ThThe General Data Protection Regulation (GDPR) is one of the most stringent data protection laws in the world. Though this regulation primarily protects the privacy and security of individuals in the European Union, its reach extends well beyond EU borders. Any organization that processes the personal data of EU residents must comply, regardless of where it is based.
If you are working toward GDPR compliance, this guide walks you through the key areas you need to cover. While GDPR does not mandate a formal certification audit, organizations are still expected to demonstrate compliance to supervisory authorities at any time, and failure to do so can result in administrative fines of up to €20 million or 4% of annual global turnover, whichever is higher, under Article 83 of the regulation.
The ten areas below break down what demonstrating that compliance actually looks like in practice. We have also included a downloadable GDPR audit checklist PDF at the end of this article to help you track your progress.
Automate all your GDPR requirements with the help of Sprinto. Talk to our experts now
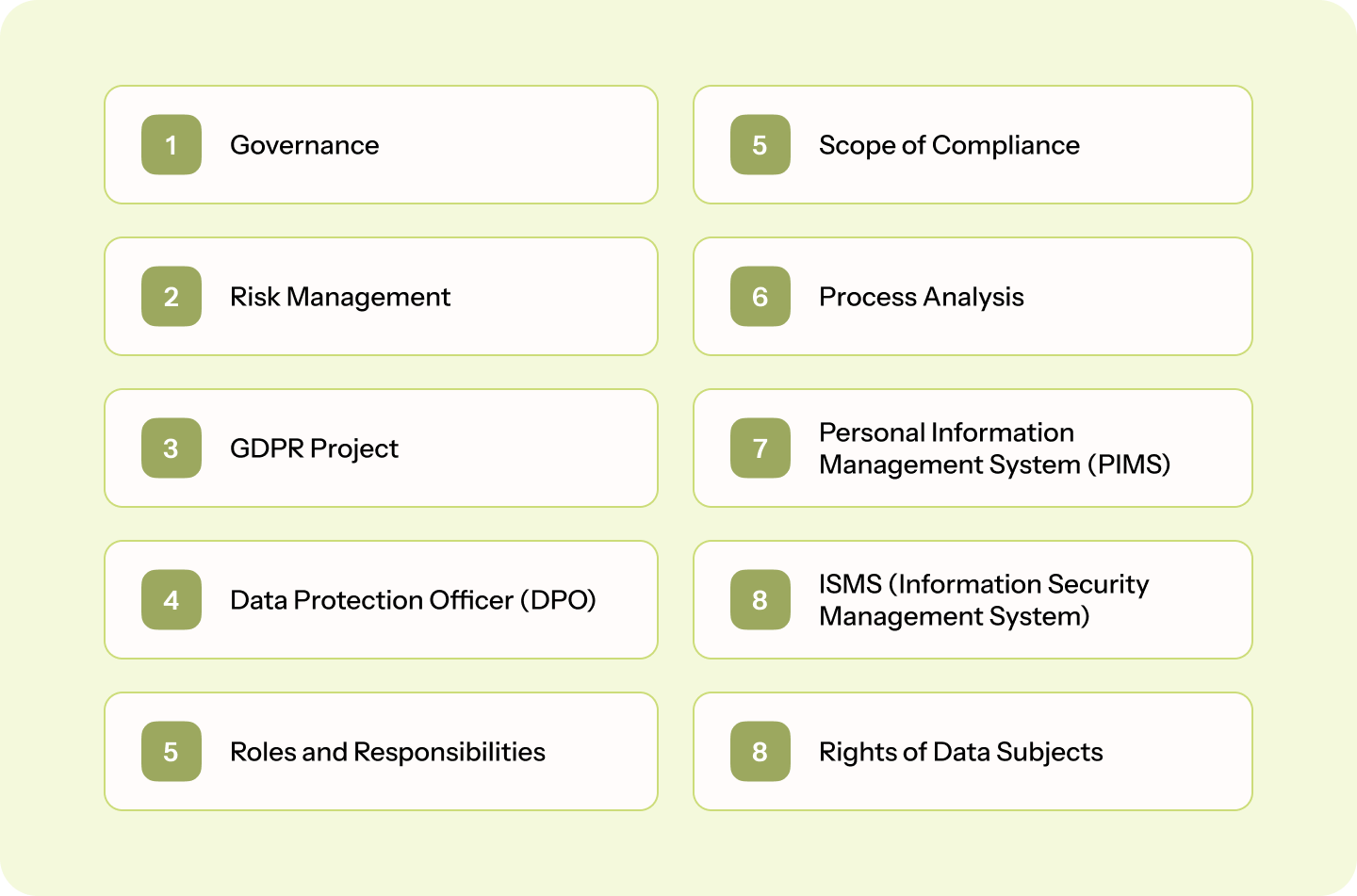
GDPR Audit Requirements
Here are the list of 10 GDPR audit requirements:
Area 1: Governance
You must ensure that the security standards and organizational policies defined by you are coherent throughout the life cycle of the data process. To ensure continuous data governance, abide by these six principles:
- Lawful, Fair, and Transparent
- Purpose Limitation
- Data Minimization
- Accurate Data Collection and Storage
- Storage Limitation
- Integrity and Confidentiality
When supervisory authorities or internal compliance teams review your organization’s practices, they will look for evidence that your policies and security standards demonstrate maintenance of data integrity, security, and confidentiality in line with GDPR requirements.
