When a company works with a third party, vendors often gain access to sensitive data that is processed on behalf of the company. This compounds the risk of exposure and therefore becomes an extension of their compliance needs. Because of this, businesses consider vendor risk management as a crucial point of contention when developing a security strategy.
In this article, we take a deep dive into vendor risk management, its use, lifecycle, maturity levels, and how you can set up an effective strategy to eliminate or mitigate risk.
Vendor Risk Management (VRM): VRM is the structured process of identifying, assessing, monitoring, and mitigating risks associated with external vendors, especially those with access to sensitive systems or data.
Why It Matters:
• Reduces exposure to cyber, legal, and operational risks
• Ensures vendor alignment with compliance requirements (e.g., ISO 27001, SOC 2)
• Protects brand reputation and customer trust
• Enables informed vendor selection and performance tracking
Vendor Risk Management Lifecycle:
1. Onboarding – Due diligence, risk assessment, compliance checks, and contracts
2. Monitoring – SLA tracking, audits, risk re-evaluation, breach response
3. Offboarding – Secure exit plans, data destruction, and final risk closure
Best Practices:
• Use a uniform framework tailored to vendor type
• Document roles, security expectations, and audit rights in contracts
• Continuously monitor risks, compliance gaps, and vendor performance
• Centralize vendor oversight and automate key processes
VRM Maturity Model:
• Ranges from Ad hoc to fully operationalized to continual optimization
• Higher maturity = Better controls, quicker remediation, stronger oversight
Why Sprinto?
Sprinto automates third-party risk evaluations, control monitoring, and audit readiness to ensure continuous vendor compliance across frameworks like ISO 27001, SOC 2, GDPR, and HIPAA.
What is Vendor Risk Management?
Vendor risk management is the method of mitigating any risk that results in business or performance disruption associated with the use of vendors or service providers. Vendor risk management lays down the foundation to identify, evaluate, track, and eliminate any risks that external vendors might pose to your business.
How is Vendor Risk Management helpful for organizations?
Recent occurrences like the SolarWinds data breach, the Colonial Pipeline attack, and other ransomware intrusions have highlighted the danger of vendor-related exposure. Regardless of the sector, size, or location of the company, these events have had an impact on millions of businesses and other entities.
Here are 4 reasons why vendor risk management is so important for organizations:
Risk identification and mitigation
Vendor risk management offers a structured method for discovering and evaluating potential risks related to external vendors. Organizations can minimize disruptions, financial losses, and reputational damage by proactively addressing these risks.
Choosing the right vendor
Vendor risk management enables thorough due diligence procedures, enabling businesses to assess potential vendors’ financial standing, operational capabilities, and track records. This facilitates decision-making and eliminates the likelihood of dealing with unethical or deceptive organizations.
Managing reputation
Companies can protect their reputations by proactively managing vendor risks. Vendor risk management helps prevent circumstances that might lead to data breaches or other incidents that damage the company’s reputation or cause customers to lose trust.
Assuring compliance
Effective vendor risk management assures compliance with industry norms and regulations. Organizations can lower the risk of non-compliance fines and legal entanglements by confirming that vendors follow appropriate security processes, data protection safeguards, and regulatory requirements.
Also check out: Guide to Compliance Risk Management
Stages of Vendor Risk Management Lifecycle
The vendor lifecycle is a set of procedures that ensures your vendor relationship is consistently and correctly managed at every step. Actively managing this lifetime is not only a best practice, but it is also required by law. You probably have vendors in each stage of the lifecycle at any one time, whether you’re conducting due diligence, managing the contract, or offboarding the vendor.
The vendor risk lifecycle is divided into three stages: onboarding, continuous monitoring, and offboarding, with the added context of operations.
Examining the basic factors that guide and support each stage will help you better understand the three primary stages of the vendor risk lifecycle. These factors include oversight and accountability, compliance, recordkeeping and reporting, and independent review.
A vendor risk management program based on these factors makes it easy to determine who in your organization is responsible for vendor risk management, what needs to be addressed, and how the overall program can be enhanced.
