management frameworks to consider:

ISO 27001 & ISO 27002
The ISO catalogue is among the most recognized risk management references. Before pursuing certification, understanding the ISO 27001 certification cost helps organizations budget for implementation, gap analysis, and annual surveillance audits.
Within the information security community, ISO 27001 is one of the most widely known and globally adopted standards. The framework lays down specific guidance and security controls for processing financial information, employee details, intellectual property, or information entrusted to you by third parties.
ISO 27002 is based on ISO/IEC 27001 for institutions to establish an Information Security Management System (ISMS). It helps organizations best implement the framework within their unique operations by providing in-depth detail about key controls from 27001 and details the control objectives as well.
Cybersecurity Maturity Model Certification (CMMC)
The Cybersecurity Maturity Model Certification, published in January 2020, and revised in 2022, delivers a comprehensive model based on the latest NISP SP 800-172 and NIST SP 800-171.
NIST 800-53 & NIST CFS
The NIST, or National Institute of Standards and Technology, is responsible for publishing a handful of process guides and IT risk management frameworks.
Designated for U.S. federal information systems, NIST 800-53 & NIST CFS. NIST 800-53 are the most notable documents providing a robust catalogue of security and privacy controls and objectives to support best-in-class cybersecurity standards. The standards, guidelines, and practices are written in simple language suited for even non-technical executives or line of business individuals.
AICPA, SOC 2
The American Institute of CPAs (AICPA) developed and published SOC 2 to define criteria for managing customer data based on the following five core principles:
- Security
- Processing integrity
- Availability
- Privacy
- Confidentiality
Organizations can define their set of Service and Organization Controls (SOC) rather than follow a detailed IT risk management framework of pre-defined controls. The organizations can audit effectiveness, embed controls into their corporate policies, and design to evaluate how well the control model fulfils the five principles according to business operations.
Expression des Besoins et Identification des de Sécurité (EBIOS)
EBIOS is a French information security framework published and maintained by The National Cybersecurity Agency of France (ANSSI) under the French Prime Minister.
The EBIOS reduces risk and secures the handling of a confidential or sensitive information framework for organizations working directly with the Defense Ministry.
Steps to Prepare for IT Risk Management Framework
Risk management frameworks are guidelines to help protect every aspect of business against possible threats. This includes the risks posed by unwanted or faulty products, poorly executed business plans, volatile markets, etc.
IT risk management frameworks are designed to aid businesses as well as government institutions in identifying possible data risks, determining which systems they pose a threat to, and what options they have for remediating or preventing said risks.
The steps to prepare for IT risk management frameworks can be broken down into five essential stages:
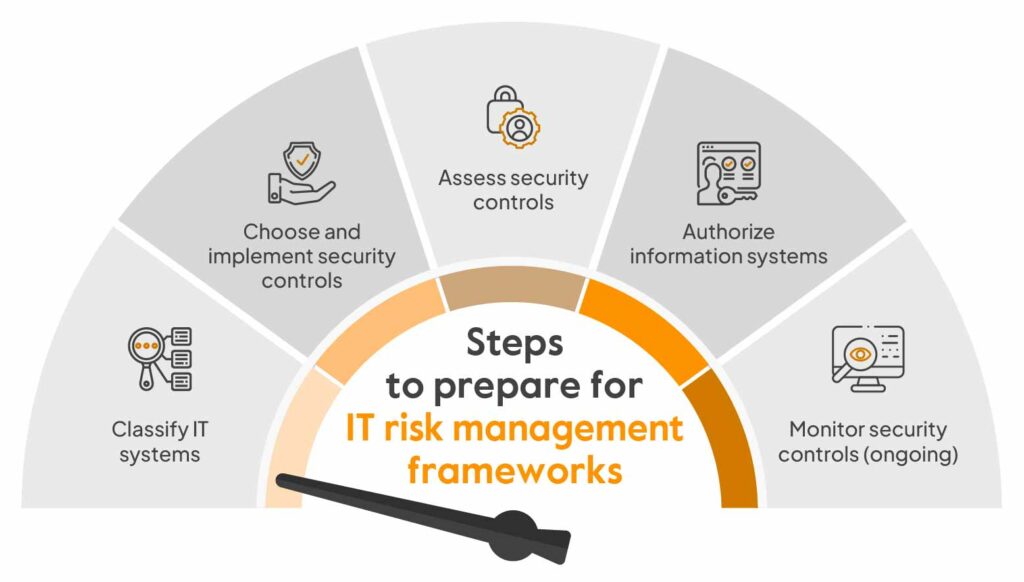
Classify IT systems
All IT systems within the organization should be periodically reviewed and categorized. Define and identify system boundaries as well as classify which kinds of information types are associated with the system.
Likewise, take into account relevant information relating to the organization itself, connections to other systems, the system’s operating environment, and intended use.
Choose and implement security controls
Choosing the right security controls is an essential step towards the right framework. An organization’s security controls are the operational, management, and technical safeguards available to an organizational information system, designed to help protect the availability and integrity of the system.
Different security controls cater to specific kinds of systems and information, and choosing the right controls is essential to close the gap between adequate protection and system vulnerability.
Assess security controls
With the security controls implemented, the next step is to assess their functionality as well as outcomes. The controls need to be checked to see if they are correctly installed and operating, if they are meeting required security requirements and their effectiveness at protecting business operations and data.
Authorize information systems
Once the security controls are in place, authorize control over the system and enable it to get to work. Correctly implemented, to help protect the business, RMF automated workflows will begin operating.
Monitor security controls (ongoing)
The risk management framework should remain viable throughout its use with the help of ongoing monitoring of security controls. Regularly conduct impact analyses, document changes, and continuously report on security controls’ statuses to establish ongoing efficacy.
Importance of IT Risk Management Frameworks