If you are a Data Controller, ensure you maintain an accurate and up-to-date data map alongside your Records of Processing Activities (RoPA) and internal compliance documentation. These are your primary tools for demonstrating accountability under GDPR.
Area 2: Risk management
As an organization processing personal data, you must continually assess the risk level your organization is susceptible to and deploy security measures to counter said risk level to ensure data security.
Periodically run Data Protection Impact Assessments (DPIA). Based on the impact on the data, determine the resultant effect on the risk.
Set up automatic security measures to ensure data security. Take the expert’s advice
Area 3: Organizational governance and accountability
Becoming/remaining GDPR compliant is an organization-wide activity. Unless every team member, starting from the top of the hierarchy, is involved, the chances are that you will run into difficulties keeping this up.
Run GDPR audits to determine whether your organization is adequately staffed to take on a challenge like this and whether every stakeholder in the organization is supportive of this activity as per GDPR audit checklist.
Area 4: DPO
A Data Protection Officer (DPO) is responsible for monitoring your organization’s compliance with GDPR, advising on data protection obligations, and acting as the primary point of contact with supervisory authorities. The DPO role is ongoing, not limited to audit periods, and requires independence from the processing activities they oversee.
Here are the three conditions which determine whether appointing a dedicated DPO is mandatory within an organization.
- You process large amounts of sensitive personal data/ data with information on criminal history
- A public authority executes your data processing
- You are required to constantly monitor your data subjects in large volumes.
If your organization qualifies to require a dedicated DPO, ensure that the person filling the position has the potential to deliver as per GDPR’s requirements.
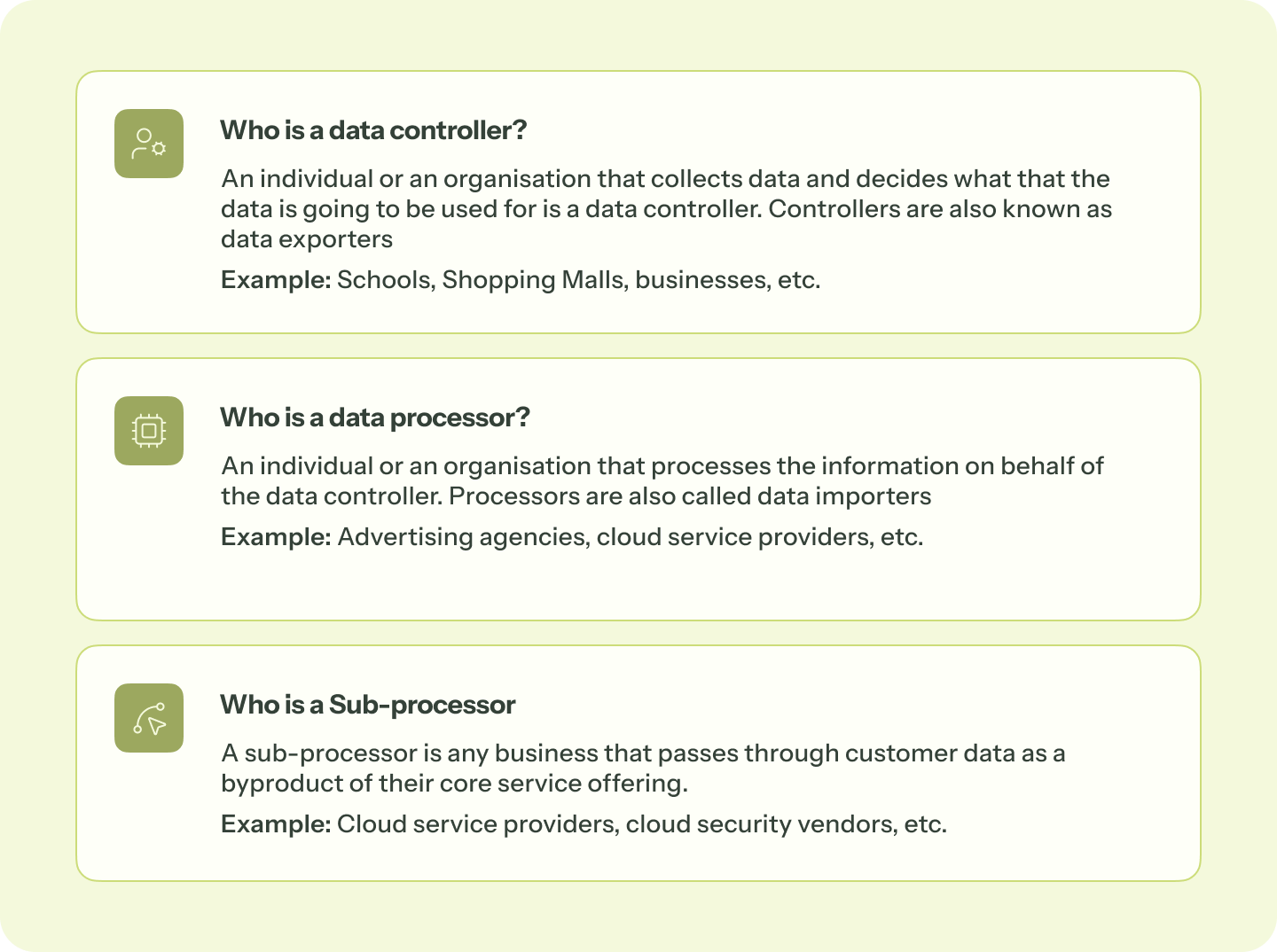
Area 5: Roles and responsibilities
Before beginning your GDPR Framework journey, establish and assign roles and responsibilities. A few duties could be towards data processing, a few towards technical security, and a few towards internal training.
This helps you continuously monitor your internal systems and their role in an effective compliance posture. This also contributes to effective training, onboarding, and offboarding.
Area 6: Scope of Compliance
Define the scope of your compliance. As an organization processing user data, it is imperative to define your data processing activities in terms of their purpose, lawful basis, categories of data involved, data subjects affected, and retention periods. In addition, it is a healthy practice to map your data, note internal and external movements, and have processes in place to ensure data integrity for data transfer to third countries, if any, as per the GDPR audit checklist.