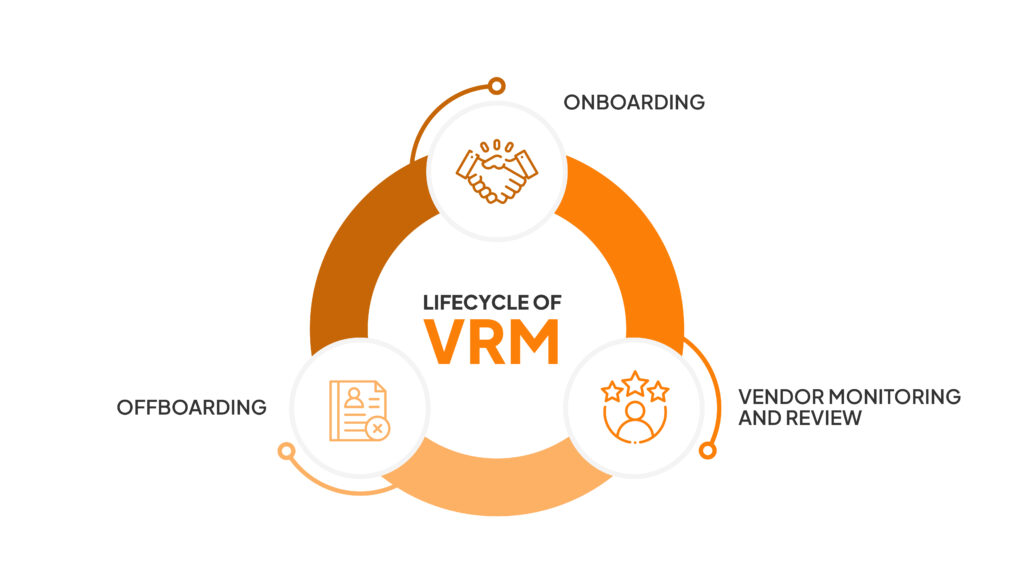
Here are the 3 stages of vendor risk management lifecycle
1. Onboarding
Identifying and assessing potential vendors is the first stage in the vendor risk management lifecycle. This includes investigating their background, assessing their financial viability, and comprehending the variety of services they offer.
This procedure also includes confirming their compliance with applicable rules and regulations pertaining to their business, as well as the whole third-party lifecycle.
Screen smarter. Use our Vendor Due Diligence Checklist to vet vendors before onboarding and ensure only trusted partners make the cut.
Contracting is the final stage in the onboarding process. It involves planning, developing, negotiating, approving/executing, and managing the legal agreement between the vendor and your company. Your contract should include service level agreements (SLAs) and other necessary restrictions.
2. Vendor monitoring and review
Once vendors have been identified and evaluated, it is important to implement a continuous monitoring system to idеntify changes in thе vеndor’s business and compliancе status
This involves doing regular audits and reviews to ensure the vendor is mееting all contractual commitments and is aware of any relevant legal devеlopments.
Additionally, it is important to have a system in place to monitor incidents such as security breaches or data loss associated with the vendor so that corrective actions to the vendor’s performance can bе made when necessary.
Here’s a step-by-step breakdown of the vendor monitoring process:
- Create a monitoring and review plan based on the inherent risk assessment.
- Perform a yearly risk re-evaluation to discover new or emerging hazards or to validate that nothing has changed.
- Make a system for tracking SLAs.
- Regularly report vendor risk to senior management and the board.
- Keep track of critical dates, such as contract renewal and expiration notice periods
3. Offboarding
If it becomes necessary to break a relationship with a specific vendor due to non-compliance or other reasons, it is critical to have a plan in place to replace them.
Understanding your organization’s third-party risk management lifecycles is critical for identifying and mitigating supplier risks.
Furthermore, there is a common misconception that third-party risk management is a yearly risk assessment or remediation program. Here are the specific processes while terminating the contract:
- Contract termination – This is the formal statement to the vendor that the contract will not be renewed. Even if you notify the vendor of their termination far in advance of the contract expiration date, the vendor engagement will not be officially terminated until the contractual date.
- Exit plan execution – The exit plan should define both parties’ particular roles, duties, and tasks for exiting the relationship safely and soundly. Returning or destroying sensitive data is one example of removing vendor access to data, networks, systems applications, and physical facilities.
- TPRM closure – Once the exit plan has been completed, there may be a few final procedures, such as paying any final invoices, updating vendor status in all systems, and archiving pertinent vendor material.
Also check out: How to Set up Vendor Management Policy
How to set up a vendor risk management process?
If you want to develop a framework for third-party risk management that works, you must use uniform standards for all vendors that are tailored to the kind of products and services that they offer. Setting up a vendor risk management process requires you to:
- Recognize and list all difficulties. For example, you should examine the settings of your cloud provider, confirm that the vendor notifies you of data breaches, designate a data protection officer, request user consent before processing users’ data, and anonymize data for privacy.
- Make sure the entire organization is on board; if your vendor management structure is not fully followed, it won’t be as effective as it may be.
- Ensure your contracts specify the “right to audit” and the security measures and specifications that the provider must meet.
- Describe how and when monitoring will take place, as well as how reviews and feedback are undertaken and risk exposures are discovered and reduced.
An ideal vendor risk management framework should streamline the whole lifecycle of vendor risk management, from sourcing and vendor selection to vendor contract negotiations, business relationship setup, and continual monitoring.
A big part of VRM goes concurrently with compliance. Sprinto is a compliance automation solution that also helps you with vendor risk management by monitoring controls in compliance preparation that goes hand-in-hand with vendor risk management.