As discussed, businesses everywhere are susceptible to risk. Importance of IT risk management frameworks cannot be underestimated at a crucial time like this.
Organizations can navigate the complex landscape of risk management with the right risk management frameworks, providing a number of key advantages in the process.
Key benefits of risk management frameworks are:
Increased supply chain security
Significant risk is imposed on businesses as modern supply chains are becoming ever more complex. Effective RMF solutions can help organizations in improving the quality and usability of supply-chain-relevant data streams.
As a result, organizations have accurate insights into the factors that may influence essential supply chains.
Effective asset protection
An organization is only as secure as its assets. Risk management frameworks help protect those assets, understanding and prioritizing risks, identifying relevant information, and empowering organizations to respond quickly and efficiently to mitigate and resolve emergent risks.
Reliable protection of intellectual property
Risk management frameworks lay guidelines on how intellectual property may be protected against misuse and theft.
Businesses can operate more efficiently, backed by relevant data and clear standards, feeling secure in the fact that their intellectual property is better protected and the chance of theft is minimized.
Improved reputation management
A business can keep its security processes consistent by having clear criteria of security and operational standards in place and implemented through all levels.
This reduces the danger of data exposure and improves risk mitigation. This, in turn, protects the organization against costly mistakes that could lead to reputational damage.
Powerful competitor analysis
Understanding competitors in these aggressive markets can be just as important as understanding your own business.
Disparate outside information sources within risk management frameworks, such as social media, news reports, blogs, etc., so that organizations can keep close surveillance on their competition and react quickly when necessary.
Easy Automated Risk Insights
Sprinto for Risk Management

There has never been a time more important than today for organizations to get compliant in order to conduct business. In scenarios of non-compliance, companies may suffer heavy financial and reputational loss. However, with the right risk management solutions, organizations can effectively monitor and manage risks while ensuring resilience and continuity in the face of an uncertain future.
Sprinto offers powerful compliance automation capabilities. It seamlessly integrates with your cloud setup and to helps monitor entity-level risks as well as implement controls from a single dashboard.
Sprinto helps software-as-a-service (SaaS) based companies in obtaining security compliances, such as SOC 2, GDPR, ISO 27001, and HIPAA certifications, among others.
Sprinto has been consecutively recognized as a Leader in Security Compliance as well as has also been named a leader in the Cloud Compliance and Cloud Security categories by G2, where it was rated #1 in User Adoption, Usability, ROI, and Ease of Implementation.
Learn all about how Sprinto can help you automate your compliance.
FAQs
There are five critical components that must be considered when designing a risk management framework. They include risk identification; risk mitigation; risk measurement and assessment; risk monitoring and reporting; and risk governance.
Developed by the National Institute of Standards and Technology, NIST RMF is the most popular IT risk management framework, but it needs many dedicated resources to implement.
The three different types of risk are:
Systematic Risk.
Regulatory Risk
Unsystematic Risk.
IT risk management focuses specifically on technology, cybersecurity, systems, and data-related risks, while Enterprise Risk Management (ERM) covers broader organizational risks including financial, operational, strategic, legal, and compliance risks. IT risk management is often a subset of ERM.
Start by identifying critical IT assets and risks, define risk assessment methods, implement security controls, assign ownership, establish monitoring and reporting processes, and continuously review and improve controls using frameworks like NIST RMF or ISO 31000.
ISO 31000 is a broad, business-wide risk management guideline, while NIST SP 800-37 provides a structured RMF process for managing information system and cybersecurity risks. ISO 31000 is flexible; NIST 800-37 is more technical, control-focused, and commonly used in federal IT environments.
Author
Ayush Saxena
Ayush Saxena is a senior security and compliance writer. Ayush is fascinated by the world of hacking and cybersecurity. He specializes in curating the latest trends and emerging technologies in cybersecurity to provide relevant and actionable insights. You can find him hiking, travelling or listening to music in his free time.Explore more
research & insights curated to help you earn a seat at the table.





















