Passwords have always been a contentious topic within the cybersecurity world and among everyday users. No one enjoys understanding the complex rules or changing passwords regularly just because the calendar says so.
Over the years, these frustrating requirements have led to poor password practices like sticky notes, password123, or reusing the same login across platforms. This is a breeding ground for compromised passwords and data breaches.
The National Institute of Standards and Technology (NIST) has provided refreshed guidance designed to simplify password management while improving security. These updates, outlined in NIST Special Publication 800-63B, reflect a fundamental shift from outdated, counterproductive practices to user-friendly, research-backed solutions.
The guidelines are evolving again with the release of the Second Public Draft of NIST SP 800-63B-4 in August 2024. While primarily targeted at federal agencies, these standards have become the de facto benchmark for password security thanks to their comprehensive research, rigorous review process, and universal applicability.
Let’s unpack what’s new and why it matters.
TL;DR
| NIST SP 800-63 was published and revised in 2017; however, the most recent revision to this guideline was made in August 2024, and stakeholder comments are being accepted. |
| Some of the recommendations from the list created by NIST apply to previously used, and in fact, most of them were just suggestions. The change now in question seeks to make these guidelines requirement where some standard on password security is prescribed for organizations. |
| The new standard proposed by NIST guidelines states that enforcing password expiration every 90 days is no longer necessary. Instead, passwords should only be changed if they have been compromised or leaked in a data breach. |
Why NIST password guidelines are crucial?
NIST password guidelines protect your information assets and comply with security standards requirements. They represent a set of internationally recognized best practices endorsed worldwide to enhance cybersecurity.
NIST SP 800-63-3 password guidelines are important as the number of password-cracking attempts increases. When attackers gain valid credentials, they can access your systems and escalate their privileges to an administrator or superuser level, resulting in a security breach.
This breach can have severe consequences, from compromising your organization’s security posture to damaging your reputation and financial stability. To avert this, passwords serve as the first line of defense against cyber threats. Following the NIST SP 800-63-3 guidelines fortifies your information security infrastructure.
At a Glance: Updated NIST Password Guidelines for CSPs
The August 24th release of NIST password guidelines introduces a more flexible and user-friendly approach to password security, focusing on both length and complexity. Here’s what you need to know:
What to Do:
- Password Length: A password should be at least 8 characters long and preferably 15 characters. This is because passwords can be cracked, and the longer the password, the longer it takes to crack the code.
- Allow Flexibility in Length: You can go up to 64 characters for passwords thus providing users with the opportunity to create a more complex password.
- Character Options: More password entropy, meaning the passwords should also be able to accept space and all printable ASCII characters.
- Unicode Support: Passwords should also allow Unicode characters, which helps users include characters from different languages. Each Unicode character counts as one towards the total password length.
What to Stop:
- Arbitrary Complexity Requirements: Eliminate unproductive, rigid guidelines that currently include having to type both lower and upper case, numbers, and symbols. Most of the time they don’t offer protection and are incredibly annoying to the users.
- Periodic Password Resets: Don’t force users to change passwords at regular intervals unless there is evidence of a security breach. Requiring constant resets can lead to weaker passwords over time.
- Password Hints: Stop allowing users to store password hints that could potentially be exposed to unauthorized users.
- Security Questions: Stop relying on outdated security questions like “What was the name of your first pet?” These are easy for attackers to guess or find out through social engineering.
- Truncating Passwords: Always verify the entire password, not just part of it. This ensures that users’ full password strength is considered during authentication.
Get NIST compliant on a budget
NIST password guidelines
These password best practices from NIST SP 800-63-3 guidelines don’t just emphasize the strength of passwords but also consider the behavior of the individuals creating these passwords while recommending a fortifying method.
NIST proposes that you need to clearly communicate to users how to do so and explain the requirements, like having passwords of at least 15 characters, with the option for up to 64 characters for passphrases.
Encourage users to make their passwords as long as they like and to include any characters that help with memorization, including spaces. The user interface should support these long passwords.
It’s also crucial not to impose unnecessary rules, such as requiring a mix of character types. Also, password resets should only be required when there is a breach or a user request, not just on a regular schedule.
The goal is to provide recommendations on various aspects of password management, including creation, authentication, implementation, storage, and regular updates.
Here are the 11 rules of NIST Password guidelines are as follows:
1. Use a password manager
Boosting your password strength is easier than you think. According to NIST SP 800-63-3 guidelines, one effective way is by using a password manager. It’s a tool that effortlessly encrypts your passwords and conjures up robust ones.
Ideally, systems should let you paste passwords when logging in. This makes life way easier, especially if you’re using a password manager or have a super long password saved elsewhere.
Research shows that when people use password managers, they’re more likely to create stronger, more secure passwords—especially if you have a built-in password generator to create unique ones for every account.
