TL;DR
| The ISO 27000 series of standards provides a framework for establishing, implementing, and maintaining information security best practices. If you’re wondering where to start: – Use ISO 27017 / 27018 if cloud and data privacy matter heavily – Start with ISO 27001 if you want certification – Use ISO 27002 for control guidance – Use ISO 27005 for risk management |
With data breaches on the rise, more businesses are seeking vendors who can protect their sensitive data. To provide that guarantee, you need to maintain the highest security standard. And the ISO 27000 series is a good starting point.
The ISO 27000 is a series of information security standards that help ensure that your organization has appropriate safeguards in place to mitigate risks and build a robust Information Security Management System (ISMS).

In this article, you will learn what ISO/IEC 27000 standards are all about, why they are important, and what each standard of the family is concerned with.
What is ISO/IEC 27000 series of standards?
ISO/IEC 27000 is a series or a family of standards published by the International organization for Standardisation (ISO) and the International Electrotechnical Commission (IEC) . Also abbreviated as ‘ISO27K’, it combines a range of information security standards to form a comprehensive framework to help organizations strengthen their information security management system (ISMS).
The series begins with ISO/IEC 27000, which provides a glossary of key terms essential to the ISMS. It is followed by a variety of standards, each addressing a specific aspect of information security. For example, ISO/IEC 27001 outlines the foundational requirements for designing and implementing an ISMS, ISO/IEC 27005 focuses on risk management, and ISO/IEC 27017 offers guidelines for cloud services.
The series provides a structured framework with implementation guidance to protect sensitive information, meet regulatory requirements, and build market credibility.
Understanding the categorization of the ISO 27000 series
The ISO 27000 family of standards can be broadly classified into four categories of standards based on its function. Each has a purpose and can be normative or informative.
Normative elements are used to describe the scope of each standard and how to comply with it. These elements include recommendations, requirements, and possibilities.
Informative elements are descriptive in nature and help to understand the concepts. It provides context, background, additional recommendations, and relation with other elements.
Only the normative standards can be audited for compliance.
| Purpose | Standard Name | Type |
| Overview and terminology | ISO 27000 | Informative |
| Requirements | ISO 27001, ISO 27006, ISO 27009 | Normative |
| General guidelines | ISO 27002, ISO 27003, ISO 27004, ISO 27005, ISO 27007, ISO 27013, ISO 27014, ISO 27021, TR 27008, TR 27016 | Informative |
| Sector-specific guidelines | ISO 27010, ISO 27011, ISO 27017, ISO 27018, ISO 27019 | Informative |

List of ISO 27000 series of standards
The ISMS family of standards are interrelated and focus on ISMS requirements. Here’s a summary of what each describes and is concerned with:
ISO 27000 – Information Security Management Systems
ISO 27000 provides an overview, definitions, and introduction to the ISMS family of standards. This family of standards work together to help organizations efficiency manage their digital assets.
ISO 27001 – Information security, cybersecurity, and privacy protection
Concerned with normative requirements to develop, implement, monitor, manage, and operate ISMS, it helps with controls to mitigate risks associated with data assets specific to your business needs. It details a set of controls and control objectives from Annex A that you must select as part of your ISMS to meet its requirements.
Case Study
Find out how Equalture got ISO 27001 compliant and increased sales velocity
ISO/IEC 27001:2013 has now been updated and named ISO/IEC 27001:2022. Check what’s new.
ISO 27002 – Information security, cybersecurity and privacy protection
ISO 27002 guides organizations to select and implement common information security controls to bolster their information security. It provides best practices and guidance to implement, establish, and improve your ISMS. Additionally, ISO/IEC 27002 outlines the practices related to cybersecurity, such as access control, incident response, and effective threat management.
ISO 27003 – Information security management system implementation guidance
ISO 27003 explains and guides how to implement ISMS as per ISO 27001 successfully. It helps users analyze organizational issues, meet stakeholder expectations, develop policies, determine ISMS scope, manage risks, and evaluate ISMS performance.
