Maintaining a secure environment has become the top priority with the increasing volume of malicious attacks on business processing user card data. The (Payment Card Industry Data Security Standards) PCI DSS compliance, though not legally mandated, is a globally accepted security standard for businesses processing transactions either in physical or digital form.
This article focuses on the best practices for PCI DSS Compliance that you can follow to remain compliant.
Before we dive deeper and learn how to implement best practices of PCI DSS, let’s do a quick recap of what PCI DSS is, its levels, and what you’d need to do to remain compliant according to the specifics of your business.
What is PCI DSS?
In 2004, the giants (VISA, Master Card, American Express, JCB International, and Discover Financial) of the payment card industry came together and proposed a security standard to ensure data integrity of user card information. This laid the foundation for what we know today as the PCI-DSS compliance framework.
Being PCI DSS compliant allows businesses to showcase their security standards, and policies and procedures to ensure data security. It also instils confidence in users to share their sensitive data with companies and be assured of its safety.
The cost of non-compliance is also a huge motivator for businesses to be on the right side of maintaining compliance. A single incident caused due to non-compliance could cost a business over $500,000, broken relationships with card merchants, increased audit requirements, make them vulnerable to lawsuits, and cause irreparable damage to their brand equity.
Must check: The Ultimate PCI DSS Compliance Checklist
Also check out this video on what’s new in PCI DSS 4.0:
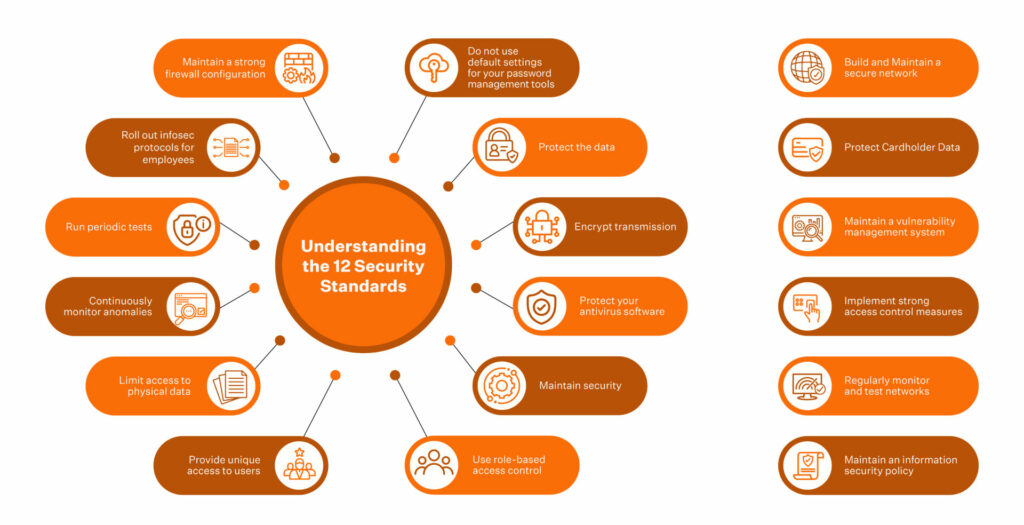
The PCI DSS best practices discussed in this article will add a layer of protection, and reinforce the Six Goals and Twelve Requirements recommended in the framework.
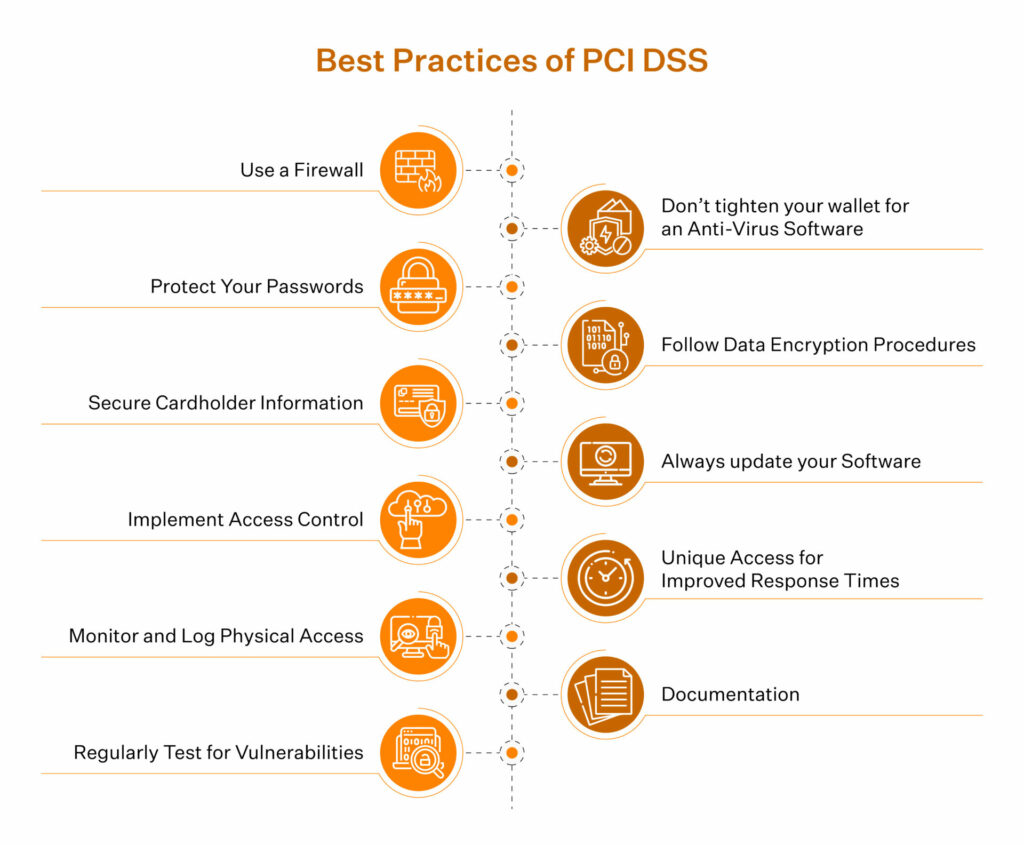
PCI DSS Best Practices
