During a recent conversation with Christophe Foulon, a vCISO at Qusitive who has over 17 years of experience, I naively asked him Can we equate bigger cybersecurity budgets with better protection—or are we missing the bigger picture?
Christophe didn’t hesitate. “A big budget doesn’t guarantee good security—if it did, we’d never hear of billion-dollar companies getting breached,” he said. His point resonates with industry observations. According to research by McKinsey, there is no direct correlation between how much a company spends on security and the success of its security program. In fact, some organizations that pour hefty funds into cybersecurity are underperforming in resilience compared to lower-spending peers.
Money without strategy is an expensive PLACEBO.
Security budget: how much do you need?
Of course, too little budget will almost guarantee weak security (you can’t defend a castle with pennies). But beyond a certain point, more dollars don’t automatically translate to fewer incidents. It matters how that money is used: what assets you prioritize, which risks you mitigate, and whether security is woven into company culture.
“We need more budget”; why do the calls never go down?
When I asked him this, he told me that there are two main reasons why the persistent call for more budget never quite goes away:
- Invisible ROI: GRC is a strange beast for ROI. When you do your job well, nothing happens. There’s no tangible profit or product; the reward is simply the absence of disaster. As a result, executives struggle to quantify the return on security spending. “Explaining our ROI to the board means asking them to imagine the headlines we avoided”, says Christophe.
- Fear of regret: Budgets often spike right after a major breach—nobody wants to be the next headline. Not wanting to be caught underfunding security, C-suite leaders will reflexively approve increases. But over time, that urgency fades in the absence of incidents, and security funding can stagnate or get cut. Security teams then clamor for more budget because they know a lull in incidents is precisely when complacency sets in.
So, the call for budget persists largely because security teams are trying to hedge against an ever-expanding universe of threats without a clear yardstick of success.

More importantly, why haven’t we solved this problem?
When I asked him why security leaders are still fighting for basic budgets—especially when the importance of cybersecurity is well-established. His answer pointed back to a deeper organizational flaw:
Security budgets shouldn’t live in a silo. According to Christophe, they need to come from two places:
- Organizational overhead: For foundational requirements like compliance, data governance, and privacy controls.
- Business unit budgets: When projects like a new CRM or a marketing automation platform introduce new risks, the cost to secure those initiatives should be built into the budget—not offloaded to the central security team.
The problem is most organizations haven’t matured enough to structure budgets this way. In more evolved companies, internal chargebacks are common—business units “pay” for the security services they consume. But in smaller or mid-market organizations, that’s rare. As a result, security teams are under-resourced and expected to cover risks generated by other departments without additional funding.
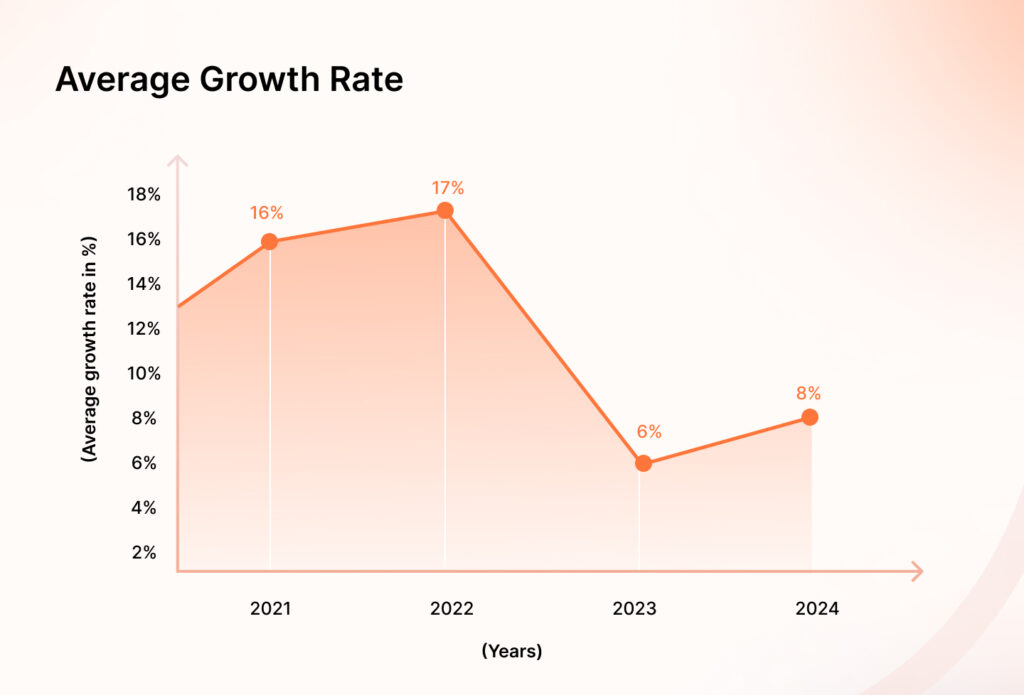
Here’s another thing to keep in mind while understanding the budget problem; while budgets might* have grown, hiring hasn’t kept pace. Security team expansion has slowed sharply—dropping from 31% in 2022 to 16% in 2023, and falling further to just 12% this year. Meanwhile, over a third of CISOs say their team sizes have remained unchanged, signaling a more cautious, deliberate approach to scaling headcount.
