The significance of cybersecurity is growing. The world now depends on technology more than ever before, and there are no signs that indicate a possible reversal.
Organizations can no longer exclusively rely on standard cybersecurity solutions like firewalls and antivirus software. Hackers are consistently improving their strategies and are now able to easily penetrate traditional cyber defenses. To ensure continuous security, organizations need better planning and preparedness. A Cybersecurity Incident Response Plan is essential in this regard. It gives a structured approach to managing security breaches and ensures business continuity.
This blog is your quick guide to creating an incident response plan and understanding the incident response process.
TL,DR
- The CIRP is a documented set of procedures to help manage security incidents
- Organizations need a CIRP to respond proactively, minimize the damage, save reputation and stay compliant
- Incident response planning requires you to set objectives, appoint a team, set Standard Operating Procedures (SOPs) and communication plans and distribute the plan after testing
- The cybersecurity incident response process requires preparation, detection, containment, eradication, recovery and post-incident analysis
What is a Cybersecurity Incident Response Plan?
Cybersecurity Incident Response Plan is a documented set of procedures that help organizations prepare before incidents, investigate them during occurrence, and perform post-incident steps after the incident. The goal of incident response is to prevent cyberattacks from happening and to reduce the cost and disruption caused to an organization in the event of an attack.
Ideally, an organization establishes incident response methods and technology in a formal incident response plan (IRP) that outlines how various types of cyberattacks should be discovered, confined, and handled.
An efficient incident response strategy can assist cybersecurity teams in identifying and containing cyber threats, speeding up the restoration of compromised systems, and lowering other associated expenses such as lost profits and regulatory penalties.
Why do organizations need to have a Cybersecurity Incident Response Plan?
Organizations need to have a cybersecurity incident response plan to ensure a timely and well-coordinated response to incidents and minimize its impact. The plan is also required for regulatory purposes and is an important component of the overall risk management strategy.
Here are some reasons why CSIRP is essential for organizations:
Timely Response
A cyber security incident response plan helps organizations respond quickly and efficiently to cyber incidents. The plan outlines the roles and responsibilities of different stakeholders, such as IT staff, incident response team, and management, to ensure a coordinated and effective response.
By having a clear and structured plan, organizations can minimize the impact of a cyber attack and reduce downtime.
Minimize Damage
A cyber attack can cause significant damage to an organization, such as loss of data, reputation, and financial losses. A CSIRP provides a framework to manage the incident and minimize the damage. It includes procedures to contain the attack, identify the source, and remediate the issue. By having a CSIRP in place, organizations can quickly recover from an incident and resume normal operations.
Compliance
Many regulatory bodies and industry standards require organizations to have a CSIRP in place. For example, the General Data Protection Regulation (GDPR) mandates organizations to report data breaches within 72 hours. Failure to comply with these regulations can result in severe penalties and fines. A CSIRP helps organizations meet these compliance requirements and demonstrate their commitment to cybersecurity.
Sprinto’s compliance automation platform has readymade cybersecurity incident response procedure templates to eliminate the need to start from scratch. Sprinto also has an in-built incident management system and integrates with many such services to enable you to ensure faster threat detection and proactive address and deal with all types of security incidents. See Sprinto in action.
Continuous Improvement
A cyber incident response plan is not a one-time exercise. It requires regular testing, updating, and refining to ensure its effectiveness. By regularly reviewing and improving the plan, organizations can identify weaknesses and gaps and implement measures to strengthen their cybersecurity posture.
Let us now have a look at what goes on in creating a Cybersecurity Incident Response Plan.
