Cloud computing is an evolving technological sphere. It is revolutionizing the way enterprises conduct business while accelerating digital transformation, proving beneficial not only for small-scale businesses but also large-scale as well as mid-size brands. These revolutionary developments also mean more challenges in cloud computing.
Cloud technology offers benefits in terms of data security, flexibility, high performance, and efficiency offering smoother processes as well as improved collaboration between enterprises while cutting costs.
However, there is quite a lot of ambiguity surrounding the cloud, and it has its own drawbacks when it comes to privacy concerns and data management. The list below discusses some of the key challenges in the adoption of cloud computing.
What is cloud computing?
Cloud computing is the process of deploying computing services—including servers, storage, software, analytics, databases, networking, and intelligence—over the Internet (“the cloud”) to offer flexible resources, faster innovation, and economies of scale.
Cloud services aid organizations in running their infrastructure more efficiently, lower operating costs, and scale as their needs change. Businesses around the world, post-COVID-19 pandemic, have increased their investments in cloud technology solutions.
Top 11 challenges in cloud computing
Cloud is an important resource with its various benefits, but it has various risks and challenges as well. This article will dive deep into a few of the most common cloud computing challenges faced by the industry, cloud security challenges and risks, and cliched cloud computing problems and solutions.
The top 11 cloud computing challenges are:
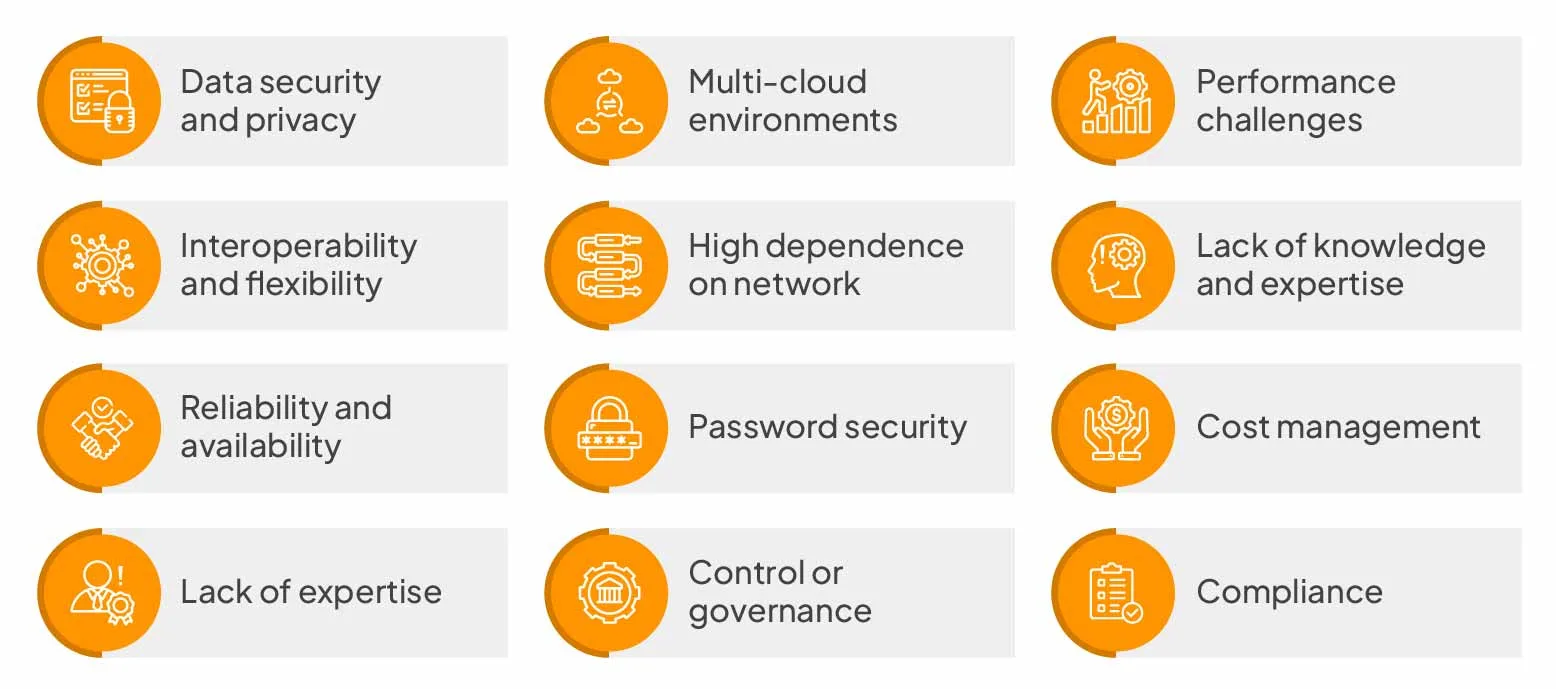
Data security and privacy
When working with Cloud environments, data security is a major concern as users have to take responsibility for their data, and not all Cloud providers can assure 100% data privacy.
No identity access management, lack of visibility and control tools, data misuse, and cloud misconfiguration are the common reasons behind cloud privacy leaks. There are also concerns about malicious insiders, insecure APIs, and neglect or oversights in cloud data management.
Solution:
Install and implement the latest software updates, as well as configure network hardware to prevent security vulnerabilities. Using antivirus and firewalls, increasing bandwidth for Cloud data availability, and implementing cybersecurity solutions are some ways to prevent data security risks.
Multi-cloud environments
Multi-cloud environments present issues and challenges such as – configuration errors, data governance, lack of security patches, and no granularity. It is difficult to apply data management policies across various boards while tracking the security requirements of multi-clouds.