* I say might because
Multiyear security budget trends show clear differences across industries. Financial services, tech, retail and hospitality, and legal sectors have seen modest improvements over 2023, with growth settling in the mid-to-high single digits.
In contrast, sectors like healthcare, business services, and consumer goods have experienced further slowdowns, with average growth rates continuing to decline year over year.
And so in order to optimize what you have, I asked if there’s a way you can split your budget for maximum ROI
The formula for splitting your security budget
At one point, I asked Christophe if there was a rough formula for how companies should split their security spend—between tools, training, and processes. His answer?
“The famous answer: it depends.”
But he did offer a way to think about it. Instead of forcing a fixed percentage across the board, start by looking at what your security program tries to enable. For example, if your goal is to bring on the right vendors securely, you’ll need investment in procurement processes, vendor assessments, and maybe a tool for continuous monitoring—but not necessarily a suite of heavy-duty platforms.
More tools can create more problems
Many companies have accumulated a staggering array of products: firewalls, anti-virus, EDR, SIEM, SOAR, DLP, CASB—the alphabet soup goes on. In fact, firms have an average of 60 and 75 security tools in their environment. This kind of tool sprawl has become its own problem.
Each new tool is initially acquired to fill a gap or add a new capability. But over time, you end up with overlapping functions, siloed data, and an integration nightmare. Instead of making security stronger, an excess of tools can create noise and complexity:
- Each tool needs configuration, monitoring, patching, and expertise to be used effectively. Maintaining 70 different systems can overwhelm security teams. One study found companies deploy an average of 47 different security solutions, but only 39% of IT experts feel they’re getting full value from those investments
- Many tools don’t talk to each other well. Data sits in silos, making it hard to get a unified view of threats. A vulnerability scanner might flag an issue, but if it’s not integrated with the asset management or ticketing system, remediation falls through the cracks. Ironically, buying more tools can reduce visibility if you can’t aggregate their outputs.
In our chat, I mentioned feeling pressure to buy the “latest and greatest” tools. Christophe cautioned that chasing shiny new tech can backfire: “Every new tool comes with hidden costs – you need people to run it and processes to leverage it. Otherwise, it’s shelfware.” He has a point.
Closing thoughts
The takeaway isn’t that budget, tools, or compliance don’t matter—they do. But none of them work in isolation, and don’t guarantee security without the right mindset, structure, and intent behind them.
As Christophe reminded me, “Security is about mindset and execution. Budget, tools, compliance—those are just support.”
For CISOs, this means a few things:
- Budget asks need context—tie them to business goals, risks, and outcomes, not fear.
- Tools need discipline—buy what you can use well, not what looks good on a Gartner slide.
- Compliance needs nuance—treat it as hygiene, not headline.
- Most importantly, budget responsibility should be shared, not centralized. Security isn’t just your problem—it’s the company’s.
We may not be able to eliminate the “more budget” conversation entirely, but we can shift how we approach it from a reactionary cycle to a proactive, risk-aligned strategy.
Author
Heer Chheda
Heer is a content marketer at Sprinto. With a degree in Media, she has a knack for crafting words that drive results. When she’s not breaking down complex cyber topics, you can find her swimming or relaxing by cooking a meal. A fan of geopolitics, she’s always ready for a debate.Explore more
research & insights curated to help you earn a seat at the table.