What if a single cyberattack or supply chain failure could halt your operations overnight?
Preventing such scenarios requires a sophisticated security framework for organizations managing vast data stacks and complex processes.
This is where risk mitigation becomes essential!
It helps you prepare today so risks don’t derail business operations tomorrow. In this blog, we’ll explore risk mitigation, its importance, types, step-by-step process, and best practices to implement.
TL;DR
- Risk mitigation is the process of identifying, analyzing, and addressing risks to minimize their impact on business operations.
- It involves identifying, prioritizing, and addressing risks through structured approaches like avoidance, reduction, transfer, or acceptance.
- Best practices are robust accountability, regular monitoring, frequent reviews, and promoting a risk-conscious culture in teams.
- By aligning with standards like SOC 2 and ISO 27001, organizations enhance compliance, maintain their reputation, and ensure resilience.
What Is Risk Mitigation?
Risk mitigation is a part of the broader risk management process that focuses on identifying, assessing, and neutralizing potential threats to limit operational setbacks. It doesn’t aim to eliminate risks; instead, it reduces the impact of identified threats through risk mitigation strategies and fuels operational sustainability.
Ideally, at the time of threat, teams follow the course of action mentioned in the mitigation plan to soften the blow. The key elements of risk mitigation include:
- Identification: Recognizing potential internal and external threats.
- Assessment: Probability and severity of anticipated risks.
- Prioritization: Ranking risks so critical threats are addressed first.
- Strategy: Deciding specific actions to reduce, transfer, and avoid risks.
- Monitoring: Continuous monitoring to ensure effectiveness.
Let’s see how it works!
How Does Risk Mitigation Work?
Risk mitigation transforms uncertainty into manageable actions through a coordinated combination of teams, processes, and technology. It is not just a set of tasks but a systematic workflow that enables organizations to anticipate and tackle threats.
Although the risk mitigation plan isn’t always the same, the elements unfolding the process remain strikingly similar. Here’s how it works:
Note to designer: Make a diagram that illustrates three layers: Teams, Processes, and Technology, working together to make risk mitigation actionable. The diagram can show these layers feeding into a continuous cycle of Identify → Assess → Mitigate → Monitor
1. Teams and responsibilities
- Different teams play distinct roles in the mitigation process.
- Security and compliance teams conduct risk assessments by analyzing system vulnerabilities and reviewing regulatory requirements.
- IT and operations teams implement technical and procedural controls, such as firewalls, access management, and system backups.
- Leadership defines which risks require immediate attention and assigns budgets, workforce, and tools to address them.
2. Technology and tools
Technology supports the process by providing visibility and automation. Risk registers, monitoring dashboards, and analytics platforms help track real-time risk indicators to alert teams about emerging threats and document mitigation actions.
3. Management processes
- Processes determine how identified risks should be handled at each stage.
- Clear workflows guide teams on evaluating risk severity, prioritizing threats, selecting mitigation strategies, and monitoring results. This ensures that uncertainty is consistently turned into coordinated, actionable plans across the organization.
4. Monitoring and review
- Consistent monitoring validates the effectiveness of the mitigation plan.
- The risk management or compliance team tracks key risk indicators (KRIs), conducts audits, and reviews incident reports to ensure that mitigation strategies remain effective and updated as conditions change.
What Is the Purpose of Risk Mitigation?
Risk mitigation aims to prepare organizations for inevitable risks by bringing them down to a tolerable or acceptable level through a pre-planned response framework. Its 5 key purposes include:
1. Business continuity
To make systems and processes resilient so organizations can adapt to disruptions without jeopardizing long-term survival.
2. Financial stability
To minimize losses, maintain steady cash flows, and withstand economic uncertainty, enabling sustainable long-term growth during adverse market conditions.
3. Resource allocation
To ensure time, money, and talent are directed toward the most significant risks by ranking and prioritizing them.
4. Safeguard reputation
To demonstrate accountability and foresight so stakeholders remain confident in the organization even during uncertain times.
5. Decision-making
- Establish clear guardrails by defining risk appetite, tolerance levels, and escalation thresholds so leaders can make strategic choices.
- Together, the purpose circles around promoting a risk-resilient culture that equips existing systems and employees with a plan of action to face threats confidently.
Types of Risk Mitigation
Organizations follow targeted mitigation strategies depending on the nature and magnitude of the risk. These strategies are classified into four types:
1. Risk avoidance
Risk avoidance focuses on avoiding business projects, software, third-party tools, and high-risk markets that can expose system vulnerabilities and trigger losses.
This is generally applied when the projected impact is too high and the likelihood is significant. By not engaging in high-risk operations, businesses eliminate the threat, even if it means losing a business opportunity.
2. Risk reduction
Risk reduction minimizes the likelihood or probability of a risk through proactive security protocols.
Organizations implement a combination of technical controls (firewalls, intrusion detection, and encryption) and procedural controls (compliance policies, employee training, and monitoring systems) to reduce the probability of risks.
3. Risk transfer
Risk transfer shifts a risk’s financial or operational burden to another party, typically through contractual agreements, insurance, and outsourcing.