Sprinto Advantage
Sprinto helps you implement, manage, and monitor a tightly integrated pipeline of controls and automated checks. It consolidates risks, controls, and checks from a single console. See Sprinto in action.
ISO 27004 – Information security management — Monitoring, measurement, analysis and evaluation
Guides and assists organizations in evaluating and measuring the performance of ISMS to fulfill ISO 27001:2013, 9.1 requirements. Applicable for organizations of all sizes and type, ISO 27004 covers how to:
- How to monitor and measure ISMS performance
- How to monitor and measure the effectiveness of ISMS processes and controls
- Analyze and evaluate the result of ISMS monitoring and measurement
ISO 27005 – Guidance on managing information security risks
Guides organizations to implement risk management processes as per ISO 27001 to address security risks and perform risk assessments and risk treatment. This standard applies to organizations of all types and sizes. The latest edition was released in 2022.
ISO 27006 – Requirements for bodies providing audit and certification of ISMS
Provides guidance and specifies requirements to organizations that offer auditing services and ISMS certification as per ISO 27001. These service providers must demonstrate competence and reliability in keeping with ISO 17021 requirements.
Auditors offering certification services must familiarize themselves with the controls, requirements, terminology, principles, references, and legal mandates of ISO 27001 and 27002. They should know how to monitor, measure, evaluate, and analyze ISMS and the technicalities of auditing systems.
ISO 27009 – Information technology — Security techniques — Sector-specific application of ISO/IEC 27001 — Requirements
Outlines requirements to create standards in a specific sector by extending iso 27001 and complementing iso 27002. It also specifies how to
- Interpret and include the requirements of ISO 27001
- Include controls that are not mentioned in ISO 27001 and 27002
- Modify controls mentioned in ISO 27001 and 27002
- Modify the guidance of ISO 27002 or update it
ISO 27007 – Guidelines for information security management systems auditing
Guides organizations to conduct ISMS audits and discusses the competence of ISMS auditors as per ISO 27001. The document complements ISO 19011 and applies to those looking to conduct internal or external ISMS audits or manage an ISMS audit program.
ISO 27013 – Guideline on the integrated implementation of ISO/IEC 27001 and ISO/IEC 20000
Guides organizations that intend to
- Implement ISO 27001 when ISO 20000-1(standard for service management system) is already in place or implement the latter (ISO 20000-1) when ISO 27001 is in place
- Implement both ISO/IEC 27001 and ISO/IEC 20000-1 together
- Integrate their management systems as per ISO/IEC 27001 and ISO/IEC 20000-1
- It also helps organizations understand the similarities and differences between these two.
ISO 27014 – Governance of information security
Guides users on the principles, goals, and processes to govern information security in a way that enables them to evaluate, monitor, measure, and communicate ISMS processes to stakeholders within the organization.
The ISO 27014 document aims to guide top management in an organization, governing bodies, and individuals responsible for ISMS management and evaluation based on ISO 27001 to meet the governance aspect.
ISO 27021 – Competence requirements for information security management systems professionals
Intends to help a number of entities, such as:
- Individuals who wish to demonstrate their competence as ISMS professionals or gain the knowledge needed to work in this field
- Organizations hiring ISMS professionals
- Bodies that certify ISMS professionals
- Organizations or institutes that offer courses to educate or train candidates for ISMS
ISO TS 27008 – Guidelines for the assessment of information security controls
Previously ISO/IEC TR 27008:2011, this document guides organizations to review and assess the effectiveness of information system controls in keeping with the specific obligations of the business.
It is applicable for organizations of types and sizes like public companies, private firms, government bodies, non-profit organizations, and others.
TR 27016 – information security economics
Enables organizations to make informed decisions on the assets while ensuring economic sustainability and gaining insight into the economic consequences of their decisions. This guideline centers around infosec economics, which impacts the demand and supply of goods and services.