Here, reducing human error is key. Password managers automatically whip up NIST SP 800-63-3 guidelines for password length and potent passwords or passphrases, sparing you the headache of crafting them manually.
Studies have also revealed that user behavior plays a significant role in password security. Many folks recycle weak passwords rather than fashion new ones that adhere to security guidelines.
This practice opens up multiple vulnerabilities, especially when the same strong password is used across various platforms.
The solution? Equip your team with a password manager like the 1 password tool and give them the know-how.
2. Password length is always greater than complexity
Any system that manages passwords must require passwords to be at least 8 characters long. This is the absolute minimum to make your account harder to crack.
While 8 characters are the bare minimum, systems should ideally encourage passwords to be at least 15 characters long. Why? Longer passwords are way more secure because they’re harder to guess or break with brute-force attacks.
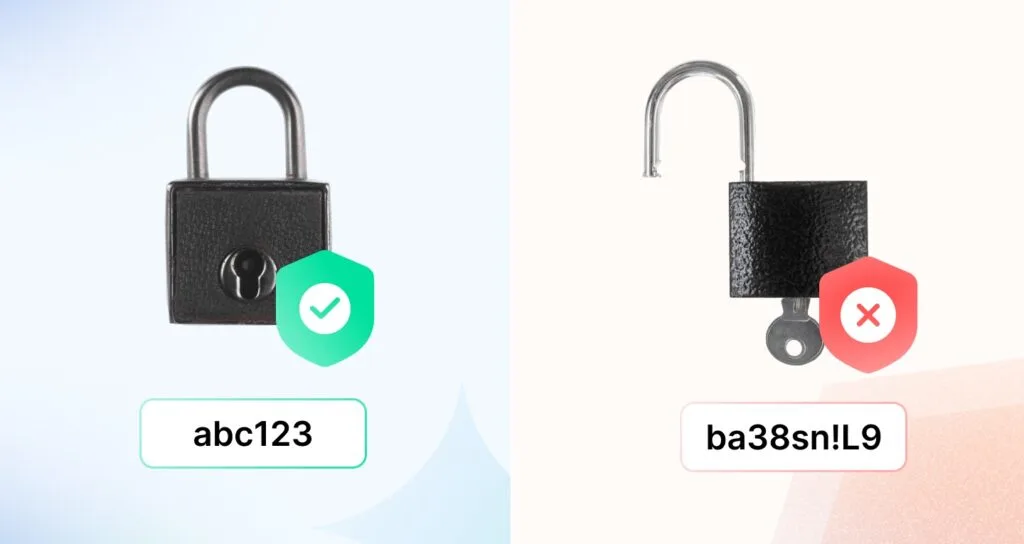
Insisting on complexity, like throwing in special characters or uppercase letters, can sometimes backfire. People take shortcuts, like capitalizing the first letter or adding a predictable “1” or “!” to the end.
While this adds some difficulty, experienced password-crackers anticipate this rookie moves with easy phishing attacks. That’s why the NIST SP 800-63-3 guidelines demand a minimum of 8 characters for standard passwords as a part of the risk management process or privacy risk assessment. Don’t use the same single character or consecutive characters for all your passwords.
3. Choose the “Show Password While Typing” option
Making typos while entering passwords is as common as a cup of morning coffee. When those characters instantly turn into those mysterious dots, it’s easy to lose track of where you went wrong.
This can be frustrating and push you to pick shorter, simpler passwords, especially on websites that limit login attempts and make it easy for unauthorized access.
If you can toggle the option to show your password recommendations as you type from your password lists or passwords against lists. You’ll be much more confident entering those long, complex common passwords correctly on the first attempt, making your online life much smoother with distinct authentication factors.
4. Breached password protection
According to NIST SP 800-63-3 guidelines, every time you create a new password with some password recommendations, it gets a thorough check against a “blacklist.” This list includes no-nos like common dictionary words or simple passwords, repetitive or easily guessable strings, passwords compromised in previous security breaches, and even sneaky variations on the site’s name.
Basically, it looks out for all the tricks cybercriminals might try.
What’s on this blocklist?
- Passwords from previous data breaches (“123456” or “password”).
- Dictionary words (like “apple” or “sunshine”).
- Words specific to the account you’re setting up, such as the service name, your username, or slightly altered versions of them (e.g., “Ryan123” for a username Ryan).
If your password shows up on this blocklist, the system won’t accept it. You’ll need to pick a different one, and the system will explain why it was rejected.
This process helps protect you from brute-force attacks, where hackers try a bunch of common passwords to break into accounts. The blocklist makes it way harder for them to guess your password.
Also, systems are designed to limit how many guesses an attacker can try before being blocked, so the blocklist is a key layer of defense.
