One of the inevitable outcomes of growth that doesn’t get the attention it deserves is security risk.
As the organization grows, technologies and third-party systems become mainstay. This directly increases the probability of risk. Information security policy is the glue that holds everything together in a way that nothing falls apart.
Let us understand what information security policy is, its importance, and the key elements.
What is information security policy?
Information security policy is a set of rules, practices, guidelines, and processes that governs the management, protection, and access of information. It ensures the confidentiality, integrity, and availability of networks, applications, systems, programs, and data across the infrastructure.
An effective information security policy helps to document security policies, respond to incidents, protect sensitive client data, and comply with regulatory frameworks like ISO, SOC, or HIPAA.
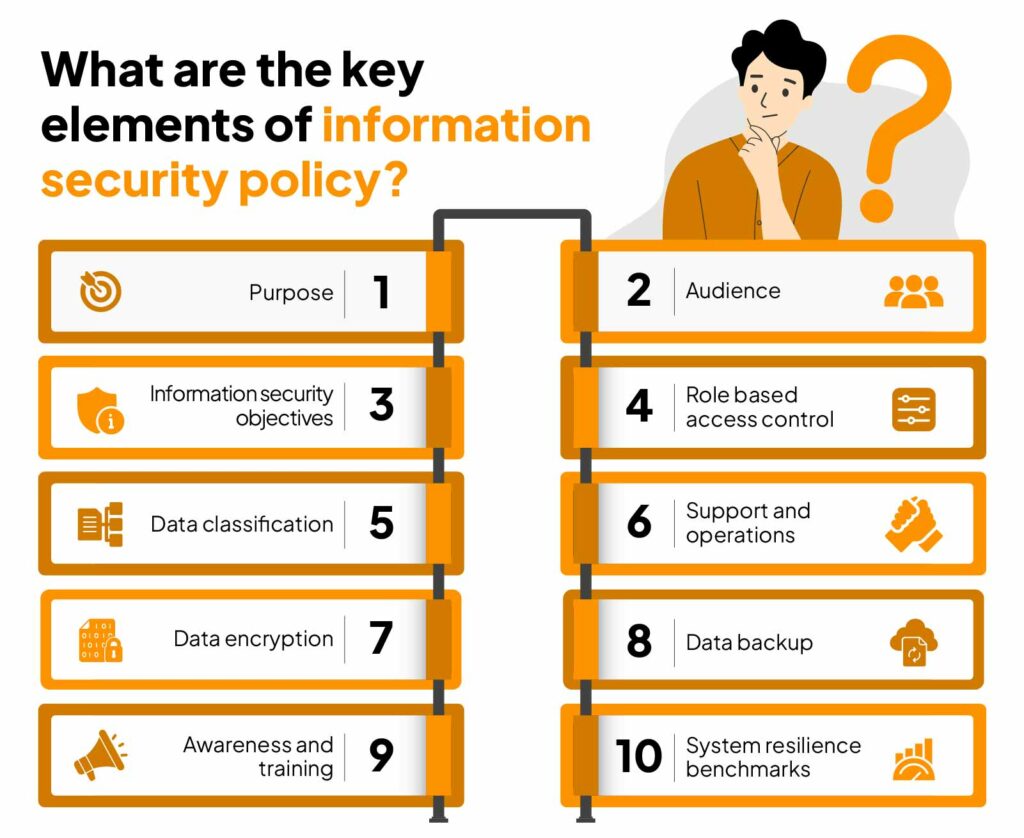
10 Most Important Elements of Information Security Policy?
Information security policy combines several elements to create a holistic approach to protection against threats. This includes:
1. Purpose
Program policies are actionable strategies that define the goals and scope. It should include your approach to information security, preventive measures, threat detection systems, legal compliance, and data transparency to clients.
2. Audience
Clarity on each policy, its clauses, and subsets help end users understand their roles and responsibilities. Employees, top management, third parties, and consultants should be aware of what they are accountable for.
3. Information security objectives
Refers to the trinity of information security; integrity, confidentiality, and availability.
- Integrity means that the data is complete, accurate, and fully operational.
- Confidentiality refers to protecting data from unauthorized access by implementing privileged or role-based access.
- Availability allows privileged users to access information required to carry out their functions as and when required.
4. Role-based access control
Every business infrastructure comprises heterogeneous data. Your policy should be set up to allow each function and subfunction to access data needed for their tasks – also known as the principle of least privilege. This helps to reduce data loss or accidental disclosure.
Effortless, Efficient Information Security
5. Data classification
Data classification is a good practice that helps organizations prevent intentional or accidental disclosure. You can conduct a risk assessment to categorize data into the following levels:
- Publicly available information.