For example, a company transfers operational risk by outsourcing its cloud hosting to a vendor under a Service Level Agreement (SLA), making the vendor financially liable for downtime or data loss.
4.Risk acceptance
Risk acceptance refers to acknowledging a risk but choosing not to take precautionary measures because the cost of mitigation outweighs the potential impact.
It is a conscious decision taken by stakeholders and CEOs. Acceptance usually happens after they realize that some risks can’t be avoided or are so minor that mitigation is not justified.
Step-by-Step Risk Mitigation Process
Below, we have broken down the risk mitigation process into 5 key steps:
1. Target a specific risk
Focus on one priority risk at a time, especially those with high potential impact. Clearly define the scope of the risk and the impact on operations, finance, compliance, or reputation.
Key measures:
- Incident reviews
- Internal and external audits
- Analysis of historical risk patterns
- SWOT analysis (Strengths, Weaknesses, Opportunities, Threats)
2. Define the acceptable level of risk
After choosing the risk, set a clear objective for how much risk the organization is willing to tolerate.
Key measures:
- Compare risk severity against organizational risk appetite.
- Determine thresholds for financial loss, downtime, or compliance breaches.
Note: The outcome of these measures is documented in a risk register.
3. Prioritize risks
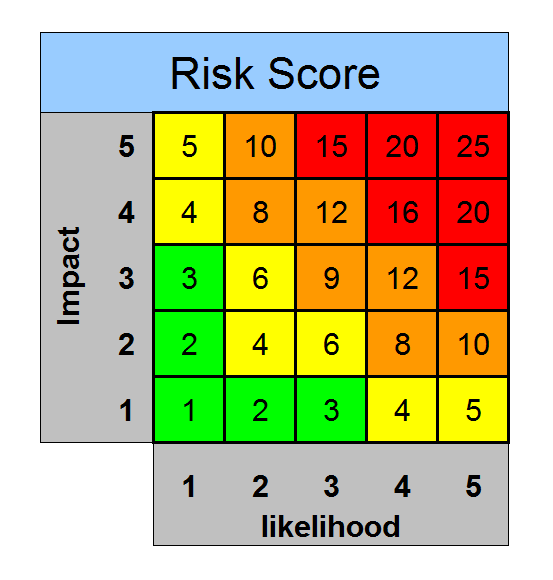
Rank the identified risks based on potential impact, likelihood, and available resources by assigning them a Risk Priority Number (RPN).
Key measures:
- Risk matrices: Visual heat maps to compare risk impact
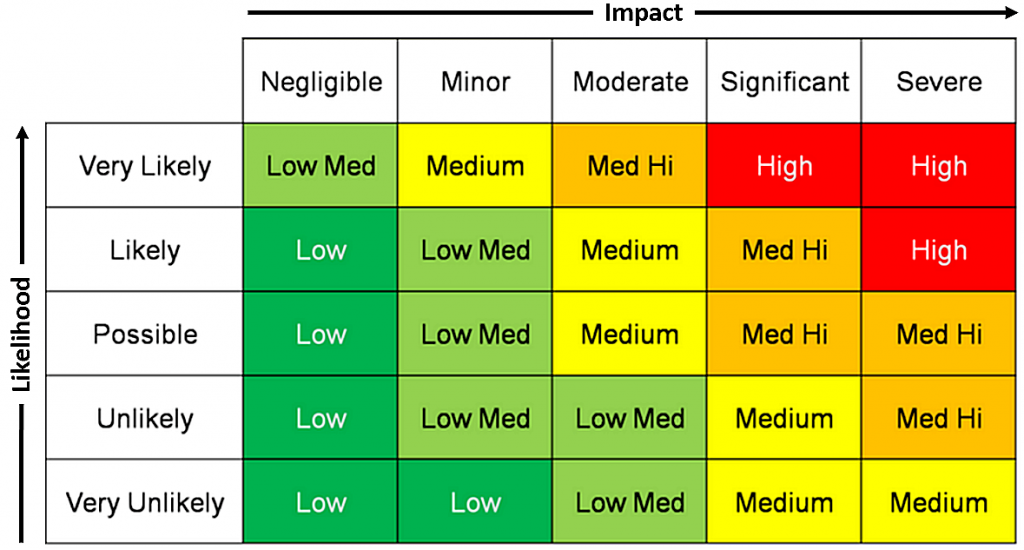
- Risk scoring: Numerical values to rank severity and urgency
4. Choose a mitigation strategy
Now, curate a plan of action and finalize a strategy or a combination of strategies:
- Risk avoidance: Stop activities that expose the organization to risk.
- Risk reduction: Implement controls to lower the likelihood or impact.
- Risk transfer: Shift the risk to another party via insurance or outsourcing.
- Risk acceptance: Decide not to mitigate if the impact is acceptable or mitigation is costly.
5. Apply specific mitigation controls
Implement concrete actions aligned with the chosen strategy. This is where risk mitigation becomes actionable.
