The digital landscape has gone through wave after wave of change, and compliance has evolved right alongside it. Over the years, what was once a static checklist has turned into a moving target, shaped by new technologies and rising risks.
And while proof has always been part of compliance, it’s now more important than ever. It’s no longer enough to say the right policies exist or that controls are in place. Businesses are expected to show clear, verifiable evidence that their programs actually work. And enforcement is making that expectation real, pushing organizations to back up their claims with tangible practices or face serious consequences.
To understand what this new reality looks like, we talked to two experts in the field: Eric Madden, President of Astute Technology Management, and Scott Ehrman, the firm’s Virtual CIO.
With decades of experience helping companies align security goals with day-to-day operations, they shared practical insights on what companies need to do to stay ahead and the consequences of failing to do so.
Proof or penalty
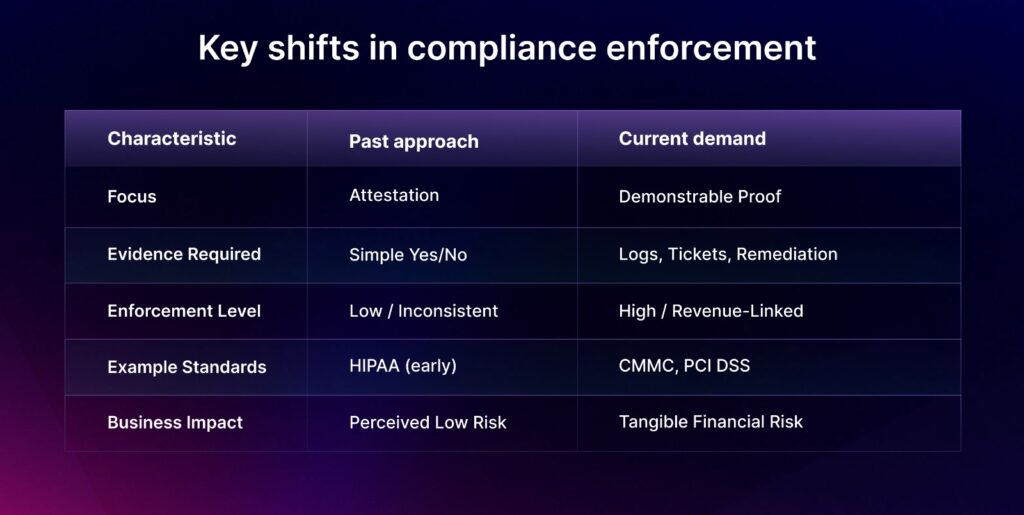
There was a time when simply having a policy was enough. You would check boxes, pass an audit, and move on. Not anymore.
Scott Ehrman, who has guided many companies through audits, sees this change clearly:
“It used to be, ‘Do you have a process?’ Now it’s, ‘Show me how you’re enforcing it.’ That shift, requiring tickets, logs, and proof of action, is catching many businesses off guard.”
PCI DSS, which was once relatively easy to achieve, now needs documented proof of vulnerability scans and evidence that you acted on your findings. HIPAA, once seen as a “speed limit with no cops,” is finally getting enforcement. Interestingly, the growing demand for cybersecurity services has established a clear link between compliance and revenue growth.
Lose compliance, and you lose contracts. What was once an IT concern is now a boardroom imperative. As Eric Madden puts it, “Businesses make decisions based on financial risk. And now, non-compliance is a financial risk.”
Why compliance still feels broken: where companies fall behind

Compliance may be more urgent today, but it hasn’t become easier. Even when the stakes are sky-high, many businesses still struggle to keep up due to a lack of resources or processes in place.
Budget vs. reality
For most small and mid-sized businesses, security and by extension, compliance ends up competing for resources against revenue-driving initiatives. Scott Ehrman notes, “They understand the risk. But security often gets treated as an afterthought, something they know they need but would rather spend elsewhere.”
This means they often overlook the long-term benefits of compliance over the short term costs.
The result? Last-minute scrambles during audits, unplanned expenses, and a reactive mindset that offers little room for strategy.
The talent bottleneck
Hiring is complicated, given SMBs don’t just need a cybersecurity expert, but someone who can handle a variety of tasks. “The person who can manage help desk support and advanced cyber policy? That unicorn doesn’t exist anymore,” says Scott.
The specialization of the workforce has made it harder to find generalists, leaving lean teams overstretched and vulnerable.