The target reader for this guideline is the executive management responsible for strategizing the allocation of resources to support control implementation.
TR 27016 helps businesses reduce the negative impact to their objectives, reduce the impact of financial losses, meet legal obligations, manage customer expectations, improve brand reputation, and deliver accurate financial reports.
ISO 27010 – Information security management for inter-sector and inter-organizational communications
Guides and provides controls to initiate, implement, maintain, and improve information security with other organizations and sectors. It specifies the principles to meet the requirements through various technical processes. This document is designed to ensure trust while exchanging any form of data and sensitive information so that it boosts international growth.
ISO 27011 – Information security management guidelines for telecommunications organizations
Helps telecommunication organizations to implement information security controls. It helps them meet security management requirements like integrity, confidentiality, and availability. The guidelines of this document are based on the controls and objectives of ISO 27002.
ISO 27017 – Code of practice for information security controls for cloud services
Guides cloud service providers to implement security controls as per and in addition to ISO 27002. ISO 27017 is aimed at cloud service customers looking to implement the controls as well as cloud service providers to support the control implementation.
ISO 27018 – Code of practice for protection of PII in public clouds acting as PII processors
Establishes control objectives, controls, and guidelines to protect personally identifiable information (PII) for cloud computing as per ISO 29100. It aims to combine the controls objectives of ISO 27002 to create security controls that can be implemented by cloud service providers who qualify as a PII processor.
Public cloud PII processors can use ISO 27018 to comply with relevant obligations, ensure transparency with their customers, enter contractual agreements without hassle, and meet audit requirements if they host data in a risky environment.
ISO 27019 – Information security for process control in the energy industry
ISO 27019 applies to process control systems used by the utility industry and guides them to control and monitor the production, transmission, distribution or generation of energy. It includes:
- Technology for process control, monitoring, automation, and its supporting infosec systems
- Digital controllers and automation systems
- Components of Advanced Metering Infrastructure (AMI)
- Technologies used for communication, such as networks, telemetry, and remote control devices
- All information systems that support process control domain
No matter which standard from the ISO 27000 series you are looking to implement, Sprinto helps you ease the burden by consolidating risks, checks, and assessments from a single place. You can:
- Integrate your cloud stack to automatically identify, classify, and manage risks based on category, severity, and criticality.
- Review and enhance your ISMS any 27k standards using automated checks and real-time monitoring. Continuously monitor controls from a centralized dashboard.
- Engage an accredited Sprinto partner auditor for certification, leveraging automated evidence collection to demonstrate compliance.

How to get certification for ISO 27000 family of standards?
There is no such thing as an ISO 27000 certification. The series only provides a framework and vocabulary for information security and the certification is achieved through ISO 27001 which is the core standard in the series.
As for other standards, you can align and comply with them but the certification is achieved only for ISO 27001.
To get ISO 27001 certification:
- Familiarize yourself with the requirements of ISO 27001 and conduct a gap analysis to compare your current information security processes against the standard.
- Design and deploy an ISMS aligned with the ISO 27001 requirements and provide training to your staff.
- Conduct internal audits to ensure that the controls are working as intended and fix any issues.
- Select an accredited certification body and go through the audit— stage 1 is documentation review and stage 2 is an on-site audit
- Ensure ongoing compliance and address non conformities proactively to remain prepared for recertification audit.
Download Your Gap Analysis Template
How ISO 27000 series of standards streamlines security management
Managing information security without a structured framework makes your effort disconnected and disorganized. Here’s why you should use an internationally recognized standard to manage your ISMS.