Solution:
Implementing a multi-cloud data management solution can help you manage multi-cloud environments. We should be careful while choosing the solution, as not all tools offer specific security functionalities, and multi-cloud environments continue to become highly sophisticated and complex.
Performance challenges
The performance and security of cloud computing solutions depend on the vendors, and keep in mind that if a Cloud vendor goes down, you may lose your data too.
Solution:
Cloud Service Providers should have real-time SaaS monitoring policies.
Interoperability and flexibility
when you try to shift applications between two or multiple Cloud ecosystems, interoperability is a challenge. Some of the most common issues are:
- Match the target cloud environment’s specifications by rebuilding application stacks
- Managing services and apps in the target cloud ecosystem
- Working with data encryption during migration
- Configuring networks in the target cloud for operations
Solution:
Before starting work on projects, setting Cloud interoperability as well as portability standards can help organizations solve this problem. The use of multi-layer authorization and authentication tools is a good choice for account verifications in hybrid, public, and private cloud ecosystems.
High dependence on network
When transferring large volumes of information between Cloud data servers, a lack of sufficient internet bandwidth is a common problem. There is a risk of sudden outages, and data is highly vulnerable. To help prevent business losses from sudden outages, enterprises should ensure there is high bandwidth without sacrificing performance.
Solution:
Focus on improving operational efficiency and pay more for higher bandwidth to address network dependencies.
Lack of knowledge and expertise
Hiring the right cloud talent is another common challenge in cloud computing. There is a shortage of working security professionals with the necessary qualifications in the industry. When in-house hiring lags behind the threat curve, choosing a SaaS security company that brings operational capacity in addition to tooling is often the more practical path, since the right partner supplies analysts, playbooks, and on-call coverage alongside the platform itself.
Solution:
Hire Cloud professionals having specializations in DevOps as well as automation.
Reliability and availability
High unavailability of Cloud services, as well as lack of reliability, are the major concerns in these ecosystems. In order to keep up with ever-changing business requirements, businesses are forced to seek additional computing resources.
If a Cloud vendor gets hacked, the sensitive data of organizations using their services gets compromised.
Solution:
Improve both aspects by implementing the NIST Framework standards in Cloud environments.
Password security
Account managers manage all their cloud accounts using the same passwords. Password management poses a critical problem, and it is often found that users resort to using weak and reused passwords. Organizations managing multiple virtual environments and remote mobile infrastructures should also evaluate secure device strategies, including the use of top cloud phones to isolate sessions and reduce credential exposure risks.
Solution:
Secure all your accounts by using a strong password management solution. To further improve security, in addition to a password manager, use Multifactor Authentication (MFA). Cloud-based password managers should alert users of security risks and leaks.
Cost management
Although Cloud Service Providers (CSPs) offer a pay-as-you-go subscription model for services, hidden costs are charged as underutilized resources in enterprises, making the costs can add up.
Solution:
Implementing resource utilization monitoring tools as well as auditing systems regularly are some ways organizations can fix this. It’s one of the most efficient methods to deal with major challenges and manage budgets in cloud computing.
Lack of expertise
Cloud computing is a highly competitive field, and there are many professionals who lack the required knowledge and skills to be employed in the industry. There is also a huge gap in supply and demand for certified individuals and many job vacancies.
Solution:
Companies should help existing IT staff in upskilling their careers and skills by investing in Cloud training programs.
Control or governance
Good IT governance makes sure that the right tools are used and assets get implemented as per procedures and agreed-on policies. Lack of governance is a common problem in cloud computing, and companies utilize tools that do not align with their vision. IT teams don’t get total control of compliance, data quality checks, and risk management, thus creating many uncertainties when migrating to the cloud from traditional infrastructures.
Solution:
Traditional IT operations should be adopted to accommodate Cloud migrations.
Compliance
When it comes to having the best data compliance policies, cloud Service Providers (CSP) are not up-to-date. Organizations run into compliance issues with state laws and regulations whenever a user transfers data from internal servers to the cloud.
Solution
The General Data Protection Regulation Act is expected to address compliance issues in the future for CSPs.
Overcome cloud computing challenges with Sprinto

Sprinto is a powerful compliance automation software that monitors entity-level risks while seamlessly integrating with your cloud setup as well as implementing security controls, all from a single dashboard.
- Maintain a register of all cloud infrastructure, including cloud services as well as on-premises
- Identify and classify all the critical systems
- Protect systems against malware
- Perform regular backups
- Enable logging and monitoring
Recognized as a Leader in Security Compliance as well as a leader in Cloud Compliance and Cloud Security categories, Sprinto helps software-as-a-service (SaaS) based companies in obtaining security compliance certifications such as GDPR, ISO 27001, SOC 2, and HIPAA certifications, among others.
Get in touch with experts at Sprinto to learn more.
FAQs
What are the three challenges of cloud computing?
The three challenges in cloud computing are Cybersecurity issues. Lack of resources/expertise. Cost management and containment.
What is the risk of cloud computing?
Data loss, also known as data leakage, is the most common cloud security risk of cloud computing. Data loss is the method in which data is corrupted, deleted, and unreadable by a user, application, or software.
What is SLA in cloud computing?
A cloud SLA (cloud service-level agreement) represents an agreement between a client and a cloud service provider to ensure a minimum level of service throughout the contract.
Author
Ayush Saxena
Ayush Saxena is a senior security and compliance writer. Ayush is fascinated by the world of hacking and cybersecurity. He specializes in curating the latest trends and emerging technologies in cybersecurity to provide relevant and actionable insights. You can find him hiking, travelling or listening to music in his free time.Explore more
research & insights curated to help you earn a seat at the table.