- Confidential data that would cause zero or little damage is disclosed.
- Confidential data that would potentially cause substantial harm if leaked to the public.
- Confidential data that would undoubtedly cause substantial harm if leaked to the public.
6. Support and operations
Comprises three types of measures to protect all levels of data.
- Data protection regulation: It systems that store, process, or manage sensitive data should be compliant with industry standards and best practices. These include but are not limited to data encryption, incident response plan, backup and recovery, anti-malware, firewalls, password management, and protection against insider threats.
- Data backup: Ransomware, a type attack where malicious actors hack into a system, encrypt the data, and render it inaccessible till a ransom is paid has become the most common threat. You can avoid this by regularly backing up data in multiple locations.
- Data movement: Data in transit via electronic means should be secured through encryption and Data Loss Prevention (DLP) methods.
7. Data encryption
Whether you deploy data on the cloud or on-premise, it is transmitted electronically. To secure this data, you can use end-to-end protection measures such as:
- Advanced encryption standard (AES) to protect the online data transfer. It is an industry-standard encryption protocol that uses the same key to encrypt and decrypt. AES encryption keys are of three lengths – AES-128, AES-192, and AES-256. AES-256 is the strongest of the three, as the number of possible key combinations is the highest.
- Transport layer security (TLS) to safely transfer data via HTTPS. This method uses cryptography to secure email, payment card details, messaging, and VOIP.
8. Data backup
A strong backup and business contingency plan to ensure data integrity is crucial to retrieve information in case an incident occurs. Ensure this by
- Create backups as often as needed. You can do that manually or automate it.
- Encrypt your data while creating backups.
- Monitor the backed up data, keep track of changes, and maintain an audit log.
9. Awareness and training
Your employees are on the front lines of defense against a number of security threats. They should be familiar with the policies adopted by your organization along with industry-specific regulations or framework requirements. Basic knowledge to identify threats, know what constitutes good security practices, and steps to take against potential threats should be prioritized as a part of your training and awareness program.
10. System resilience benchmarks
Include security benchmarks such as Windows server, Linux, AWS, Kubernetes, and others in your security policy.
Importance of information security policy
When you implement information security policies, it makes a huge impact on the overall security posture. Most organizations don’t chalk out a budget for security until they face a compromise. This is a bad practice, as ISP is no longer optional for the following reasons:
The accelerated rate of digitization has increased the volume of assets deployed on the cloud—there is more sensitive data on devices than ever before.
This shift turned the cloud into a magnet for malicious actors. For businesses that store sensitive information, a security policy helps to identify and contain breach attempts should be a priority.
After May 2020, there was a 176% spike in use and installation of collaboration tools. As business dependency on third-party solutions increases, more risks add to the ecosystem.
Between 2020 and 2021, third-party breaches rose by 17%. With IPS, you can efficiently manage vendor risks and third-party risks by thoroughly evaluating and assessing them.
Regulatory compliance is compulsory for some businesses and a survival strategy for others, depending on the type of information they process.
For example, healthcare services in the US must be HIPAA compliant. Businesses that process payment must be PCI DSS compliant. If you manage sensitive customer information, SOC 2 or ISO 27001 are recommended.
When you have an information security policy, you can identify and address security gaps as mandated by the applicable framework.
How to build a strong information security policy
Building policies and processes from scratch takes an immense amount of time, cooperation, planning, and resources. Even then small to medium sized businesses with no prior security experience fail to bring it all together with success.
Sprinto brings policies, processes, and people together from a single automated platform so you don’t have to break a sweat or worry about compliance failure. It scans your system for non compliance, alerts users against vulnerabilities, and trains your employees to improve the overall posture. Talk to our experts now about your needs.
FAQs
What are the objectives of information security policy?
Information security policy seeks to preserve the principles of good security; integrity, availability, and confidentiality of tools and technologies used by members of an organization.
What are the three types of information security policies?
Three common security policies include program policies, system-specific policies, and issue-specific policies.
What is the purpose of information security policy?
A strong information security policy helps to create an efficient process to manage and monitor data assets, document vulnerabilities, changes, and updates, mitigate security threats, and build customer trust.
Author
Anwita
Anwita is a cybersecurity enthusiast and veteran blogger all rolled into one. Her love for everything cybersecurity started her journey into the world compliance. With multiple certifications on cybersecurity under her belt, she aims to simplify complex security related topics for all audiences. She loves to read nonfiction, listen to progressive rock, and watches sitcoms on the weekends.Explore more
research & insights curated to help you earn a seat at the table.





