Make sure the data you are storing is not violating GDPR standards. Talk to our experts
Area 7: Process Analysis
Article 30 of GDPR requires organizations to maintain transparent and accurate records of their data processing activities in the form of a Record of Processing Activities (RoPA). This is not a one-time exercise; it must be kept current as your processing activities evolve.
Your technical and organizational controls should demonstrably protect personal data at every stage of processing. A compliance review of this area will look for evidence of how well your controls align with each of GDPR’s core principles, including lawfulness, data minimization, accuracy, storage limitation, and integrity. Key questions to address include:
- Is there evidence of regular reviews of processing activities and associated risks?
- Are your processing activities fully documented and up to date?
- Do your controls reflect the purpose and lawful basis for each processing activity?
- Are there clear procedures for handling data subject requests?
Area 8: PIMS
Processing user data requires you to undertake a ton of documentation in the form of SCCs, DPIAs, and RoPA, among others.
The larger the organization’s size, the larger the volume of documentation involved.
Bringing in PIMS allows you to streamline your documentation processes and be ready to provide evidence when a supervisory authority, such as a national Data Protection Authority (DPA) or the European Data Protection Board (EDPB), requests it.
ISO 27701 is a privacy extension to ISO 27001 and ISO 27002, designed to help organizations establish and maintain a PIMS. While it was not implemented into GDPR, its requirements closely align with GDPR’s accountability and data protection obligations, making it a practical reference point for organizations seeking a structured approach to privacy management.
Curious about GDPR Compliance Cost?
Area 9: ISMS
To demonstrate GDPR compliance, organizations must show that appropriate technical and organizational measures are in place to secure personal data in electronic form. This includes:
- Secure coding practices that embed privacy and security from the development stage
- Regular penetration tests to identify and address vulnerabilities in your security posture
- Encryption and pseudonymization of personal data where appropriate
- Access controls ensuring only authorized personnel can access personal data
- Incident detection and response procedures
- Business continuity and disaster recovery planning
GDPR does not prescribe a specific list of ISMS requirements. However, implementing the security controls outlined in ISO 27001 is a strong starting point, as the two share significant overlap in areas such as risk management, access controls, and incident response. It is important to note that ISO 27001 certification supports GDPR compliance but does not guarantee it. GDPR has broader obligations around lawful basis, individual rights, and transparency that go beyond what ISO 27001 covers.