5. Keep your password safe with salting and hashing
To keep your secrets safe and sound, NIST SP 800-63-3 guidelines lay down some essential rules. First, when someone creates a lengthy password with lower or upper case letters, it should immediately disappear from the server or primary channel. You can do this using techniques like the zero-knowledge password protocol or zeroization.
You can also do this with Hashing. NIST defines it as a way to transform a plain password into a code, a fixed-length string that looks like a jumble of letters and numbers. Imagine turning “password123” into something like “m8kj94r2l3p8b7l1 for your secure storage.”
So, instead of storing actual passwords, you store these secret codes, known as password hashes, with proper security standards. If hackers try to break in, they only see these codes, not the real passwords.
NIST certification also recommends “salting.” Nope, it’s not your kitchen salt, but adding some extra info to passwords before hashing them. This extra bit makes it even trickier for hackers to crack the code or dry dictionary attacks from their password databases.
For example: Password value is mnc123. The salt value is saltQwoptyu@123. However, make sure to conduct period password resets.
6. Don’t use “Password Hints”
Systems and service providers can’t ask you to use things like “What was your first pet’s name?” or “What’s your mother’s maiden name?” as part of setting up your password.
Why? These “knowledge-based authentication” (KBA) methods are outdated and not very secure. They rely on personal information that’s often easy to guess or find online—especially with how much people share on social media.
Instead, systems are focusing on better ways to secure your account, like encouraging strong, unique passwords and using tools like password managers. So, no more worrying about whether you answered “Charlie” or “Fluffy” five years ago!
7. Don’t change passwords frequently
The old idea of regularly switching them out has evolved. Now, NIST suggests periodic password resets only when there’s a good reason, like when a user asks for it or if there’s real proof that someone might have cracked it.
Why the change? Well, it turns out that making people constantly change their passwords with password complexity requirements makes them frustrated. It’s a hassle, often leading to them picking simpler passwords they can remember. It gives hackers more chances to sneak in because frequent password changes are expected.
8. Limit the number of password attempts
Some bad actors like to guess secure passwords repeatedly until they get lucky (we call this a brute-force attack). You can cap how many tries they get in the repetition of passwords before the account locks up.
Attackers usually need way more tries than someone who makes a typo occasionally. Setting a limit or adding a delay will make it hard for the attacker. It’ll take them so long to crack it that it’s not worth their time.
9. Use Multi-Factor Authentication
MFA is also known as two-factor authentication (2FA). Here’s how it works: to log in, you need to prove two things out of three categories:
- There’s “something you know,” like a password. You’ve got that covered
- There’s “something you have,” like a phone. You might have an app or a code on your phone
- There’s “something you are,” like a fingerprint. That’s your unique biometric signature
NIST says MFA is a must for protecting personal info online. But they’re picky about what counts as a valid form of authentication.
For example, email and voice-over-internet protocol (VoIP) don’t cut it because they’re not considered out-of-band (OOB) authenticators.
10. Give feedback explaining why you rejected a password
It’s important to help users understand why their passwords might be rejected. Here’s how you can do it:
- You can use password-strength meters. These little helpers show users how strong or weak your secure password is.
- Consider limiting the number of secure password tries. This doesn’t give way to endless guessing.
- Let users see their secure password as they type it instead of just showing dots or asterisks. This makes it easier for them to spot mistakes.
When a user tries to create a password that doesn’t meet your standards, explaining which rule it breaks is a good idea.
This way, they can fix it and create a password that keeps their account and your database safe.
11. Keep special character rules in passwords
NIST says you don’t have to worry about including uppercase letters, lowercase letters, or special characters (like !@#$%^) in your passwords. Why? These rules can lead users to create weaker passwords.
Instead of making secure passwords stronger, people often use the same old phrases and slightly tweak them for each website’s requirements.
What’s more important now is promoting longer and more secure passwords. Systems and service providers can’t force you to include specific character types in your password.
As long as your password meets the length requirement, you can decide how to create it—whether it’s a simple passphrase like “ilovecoffeeforever” or something more complex if you prefer.
But don’t get us wrong, using special characters is still a good idea, especially when creating random passwords. The key is to not give strict rules and be more flexible about including special characters.
NIST recommendations for setting up passwords according to the new draft
Not every organization is required to follow NIST’s password guidelines, but many choose to implement them voluntarily because they provide a solid framework for securing digital identities.
This section is specifically about how verifiers (like systems, platforms, or service providers) handle passwords during setup and management—not just when you create a password but also how the system enforces rules for storing, verifying, and maintaining them.
Here’s a brief rundown of what they suggest as a part of your privacy controls as per the new update as of August 2024:
- For Unicode users: If your password uses Unicode characters, they’ll normalize it (basically cleaning it up) before hashing. This helps avoid confusion caused by different ways the same character might appear.