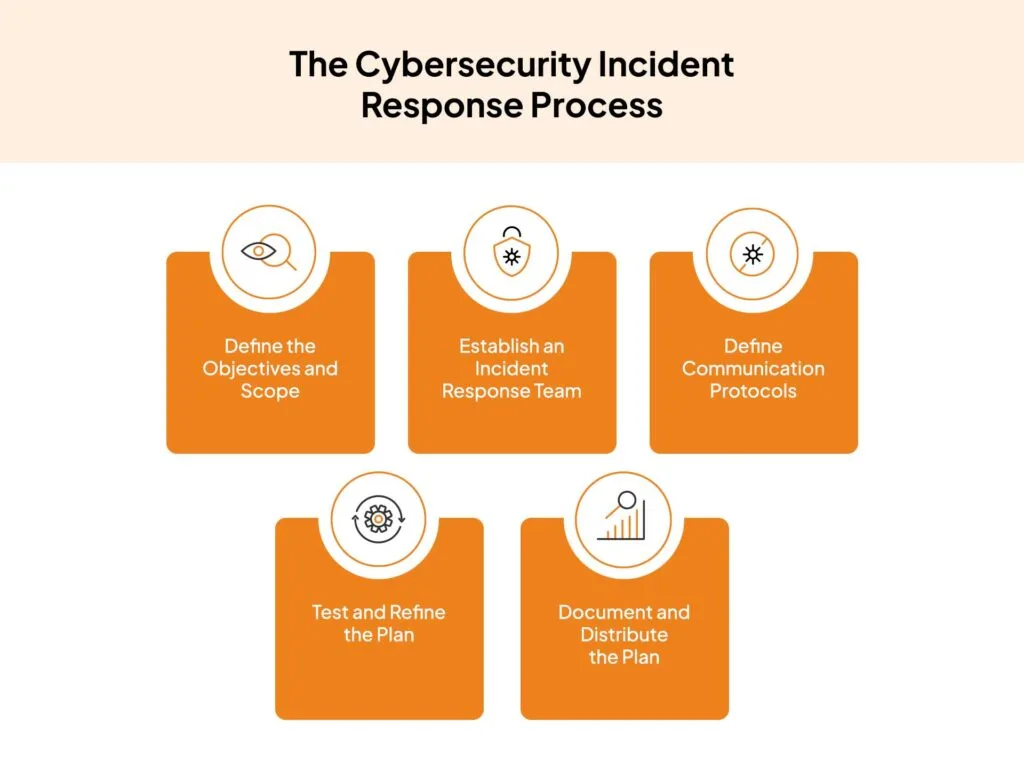
How to create Cybersecurity Incident Response Plan?
The needs of your company will determine every step of how you’ll create your incident response plan, including how big your company is, how many employees you have, how much sensitive data you keep on hand, etc. But, we’re going to offer some general advice that would be useful for almost any type of organization creating a cyber incident response strategy.

Here are the 7 steps cybersecurity incident response plan:
1. Define the Objectives and Scope
Start by defining the objectives and scope of the CSIRP. Identify the systems, assets, and data that need to be protected and the types of incidents that the plan should cover. This will help you focus on the most critical areas and create a targeted plan.
2. Establish an Incident Response Team
Create an incident response team comprising stakeholders from different departments, such as IT, legal, communications, and management. Define their roles and responsibilities and provide them with the necessary training and resources to carry out their tasks effectively.
3. Develop Incident Response Procedures
Develop procedures for responding to different types of incidents, such as malware attacks, phishing scams, and data breaches. Include steps for identifying and containing the incident, notifying the appropriate stakeholders, and restoring systems and data.
4. Define Communication Protocols
Establish communication protocols for different scenarios, such as notifying internal teams, external stakeholders, and regulatory authorities. Define the channels for communication and the level of information to be shared.
5. Test and Refine the Plan
Test the CSIRP regularly through various methods such as:
- Simulations: These drills simulate real-world attacks and test the response capabilities of the team in complex situations
- Tabletop exercises: Tabletop exercises are discussion-based exercises where the members talk about their responsibilities during a hypothetical incident scenario
- Red-team exercises: Red-team exercises are conducted by hiring external professionals that use a wide range of tactics to challenge the organization’s defense capabilities and test the response.
Use the findings and feedback of these exercises to understand what is working and what are the gaps in response. The incident response plan must be updated accordingly to ensure future enhancements.
6. Document and Distribute the Plan
Document the CSIRP and distribute it to all relevant stakeholders. Ensure that everyone is aware of their roles and responsibilities and understands the procedures and communication protocols.
7. Review and Update the Plan
Review the CSIRP regularly and update it as needed to reflect changes in technology, systems, and threats. Make sure the strategy is up-to-date and efficient.
Apart from these, it is essential to know how a Cybersecurity Incident Response Plan works. Let’s have a look at the same in the next section.
Ensure faster threat detection and proactive mitigation with Sprinto
The Cybersecurity Incident Response Process
On the basis of incident response models created by the SANS Institute, the National Institute of Standards and Technology (NIST), and the Cybersecurity and Infrastructure Agency (CISA), most IRPs likewise adhere to the same broad incident response framework.