Among the 12 best practices of PCI DSS, what you prioritize will depend on the nature of your business’ processing and where it is classified against the PCI DSS levels.
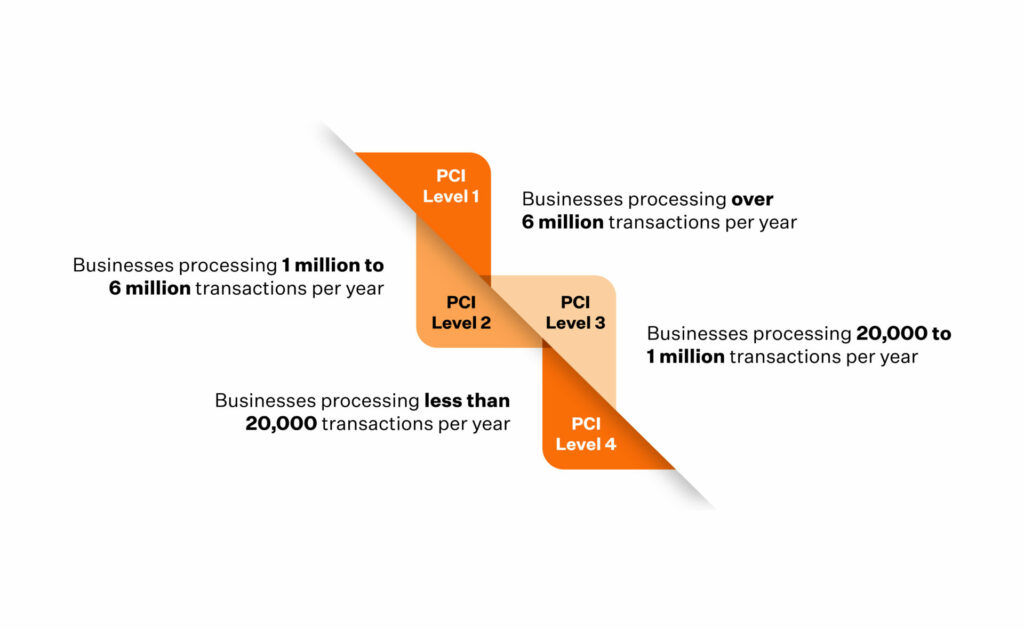
Level 1 is when you process less than 20,000 transactions/yr. As your level increases, the risk of your business becoming a victim of a data breach incident becomes higher. To compensate for the business risk, you must accommodate methods and policies equipped to handle the increased risk.
Best Practices of PCI DSS
It is essential to take this article with a pinch of salt. Why? Because even as we speak, the means to defend against a breach and new ways to break encryption models are being created. So, while this is not the ultimate list, it is an excellent start if you are becoming PCI DSS compliant or looking for methods to strengthen your existing compliance posture and adding an extra layer of security.
Use a Firewall
It’s a no-brainer that you would need a firewall. The firewall configuration is what changes the game.
Here are a few things you could do in this context.
- Always have the upgraded version of the software running in your business environment
- Remove default accounts and make it mandatory not to use default passwords. The new passwords must contain special characters, numerals, and uppercase letters. A better way to do this would be to use an offline password generator
- Always have dedicated accounts for employees who require secure access to the databases. Never share passwords/accounts
- Disable or configure a simple network management protocol (SNMP) to use a secure community string
Also check: 8 Steps to Get PCI Compliance for Small Business
Don’t tighten your wallet for an Anti-Virus Software
Requirement 5 discusses the need for Anti-Virus software to detect and delete malware from secure networks. While many free antivirus solutions are available to tick the box and keep the costs low, it is essential to know that the small price you pay towards getting a subscription from a reliable antivirus solution provider could save you millions of dollars in lawsuits and penalties.