- Password length requirements: Passwords must be at least 8 characters long. Ideally, they should allow up to 15 characters or more, the longer, the better for security.
- Go long, if you want: Passwords can go up to 64 characters max.
- Freedom in characters: Use any printable ASCII characters (letters, numbers, symbols, spaces). Unicode characters are also fair game, meaning emojis or characters from other languages are allowed. Bonus: each Unicode character counts as a single character for password length.
- No weird password rules: There are no annoying “must include an uppercase letter, a number, and a symbol” rules. You get to create passwords that make sense to you, not just your IT team.
- No forced resets (mostly): Forget the hassle of changing your password every 90 days “just because.” That’s no longer a thing. The catch? You’ll still have to update it if your password has been compromised.
- No password hints: You know those “password hint” fields? Yeah, those are gone. Anything that an attacker could see without logging in is off-limits.
- No more security questions: “What’s your favorite color?” or “What’s your mother’s maiden name?” Nope, there are no more knowledge-based authentication questions when setting up passwords.
- Passwords verified as-is: When you submit a password, the whole thing gets checked, no truncating or ignoring parts of it.
As a bonus, we have collated the NIST 800-53 Controls List to help you with the risk assessment. Take a look:
Download Your NIST 800-53 Controls List
NIST recommendations on password changes as of August 2024
There’s been a lot of buzz around NIST’s New Guidelines for Passwords and two big updates to password rules, especially in the latest SP 800-63B-4 draft (check out section 3.1.1.2). Here’s the gist:
- No more complex password rules: Verifiers and CSPs aren’t supposed to enforce mixing upper and lower case, numbers, or symbols in passwords.
- No mandatory password changes: You won’t need to change your password every few months just because. The only exception? If there’s actual evidence that your account or authenticator has been compromised, then yeah, a password reset is mandatory.
What if the password gets compromised?
When the password is compromised, organizations should stop making users change their passwords arbitrarily, like on a set schedule. Instead, a password change should only be required when there’s solid evidence that the password has been compromised.
When you change a compromised password, make sure you change all variations. And, whatever you do, never use that compromised password or any variation of it again. Because cybercriminals know that users often revert to their old passwords, they’ll keep trying that compromised password, or variations of it, for years to come.
Need Help Implementing NIST Password Guidelines for Your Business?
The NIST password standards mark a major shift from the federal password policies we’ve seen for decades. To stay secure while adhering to these guidelines, it’s important not to cherry-pick which recommendations to follow (for example, opting for just an 8-character minimum without considering other factors like password complexity).
So how do you make sense of these guidelines and apply them in a way that fits your business’s needs? That’s where compliance automation tools like Sprinto come in. Sprinto makes it easier to follow password best practices with automated updates and ensure your IT infrastructure stays secure without overburdening your team.
While tools like Sprinto can streamline the process, expert advice is a game-changer. Our clients have successfully aligned their systems with the latest cybersecurity standards while staying focused on what matters most—their business growth.
Ready to implement the NIST password guidelines effectively and protect your business? Let’s chat about how you can do it with ease!
FAQs
Yes, NIST’s 2024 updates have introduced significant changes to their password guidelines. One of the most notable changes is the recommendation to stop enforcing mandatory periodic password changes.
The reasoning behind this is that frequent password resets often lead to weaker passwords, as users tend to make minimal, predictable changes. Instead, passwords should only be updated if there is evidence of compromise.
A 12-character password is extremely safe because they are impossible to guess for a person and is considered the best safeguard against threat actors. Combining lowercase letters, uppercase letters, numbers, and symbols will make it much better for you.
According to the password rules of NIST, user-generated passwords should be at least 8 characters, while machine-generated passwords can get away with 64 characters in length.
No, it’s important to note that NIST recommends resetting passwords only when necessary. While many organizations traditionally enforce a NIST password policy where passwords expire every 60 to 90 days, NIST diverges from this approach. NIST does not recommend password expiration as a general practice.
The strongest password is one that includes numbers, symbols, and a mix of uppercase and lowercase letters. Avoid using common dictionary words in your password.
Follow NIST’s password guidance by choosing longer passwords or passphrases (at least 8–15 + characters, up to 64) instead of just mixing symbols. Use a password manager, avoid common or breached passwords, and don’t rely on hints or forced periodic changes. Longer, memorable passphrases are harder to crack and easier to manage.
Author
Meeba Gracy
Meeba, an ISC2-certified cybersecurity specialist, passionately decodes and delivers impactful content on compliance and complex digital security matters. Adept at transforming intricate concepts into accessible insights, she’s committed to enlightening readers. Off the clock, she can be found with her nose in the latest thriller novel or exploring new haunts in the city.Explore more
research & insights curated to help you earn a seat at the table.