Area 10: Rights of data subjects
Every data subject protected by the GDPR law is entitled to rights. As an organization processing user data, you must implement processes that enable you to process any activity when a user exercises their rights.
Rights of data subjects under GDPR are:
- The Right to be Informed
- The Right of Access
- The Right to Rectification
- The Right to Erasure
- The Right to Restrict Processing
- The Right to Data Portability
- The Right to Object
- Rights concerning Automated Decision-making and Profiling
Disclosure Audit Checklist
Your organization has to clarify the information they intend to source user data and the purpose for sourcing it. In addition, all the information should be available in an easy-to-access location without confusion.
Here’s a list of things you’d need in your disclosure checklist:
Privacy Policy
Include details about your approach toward security and privacy. Talk about the personal and non-personal data you intend to collect and the intent to use.
Data Retention Policy
Your Data Retention Policy should talk about the duration you intend to use user data. Ensure that you do not exceed the retention period. In instances where you keep it for a longer duration, ensure that the data is pseudonymized or anonymized.
Data Transfers to third countries
If you are transferring data to processors in third countries, talk about the preset conditions you have to qualify for such transfers.
Data Protection Policy
Talk about all the security measures you have to ensure data security per the GDPR audit checklist.
Contact Information
In this, provide your organization’s legal address, contact information, or ways to reach your Data Prototection Officer. If you don’t have a DPO, the contact details of the person filling that role should be provided.
Terms of Use
If your organization does not collect user data of children, ensure to present this disclaimer in a format that is bold and easily visible.
Under GDPR, the default minimum age for digital consent is 16 years. However, EU member states may lower this to a minimum of 13 years under their national laws. Organizations should verify the applicable age threshold in each member state where they operate and reflect this accurately in their terms.
For example: ‘This website is available only to individuals who meet the minimum age requirement in their country of residence.’
Otherwise, include a checkbox that takes parental permission.
Cookies and Payments
Talk about all the GDPR cookie consent you use and how payments are processed across the organization.
For example, POS, e-commerce, etc.
Registration Page Checklist
When designing your registration page, ensure that it is clean and straightforward. Here are a few other things you should look out for:
Give a granular scope of the data you are collecting and allow users to select which marketing collaterals they wish to receive from you. Make it easy for users to opt in. This means instead of giving a single check box for taking consent, include multiple checkboxes, each dedicated to a specific function.
Include a section where users can explicitly consent to your organization’s terms and conditions.
Download GDPR audit checklist PDF
Document Checklist
Here’s a consolidated GDPR audit checklist of all the documents your organization would need:
- Privacy Policy
- Data Retention Policy
- Inventory of Processing Activities
- Incident Response Policy
- Data Breach Notification policy (used when notifying the GDPR authorities about an incident)
- Data Breach Notification to Users
Data Protection Checklists
While GDPR does not prescribe a fixed list of security measures, Article 32 requires organizations to implement appropriate technical and organisational measures to ensure a level of security proportionate to the risk.
This includes measures such as encryption, pseudonymization, ensuring ongoing confidentiality and resilience of processing systems, and regularly testing and evaluating the effectiveness of those measures. Organizations are also expected to embed the principles of data protection by design and by default into their systems and processes from the outset.
Why Choose Sprinto for Your GDPR Audit?
When your organization starts its GDPR Framework journey or adds patchwork to the existing structure, the GDPR Audit Checklist could be a significant first step. However, implementing all the principles, articles, and technical requirements could become expensive and inefficient if done incorrectly.
Sprinto is an Autonomous Trust Platform that continuously monitors your GDPR controls, detects changes across your compliance posture, and acts — closing gaps, refreshing evidence, and keeping you audit-ready without the operational overhead. From automated RoPA maintenance and DPIA workflows to built-in training modules and real-time control monitoring, Sprinto gives you a single, unified view of your entire GDPR compliance program. Talk to us today to understand your organization’s GDPR compliance scope.
Author
Vimal Mohan
Vimal is a Content Lead at Sprinto who masterfully simplifies the world of compliance for every day folks. When not decoding complex framework requirements and compliance speak, you can find him at the local MMA dojo, exploring trails on his cycle, or hiking. He blends regulatory wisdom with an adventurous spirit, navigating both worlds with effortless expertise
Reviewer
Swapnil Tripathi
Swapnil Tripathi is a seasoned Governance, Risk, and Compliance (GRC) professional with deep expertise in information and payment security. Certified as a PCI-DSS Qualified Security Assessor (QSA), ISO 27001 Lead Auditor (LA) and Lead Implementer (LI), he specializes in compliance frameworks essential for secure operations.Explore more
research & insights curated to help you earn a seat at the table.


