Confusion over responsibility
Another blind spot is who’s actually responsible for compliance. Many businesses assume their Managed Service Provider (MSP) covers it. But as Scott notes, “Clients think we’re handling certain things, but in reality, those are internal processes they need to define and document.”
This gray area becomes a problem fast when auditors arrive.
The growth trap
The faster a company grows—new users, new systems, and new customers—the easier it is for its security to fall behind. Without strong documentation and clear ownership, security efforts will always be fragmented.
A manageable 10-person team can quickly turn into chaos when improperly scaled to a 100-person team.
How businesses can maximize their security investment
When resources are limited, as they almost always are, businesses need to make deliberate, high-impact choices. The good news is that a handful of smart security measures can deliver outsized protection:
Start with the first line of defense
If there’s one thing every business should have implemented by now, it’s Multi-Factor Authentication (MFA).
“Still the biggest return on investment,” says Scott Ehrman. “It hardens the environment almost immediately.”
MFA should cover any system that could affect security or operations, including VPNs, remote access, elevated privileges, and SaaS tools. For apps that don’t support native MFA, route access through tools like Microsoft SSO.
The numbers support this: companies that invest in identity security measures like MFA see up to a 309% return over three years, with a 67% decrease in account takeover attacks and a 60% drop in over-privileged accounts.
Follow the threats
“Most of the attacks we see, over 90%, are identity-based,” says Eric Madden.
That’s why Identity-Based Detection and Response (ITDR) is becoming essential. These tools monitor behavior across identity accounts, flag suspicious activity, and can take automated actions before real damage occurs.
This is especially crucial for Microsoft 365 environments, where attackers typically target user credentials instead of infrastructure.
Don’t just detect, log it
You can’t fix what you can’t trace. Without logs, investigating after an attack is like searching for a leak in a ship that has already sunk.
“If you don’t have the logs, you’re guessing,” Eric warns. “And that’s not recovery, it’s panic.”
SIEM (logging and event management) tools that were once only for large enterprises are now accessible to small and medium businesses, largely due to cyber insurance requirements. Many insurers now require over 90 days of log retention and proof that monitoring is implemented.
The takeaway is clear: prevention is important, but recovery is just as vital. And you can’t recover without visibility.
Partner up
Ultimately, even the best tools need the right guidance. Scott notes:
“Our role as a vCIO team is to advocate for the client. Map out what’s most urgent, what gives them the most value, and help them phase in the rest.”
In other words, don’t buy every tool. Start with the investments that provide leverage now and expand from there.
Scaling compliance without burning out
With leaner teams and growing frameworks, scaling compliance without increasing headcount can feel impossible. That’s where automation and AI come in—not to replace strategy, but to improve it.
Doing more with less
For both SMBs and mid-market teams, automation helps manage the routine tasks that often disrupt audits:
- Documenting processes in real time
- Mapping evidence to controls
- Maintaining continuous compliance across frameworks
“The smartest thing businesses can do is document as they go,” says Scott Ehrman. “Trying to backfill it all before an audit? That’s where things fall apart.”
Automated GRC tools reduce manual work and provide transparency to stakeholders, ensuring compliance isn’t just a file sitting in backup but a visible part of daily operations.
AI vs. AI
While AI helps defenders, it’s unfortunately also boosting attackers. As Scott puts it:
“The phishing emails look more legit. The attacks are evolving faster. We need AI fighting AI now.”
This means investing in AI-powered detection and response tools that adjust in real time, flag anomalies quickly, and cut through alert fatigue. For mid-market teams especially, this helps level the playing field without increasing headcount.
The bottom line? Automation and AI aren’t just nice to have—they’re the best way lean teams can keep up with evolving threats and growing demand for proof.
The path forward
While achieving compliance requires the right tools, the real foundation is a change in mindset.
As Eric Madden put it, navigating security and compliance is like walking a tightrope: “You’re balancing growth and protection. Push too hard on one, and the other starts to slip.”
That tension isn’t going away. It’s getting worse as frameworks multiply, attack surfaces grow, and enforcement becomes stricter. While there’s hope that some consolidation will happen—fewer standards, better alignment—the short-term reality is more complexity, not less.
The companies that succeed won’t be the ones that scramble to catch up during audits, but the ones that invest early and build proof into everything they do.
Author
Srikar Sai
As a Senior Content Marketer at Sprinto, Srikar Sai believes good content should be bookmark-worthy by default. He writes about cybersecurity and GRC, aiming to move the needle with every piece. He’s also an ISO 27001-certified Lead Auditor.Explore more
research & insights curated to help you earn a seat at the table.