Preparation
This first stage of incident response is ongoing to ensure that the CSIRT always has the best policies and resources available to respond to incidents as rapidly as possible with minimal business disruption
The Cyber Incident Response Team must regularly assess security risks to identify network vulnerabilities, categorize the different security incidents that could endanger the network, and assign a priority to each category based on the likelihood that it would have an adverse effect on the organization. The CSIRT may revise current incident response plans or create new ones in light of this risk assessment. Sprinto can help simplify the workload of CSIRT team with quantitative risk assessments so they can identify risks unique to the business, prioritize them better and manage them systematically.
Detection and Analysis
Members of the security team keep an eye on the network throughout this stage for any unusual activity or potential threats. They examine information, notifications, and alerts obtained from device logs and from various security technologies (firewalls, antivirus software), which are deployed on the network. They remove false positives and rank the true alerts according to their seriousness.
When the CSIRT team identifies suspicious activity such as unauthorized access or malware, it will notify the reporting point of contact for further action.
Containment
The incident response team takes action to prevent the breach from causing the network additional harm. There are two types of activities in the containment phase:
- Short-term containment strategies concentrate on isolating the affected systems to stop the current threat from spreading, such as by taking infected devices offline.
- Long-term containment methods put further security protections around unaffected systems to protect them, like separating sensitive databases from the rest of the network.
In order to minimise further data loss and to gather forensic evidence of the incident for further investigation, the CSIRT may also, at this point create backups of both affected and unaffected systems.
Eradication
The team then moves on to complete the cleanup and removal of the threat from the system once it has been contained. In order to do this, the threat must be actively eliminated (e.g., by destroying malware or kicking an unauthorised or rogue user off the network). Affected and unaffected systems must also be examined to make sure no evidence of the breach is still present.
Recovery
The impacted systems are returned to regular operation after the incident response team is certain that the threat has been completely eliminated. The recovery phase could entail applying updates, reconstructing systems from backups, and reactivating repaired systems and devices online.
Post-incident analysis
The CSIRT gathers evidence of the breach and records the steps it takes to contain and eliminate the threat during each stage of the incident response process. The CSIRT now examines this data to comprehend the situation more fully.
In order to prevent similar occurrences from happening in the future, the CSIRT aims to identify the attack’s primary cause, pinpoint how it successfully infiltrated the network, and fix any vulnerabilities.
In order to reinforce incident response measures against future assaults, the CSIRT also evaluates what went well and looks for chances to improve systems, tools, and processes. Law enforcement may also be involved in the post-incident inquiry, depending on the specifics of the breach.
Manage and track incidents throughout their lifecycle within a single interface.
Sprinto’s take on CSIRP
With the increasing dependence on technology, cybersecurity has become crucial for organisations as cybersecurity incidents are becoming more common. A CSIRP helps organizations respond quickly and efficiently to cyber incidents, minimize the damage caused, comply with regulations, and continuously improve their cybersecurity posture.
Developing a Cybersecurity Incident Response Plan involves defining the objectives and scope, establishing an incident response team, developing procedures, defining communication protocols, testing and refining the plan, documenting and distributing the plan, and reviewing and updating it regularly.
With the right CSIRP in place, organizations can be better prepared to handle cybersecurity incidents and reduce the impact of cyber attacks. That said, you can get in touch with our industry-leading experts who can cut down your compliance time by 70%-90% depending on your framework.
FAQs
What are the 8 basic elements of an incident response plan?
The eight basic elements of an incident response plan are Preparation, Identification, Containment, Eradication, Recovery, Investigation, Notification, and Post-incident activities. With all of these in place, companies can handle cybersecurity incidents well.
What is a good incident response plan?
A good incident response plan is a comprehensive and tested set of procedures that enables an organization to quickly and effectively respond to and recover from security incidents and other disruptions. It should include clear protocols for identifying and reporting incidents, containing and eradicating them, and restoring normal operations, as well as regular training and testing to ensure its effectiveness. Additionally, it should be regularly reviewed and updated based on lessons learned from past incidents.
What is the incident response in SOC?
Incident response refers to the process of quickly identifying, analyzing, and responding to security incidents within an organization’s network or systems. This involves following a predefined set of procedures to contain and eradicate the incident and restore normal operations as quickly as possible.
Author
Shivam Jha
Shivam is our in house cybersecurity sage with over six years of experience in cybersecurity under his belt. He is passionate about making the digital world safer for everyone and whipping up Indian delicacies on the weekend.Explore more
research & insights curated to help you earn a seat at the table.





