McAfee, Kaspersky, ESET, and Cloud Security Storage are a few vendors you could get a quote from.
Protect Your Passwords
The scope of this one does not limit to the best practices for PCI DSS. You can also apply this in any other phase of your business environment and use it when going for SOC 2 or GDPR.
The best practice is using a password manager solution and clearing unreliable plugins.
Follow Data Encryption Procedures
Every payment card transaction has multiple touch points before it reaches the source and is marked ‘complete’. Securing data across these touch points using encryption models is one of the requirements of PCI DSS.
One of the PCI DSS 3.2 best practices in the context of encryption is using encryption methods recommended by NIST (National Institute of Standards and Technology). Here are a few best practices for encryption:
- Establish dual control: No one user alone can make critical changes in your production environment/secure servers
- Don’t store encryption keys at a single location. Split and store parts of the encryption keys at several secure locations.
- Use AES and PGP Encryption models
Secure Cardholder Information
The use of encryption should not be limited to the internal environments of your organization. Using tokenization and pseudonymization models to encrypt and protect cardholder data during transmission dramatically reduces the risk of a data breach.
Always update your Software
Software updates, though time consuming, play a critical role in ensuring that you are protected from an incident. When a service provider rolls out a software update, they often include crucial bug fixes and improvements that aim to strengthen the application’s ability to tackle a breach.
Here are the best PCI DSS compliance softwares
Implement Access Control
Sensitive cardholder data should only be accessible by those in your organization whose roles require it.
For example, an employee from the Human Resources team does not need access to payment card data. Still, an analyst needs access to the said data to make projections on the future road map by extrapolating from the current and past data sets.
Unique Access for Improved Response Times
Sharing unique IDs and passwords across employees in an organization makes it difficult to follow the events to pinpoint the cause/vulnerability in the event of a breach.
With unique IDs, you can avoid this confusion and immediately head straight to the source to deploy time-sensitive security patches. This helps you reduce your response time, thus letting you get your systems up and running quickly.
Good read: A Detailed Evaluation of PCI DSS Certification Cost
Monitor and Log Physical Access
Like digital data, access to physical data must also be restricted to authorized personnel. Using monitoring devices, RFID for entry, USB-free zones (if applicable), and shredding any paper storage with cardholder data immediately after use is recommended. Restrict access wherever applicable.
Documentation
Documentation is a critical PCI security requirement. Documenting your processing activities not only helps you be on the right side of PCI compliance but also helps as a roadmap to identify the source of a breach and do the patchwork required. Simply put, your incident response mechanism improves.
Regularly Test for Vulnerabilities
Hackers and bad actors are looking for vulnerabilities in businesses to exploit them for ransom, damage reputation, etc. Before a hacker finds the vulnerabilities in your environment, it is better that you beat them to it and fix it.
Vulnerabilities are common, and there is no single solution to fix them. So, conduct periodic scans and tests for vulnerabilities and fix them to stay ahead in the game.
Understand the real intent and Implement Best Practices of PCI DSS
Most businesses treat complying with PCI DSS compliance as a thing to strike out in their checklist of things to do by following a few PCI DSS implementation best practices. But, PCI DSS certification is much more complicated than that and requires business leaders to approach it with genuine determination and interest, especially if they take the DIY route. A certain amount of security awareness is a prerequisite.
Having know-how of your business environments, cloud subscriptions, storage units, touch points in the life cycle of cardholder data, and route maps of transactions becomes essential.
Keeping your cardholder data secure from the constantly improving penetration models of hackers requires that you spend the time and effort to keep up with the market and deploy solutions that are up to date and promise a vision of security.
The Scope of PCI is not just about deploying the legal and infrastructural (physical + technical) measures to become compliant. It is also about promoting a security-first culture.
How can Sprinto Help With The Best Practices to Insure PCI DSS Compliance?
Sometimes implementing compliance-related controls and policies is easier said than done. We understand that. To simplify this, our solution presents the perfect blend of automation and human involvement. This empowers us with the ability to help you seamlessly breeze through your compliance journey without compromising your business development and continuity plans. Talk to us today to see how we can make your PCI DSS compliance journey a breeze!
Author
Vimal Mohan
Vimal is a Content Lead at Sprinto who masterfully simplifies the world of compliance for every day folks. When not decoding complex framework requirements and compliance speak, you can find him at the local MMA dojo, exploring trails on his cycle, or hiking. He blends regulatory wisdom with an adventurous spirit, navigating both worlds with effortless expertiseExplore more
research & insights curated to help you earn a seat at the table.