Examples:
- Technical controls: firewalls, encryption, intrusion detection systems
- Procedural controls: employee training, compliance policies, monitoring processes
- Contractual controls: SLAs, insurance agreements, vendor risk clauses
6. Monitor and evaluate effectiveness
Track the mitigation plan’s results using risk management software to ensure risks are reduced as intended. Update the mitigation plan when risk levels change or new threats emerge.
Key measures:
- Review and update risk registers
- Use risk indicators and dashboards to measure impact
- Conduct periodic reviews, audits, and scenario testing
- Adjust controls or strategies based on feedback
Best Practices in Risk Mitigation
The key best practices for implementing a risk mitigation plan include:
Assign clear roles: Appoint a risk manager for a specific threat scenario who will be responsible for implementing mitigation strategies and reporting progress.
Strong communication: Establish a robust system where employees can quickly report warnings (big or small) to the cybersecurity team.
Risk-aware culture: Conduct regular workshops and awareness programs to educate employees about technology advancements and risk patterns. A risk-aware culture keeps staff and management aligned.
Leverage dedicated tools: Use specialized software for monitoring, documentation, and incident response. Tools like GRC platforms and aggregated monitoring dashboards improve accuracy, save time, and reduce human error in mitigation.
Validate strategies: Test mitigation measures by conducting mock drills to check their effectiveness. Update risk registers and track efficiency through audits and reviews.
Benefits of Risk Mitigation
Risk mitigation benefits aren’t just limited to anticipating and avoiding threats. When you implement well-structured mitigation frameworks, business operations become more resilient, and decision-making takes a productive leap.
The key benefits of risk mitigation include:
1. Competitive advantage
Demonstrating preparedness builds customer trust, accelerates opportunities, and secures a competitive edge in volatile markets.
2. Reduces risk severity
It reduces the likelihood of risks and keeps their impact manageable when they occur. For instance, strong cybersecurity protocols quickly neutralize threats at an early stage.
3. Planning agility
It enables organizations to translate risk insights into faster planning cycles, proactive resource realignment, and scenario-based adjustments as conditions evolve.
4. Streamlined communication
Effective risk management naturally promotes strong communication between teams and stakeholders. Smooth coordination during a crisis reduces confusion among engaged parties and ensures quick resolution.
5. Maintains compliance
Keeps the organization aligned with industry regulations, like GDPR and SOC 2. This ensures greater auditability, smoother reporting, and reduced risk of penalties or legal disputes during compliance checks.
Mitigate Risks with Sprinto
Risks aren’t rare; they are constant, evolving, and often interconnected. Identifying vulnerabilities early, allocating resources effectively, and building operational resilience lay a secure foundation for sustainable growth.
Sprinto simplifies and automates risk management and compliance. It strongly integrates with compliance frameworks such as GDPR, HIPAA, SOC 2, and ISO 27001. From running precise risk assessments to maintaining a centralized risk register, Sprinto empowers you to tackle risks confidently and visualize their impact.
The platform handles 80% compliance work with a comprehensive risk library, enabling businesses to stay secure, audit-ready, and resilient.
Ready to strengthen your security posture? Schedule a personalized demo today!
FAQs
1. What is the difference between risk mitigation and risk management?
Risk management is the framework for identifying, assessing, and controlling risks. Risk mitigation is a subset of this process that focuses specifically on reducing the impact or likelihood of risks.
2. How do I develop an effective risk mitigation plan?
To build an effective risk mitigation plan:
- Identify potential risks.
- Evaluate them and set priority based on their impact.
- Choose from avoidance, reduction, transfer, or acceptance.
- Assign clear roles.
- Regularly track progress and refine strategies.
3. How to Mitigate Risks?
Mitigate risks by identifying potential threats, assessing their severity, and applying measures such as transferring risk via insurance, avoiding risky activities, or accepting manageable risks with contingency plans in place.
4. What risk mitigation measures are required for SOC 2, ISO 27001, or GRC?
SOC 2, ISO 27001, or GRC require a risk-based approach and specific organizational controls. The key measures include:
- Incident response plan\
- Data encryption
- Access controls
- Continuous monitoring
- Documented policies
- Compliance with industry-standard frameworks
5. What’s the role of risk mitigation in business continuity planning?
Risk mitigation minimizes potential disruptions, such as cyberattacks and supply chain failures. It strengthens operational resilience, enabling critical operations to continue during and after a crisis.
6. How do I monitor the effectiveness of risk mitigation measures?
Track KRIs, conduct audits, review incident reports, and test mitigation measures. Moreover, risk registers should be updated to refine measures based on emerging risks and historical threat patterns.
Author
Sriya
Sriya is a strategic content marketer with 5+ years of experience in B2B SaaS, helping early- and growth-stage companies build and scale content engines from scratch. She specializes in long-form storytelling, thought leadership, and content systems that grow traffic and drive pipeline. Passionate about solving messy, early-stage challenges, she loves figuring out what to build, how to say it, and who it’s for.Explore more
research & insights curated to help you earn a seat at the table.





