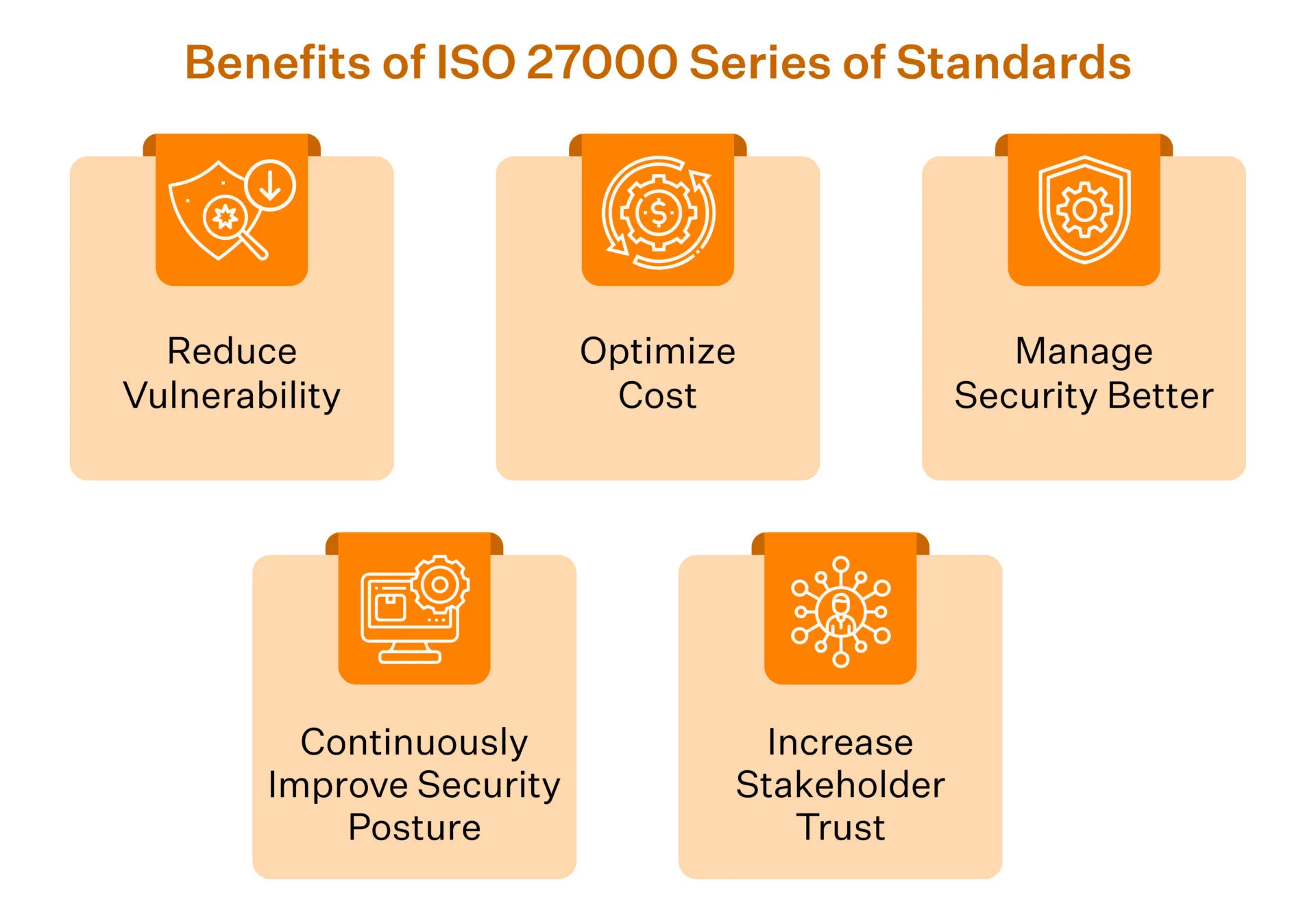
- Reduce vulnerabilities: When you implement ISMS, it reduces vulnerabilities across your IT infrastructure. It enables you to gain sustainable security success.
- Optimize cost: It is a structured framework that helps you implement and maintain a comprehensive and cost-effective process across all operations.
- Streamline security management: It assists you to manage security holistically and responsibly through better education and training.
- Enhance security management: When you implement an internationally accepted standard of security, it gives you the flexibility to continuously improve controls to keep up with dynamic security needs.