Vendor Risk Management Maturity Levels
A vendor risk management maturity model (VRMMM) is a comprehensive methodology for assessing the level of maturity of third-party risk management programs, including controls for data security, cybersecurity, and information technology.
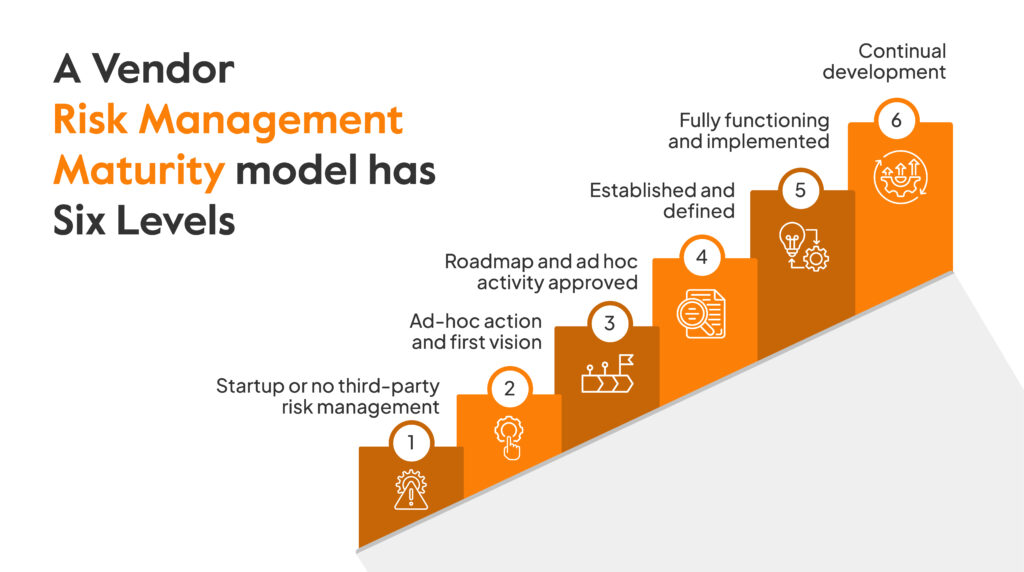
A vendor risk management maturity model has six levels:
- Startup or no third-party risk management: Organizations that are just starting out or those who don’t currently engage in vendor risk management.
- Ad-hoc action and first vision: Ad hoc third-party risk management activities are carried out, and the optimum way to structure third-party risk activities is taken into consideration.
- Roadmap and ad hoc activity approved: Management has given the go-ahead for a strategy to organize action in an effort to complete full implementation.
- Established and defined: Organizations with fully operationalized risk management operations that need measurements and enforcement but have been completely defined, approved, and created.
- Fully functioning and implemented: Organizations with fully operationalized VRM practices and compliance controls, such as reporting and independent scrutiny.
- Continual development: Organisations that aim for operational excellence and have a comprehensive understanding of best-in-class performance standards and how to apply program adjustments to constantly enhance the procedure.
The ideal way to manage vendor risk and where you may make improvements depends on how maturely your organization manages vendor risk.
Sprinto’s take on vendor risk management
It is evident by now that VRM is a crucial part of cybersecurity and a smooth business operation. No matter the size of your organization, the importance of secure handling of customer data can not be overstated.
Sprinto is a compliance automation solution that helps you in your vendor risk management by getting you compliant with major compliance frameworks across the world. Sprinto provides a single dashboard to ensure you can access all your controls in a single place. The best part is you can achieve compliance in a matter of weeks, whereas you’d need months or years if you plan to do it manually.
Talk to our experts to know how Sprinto can help you in your cybersecurity initiatives.
FAQs
What are some typical risks related to vendors?
Data breaches, inadequate security measures, regulatory violations, financial instability, and potential vendor-related company operations disruptions are common dangers connected with suppliers.
How can we recognize high-risk sellers?
High-risk vendors can be identified through a thorough risk assessment process that includes assessing the vendor’s security measures, financial stability, prior performance, and the criticality of the services they offer.
What is the procedure for evaluating vendor risk?
To identify the potential hazards that suppliers might provide, the risk assessment process often entails gathering information from them, evaluating their responses, rating their risk levels, and, if necessary, performing additional due diligence.
Author
Anwita
Anwita is a cybersecurity enthusiast and veteran blogger all rolled into one. Her love for everything cybersecurity started her journey into the world compliance. With multiple certifications on cybersecurity under her belt, she aims to simplify complex security related topics for all audiences. She loves to read nonfiction, listen to progressive rock, and watches sitcoms on the weekends.Explore more
research & insights curated to help you earn a seat at the table.





