- Boost customer and stakeholder trust: It empowers you to manage information security in an economical way and increases stakeholders’ trust.
Streamline ISO 27001 with the help of ISO 27001 compliance checklist.
Why should you implement ISO 27000 standards?
ISO 27000 series of guidelines provide a framework for your organization to assess risks and implement custom security protocols. But it does more than provide guidelines – you gain a host of benefits.

1. Highlights gaps in security management
As a business owner, you may assume that your organization’s functions and the process you adopted are the right way and make sense to you. This is called paradigm blindness and prevents businesses from overcoming challenges.
Implementing new controls and systems may seem difficult at first. But knowing your security status highlights existing gaps and encourages you to fix those. ISO 27000 series of standards helps your organization to identify gaps, eliminate roadblocks, discover growth opportunities, and manage better.
For example, the ISO/IEC TR 27008 document guides users to implement and check the operation of controls against the already established infosec standards. This will inevitably surface your gaps and enable you to fix those. As a result, you can improve your security posture and performance.
Check out how to perform ISO 27001 gap analysis
2. Prevents costly incidents
Breaches don’t just cost you money – they cost you your reputation. Damage control is time-consuming and a hassle nobody wants. The solution? Buckle up your security. The benefits of a strong security posture outweigh the cost of implementing it, especially in the long run.
ISO 27001 helps you develop controls necessary to mitigate risks within your organization. ISO/IEC 27005 provides a comprehensive guidance on risk assessment. You can use these to identify malicious behavior and mitigate them before it affects your system.
As malicious actors become smarter, so should your IT infrastructure. With the number of breaches rising, you can no longer afford to consider security as an optional investment.
3. Gives competitive advantage
Businesses don’t want their data mishandled or tampered with – they want a trustworthy partner. ISO 27001 is an internationally accepted security standard that is a great way to establish trust. An industry respected standard helps you efficiently manage third party financial data and intellectual property. It shows that you take data security seriously.
Note:
A survey conducted by ISO in 2021 shows that more than 10000 information technology companies were ISO 27001 certified in 2021.
When you are compliant, and your competitors are not, sales prospects are more likely to partner with you.
Automate your ISO compliance with Sprinto
Compliances are complicated and confusing, but they don’t have to be. Sprinto offers an automated solution that uncomplicates your compliance journey. It takes care of every manual task – from policy creation to mapping security controls and overseeing gaps in security posture.
Sprinto also offers an in-app staff security training and tracking feature that helps your employees stay educated and updated on the latest in cybersecurity as well as fend off breach attempts, such as phishing.
Wondering how much ISO 27001 certification would cost you? Have more questions? Book a demo with us to learn more about how we can make your compliance journey hassle-free.

FAQs
The principles of ISO 27000 revolve around information security and information risks through the appropriate implementation of controls of your ISMS (Information Security Management System)
ISO 27001 is the central standard to the series of ISO 27000 family. ISO 27000 provides the foundational framework and terminology for infosec management, while ISO 27001 specifies the requirements for implementing an ISMS.
As of 2022, there are a total of 63 published standards and substandards in the ISO 27000 family. The International Organization for Standardization continuously adds new standards, so this number is subject to change.
Author
Anwita
Anwita is a cybersecurity enthusiast and veteran blogger all rolled into one. Her love for everything cybersecurity started her journey into the world compliance. With multiple certifications on cybersecurity under her belt, she aims to simplify complex security related topics for all audiences. She loves to read nonfiction, listen to progressive rock, and watches sitcoms on the weekends.Explore more ISO 27001 articles
ISO 27001 Overview & Requirements
ISO 27001 vs Other Frameworks
ISO 27001 Audit & Certification Process
ISO 27001 Management & Assessment
ISO 27001 Implementation & Automation
ISO 27001 Industry-Specific Applications
research & insights curated to help you earn a seat at the table.











